BSides Boulder - 2022 Keynote - Greg Foss
Show transcript [en]
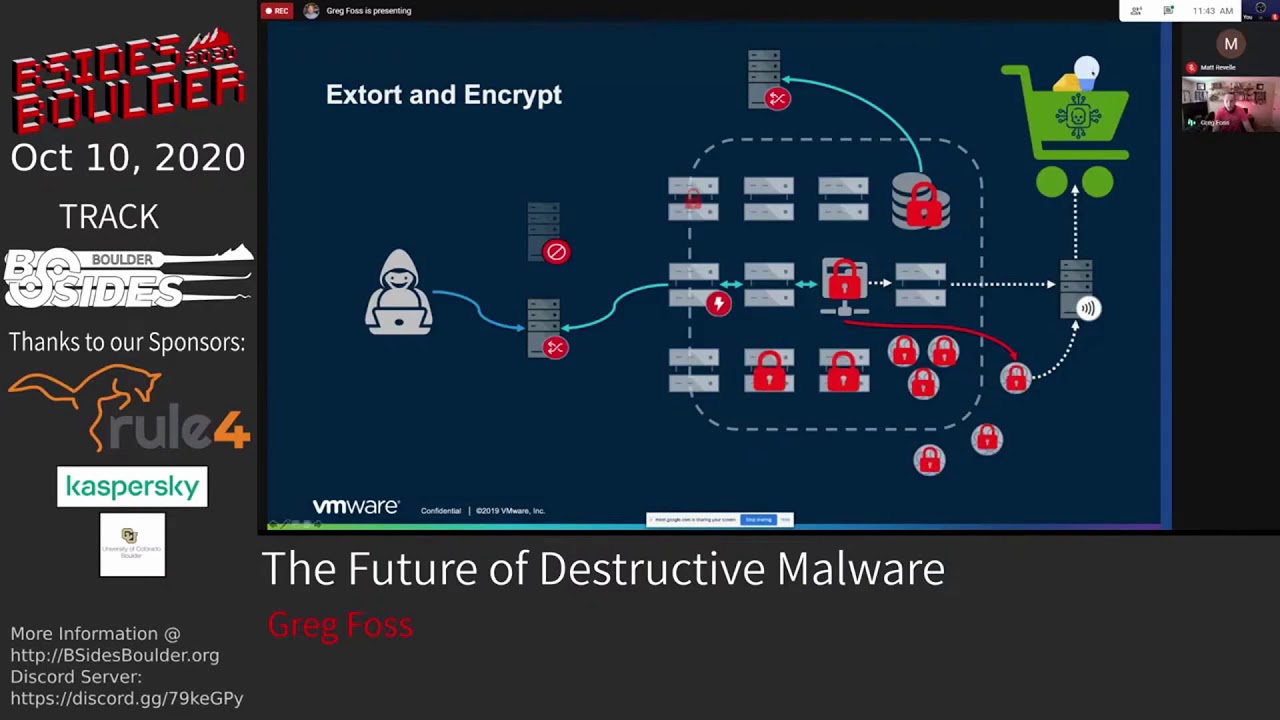
I'm going to do this are you ready okay cool we're going to start a little early sorry uh but I um Greg is a uh principal Cloud security researcher with la lace workk Labs uh where he focuses on large scale data science and threat research intending to help secure customers Cloud environments uh fost has led the research team built and ran a Global Security operations program consulted in red teaming and worked as um as security analyst for federal government in previous roles and um is all around a great person in the community I added that um uh in his free time he spends time with his wife two children and is an avid Runner and swimmer so please welcome the keynote today Greg Fox [Applause] there's power there too yeah Power perfect I think this is the first conference I've ever been to I don't need an adapter this is amazing try it try it this is unheard of you guys are too prepared all right see if oh there we go all right perfect well thank you all so much for for joining us today um man I can't I can't uh even begin to express how nice it is to actually be in person for for this event uh I I remember talking to you guys when you were first planning this you know through years ago and then all of a sudden you know everything changed and we had to go online and you guys you guys did that and you know actually converted very successfully um you know we all had no clue what was going on uh so so Props to you guys and especially pulling this together you know getting us all back together here this year so let's give a round of applause to all the organizers uh such a great events man talk about a venue too this is cool this is this is way too fancy I'm here to class it down a bit so be perfect well so you know this uh this talk the fun part of the keynote is I didn't have to submit an abstract so this is going to be like an amalgamation of random stuff that I just find very interesting so hopefully you do as well and so uh so you know uh eron's introduced me um for those of you that don't know me uh I'm a principal Cloud security researcher with lace work uh I'm also an advisor at uh multiple startups a couple of them here in Colorado which very happy about um you know all that I think is you know on on the surface the job fun stuff but I think one of the more fun parts of what I do nowadays is I working with a lot of people who are getting into the space and trying to Mentor people who are trying to learn uh and grow and and come out uh into this industry because it's a hard industry and so that's why I'm going to start with you know why are all of us here right on a Saturday why are we spending our time working uh you know trying to learn about uh how to do our jobs better how to secure things better and I think uh it comes down to one thing at least for me we're all pretty passionate about this right this is something that's important to us uh that I think you know we would probably do at least I know I know I would probably do this even if I wasn't being paid for it so I think that's why a lot of us are dedicating our free time over the weekend we could be at home doing whatever to being out here learning um and so you know I uh applaud all of you who've come out here to listen to me ramble um because I think it's I think it really speaks volumes to you know how passionate important uh you know these people in this room are to this industry because it's hard uh many of you guys know AJ good friend of a lot of a lot of us here and I I found this quote really good I think he hits the nail on the head um you know starting in cyber security is very hard it's not an easy field uh I talked to a lot of people who want to come into this field because there's money in it and stuff like that and I always tell them like cool go to sales or something because you're going to burn out uh if you're not actually interested in this you're not actually willing to go above and beyond uh because that's what it takes to be really good at this um especially nowadays you know we uh have had our world shifted all of us and and all of us in this room are much more fortunate than a lot of people who didn't have the ability to go work from home and go log in and just you know work work on the computer all day so it affected a lot of people in a lot of significant ways um you know now we're dealing with a whole other kind of tumultuous times we have we have the war going on which is affecting a lot of things uh our economy now we're definitely seeing that impact there and people's lives are being being shifted and then of course you know terrible mass shooting just about every day in Colorado all of this is really affecting a lot of things and uh you know not just uh you know not just in uh the personalizes but cyber security as well is all going to be impacted by all of these events um especially as it starts impacting the economy um you know as we saw recently there's been a lot of companies affected a lot of individuals affected by this uh you know our company as well recently had to lay some great people off uh it's unfortunate and if you haven't seen the site it's pretty eye opening layoffs.fyi uh man there's a ton of companies out there that have cut a lot of very very good people recently a lot of comp companies have completely gone under and um you know it's it's kind of heavy way to start this talk I promise it's not all like this but it does lead into the main topic I do want to hit on which is cyber crime uh you know for years we've had so many people focus solely on advanced persistent threats and and all that kind of stuff but the thing is like most companies cannot detect or prevent cyber crime basic script Kitty stuff uh is getting by just about most companies that a lot of us who work with a lot of different companies see on a daily basis um so that's kind of the focus I want to talk about today is is cyber crime in general and uh really centering around how technology and some of the improvements that are being made uh in sort of the whole underground scene are making it easily much more accessible for people who might not have been uh into cyber crime before so what am I actually talking about here well how many of you have heard uh from many people that my business doesn't do anything important we're not going to be impacted by hackers we don't have sensitive data like all the time people say that they're like we're a school we're you know whatever you know we're hosting providers streaming we do these kind of things the thing is uh hackers are very opportunistically driven a lot of this is just gaining infrastructure gaining ground so that they can perform other attacks down the line so when you look at all these different types of businesses I I really like showing people how attackers view their business and it's eye openening to some people you know schools this is a prime target for emails uh and emails from educational institutions get by a lot of filters uh very prime target and we'll actually show some numbers about why this is so key in a bit hosting of course Anonymous infrastructure if you can compromise assets you can stage your your malware your command and control infrastructure on other people's computers kind of gets you in the clear a bit what about streaming well that seems like a good denial of service platform to me e-commerce how many people have heard of Mage card you know the credit card skimmers injecting JavaScript stealing credit cards when people are paying for things online social media anyone here do red teaming that's the first place we go we're trying to figure out who to Target who's going to have access to things uh everything's out there now you don't even have to do much work to figure out what tools the company uses who works there and everything else in between image hosting well you can store your malware there you can store payloads sometimes steganography if you want to do hidden messages and and that kind of stuff big one that's uh scared me recently is these managed uh service Prov providers pivot Points all of them have access into companies they have credentials they're whitelisted you know all these things where you're already purposefully putting blind spots into what they do because you don't want to trip your alarms uh because these people are logging in anyways through legitimate means perfect Avenue for attackers and we've seen that uh come to fruition recently in a couple very prominent attacks um so you know just just setting the stage with these are the kind of things we should be telling people when they say they don't think they're a Target because everyone is even personal accounts right anyone see this tweet when it came out brutal brutal right especially for those of us in Cloud security this is happening every single day to people uh and hopefully not at this scale like there's a thing called guard rails that you can put in in AWS so all of a sudden if your systems are going wire and your uh your billing is going through the roof you can at least stop it um but pretty scary I mean this guy uh you know ended up being charge $45,000 for someone going into their systems and installing crypto miners uh the real kicker here too is the attacker only made like $800 from this attack which I mean man but if you're using someone else's computers like the cost benefit doesn't matter uh We've even seen somewh people are spinning up landas that do like crypto mining even more exponentially uh you know uh costs that come along with that um but also incredibly inefficient I don't know why they would even do that there's a lot more better uses for lambas for attackers but still oh that's a good oh man that is a very good point I think that's like 25 cents today so it's even worse man that's a very good point well and so you know that that brings us to um you know ic3 always tracks uh the losses associated with these types of attacks and I I was like just showing the scale at which uh these these uh crimes are very successful and these are just the ones that are known and reported to uh to these institutions there's a lot more that that don't even fall into uh you know these these lists here but as you can see uh just last year the total was 6.9 billion do uh in losses due to cyber crime in general now this kind of encompasses everything this isn't just you know one type of cyber crime or another but uh significant uh amount of money being lost here every every single day um and every year it's just about doubling they're expecting this to double again uh this year which is terrifying so one of the real uh kind of core components of this is business email compromise um you know business email compromise is one of the most successful by far uh forms of attacks that we're seeing today uh business email compromise alone accounted for 2.4 billion losses uh in 2021 and that's just what's known right uh and that's from businesses let alone the personal impact personal accounts that are targeted um because this affects everyone in different ways um basically just you know committing scams trying to get people to send money and it's crazy to think that this much money can be generated a lot from like gift cards and things like that uh some of these companies that that do those types of attacks end up making just million doll uh you know like uh hundreds of millions dollars just their single company in a year uh and they have little like actual businesses uh that do like cold calling and stuff like that but then they also have these illegitimate factions so that when they're audited they can point to here's here's our legitimate business and they have everyone else kind of hide uh what they're actually doing in that other side of the of the building um but often times are trying to go for large transfers of money in one time um you know uh really uh trying to get people to transfer money out of the company just by submitting fake uh forms for purchase uh orders and things of that nature and then targeting individuals uh for gift card scams I mean like all of us are affected who in here uh knows someone who's been affected by a gift card scan and fell for it quite a few people I have family members that have that have fallen for it it and the sad thing is we always find out about it too late they tell us after the fact after they've already sent like three grand in in cards to somebody so it's sad it's a very uh kind of terrible scheme that affects people especially the most vulnerable people uh and then romance scams this is a whole other level of evil these people are are terrible uh the the scams they commit some of these go on for years um you know a few of us were just had a conference where someone dove very deep into this and it kind of open my eyes to just kind of how terrible some of these people are uh to the extent of you know some of them are actually practicing Juju and committing very crazy uh ritualistic kind of uh kind of things with money and stuff like that in order to ensure their scams are uh successful um really kind of interesting when you look at like the people behind this so uh there's one group if you want to learn more about this called the Yahoo boys who uh it's kind of terrifying when you look into like what do in order to ensure their scams are successful in these kind of JuJu rituals and and things like that but there's a lot of documentaries out there where you can look into and and learn more about this but business email compromise uh is one of the biggest problems I think our industry is is kind of facing today but the stats from it are pretty interesting right so uh one of the things we've been doing is collecting a lot of the the numbers for uh what's for sale on online forums uh so one of the things I I like doing is going and scraping this content and uh automating the collection of seeing you know what's for sale what's the dollar value how much is out there um and the real interesting thing here you know we're talking about educational institutions uh you can see they made up 35% of email uh compromises that were for sale so this is basically someone gains access to an email account or a set of email accounts or even an entire company companies uh email servers and then offers these up for sale online uh and over here you can see the pricing as well based on each uh essentially uh provider but what's real interesting here is those educational institutions there's a lot of reasons behind it they kind of Market it as like you can get discounts on things it gets by spam filters you know all all those kind of things that lead to it being one of the more prominent uh items for sale on these forums um of course uh the pricing is very cheap you know for around $5 to $10 you can purchase access to someone's email account uh and then you can use that for whatever you want you can go through their uh list of contacts you can spam all them you can use this to Target other companies and things like that um just infinite kind of uses that attackers will find just for email accounts and these are very abundant if you look uh if you do any crime whereare research the big one I think um the that I that I really want to highlight you know with this whole talk right is just like these cyber crime markets have really changed the game over the last few years uh lowering the bar making it so people who have no clue what they're doing have access to these tools and techniques and resources in order to commit some pretty uh serious crimes um you know right now you could purchase these emails you could purchase access to systems you can rent access to a ransomware service you can rent a command and control server you don't have to know anything about how to launch these attacks or do anything they come with step-by-step guides uh you know we saw recently with the Conti leaks uh they actually had a training program for onboarding new people and they even told them that this was like a legitimate job and people didn't really realize until they were there uh so they had a very high turnover because of that which is kind of hilarious but uh but when you look at these com these uh groups a lot of them operate like legitimate businesses they have someone at the top they have people kind of directors running different parts of the operation uh and I think the K Elites is one that you know really uh highlights this because uh due to the the War uh going on in Ukraine right now they were split right they had one group that was in Russia and they all of a sudden came out publicly and said we support Russia and we're going to you know attack Americans or anyone who you know goes against Russia and then the ukrainians over there also team members were like [ __ ] that we're going to dox all your stuff online and they did and so we got to learn a lot about how these groups operate in terms of business structure so it's real interesting but the scary thing for us is like this really lowers the bar and makes it easy for a lot of people to get into this space who might otherwise not uh not be able to or not have the knowledge to do so uh which brings me to initial access Brokers any here here of uh initial access Brokers these are essentially these groups that uh or individuals mostly that go and compromised assets they as the name States their uh you know main goal is just gaining access to things whether it's personal resources corporate resources things of that nature and then they just turn around and sell it uh online often for very cheap some of these you can buy access to uh you know personal assets for around $10 um you know this has been going on for a long time the big part uh the big change I think is the resale of corporate access uh you know we've seen that going for you know many thousands of dollarss depending on the company we even saw a few years ago there were three different antivirus firms that were offered up uh for sale online access into their environment uh they also sold their source code uh which is also a very common happening in these groups so what do these look like right they come in all sorts of different shapes and sizes and forms uh you can see this one this was initially posted in uh 2018 this group is still operating by the way the Genesis store uh you you know they just keep shifting infrastructure and whatnot uh but essentially they sell access in a lot of different ways um you know they'll have browser fingerprinting they'll have logs that have been exfiltrated from environments they'll have just St uh straight credentials remote desktop SSH things like that um you know and sometimes they'll even just have rats where you can just log into systems that are shelled uh especially web servers the web shells where they'll provide credentials to to access um and the breakdown of these is kind of interesting this is a different store this is a dedicated actual Marketplace and you can see the breakdown of the assets that they have for sale uh quite a few assets as well so C panel access uh into various servers leads uh that's commonly emails so that's like email lists uh and leads are basically what spammers will take so they have a Target list to go after um SSH RDP SMTP is the big one uh because then they can relay their spam they can do all sorts of things that allow them to commit uh you know more acts of Fraud and and things of that nature but it just you know goes down from there and this is only growing uh every time we find one of these stores or one one gets taken down uh like five more pop up and so it's actually like become like a full-time job just trying to trace all these and and keep on top of them uh because they're always changing and they're always improving and there's always new uh upand cominging stores that are coming out with more and more more offerings at cheaper rates um but the big one I'm real interested in uh coming from lac