Dealing With The Devil: Ransomware Negotiation Tactics - Michael Lamb
Show transcript [en]
could hear a thing um cool so I'm Michael uh I am the sa Ops director at precur security um I'll just be going through a talk today about ransomware negotiation tactics um I'll actually be making reference to a genuine incident that I handled uh last year with um a group called lock bit bit a reoccurring theme here um just to get into it uh a bit about who am I uh what have I done whoever been Etc um so so bit of a weird St actually I actually totted up across all the incidents how many actual hours I've spent doing internet response now works out about 5,000 hours um so probably missed quite a lot of key events especially over last
year as things ramped up um I've responded to incidents involving Akira lock bits No Escape few different ones the tldr is that they're all very much the same um in terms of the groups that they are um and one key thing is I love building really good teams uh currently building one with precursor so we launched our security operations center this year um to kind of complement the the pent testing team that's been running for about five or six years now uh my GitHub and Twitter's there as well so I do a few uh open source share a few tools not going to lie most of them are written by CH EBT Shameless plug about prec cursor who
we are what do we do quickly um so we are a Crest certified organization we're partnered with the nbrc um all the usual um badges creds Etc that you would expect to come from a pentest and Company so I don't know if anybody's seen this this episode anyways but this is very much what I see in my head when we put forward the work stream of negotiating with a ransomware actor to the decision maker IE it manager seesaw whoever we're dealing with in the client organization um in this episode of The Simpsons for anyone that doesn't know hom hom Simpsons sells is uh soul to the devil for a donut and he effectively takes bites from that donut as he gets more
into it and then he just loses his soul um it's from experience of doing this that's kind of the way that I see this sometimes seems a bit pointless to negotiate with threat actor you only end up very much worse off the data is already left um so those main organizations that you're you're reporting to for regulatory purposes they don't really care that you're negotiating with them because it's already gone out the network you get no guarantees we know this now there's there's no honor among those thieves um so yeah you've definitely sold your soul however what I'll be going through here is just some of the benefits to actually doing it uh a lot of people think that
Ransom way negotiation is just negotiate the price and ultimately there's a lot of other things you can actually do um such as slowing down the actor getting intelligence um I know Rory at the back there you're doing a little bit of talk earli on about um instant response and getting those answers as quick as possible for different people um and that's it's very much a pressurizing situation you need to get those answers so could we use the negotiation element to kind of slow that down regain control of the pace of the incident and get the answers so the landscape so far um obviously one of the key things that have been all over the news is um the
main person behind lock bit is being identified whether or not that's really changed much because he's just popping back up on Cyber Crim forums this week as well and seeing that China's you know fair game as well all of a sudden um the landscape is still somewhat changing so you've got the shaman element as well exfiltration only as well um sex violence in the US that's been an interesting one so us organizations effectively have to um disclose their incident to the SEC and the problem with the way that they do things over there is you can actually report that incident on behalf of the organization so threat actors will as part of the Distortion elements here if you don't pay us or you
don't work with us we can't see that you're actually cooperating throughout this exercise we'll just tell the SEC you've had an incident and that creates a lots of regulatory fines lots of pressure for the organization again they lose control of the incident the xalon uh element as well is interesting so just removing encryption alt together like does it really matter if the system's encrypted if they've already sto stolen the data because that's the main impact there the shaman element as well isn't just the SEC being in issue um of handle incidents in the past again with lock bit where they effectively said if you do not work with us you don't pay this ransome we'll just tell
all of your clients that you're the approximate cause of their data loss as well and that kind of compounds the issue obviously in the US as well if they've got us um clients as well class action lawsuits well on the cards and that company effectively ceases to desist um ceases to exist sorry within about a week um it's pretty crazy stakeholder extortion as well um and another interesting tactic that these these actors will go through so not just extorting you know directly uh the organization but their investment funds uh they could extort their partners for example as well so it's generally quite a shared issue um when an organization of a certain size um becomes uh ransomed
for one of a better word so the so what um what what is the benefits of actually doing this then so as I've mentioned earlier on obviously um negotiating the price that's it's going to be top of the list there um depending on what your considerations are It ultimately depends on the impact of the incident as well um whether or not they've already stolen the data so by paying them does that prevent them from doing so um mentioned earlier on regaining control of pace of the incident as well and that's an important part of internet management naturally either in it or cyber as well um so kind of feeling that that control again as um
a cyber security team but also as a board as well feeling that you're back in control you can send those coms out and you can say confidently what's happened so far what do we know what are we doing next threat intelligence is a huge Advantage as well um so obviously getting the right person in the seat to negotiate with the threat actor um effectively getting down those objectives of what do we want to get out of this if threat intelligence is up there and you've got the right person they can do some analysis on the type of messaging The Narrative that that individual is using that you're talking to um you can also gauge some obvious
things like time that they're engaging you with um but then there's other things certain indicators that they might share with you that you wouldn't otherwise get from your own network uh which I'll go into as well proof of life is very interesting as well it's very important to have uh proof of life and we mean that by uh the data that's actually being stolen obviously we can see the spikes on the firewall so we can see the data's left we could look at process usage on the system Etc from a forensics perspective But ultimately a lot of this is just a claim from a threat act being made that they've stole the data um and one of the key
objectives maybe of the board or the stakeholder or whoever's effectively responsible for the organization they need to go back to their stakeholders and say confidently what's being stolen what's the impact and what are they doing next so you can actually go in there and ask for proof of life you can use that to your advantage to slow down the incident as well um we've seen it with negotiators where the ask for proof of Life maybe on day three rather than day one and then at day three they ask for that proof they send through maybe a sample set of data and and they can simply use that delay tactic and say look it's going to take us a couple of
days to get through this and by then you're a day five your forensic team is starting to flow in with some potential answers you can start to put in some containment and start to play a bit of cut and mouse as well trip wires um again probably uh quite obvious what you can do here um but you can almost trip the individual into sharing information that they wouldn't otherwise share or leak whilst they're on the network um it starts to introduce more of a human element there as well assessing potentially things like the geopolitical climate that that individual stuck within as well which I'll get into in some of the next slides so three top lessons that I've
learned so the first thing when you're talking about negotiation is have a plan B you can't just start that negotiation with like just this is how it's going to go you're talking to a criminal these people tend not to be wired the same as as normal individuals fingers crossed um and that means that again because you're not in control the incident this is going to go down potentially a few different Avenues and paths depending on what side of bed they got out of that day depending on the way that you talk to them depending on the plan that you've used as well you might not get out of them what you're expecting and that could also cause issues for the in
response team it could also cause a bit more impact for the business as well so this has to be very carefully planned and thought out um not all threat actors really engage the same way um so again a common misconception is just a go in there and say okay well if we wanted to delay the incident a little bit let's say on day three we're going to ask for that proof of life but what if on day one as soon as you open that chat that threat actor then goes there's your proof of life straight away um we see that with black cut or Alpha V they used to do that quite a lot um to effectively
stop you from using that card and delaying them with that proof of life it's just like here's your sample files you need to tell me straight away if you're interested in that um another thing that we see which is quite common is organizations will sometimes Panic as soon as they identify that incident they'll invoke their cyber insurance they go on Google and find inet response teams their it team gets on it and what you end up with is three maybe four different organizations of teams interacting with that Ransom note and on that Ransom note is typically a link to um the dark web that tends to have a chat room in there and when they click
that link what they sometimes don't realize is that can sometimes start a timer and when that timer starts that's it you know you can't really go back from that starting so it's not uncommon for us to land on an incident where typically a 7-Day timer is now only two days and the organization's objectives are still exactly the same it's like we still want all the answers we still want you to help us recover and it's you just look it you go we can't we can't do that unfortunately um so again interacting with chat room links interacting with threat actors Ransom not probably a bad idea so with um threat actor engagement Ransom my negotiation one of the things that you
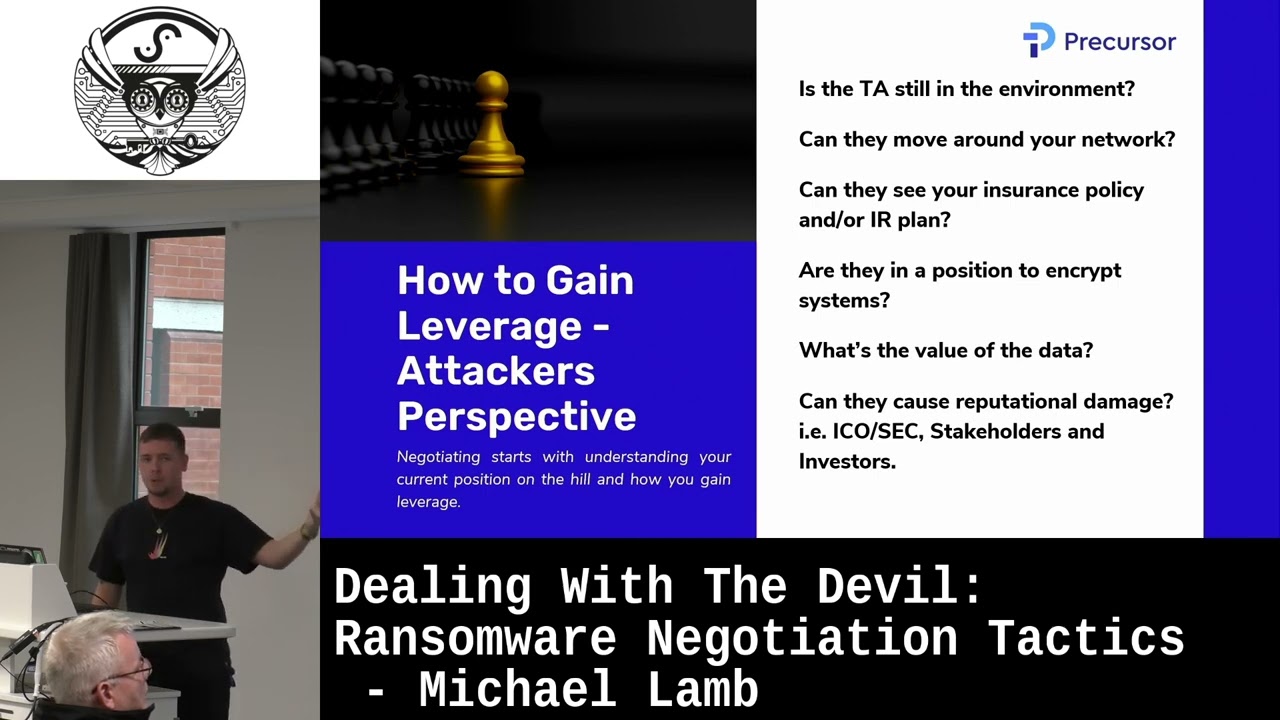
can really do with this is regain some leverage um these are some of the questions that you can generally ask that would help you assess what leverage do you have um over the threat actor and over the incident how much of control do you actually have so is the threat actor still in the environment can they move around the network those two key questions are going to tell you when you're talking to the threat actor you probably don't want to annoy them too much because if you haven't se seen an entire encryption yet they're not on your private Cloud they Haven moved to your public cloud yet you'll probably assume if they're still in your network
that could probably do that within a few minutes or they might have already have and you might not have visibility of that yet as well another quite quite E comical one again that we see can they see your insurance policy and your and your Disaster Recovery plan we see it time and time again people put their insurance policy on file servers the Seesaw leaves it in their in their mailbox they back it up to SharePoint the threat actor's got it and we see it through negotiations and we say look sorry we can only pay this amount of of the ransom can we reduce it to 100K CU that's all we can afford and the threat
threat actor then sends a copy of the insurance policy back and goes well looks like you can afford it um so again that's a sure fire way to lose leverage during that um scenario what's the value of the data can they cause reputational damage um so considering things like the information commissioner's office again the SEC in the US stakeholders and investors you're going to put put them off as well it gets very difficult to quantify what that damage is in a long term um how do you quantify a loss of business as a result of ransomware maybe through reputation damage again it's it's very difficult to quantify um so just try and eliminate unquantifiable damage by just
asking could they just cause it straight away from the organization's perspective some of the ways to gain Leverage is obviously be aware of your statutory notifications um so how soon do we have to report an incident to the is that different to our insurance we've seen it with organizations who have cyber Insurance who don't want to disclose it but actually their policy does stipulate you do still have to report it even if you don't want to make claim and be indemnified for this so it's very important to be aware of what your obligations actually are because come the next year you come to do that insurance policy and they say well actually we did say you on the dark web
and it was leaked but you didn't tell us so that causes issues avoid that shaming tactic um we don't see it a lot out side of the UK but the UK people do not like disclosing things um it's I don't know whether it's a cultural thing with this country but time and time again speaking to different organizations they don't like to tell um their customers they don't like to tell their stakeholders they partners that there's been um an incident and this is what happened but actually it removes that shame and tactic if we already tell our clients what happened it stops the likes of lock bit from them approaching those clients and saying actually did
you you know that they've had an incident and what we started to do was we started to recall the responses that came from the the end clients of these um these organizations and just rated whether or not they were positive or negative and to be honest 80 to 90% of responses that we seeing are actually positive organizations are actually happy to see that they're being told that their data has being leaked through a supply chain attack through third party compromise Etc they're actually quite welcoming of that perform of data loss impact ass even if it's just opening up Excel and just get a list of all that data it can sound quite hard to do and but then
categorize that data and just put a score against it and then you know just give it a lovely rug everyone loves red Amber green and But ultimately the important bit there is it helps you answer key questions like what's being stolen what's the value of that data again going back to that proof of life if they've only stolen data that's maybe nonpr test sample data but they're claiming it's something quite important and valuable you've got leverage at all Al means you can go back in terms of the comm's process and go back to your stakeholders and say there has been an incident but actually through our diligence we know that it's not as big of an issue that it was being claimed to
be and again just being back in control of that incident so just to take you through this and close off I'm just going to take you through these are genuine screenshots of chat logs from Lock bit um they're not online um previously when we did this we did ask for photography but since lock bit's all kind of being caught up with be a good opportunity to share these and just show the inner work of the way that um some of these negotiations actually go um because that's a bit small I've just highlighted some bits of text but for the back probably there's some claims made in this email that's sent to the uh the victim organization so we were able to
access most of your clients bit scary I'll be forced to attack your clients and disable our systems as well as disclosing data from their servers we will put you as the initial Vector of all of these attacks so again you've got that proximate cause coming back into the single Organization for what was actually 50 other organizations around the world and there was all sorts of different jurisdictions as well so you can imagine the the potential dumpster fire that was in front of us on an email that' also pointed out along the bottom there is mail is not safe and we're also aware of your latest transactions now obviously you can go through scorin you can sit down with the
client in incident response engagements and try and discover what's the organization doing right now what's their key events what are they focusing on as a business but again unless the business is forthcoming and gives you all the right information you're n the wiser now this organization didn't actually tell us at that moment that they were approaching a merger and acquisition lock bit knew we didn't um and we didn't actually know until months after the incident and that's what that uh statement meant they'd been reading all the emails they knew that the business was looking to sell off so potentially the impact of this was that that deal was not going to go through so what happened was uh in that email
they invited us to hop on um it's an anonymous peer-to-peer chat called talks uh or Q talks and effectively you find other users on that platform by giving a you get given a very long string um characters and numbers um it's a very good platform for obviously remaining an anonymous um and then talking to people for the purposes of run to my negotiation so we joined that we got a professional negotiator of XM police he had all the War Stories um and he joined the chat and really wanted to collect things to evidential standard but also he wanted to really delay things and see what intelligence he can glean from this and straight away the way that lock bid
actually opened this up with was he said actually this is not all the evidence we've got I'm not at home yet he claims he's actually in hospital with his his daughter um and actually we're maybe going to have to wait until about feed third or the 5th to get a proof of life which worked for us but at the same time you can see that they're already trying to employ that pity tactic whether or not that was it was perfectly true we're not sure but um it definitely felt like they were trying toay delay something that could have been based on where they were in the network maybe they knew we were deploying EDR and they were trying
to delay us uh we're not sure but that's what the tactic was and then at some point they also mentioned that um this person might actually be being sent a war so obviously playing on poten potential Russian Ukraine conflict here we thought this person was already Russian we thought lockit already were anyways so only made sense that potentially they were making a link to that conflict um that made us build up a potential profile physically of that individual that person's fit to go to war it's very easy to build a profile of who they are um and they mention okay the government wants to send them to war so is that going to come around soon is that going
to cause any issues um then they made quite a big epic fa um so upsc if nobody's heard of that term as operational security that's all about protecting yourself um from effectively being exposed um an obsc is naturally a big part of being a ransomware actor it would be very silly if everybody knew your name where you lived Etc who you were uh wouldn't really work unless obviously you lived in Russia which I think the FBI proved so far that exposing the guy behind lock bit it doesn't really make much difference but what he did on TOS was um he went quiet for two weeks and then he came back and went sorry uh been a bit busy you know
countries at War and all that um but if you want to keep in touch here has an email and uh like yeah nice and useful love the customer service and uh as as you do an incident response you sat there at night and you're watching the TV and then your brain just clicks and you're like hang on he gave us an outlook.com email address it wasn't prot on mail it wasn't something where it would be difficult to find out who that individual might be so I just hopped on Twitter hopped on LinkedIn I was like who knows Microsoft Star team who knows people in law enforcement I've got some potential TLP Reddit Intelligence on lock bits can't share it need ndas
someone reached out they said put your in touch on Microsoft what do you need we sign mutual ndas and then we shared this Outlook address um and then they came back and actually said um we've identified that actually uh an IP address is linked to Canada for the person who registered this email address and we've also been able to find a genuine person and Link that to a human in Canada do you have any more intelligence that can prove that this person um that you're talking to on talks is also the person that is implicating the attack on your end client and these 50 other organizations so we just went away was like yeah hands
on deck get a full threat intelligence Park he's all the ioc's and just threw it all out with um permission from the client and it went a bit quiet they said thanks for that we hopped on a call with the NCA the ncsc ET um and obviously people have very few words in those kind of agencies um it went quiet couple of months actually passed and at this point obviously the the incident had kind of been put to sleep because the threat acent just disappeared off talks so it was like last online a few weeks ago and it was like well you kind of wanted to pay the ransom but whatever um so the company
recovered Etc um and then the contact that put me in touch with Microsoft originally text me on Signal and said just watch the news with an eyes emoji I said well there's lots to watch on the news I haven't got time to watch the news um and then this popped up which is that article along the bottom and it was on the US um doj's website you can Google our title you'll find the link um and a Russian national had been arrested in Canada and they actually listed the Alias that that person goes by on talks which was the exact Alias that we've been talking to this point it was like offline for like 3 months when we logged
back on the talks to have a look um so it was quite an interesting incident where we went from obviously having no leverage at all getting somebody in who can regain that leverage get the coms out to the clients and then also realizing that there's a lot more benefit to doing ransomware negotiation than just talking about the price um that's it going to come to a very abrupt end um but if anybody would like to chat after any questions um just give me a shout I'm on LinkedIn and Twitter and GitHub thanks
we've got five minutes left if you do you take questions got five for questions if anyone's got questions easy all right thanks very much do you uh recommend any specific [Music] um yeah like how to kind of analyze R not safely um if there's links like don't click them don't put them in s boxes uh researchers will be looking for onion links appearing en virus to and stuff um apart from that they don't leave a great deal to interact with but again we do see organizations just replying straight back to the email which acknowledges the incident as well um you can kind of leave the threat actor in the dark a little bit by not replying
back to that email and they tend to send a couple more and be like do you know that he's encrypted well obviously but um so apart from that yeah it's just not to interact with it yeah yeah yeah people yeah that's it yeah yeah thoughts on the DAT valuation aspect you mentioned and what was on a server and like obviously protecting those servers um in advance of like the million dollar question um it depends can I just give you that consultancy answer um we see obviously see a lot of XO from SharePoint because that's the easiest place to do it um easiest way to scale it as a threat actor um but file servers tends to be domain joined so it's smb1
having default shares enabled um but you you back into that realm of trying to protect ad which I think has been like a multiple decade Mission though um but yeah SharePoint seems to be probably the worst place for it and I would argue a little bit easier to protect than um than just a file share that's on a network so whilst sharepoint's more accessible you've got L what yeah yeah and they should have hard to get yeah cool





