How To Estimate The Vulnerability Of Users?
Show transcript [en]
Thank you very much. So I think I have now a difficult task as the last presenter after a very long day. But first of all, I would like to underline that there would not be any technical details here, just some little mathematical things. But don't worry. So first of all, may I say some words about me So now I can say that I have started my experience in the security industry more than 30 years ago when I was a student at the Technical University of Budapest and I have found a virus on my computer and it was my first contact with the security and it started in my mind that I should work in this industry.
So, in this presentation, I would like to provide a very short introduction about the project, which is dealing with the human factor. And I provided the title that measuring the unmeasurable and the subtitle that how to estimate the vulnerability of the users. When there is a security person and I say the word vulnerability, I think 99% of them are thinking on the technical vulnerabilities the security holds in the devices. In this presentation, I would like to use the word vulnerability, the vulnerability of any element of an organization, including the humans, including the people as well. So a short agenda is, first of all, I would like to provide a very short sentences about the distributed vulnerability assessment and how can it
calculate, how can it estimate a vulnerability relative to an organization, not just for a device and for a user, but for a whole organization as well.
One of these parts is the user awareness measurement. And I would like to say some words. How can we create user awareness measurement passages? How can we do it? And what are the possibilities? After that, I can provide some use cases about users and some of the very trivial cases when we can decide which of the two users are more dangerous and then of course we can provide and we can highlight the expectation of any metric related to the human factor. And after that the conclusions and future work and all of these things in this presentation is a lot of research work between the University of Dunariváros and the second it. So, first of all about the
Distributed Vulnerable Assessment. It is a methodology including three main information pillars, three main feed pillars. One of them is the malicious activity on the left bottom corner. It is related to any threat can reach an organization not already
reached, but can reach sometime later. The other two elements are the protected IT. It means that any IT elements, hardware and software elements, protections there and so on. And the third one is the, otherwise I call it otherwise use, so the human factor, how the users in the organization use the computers, the devices, the IT infrastructure. It means that we are looking for the middle, the intersection of them. So what are the malicious activities that can reach the organization? What are the threats that can be executed by the IT infrastructure, the hardware and software elements there? And what are the threats that can be enabled by the users using the devices there? So we are looking
for only the intersection. They are dangerous. They are dangerous, the organization really. The structure is related to the following slide. It includes some kind of inner sensors. Inner sensors mean that sensors inside the organization. It means that some kind of assessment of the IT infrastructure and the user behavior assessments as well. And at the top there are the outer sensors from the security vendors, security industry. There are a lot of feeds including the malicious activities, malicious vulnerabilities, and so on, and so on, and so on. And we can provide some kind of preliminary analysis. And of course, these two main parts, the inner sensors and outer sensors, are going to the calculations part, which can
use some mathematics and calculate some kind of vulnerability metric which is related to the organization itself. So what can we do if we have a vulnerability metric? It is a customized metric. It is related to the given organization only, because we use the information from that organization, from the IT elements, the human related information as well. But if we have only one number, we can do nothing about it. But on the other hand, we can identify the dangerous users' behavior as well. So for example, we can choose who are the most dangerous users in the company who can provide the big contribution to the vulnerability metric. So we can identify the vulnerability elements as well, and we can estimate the different contributions, including the users, the devices,
and the threats, and the groups of them as well, or individually as well.
And on the other hand, Another advantage of this metric calculation is that as it is calculated in a simulated system, then we can change a lot of things in the simulated system as well. For example, if we change the operating system in the simulation, then it means that we can calculate what would be if the organization
change the operating systems in the infrastructures from Windows 7 to Windows 10? What is the impact to the vulnerability metric? What would be if they send the most dangerous temp percentage of their user to a tremendous training? What would be the result? From this viewpoint, the usage of this metric is some kind of
decision support system because it can help the size source in their decisions.
So I mentioned that there are some kind of mathematics and I don't want to go into the details in this few minutes, but you can find it on the Secudit website. There are some some academic papers include the detailed mathematics, detailed mathematics description and equations as well. I would like to just talk about the result of this mathematic research. The mathematical background is based on that we can define the probability of that is there any probability which can able to reach, which can reach the organization and it is able to infect at least one computer using the, by the given user and the organization. What is the probability of this event? And this equation includes two main
parts related to the human factor. There is a probability which relative to a given threat and a given user. and it is relative to the user awareness, the knowledge of the user. And there is another on the right side, the frequency, how frequently use the user the devices. For example, there is the difference if there is a user who uses a computer one hour a day, and there is another who uses a computer for eight hours a day. So there are a huge difference between them. On the right side, the frequency can be measured very easily. It means that there are a lot of
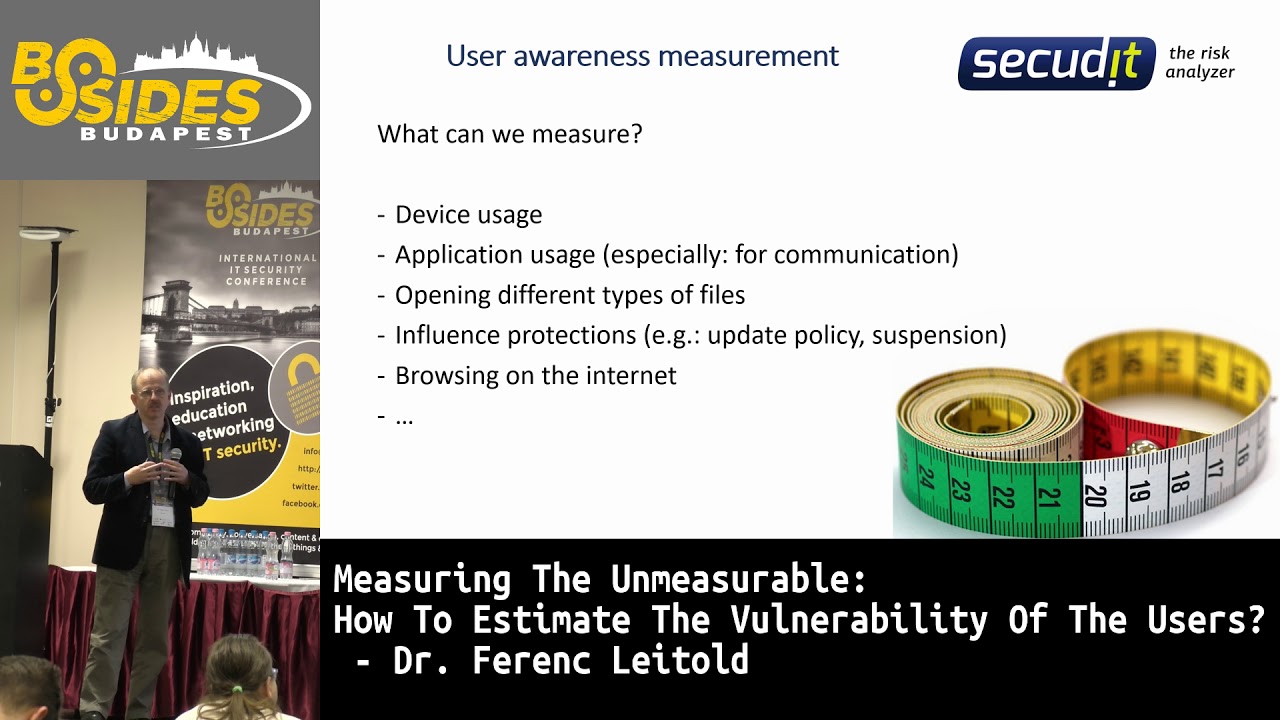
log information to log in and log out from the system and starting and ending in an application and so on. So it can be calculated very easily. The other part is the user awareness is much more difficult. What can we do with the user awareness? So, what can we measure? We can measure a lot of small signals, and we can feel that they have some kind of relations with the user behavior, but on the other hand, it is not exactly proven that what is the relation. So, for example, the device usage, the application usage, especially for communication. I mean the application used for communication includes Facebook, Skype and so on. Opening different types of files. So when a user receives an email,
clicks on the attachment, then it executed on the computer, then it can be a dangerous thing as well. The user can influence the protection capabilities as well. They can change the update policy, they can suspend in some situations the protection on the computer as well. And on the other hand, for example, they can use additional devices as well. It is on the first point as well. And another user habit could be the browsing on the internet. So how often they open for example a new site on the internet. And so on. So there are a lot of things we can find already in a lot of applications, a lot of tools, log files. And we can use them for compute to the user behavior as well.
How can we measure? So about five years ago at the, I think at the biggest IT security exhibition and conference, the RSA, I could count only five, at least five, about five
solutions that were related to measuring the user behavior. Most of them, are allotted to some kind of send something to the user and check the reply. Now, after five years, there are plenty of these solutions, including, for example, using telephone calls as well. So there are two possible ways. There is a positive way and there is an active way. By the positive way, we can monitor only the normal usage of the user, what are they doing using their normal work. And in the active situation we can cause the different situation. We can trigger the user and force them to make a decision.
So now I would like to provide some user use cases. Let us suppose that There are two, we have two users. Two users with different browsing habits. All of the other things are identical. The first user in the browser, he opens only the Portmont.hu and the weather site, the intercape.hu website and nothing else on his working machine. And there is another user And in the browser, she opens at least 20 new websites a week that haven't been visited in the previous six months by her. Who is more dangerous? I think it's trivial. The second one, we can say that the girl and the button can provide more vulnerability, more contribution to the vulnerability of the organization.
Second case, there are two users with different occupations. This lady is working at the HR department and she receives job applications by email, including CVs in PDF attachment. And her work is to open them and read them. There is another guy at the company, He has never received any email with PDF attachment yet, for example in the last year. Who of them provides more problems to the first? Yes. Okay. Let's see the third case. We will make sure the first and the second. The first one is working at the HR department, he receives the PDFs in series, but he only visits only the two websites. The second one, he has never received any PDF attachment,
but in the browser he opens at least 20 new websites every week. Who is more dangerous?
So now it depends on the threats as well. If we have threat 1 and threat 2, and the threat 1 is related to, the attack vector of the threat 1 is related to the PDF attachments, then for the threat 1 is the more dangerous user is the first one. But if we have a threat 2, then The more dangerous user is the second one. So it means that
only using this information, only using the user behavior information, we cannot decide who can provide higher contribution to the vulnerability of the organization. We have to know what kind of threats are in the wide, what kind of threats can reach the organization, what kind of threats can be detected and blocked by the protections at the organization, and so on. So it is a much more complex thing. So, conclusions. So the user awareness measurement has to be distributed relative to different attacks factors. If we have different attacks vector, we have to measure by different attacks vector the user behaviors. If we would like to use the user behavior calculation for anything. On the other hand, the distributive measurement can be
used for calculating the integrated metric using to the security level of the organization. And of course, this... measurement can be relative to different attack facts or the different threats. And the integrated security level is
an aggregation can be calculated using an aggregation of the threat information, the IT infrastructure intervention and user information. And of course, it can be used for organized customized actions for the user. For example, customized user awareness training for the users as well, because we can know what kind of attacks vector, what kind of user behavior should be told them.
So I mentioned that this presentation is based on a
project with the University of Dunajváros and Cekodit. And our primary goals at this moment to identify the user interaction characteristics in case of different attacks. So what kind of attack vectors are and what kind of user interactions required for these attack vectors. We have to identify the measurable signals having any connections with the user actions. And the third one is to find correlation between the user actions identified by the relevant signals and the bad attack vectors as well.
Thank you very much.





