Greg Foss - The Future of Destructive Malware
Speakers
Tags
StyleTalk
About this talk
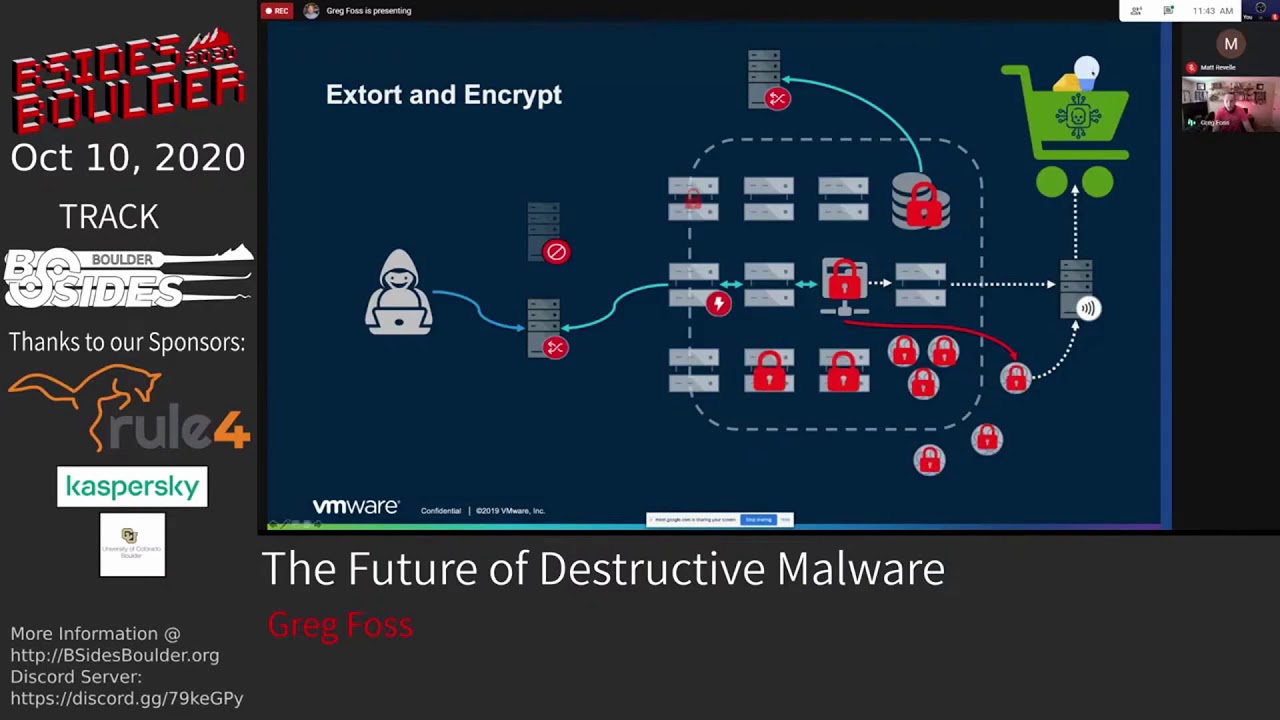
Technology continues to become more intertwined with the physical world around us. With the possibility of controlling our homes, businesses, and even major infrastructure autonomously, we are now more dependent upon technology for our daily lives than ever before. We'll take a look at the history of physically destructive malware and lead into the increasingly-complex modern attack trends and advancements being made in this ever-expanding underground community, using Carbon Black's unique attack data. Exploring the actors behind critical infrastructure attacks, uncovering the details of how they run their global operations, as we prepare for what's to come. Computing today is much more secure then it was, say 20-years ago. We are no longer bombarded with the popups and drive-by-downloads that used to plague the early internet. However, there are newer and more impactful attacks that are becoming more advanced and targeted each year, many with the goal of causing real-world impact... We'll start with a deep-dive into the history of various destructive malware families and the actors behind their operations. We'll cover their overall objectives and how they achieved them - focusing on physically destructive cyberattacks that have had significant impact to the real world. Some of which are public knowledge, others are lesser-known and/or unattributed, until now. Leading from here into the nation state sponsored threat actors, their operations, dissuasive tactics, and the lengths advanced adversaries will go to, to cover their tracks and strategically force miss-attribution. Destructive cyber attacks do not always have to materialize in the form of something physical, such as taking out power, disabling waste treatment, degrading networks, deploying ransomware, etc. Some of the most harmful infringements are subtle, even unnoticeable, but designed to break down societal trusts and weaken a society as a whole, very slowly, causing long-term and lasting impacts over time. We're seeing this today with foreign influence, not just in the United States, but all across the world. They are the games all nations play, in the constant struggle for international influence and power. We will examine case studies where social influence manipulation has had real-world impact and where this is headed with technical capacity for disinformation creation and dissemination continues to improve. Looking to the future of physically destructive malware and increasing trends - there is not only a consistent shift towards more and more infrastructure being accessible online, but new underground markets that lower the bar to entry. Access Mining has continued to increase in popularity among malware authors; wherein they siphon credentials and often deploy remote access trojan's (RATs) to a host, under the guise of being something innocuous like a crypto miner. Later posting direct access to the compromised host online for around $3/node. Couple this with specific targeting of ISP's, physical locations, and demographics, the need for unskilled attackers to understand initial exploitation is no longer required to cause significant damage. We'll examine these marketplaces and highlight how this plays into Supervisory Control System and Data Acquisition (SCADA) and Industrial Control Systems (ICS) by mapping and examining exploits for local infrastructure in the Boulder area. What impact can the continued advancement of technology have, both in terms of attack and defense? While we're primarily focusing on the destructive nature of modern malware, our defenses are continuing to improve right along with them. The security industry is keeping pace, dedicating teams to understanding and defending SCADA/ICS with a new understanding and appreciation for the complexities of these systems. This industry now has a roadmap to follow in understanding how to protect against destructive attacks - the MITRE ATT&CK Matrix for ICS. Additionally, the creation and advancement of new honeypots that emulate SCADA/ICS allow researchers to learn how these systems are attacked, so we can protect against the real thing. Along with new open source tools both for assessment and mitigation, we're able to understand and mitigate potential issues before they cause real-world problems.