OSINT in Cyber Security & Intelligence Communities
Show transcript [en]
thank you Adan so first of all hi everyone this is my first time being here even though that I'm a local I really enjoyed the previous workshops talks and let's continue with ENT let's do a short introduction on me first since this is my first time being here I'm kab Kaka certified ethical hacker from E Cil and Cisco I'm ENT enthusias and practitioner of viously and I'm a cyber security officer at ND bit previously worked in the banking sector now switched up to a startup what is open source intelligence open source intelligence with a boring definition is a practice of collecting and analyze analyzing information that is publicly available but what does that mean let's let's get
a Everyday Use or everyday case if we post a picture on our social media and we we pick the Privacy option public a developer that is located in India takes that photo downloads it and uses it for an AI machine that he's he's doing on on on his own that is ENT this is just a simple let's say case who uses oen the the the most the biggest category is Hackers when I say hackers I involve black hats and white hats so I won't separate them I've seen hackers get thousands and thousands of dollars of bug bounties by using ENT open source intelligence how come companies sometimes are not aware what they are posting on your on their social media
for example if I own X company and I'll pause that our company now has some from uh Cisco firewall implemented I'll get a picture of the firewalls posted on social media a hacker can see that I use Cisco firewalls go hunt for CVS on the specific Os or specific device and turn that information into a weapon I talked about the company perspective let's talk about the personal uh perspective usually uh I hope not anyone who is present here but uh people in general tend to leave password something that uh describes them or it's personal about them so if a hacker has free access or open access to our social media he'll know anything about us if we have any child if we have any
pet if we drive any type of specific car Etc he can get that details put it on a word list and and continue further with an attack so the the biggest category is are hackers a lot of hackers uh let's say win a lot of money by just doing Google Dorking Google Dorking or Google hacking is typing specific parameters on Google search giving specific pal specific file types and Google will will give you back the results and with just a few clicks away you you got yourself a good back Bounty the second category are law enforcement agencies and in intelligence communities the law enforcement in general uh unfortunately not in Kosovo in general they use ENT a lot
how I've seen people get arrested from social media posts criminals are being stalked on social media with sock puppet account so PE uh people who tend to post or show off their criminal activities on social social media that's just an extra pair of eyes and ears for the police officers that are stalking thousands of criminals on social media platforms as about intelligence communities there are a lot of platforms that uh we cannot mention and are confidential that use our public data and uh intelligence communities have access to it by just clicking and putting on a single name the other category are journalists journalists law free data they they love everything that is available publicly out there for their profession so
journalist also use those in a lot businesses tend to get as much information on they Co on their comp so they could get ahead uh of them and last but not least everyone who has access to public data is an ENT user if you've seen someone in this conference you were not sure who was that guy with just a few clicks on social media uh you could get to the person without even knowing him so you did an ENT Act of intelligence there's a dark side of ENT and the bright side of ENT why is that the Dark Side of ENT is I I did put a quote on this one to have a much better
overview too much information Exposed on the Internet is like leaving your front door wide open in a crowded City no one want wants to do that no one wants to leave our front door open in a crowded City so you have to be extra careful what are you posting on social media or leaving your Trace is on the internet because that simple information that does not really matter for you can be turned in into a weapon by an hacker the bright side of ENT as I said police officers around the world are stalking criminals are gaining evidence for criminal activities through oen so embracing oen is like having countless eyes and ears for law enforcement it's a
powerful technique and they do use it a lot I'm about to present a few open source intelligence tool that I can share uh without even having to hide the names you can all download by just typing the name of of the tool the first tool that I'm about to present is the web check. as93 nnet this platform uh I know that there are a lot of penetration task and security researches here we know that the most critical part of of hacking is gathering information or reconnaissance sometimes getting a lot of information for a web where having the architecture of the web is kind of tricky and can consume a lot of time for example for
the domain new is you have to visit a specific p uh page for the SSL certificate specific page headers security. uh txt present they are all specific web pages that you have to visit this platform with just a single click can give you a good overview a good mind map of the website that you are trying to ethically attack as you can see I took besides Pristina as uh an example and you can see a lot of useful information that can be turned into a weapon maybe later or can be used when you're testing a website ethically sockman tracer uh usually when uh police officers or private investigators have a single name they do not know anything about the
person they go after uh the social media Tracer is a platform on it's not a platform it's actually a tool that is available for download on GitHub it is free Stockman by the way just to clarify is social media intelligence it refers to the intelligence publicly data available on the social media with just a sing string you'll be able to automatically get a lot of information where is that user present on social media I took an example as my my first name for example I only said kab I want to know where that name is available but a private investigator would actually Trace down hunt more information with the username as you can see this tool within
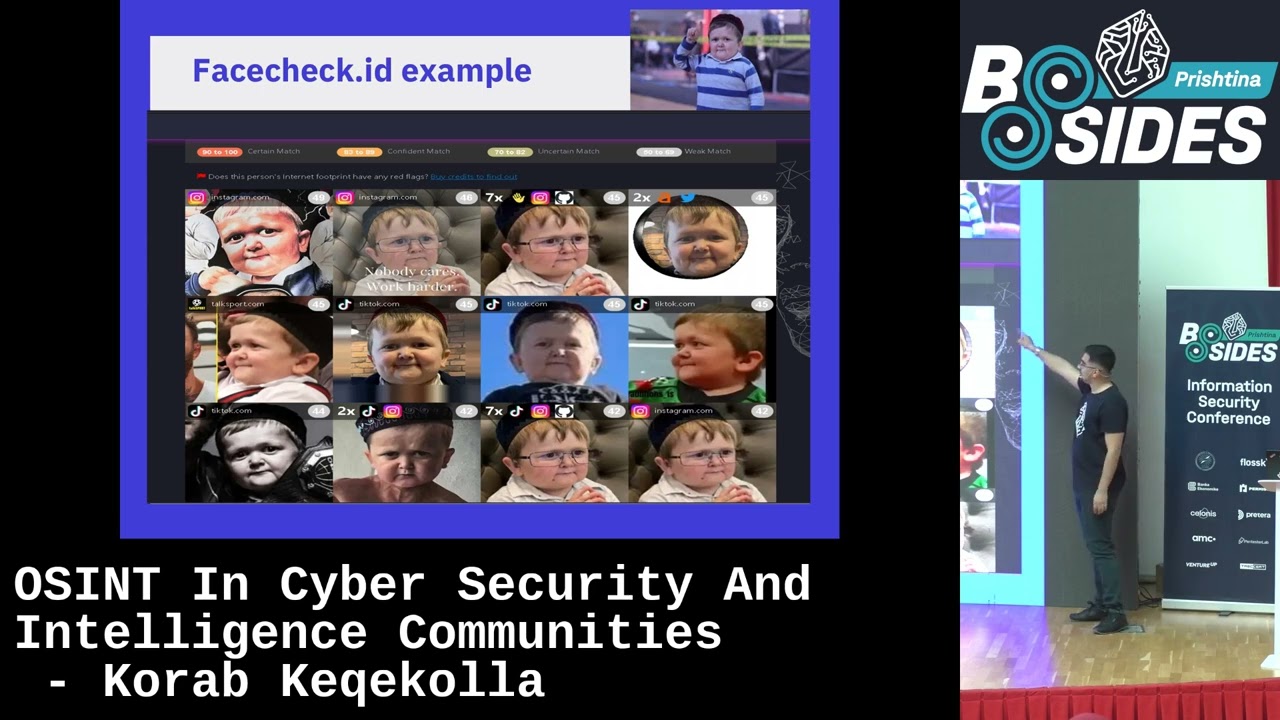
a few seconds can check 107 75 sites even more and you'll be able to know where is that username available go there and hunt down for more information for your specific Target face check ID the name says it all face check ID this platform is powered by Ai and it is pretty interesting when I first saw that even as a cyber security professional I was kind of kind of surprised because the fiction movies that we saw When We Were Young younger are turning into reality uh let's take a police example over this one a spy that is not obviously from our country comes and all we have is a single picture how to find out who's that guy
this platform helps us all you have to do is upload it and you can uh see that there are checks on social media sex offenders smug shot scammers videos news blogs everywhere what when that picture of that person was let's say present it gives you back the results for free even though this platform is turning onto a premium it gives you a free uh a couple of free shots and after that you have to pay but it's easy just open a new account uh so uh I did I did not want to take anyone else as an example or a specific person so the famous hasbullah I took his picture uploaded it as as you can see
there are links and the other social media where that picture is present you can see that uh you have numbers over there 40 60 70 that is the the the uh ratio of the tool being uh let's say true to avoid false positives test it I invite you all to test this platform test your face if your face comes up if your social media post come up you have an option to request a removal so uh if you are present on here don't be afraid you'll be able to get yourself off spy talks spy talks unfortunately is not really popular and available in Europe but the Spy talks platform is able to find people by just
giving out a single name a phone number or an email it's for free of course it has some premium options premium data that is linked to their third party vendors but in general it's for free it works awesome on US citizens in the European uh side not as much as accurate but sometimes when you receive a call from an unknown number located in us your best friend is here to solve that mystery I could not get a phone number to demonstrate so you'll be able only to see this Slide tinai the reverse image searching is very popular nowadays and the thy is one of my favorites when um the host of bides posted the the a picture of the object
that we're currently hosting this event I was thinking what if someone in the other side of the world who does not know what is besides who does not know where is Kosovo or where is Kosovo located had access to that picture and with the help of the T ey all you had to do is to upload the picture and if that picture is available somewhere somewhere else on the internet you'll be able to find it for example you can see that there's an article from a local newspaper uh and it gives you information where is it LO located and for what is used by by clicking on that first link you'll be able to know that this is some
kind of Library uh and you'll have good information you can upload a lot of uh pictures of objects Etc and tiai does not store your data of what you're searching dark web open source intelligence I could not uh present publicly the dark web tools that are free to use because the these tools can be uh weaponized and can be turned into let's say something not good for the community and I took the uni- pr. Ado domain just to classify I am aware and I am informed that some student already reported this issue and the whole system is now requesting some kind of forcefully password change so just to clarify everything that you will be about to see
is probably outdated with the use of Open Source intelligence tools all free of they are all free and a little bit bit of magic I was able to get uh accounts with this domain have them clear text uh even professors students etc etc but this probably is outdated and solved by the uh University weaponizing information versus weaponizing information when when it comes to ENT it is pretty difficult to to separate the the good from the evil because every single information that can be used for good on the other side can be used for bad weaponizing information hackers do weaponize information if they access dark web also they do have your password most of us have a problem with
credential overlap or let's say password reuse the same password maybe will be on the other social media or the other account that will be able to find via the Tracer tool the social media uh intelligence tool on the other hand weaponizing information for good is a good thing why police can use that to Catch a Criminal for our safety there are a lot of communities that use alen for good for example there is a community community Trace labs they gather they they make CTF parties and find missing people they try to find missing people and they're very very good at at at their job so this is uh let's say a topic that can go on and on
but at the end of the day is weaponizing information versus weaponizing information at at the end of the day the the police officer and the thief they both have guns but the the the one uses it for good the other uses it for bad any
questions thanks Coro that was very good presentation I'm still not getting used to you know you know like getting away from the mic from the speaker do we have any pres uh any question yeah I give me a
second thanks for presentation C so my question is because I was seeing a lot of uh online tools do you have any recommendation for operation security because for example if I want to have to find the face of Arana or whatever so if I upload his file it's kind of personal data so do you have any recommendation when we are doing end which is linked with operational security so first to not be identified and also to not leak data because who knows maybe that aome platform is owned by AP or hostile State yeah thank you that's that's that's a great question uh as I said for the face check ID it is controlled and uh they do
have some sort of compliance on specific uh Frameworks and they're not allowed to share that data they are allowed to uh manipulate for their AI purposes I know it is tricky because when we say AI purposes we don't know where the data is going but if you are able to find yourself or your friend on that platform you'll be able to remove it as for your question if I want to find Aran sorry for taking you as an example but if I want to find Aran uh I'll I'll take the the most simple example that the uh that we can all we need is to have a picture of Aran that is publicly available data
on aran's social media accounts or maybe a picture of Aran without uh his name or he him being tacked and open Google Images upload if Aran was somewhere in the Google ranked you'll be able to find Arian I hope I answered your question if if you want to discuss further feel free also not only you but everyone who wants to get involved on awesome projects feel free to reach me out on LinkedIn great thank you do we have any other question thanks very much that was great presentation