Gone Phishing: Why Do We Take The Bait?

Show transcript [en]
hi guys um Welcome to our talk uh so it's called gun fishing why do we take the bait um so I'm rafy um I am the President of cyber women at War uh I'm currently a second year cyber security student at the University of war and yeah uh I'm Ranon I've just finished my final year doing cyber security and forensic Computing at the University of Portsmouth I was the president of the cyberwoman Portsmouth Branch I am now the northern and southern branch manager for the cyberwoman group cic all right so our talk today is going to explore the concepts and psychology behind fishing campaigns as well as the impact of increasing the diversity of the cyber security industry and how that
can have an impact on the unintentional Insider threats thank you so the tactics used in fishing campaigns are beginning to Pivot um egress reported that the use of attachment based payloads um detected by their egress defend has gone down from um 72.7% in 2021 to only 35.7 in the first quarter of 2024 however QR fishing also known as quing has skyrocketed making up 1.4% of email fishing payloads in 2021 and it has jumped to 12.4% in 2022 continuing at 10.8% in the first quarter of 2024 there's also been a rise in the number of payload pay loadless attacks that rely solely on social engineering so traditionally the focus of cyber security is p is placed on
technical defenses however to defend against fishing an understanding of human psychology is required the ability to recognize tactics designed to manipulate emotions and cognitive biases is key to developing training and awareness so fishing exploits are innate tendencies that can override rational thought such as trust curiosity fear and a sense of urgency so take an email that creates a sense of urgency or fear it can prompt the recipient to act quickly without rational thought the psychological principle of trust highlights that as humans we tend to lower our guard when we believe we are dealing with a reputable organization so for example this could be your bank or a service provider that you have an account with this can be
further exploited through the use of personal information to make this email appear credible another common tactic used by Fishers is the manipulation of the principle of authority with Fishers posing as figures of authority such as senior exacts and law enforcement this leverages the human tendency to comply with requests from Authority without question so we will not second guess these emails um straight off so the susceptibility of individuals to fishing attacks is often Ed incognitive bias these biases are an inherent way of thinking that can skew judgment and decision- making one such bias is overconfident where individuals believe they are less likely to bece be deceived or that they are more capable of identifying fishing attacks this then
leads to a lower guard and thus the increased likelihood of falling victim another common VI bias that can affect the likelihood of falling for fishing attacks is the confirmation bias this is where we give weight to information or scenarios that confirm conform to existing beliefs or expectations context and timing are other key features that can influence the success of fishing attempts so stressful situations can impair judgment and critical thinking making individuals more vulnerable to deception when stressed the ability to meticulously analyze a situation diminishes thus Fishers uh May time their campaigns to coincide with were periods where individuals may feel tired and the mental resources depleted such as at the end of the day a
period of rest or during a situation that the company is undergoing that may put the employees under stress social proof is the psych psychological phenomenon of individuals copying the actions of others in an attempt to undertake behavior in a given situation so for this um attackers can create a full sense of security and legitimacy by claiming that others within your organization have complied with their requests the psychological sophistication of fishing attacks begs the question how do we Safeguard against them and an enemy that understands us so well education and awareness are the first steps and an understanding of the psychology of social engineering and the tactics I've described should be used in the development of education and
awareness to foster a healthy sense of skepticism and caution as the fine line between the real world and the digital world continues to blur so does the line between trust and deception the owners is on us to remain Vigilant to question the too good to be true and to foster a culture of cyber security awareness that can withstand the psychological onslaught of Social [Music] Engineering also don't scan Q codes that you don't know where they're coming from um I don't know if anybody actually D to scan that Q code but I trust you and I did yeah if you did or didn't trust it it was just going to the cyberwoman groups page so there was no
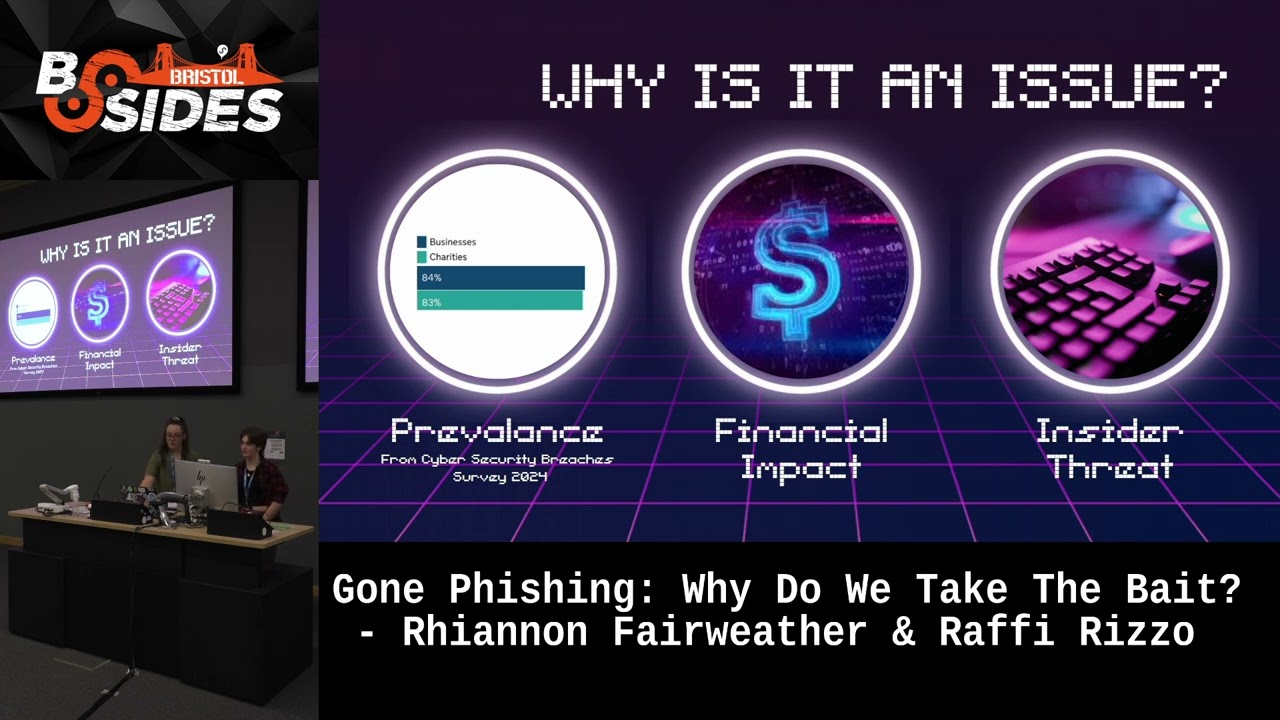
reason to actually distrust that one but yeah right um okay so as detailed in the cyber security breaches survey 2024 84% of businesses and 83% of Charities have fallen victim to a fishing attack between April 2023 and April 2024 so you can see the diagram here with it this isn't the entire diagram so if you do want to see all of the stats do go and check out that report it is very interesting um so for businesses the average cost of a breach was £ 1,25 which Rises up to about 10,830 for medium to large businesses which are categorized as companies with over 50 employees uh so however money is not the only way in which fishing taxs affect
businesses threat actors can utilize fishing to gain access to business networks through means such as credential harvesting which allows them to continue with their attack by attempting to laterally move through the network um so Cloud estimates that about 70% of cyber attacks actually start by exploiting uh employees through a successful fishing attack primarily through the use of disinformation commonly found in fishing emails so governmental organizations are most at risk with with 18% of organizations who fall victim to a fishing attack uh in 2021 to the 2022 period belonging to the government uh so the next highest victims uh proportionally were tied between science and education healthc care and Manufacturing and Industry with all three categories representing about
8% of victims each so one way that fishing attacks uh can negatively affect a business is through the use of um use of internal and adversary uh internal threats actors sorry I can't read my own handwriting there and adversary in the- Middle attacks uh so a third actor might send a spear fishing email to collect um to select employees so that if a business so if an employee falls for the fishing attacks the threat actor can gain access to the business Network through their accounts so as well as the malicious attachments uh mentioned earlier a threat actor can encourage users to click a link that directs them to a reverse proxy web page that clones
a reputable source and bypasses two Factor authentication to gain credentials so these credentials can then be used to by the threat actor to gain access to an organization's Network and further their attack so inside of threats can also be created due to an individual within the organization by using the Privileges that they gain whilst working for the company to inflict some damage to said company so uh the average cost of an Insider threat was about 700 $1,500 which primarily is spent on containing the effect of that attack so however uh the threat of an attack due to inside a threat uh not being removed soon as according to the 2023 cost of index uh Insider risks Global report the
threat the number of Insider threat attacks is increasing one reason that fishing attacks um are so prevalent is that they can Target anyone so generally it does take about 16 hours on average to craft a successful fishing email however the use of AI is drastically decreasing that time so these AI generated fishing emails can uh receive a lower click rate on average than emails solely created by humans uh but emails that are first drafted by AI then edited by humans received about a similar click-through rate um to the ones crafted solely by humans um according to a study done by academics in the US and obviously saves them a lot of time in the long run so
yeah uh one of the main ways to mitigate successful fishing attacks and the risks that they are associated with is to regularly train employees on fishing attacks so the training should cover the different types of fishing attacks as well as the different methods that an actor a threat actor might use in an attack such as time pressure so another important factor to include in training is to include a designated system that employees can report attempted fishing attacks to um in a business setting or sign them to the UK government page which has relevant links there so uh another way to support the fishing attack uh education program is through the use of educational simulations which
mimic realistic attacks so these simulations uh should be implemented before and after the training course so that the pre-training um results can act as an almost Benchmark to ensure that the training was actually effective however it is important that this education is not limited to the own to people who are working in a corporate setting and that a good level of cyber education is given to the vast majority of the public so
yeah so last month cyber women at Portsmouth ran an awareness competition for schools um so we set out with the aim to understand the knowledge and the understanding of fishing techniques and the mitigations that peoples at school have um whil also encouraging them to research and develop this awareness further so on the screen you will see our two winning um posters who actually haven't been told they've won yet so this is the first time they've come out they're finding out later today um so these are two winning posters that came out from school students in Portsmouth um we obviously very proud of how they've done but it did reveal that they had a basic knowledge of fishing
techniques and their mitigations however the school students lacked information surrounding fishing variations that may be more likely to impact organizations rather than individuals this kind of demonstrated that um sorry they may not hold the awareness to identify more complex fishing techniques that may be aimed at their schools or future universities and businesses they were going to be working in so it highlighted the need to increase the detail of fishing education ensuring it covers emerging techniques alongside the traditional within the education system however careful um consideration would need to be taken to ensure that this education and awareness that we are creating within the schools does not create the overconfidence bias mentioned previously we don't want to
create a Next Generation who think they can all identify fishing emails 100% of the time um because then we go back to the whole right at the very start so the prevalence of um fishing attacks within organizations highlights that education awareness is not just needed within schools but at all stages of an individual's career as rafy said the fishing education should be tailored to the audience um as the type of attacks encounted will vary depending on the industry job role and perceived technical literacy [Music] so as the actors continue to advance their fishing techniques it's become more critical to have a broad range of perspectives and experiences to best detect protect and respond to events a
truly diverse team can approach problems from a different angle uncovering unique Solutions and identifying specific risks vulnerabilities and target with this Insight being driven by the variance in their experiences background and cultural awareness an understanding and embracing diversity within cyber security can transform our ability to understand detect and deter adversaries not just within fishing scams but in the industry as a whole if we consider women in cyber security the cyber security skills in the UK labor market 2023 reported that only 177% of the workforce identified as female this was a 5% decrease from 2022 which demonstrates that although we are increasing the number of women in cyber and the diversity as a whole we do need
to work on the retention how do we keep these people that are coming in in the industry we need more support we need more initiatives um and diversity is a powerful tool that can only be accomplished if the industry better elevates the underrepresented groups into careers and opportunities so one way to encourage more people to join the cyber security industry is through the use of the community clusters this is because people such as especially younger students and those attempting to transition from other sectors into cyber are able to see people with a similar characteristics as themselves represented within the sector and are therefore more likely to join and then stay within the sector cyberwoman group
cic was started life at Cyber women at War um back in 202 to so still relatively new um it was founded by two students Sophie Powell and Jenny MC who led a student Le initiative to promote diversion uh diversity and equality they did not expect it to go to anywhere near what it is today it was started off literally as two people running a branch um in Warick however they had so much interest from other universities students and lecturers alike that after graduating so at 20 and 21 they walked into to accountants to set up a cic um they have now in a year developed from that one branch of War to eight branches across
the UK those branches have over 50 exact members and two reps at two different universities so with the rapid growth of the cic this week it is being announced um that recent graduates and previous exacts are joining Sophie and Jenny on the board to help aid and grow this initiative so we've got few people coming on as branch managers um we've got a technical lead uh illumin committee and social media joining um to make a board of seven yes so thank you so kind of continuing on with the theme of clusters so it really does encourage people to uh especially younger students and people transitioning into the field to uh really stay in the field if they do see
people with those similar characteristics uh so I'll out of 10 people who uh were asked um in cyber security at University of War who all identified as women or non-binary uh seven people said that they were aware of cyber women at War um before coming to the university either through offer holder days open days or just social media said that they were aware of us and they had a positive impact on their decision to study cyber security uh I would say it was 11 and eight people but I decided not to count myself in that as I feel like that would be a little bit biased uh so the other three people they were not aware of us
as an organization beforehand mostly because say they didn't attend these open days or offer holder days um but having come to the University of War have said that the branch has had a positive uh impact on them um and we've talked to other branches and it seems like people are aware of us at these other universities and that is how our other branches get started up by people finding us liking the work we do and really are passionate about a similar cause to us so uh similar yeah however we are aware that we are obviously not the only group that is passionate about women's rights about making sure people feel safe and comfortable within the
industry so we wanted to just kind of highlight some of the other amazing organizations that exists and different clusters um so as this our logo is up on the top left there um these are not all of them these were I think we drafted this slide in about a minute which just shows you how many wonderful organizations there are um that exist within the cyers sphere uh that also shows why there's so many related to um making sure that women are comfortable in the thing because that is the area that we primarily work with um but there are a million others that do amazing work uh but so yeah so one of the organizations that we've worked with
previously and hope to do more work with and I'm sure you're all aware of them is the women in technology and cyberhub which uh which is ilana's Branch um she came and helped us out at our cyber um security Conference in October of 2023 so most our most recent conference and thankfully stood in very last minute for us as we had um a panelist and uh no sorry a speaker drop out very last minute so we are very thankful for them um and yeah so yeah that is just pass over so yeah um although cyberwoman groups um obviously we are called cyber women we aim to be a fully diverse and inclusive community so a number of our exact
members identify as non-binary or male we are not just open to females our our events are open to everyone so if you see one of our events School CH whether you're a school child whether you're in Industry University student feel free to come along reach out to us um you know we're always looking to work with more people and to support anybody and everybody in the community um along with all these amazing people here plus many many more in the UK um we want to work to improve that awareness um we're going out into schools so stems are very similar to us here except they focus in time on stem as a whole whereas we go in
and give workshops um mostly pretty much mainly um around cyber security and a little bit of computer science in there as well so yeah there's some amazing ones out there Steph at neuros Cyber is working very closely with us as well to make sure that we're inclusive to um anybody with a neurodiversity um and that we're not excluding anybody all right so sorry guys that was a much quicker talk than we actually anticipated it uh but yeah so yeah does anybody have any questions at all so I go to a lot of schools and I I do loot people classes teach them lck of people the cyber security I found the young women are really really
good and I I I personally find that wom these women are so capable getting into cyber security there not approach the correct way this very Mass focused very this very coding focused have you found any particular exercises that they' just excelled in that a very good question so um I'm G to speak uh primarily from a kind of War perspective I was education officer for the last year before stepping into the role of President and then give to re give her a perspective as well um a lot of the students in the kind of West Midlands areas that the University of War has interacted with um it's we found that a lot of them a lot of the students
that we interacted with really love the kind of cryptography element of it um because with the different workshops we did we we found a lot of the guys they liked the kind of AI machine learning deep learning that kind of thing but we ran a few workshops that was like a mud mystery sort of style that had a lot of cryptographic and steganographic and mor code elements to it and we found that um my these are for the most part all these students are about year eight year nine so for comparison um and a lot of the students got really involved with kind of cryptographic elements so you could see like kind of what you're saying a
lot of schools kind of focus their students on say like maths so you could see that the students were able to find that almost cross length of oh this is like uh so with the Caesar Cipher of finding that kind of logical link between how it's uh how a cipher is formed so personally I think that's kind like the links aren't almost highlighted enough between the different areas and I think that is one way to kind of get more people interested in because there are obviously the stereotypes around um the area as a whole so I think if those were highlighted then maybe we'd be able to get more people interested in yeah so we in Portsmouth had a very
similar experience to rafy um I think because schools obviously follow their curriculum um so tightly if you're in computer science it's technical you don't really get tght any of the non-technical the lockpicking kind of sides you don't get the puzzle solving section of it so that's where we've kind of come in and decided you know we want to be that one that says hey look you're not you don't have to be technical you don't have to code to come and join the industry you could go and do English at University you don't even have to go to university but you're still more than welcome there's people in the industry that look just like you who have had
Pathways similar to you um you do not have to be that technical so I think is very similar and from speaking to other branches right across the country um but it is getting those workshops out that show them there's that non-technical side to it as well um but yeah sorry just an additional point that I thought of wasy was speaking um that's also kind of one reason that we want to highlight the kind of say also the uh cyber psychology element of cyber security um and the fishing element so obviously it's a very serious threat in its own right but I know know that I've had loads of friends um who are very interested in Psychology but very much
think that oh no it's only the like only like train like um clinical only like you can be a psychologist or go into more of a specific science or like that um element of it um so that's kind of another element that we're trying to bring to students is like no you if if you love psychology but you also like um cyber or like you the idea of tech you can combine them and you can uh really be you can go into like cyber training and be the person who is championing about cyber psychology if you choose that to be your Niche so just add on to rafy there as well um we have a number
of branches that that exacts are not computer science they are not cyber security um Lester has cyber has psychology students um on their exact board who are doing exactly what rafay has just said they have done their psychology degree or they are doing their psychology degree and they have that interest in cyber and that's precisely what they want to do is come out and show people that you know that we're in cyber but we are not technical um we are here to show you how we can link psychology and how we must link psychology into our defenses we cannot defend effectively without having that psychological understanding so it's very important um and that's why kind of
we've like I say we're inclusive to everyone um as are all the many other branches up there um and clusters that are doing similar that to us again to b h if you have not interacted with cyber women before we like to Yap you get us started on a topic we will we we will talk here ear off for days um that's again one thing that we do are trying to get into I guess really the next generation's uh brains well next Generation I think they're still classified as Our Generation Um is that cyber does not exist in a vacuum so very much you need to link it to other that har is I feel like we should wrap that bit
up yes so does anybody else have any questions no cool yeah well thank you thank you for guys for coming