Gone Phishing: Why Do We Take The Bait? - Rhiannon Fairweather & Raffi Rizzo
Show transcript [en]
cool so we're just going to start off with a really quick introduction to who we are so I'm ranan I'm the northern and southern branch manager for cyberwoman group cic I'm also a very recent graduate from the University of Portsmouth um in cyber security and forensic Computing I was a virtual track semi-finalist in the Cyber 912 competition earlier this year I'm a speaker I've done a couple of these events now um I'm I was part of the creson CTF organizing team earlier this year yeah hi guys I'm rfy um so I'm the cyberwoman at War President I'm an incoming third-year cyber security student at the University of War um similar to R um I was also a cyber 912
semi-finalist except as on the uh physical track in the actual BT Tower my team also won the um award for most engaged team award um so I'm also a current AWS data center intern and yeah also a speaker so yeah so what are we going to be doing in this talk AKA talk-- help so we're planning on exploring the con human Concepts and psychology behind fishing campaigns as well as the impact of increasing diversity in the cyber security industry and what that effect what impact that can have on yeah on in unintentional Insider threats so just a little bit of a quick overview um of what fishing is so the tactics used in fishing campaigns are
pivoting um ESS reported this year that the use of attachment based payloads um detected by ESS defend has actually decreased from 72.7% in 2021 to 35.7 in the first quarter of 2024 however QR fishing also referred to as quing has absolutely skyrocketed in 2021 it made up just 1.4% of fishing email payloads in the first quarter of 2024 it made up 10.8 there's also been a rise in the number of pay payload less attacks which are solely relying on social engineering so traditionally cyber security focus is placed on technical defenses however to to defend against fishing we have to understand human psychology um the ability to recognized tactics um designed to manipulate emotions and cognitive biases um is key to developing
the effective training and awareness campaigns so fishing exploits are inate Tendencies um that override our rational thought such as trust curiosity fear or a sense of urgency um so take an email that creates a sense of urgency or fear it will prompt us to react quickly rather than cautiously you're not going to take that time to think about what you're doing you're just going to react um the principle of trust highlights that as humans we will lower our guard if we believe that we are dealing with a reputable organization or individual and this can be obviously manipulated by pretending to represent that person um I'm further exploited then through using personal information so addressing you by your name doing o
knowing who you are what you do and playing that into the email you're going to trust them far more than if it's a generic dear name um another tactic is the manipulation of the principle of authority um where they pose as authority figures such as as your senior exec or law enforcement thus leveraging the tendency to comply with requests from Authority without question if your boss says you need to do this quickly you're more likely to just go and do that quickly without checking actually where's this come from is it a genuine request from my
boss so the uh susceptibility of individuals to fishing taxs is off often rooted in certain cognitive biases so it's not always intentional it a lot of times is completely unintentional so these biases are inherent uh ways of thinking that can scoe judgment and decision-making one such bias is overconfidence so this is when people often think ah no I've done the training so many times I'll know when I can I'll know when it's a fishing email and that's give themselves more confidence and are overly well as the name suggests are overly confident in their abilities to actually identify and avoid clicking on an actual fishing email so this can then lead to a lowered guard and thus
increased likelihood of falling victim to an attack so another common bias that can affect How likely it is for an individual to fall for a fishing attack is confirmation bias so this occurs when individuals uh give more weight to information or scenarios that confirm their existing beliefs or expectations which can happen when a person surrounds themselves people are so similar to themselves or their line of thinking that they almost form like a homogeneous group um so context and timing um can also play a significant influence on the on the success of a fishing attempt as well as stressful situations which can impair judgment and critical thinking making um which like which leaves individuals more vulnerable to deception
so not UK specific but I mean for example like actually the general election that came that was recently or the US national election in November people might be trying to imitate political parties and leverage that um leverage that trust that people give to those parties to for their own gain so when strust the ability to meticulously analyze a situation diminishes and yeah similarly the timing can diminish the level of scrutiny that's applied so emails sent later in the day for example um thus Fishers May time their campaigns to coincide with periods when individuals may be tired their mental resources depleted yeah such as as I mentioned end of the day towards a period of rest or just generally around
holidays so also social proof is a psychological phenomenon where individuals tend to copy the actions of others in an attempt to undertake behavior in a given situation this can then be manipulated by attackers to create a full sense of security and legitimacy so yeah this can be utilized by these fishes by crafting an email that uh claims others have complied with the request which plays into the kind of herd mentality and inate social social nature that humans uh play in or have around this is a cow that R and I have loved laughing about whilst creating this PowerPoint as we've nicknamed it cyber cow um this psychological sophistication of fishing attacks uh begs question question how do we
Safeguard attacks against an enemy that understands us so well through like say ENT and spear fishing so education and awareness in general are the crucial First Steps so understanding the psychology of social engineering and the tactics used um by cyber criminals should be used in the development of education and awareness to foster a healthy sense of skepticism and caution um as well as the lines between as well as this the lines between the real world and the digital world are continuing to blur um so and so does the trust and deception that people place in these online resources so to do this everyone needs to remain Vigilant in their attempts to combat cyber crime and
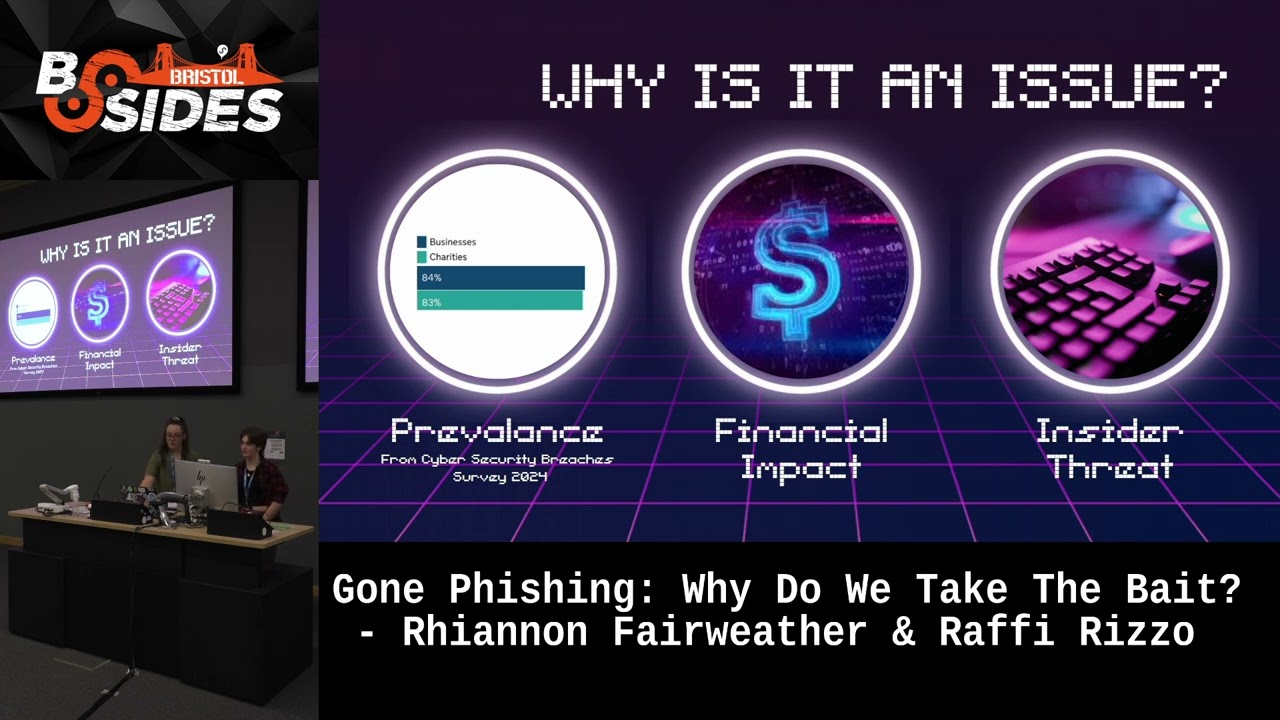
fishing attacks so again another way to do this is look out for signals that take advantage of the human brain um and question whether an offer is actually way too good to be true uh as well as making sure that you educate people early so don't wait till people are in their professional industry jobs start talking to people about it in schools yeah so we've told you what it is but why is it an issue so the Cyber breaches survey of 2024 conducted by the UK government 84% of businesses and 83% of Charities fell victim to a fishing attack between April 20123 and April 2024 for businesses that's an average cost of of a breach of £
1,25 for a medium to large business which is company's over 50 employees that RIS to 10,830 per incident obviously now money is not the only way that a fishing attack will affect your business um you know they can utilize fishing to gain access to your network through credential harvesting um and allowing them to then laterally move through your n work um cloudfare estimated that 90% of cyber attacks started by exploiting employees through a successful fishing attack primarily through the use of disinformation commonly found in those fishing emails 18% of those organizations who fell victim to a fishing attack in 2021 to 2022 belong to the government the next highest victim proportionately was tied between science
education healthare manufacturing and Industry with all three categories representing 8% so fishing attacks negatively affect a business through the use of internal threats and adversary man in the middle a lost my mouse so a threat actor may send a spear fishing email to a select employee that they might have found through ENT um to try and then gain access to the network through that individual's account we could encourage a user to click on a link that encourages them to or directs them to a reverse proxy web page that clones a rep reput I can't speak reputable one um and then bypass T Factor authentication again to gain credentials to further their exploits inside a threat it's not something when
you think about fishing that you think about commonly if you have a disgruntled employee in your company that wants to inflict damage before maybe they leave you know this is an easy way for them to do it they've got the ENT they know about the company already they don't have to go out and do that prior ENT they know everything they know your company structure they know the email addresses of the people to contact they're a trusted employee most the time the average cost from inside a threat is 715,000 and that's primarily spent on containing the effects of the attack so that's after they've done anything however that threat's not going anywhere it's not going to disappear um
the 2023 cost of Insider risk Global report actually said that the number of Insider threat attacks is increasing it's not decreasing they're not going away so how can we mitigate this so we can mitigate successful fishing attacks and the risk they're associated with by training our employees training should cover the different types of fishing we don't want to just focus on you you know you normal click on a link fishing okay we want to focus on spear fishing we want to focus on those emails that are being used to gain more information that could then lead to the attack further attacks um another important factor to include in that training is a designated system that employees can use to report
attempted fishing train them on that before they get to the point of needing to report something that is valid if they know how to use it they're not going to report it effectively so it's all well and good training them on the emails themselves but they need to know your business systems and how to manage that so we can use the fishing simulations you can create your own you can there are companies out there that do them but they need to be implemented before and after training courses so use them alongside other um means at the same time you want to be able to compare your pre-training resources and results as a benchmark to ensure that that training was effective
cuz if we are just going out and saying here is some training go do how do we know it's effective how do we know they've actually learned anything from that we don't so it's also important that this education is not limited to those in a corporate setting we've got people at home on their own devices that they might be doing work on they shouldn't but they might be train them on that as well don't limit it to those people in your office at that time quick point before going on to diversity can you put your hands up if you knew that you could report fishing emails to the government like there's a government page okay good okay good that is what I
expected at a security conference but I thought I should double check yeah so uh however the prevalence of fishing attacks uh within an organization also highlights the importance of heightened awareness and education within all stages well not only an individual's career but also the education Journey um so fishing education should be ta tailored for the target audience as uh the types of attacks encounted may vary depending on their industry job role uh and perceived technical literacy so an attack may be different for a secretary versus the chief technology officer so there is not a suitable one siiz fits or solution as many factors can be included including say neurodiversity disabilities and just cultural specific context information need to be taken
into consideration because even across say the English speaking World there are very specific culture um specific clues that yeah you might be trained over in California but it might be different in a London office U even the way people just speak casually so as threat actors continue to advance their fishing techniques it has become critical to have a broad range of perspectives and experiences to detect protect and respond to these events so a truly diverse team can approach problems from different angles um uncovering unique Solutions and identifying specific risks vulnerabilities and targets uh with this Insight being driven by the variance in their experiences uh background and cultural awareness so uh understanding and embracing this diversity within
cyber security can transform our ability to understand predict and um yeah just in general operate online so if we consider women in cyber security the cyber security skills in the UK labor market in 2023 uh report published by deit highlighted that only 177% of the Cyber Workforce identified as female so this showed a 5% decrease from 2022 um demonstrating that more work is required to ensure that the retention of these female employees within the industry stays at a good level so this is also contrast to the 29% um of workers identifying as female uh within other in digital sectors and this doesn't even address the minority of people who identify as non-binary um within the industry so diversity is a
powerful Tool uh but can only be accomplished if the industry um better elevates underrepresented groups into cyber security careers and opportunities this isn't to say oh you should specifically exclude men or exclude a certain category because that is not inclusion but uh forb suggested that one of the major barriers preventing people uh from pursuing a career in cyber security is due to the unclear idea of what a career uh in the industry actually looks like due to their lack of knowledge from the education curriculum so what's the study that Forbes did was based on Professionals in the US a similar sentiment can be assumed to be true or roughly true in the UK so uh the UK
government is aware of the need for diversity in the cyber security industry as in the 2022 National cyber security strategy um they want to aim to have a quotequote steady and diverse flow of Highly skilled people coming through our education system so they plan to do this by increasing the uptake in GCSE computer science equivalent um and equivalent um qualifications that's word sorry as well as education past that point as well as upscaling the teachers and uh providing relevant resources um up-to-date resources as well so this relates to the work that cyber groups we'll talk more about our specific work shortly does um as I know specifically in the Cyber wi at War Branch but as
well as in other branches we target students especially in the kind of year eight year n age in order to encourage them to go down the pipeline by saying hey these are the kind of jobs that you can get within the industry so outside of cyber security diversity in the workplace increases profit retention of Staff productivity and creates a general sense of belonging uh there have been studies into that as well as well so let me know if you want those so one way we can encourage more people to join the cyber security industry is through the use of community clusters you've seen and heard a few of them the last couple of days we've all been here floating
around and this is because people especially younger students and those that are looking to transition from other sectors into cyber security are able to see people that look like themselves with similar characteristics and similar background represented within the sector they want to join therefore they're also more likely to stay in the industry for longer if you've got that sense of community if you know who you're with you are more likely to remain so so cyberwoman group cic uh started life as cyberwoman in war in 2022 founded by Sophie and Jenny who are sat right there um as a student LED initiative to promote diversity and equality in cyber security after graduating they had so many people coming to them saying how
can we continue this that they founded cyberwoman group cic and in L than a year we've developed from one branch to eight I'm grabbing with over 50 exact and three representatives and seven internal team members so the rapid growth showed there was a need for this in the industry there was a place for students at University level to join industry to make those links that they weren't making through their university courses so the rapid growth obviously they went from one branch to eight they are two people they work 9 to five um they've taken very recently five new graduates myself being one of them and we're previous EXA to join them to age in the branch management social media
technical management and the development of an alumni community so our branches are purely student L they sit outside of their universities they are not societies they are initiatives that work with their universities they lead their own events as Sophie always says as long as it's moral ethical and legal they can do what they want they they hold national conferences they go into schools and they give workshops they run ctfs they give careers presentations think of it they've probably done it or are in the pipeline of doing it um there's a lot coming up in the next few months quite scarily but they're there they bridge that Gap they bring the students who are mainly first years when
they join to meet those people in Industry actually if they were to connect with them on LinkedIn they might get all that person is really scary I don't know them how am I ever going to meet them they meet them in their first year of University they work with them in their first year of University that gives them the basis to go out into their careers say I know this person or if they're stuck in a module and they can't get the help or the right advice that they need through their University or they want extra advice they've got industry professionals they can go to and ask also to add on to that a little bit
the so women at War Branch when it was initially founded was five people it was Sophie Jenny no six people I'm sorry I I don't even know who I missed off plus four people in the year below uh all of whom are have kind of gone on to helping with the internal team really um we are now a branch of 14 and most likely increasing we are the biggest Branch but it really shows that in two years there's been a lot of uptake in it and one of those first events was actually Sophie speaking at my Year's offer hole today and yeah so there was definitely a uptake in this kind of field but uh so
one way that may encourage people to join the cyber security industry is through the use of these Community clusters uh this is because yeah as R talked about um it really is beneficial for people to see people like them in the industry it makes that jump into cyber security a little less scary um especially if people have gone to an old girl school going into a very male dominated industry seeing a well multiple groups like aimed at women it makes it a lot nicer of a sector to go into it's like okay there are people like me and really Aid in them comforting them um so yeah these are well we we recognize that we aren't the
only group trying to make people feel more comfortable and more safe in this community of cyber security professionals so we just want to give a quick shout out to everybody on the screen plus so so so many more people we not an exhaustive list in any way shape or form I think we drafted this in maybe a minute or two which just shows you how many like amazing groups there are I mean even we've got witch and security Queens here today so it's one of those was like not scary at all um yeah so thinking about cyber women groups uh cic specifically it like our one of our purposes I guess is to really help
bridge the gap between Secondary School students to University students to Industry professionals so uh yeah actually talking within the speaking within the war Branch uh what was it sorry no good H yeah thank you um seven out of 10 people who went asked said they knew actually about cyber women at work before they started their degree um and said that actually made them feel more comfortable in coming to the coming to his cyber security degree um the other three didn't know about it but was glad it existed um hopefully there's no negative feedback that I know of but you know maybe it might be a bit scary considering I'm also part of the exact uh the other so similar feedback has
been given through the talking with cyber women at Birmingham Branch as well um several of whom also interacted with the war clot before yeah so yeah now on to our little demo and now we kindly ask Chris to





