Attacking JSON Web Tokens
Show transcript [en]
well next up we are very privileged to have Lois who is the man behind pentester lab a bit of an icon in Australia and around the world and his talk is on j-1 attacking JSON web token so let's give Louis a welcome reception Hey can people hear me in the back yeah okay so hello everyone my name is Louis and I'm going to talk about GWT this is my son cloud so last time I did bat talk in New Zealand an older version of our talk I messed up the first demo and my laptop freezed in the middle of the talk so I'm hoping to do a bit better today and so - about myself I'm a security engineer -
pen test code review security architect a bit of everything Yannick so I'm not a cryptographer not at all like I try to read the switch post paper this morning in the plane and yeah and I run this website named pentas terabyte basically teach people web hacking and when you teach what people think when you teach people web hacking you want good examples and JWT are amazing for that if you want to teach people applied crypto because again I'm not a cryptographer I really enjoy applied crypto and on the left corner you can see my probably like biggest achievement in life I made the CBO stickers right I got some if you want he's losing it yeah and also yeah a pen
tester lab also has like a free a lot of free content so check it out so we're using GWT so every day when you're browsing the web you Ferb is using GWT and you don't know about it because everything is going like through cookies or for HTTP header or parameters and people music a lot if they're using both or four sessions or as well to manage truss I want to sign something and to someone and make sure that no one tampered with it I'm using GWT and mostly because as well be cool so I've only one want to use something cool people using it as well if they want to be stateless so they don't want to have
a pool of session across multiple systems or a pool of session across multiple data centers so by using signed session / JWT to do this so we don't have to like share something like NFS or just one database or something ugly like that alright should use wasting so some acronyms so josée for javascript objects signing an encryption that's the group who is working on putting together or the RFC to say like oh that's all the token should be but how things should work blah blah blah dot token that's what people call them GWT or jot just an encryption JSON web encryption DW e is something I'm not going to talk about but also like a lot
of interesting thing to look at and today I'm gonna spend my time on JSON web signature so jws so basically just sign token we're gonna talk as well about jwk so just a way to represent a key so just like JSON version of a public key or private key whatever you want to put in and jwa are the algorithm but you can use for JW s or JW e so crypto 101 so encryption gives you confidentiality signature gives you integrity and people get confused with both a thing like okay if I include something people cannot see this information so they're not they cannot tamper with it it's actually not true you can modify the data without
knowing what's inside and get over results so when you're signing things what you want what when you want integrity what you do is you sign so multiple ways of signing the most common way if you're poisoned will play with payment gateway is using H mark so it's basically a construction around - like md5 and it's a chauffeur hash so you avoid attacks like length extension and a lot of ways to use a symmetric crypto with public private key so this way not everyone has a secret so if you're using a secret with a CH mark the person signing or the system signing needs to have the key because we're signing right but the person getting the message and
verifying the message need also to have the secret because otherwise they can't compute the same H mark and they can't tell ok about the same thing if you use seeing a symmetric crypto the person signing just needs a private key we also get the public key for free but we get the per get the private key and a sign on the receiving end the person verifying of the system verifying the C as a signature only needs the public key so if you have done a bit of security before that sounds like a lot better right anyway so the JWT format so the good thing with readability and probably why people like it a lot it's very very
simple or it looks very very simple so first a bit of Jason so you probably familiar with JSON you got like okay this is like a string this is like my first name my last name you can have arrays you can add a hash and you can put whatever you want inside it I was really inspired when I put that slide together as you can probably tell that's actually Silvio's address no so then you got three parts so that's why it's really easy the header the payload and the signature and the signature is here to make sure you didn't tamper with the payload and the header very separated by a dot so this way it's easy when you
receive a token to split it you don't have like okay I need like five bites when five bites you just like split on the dots and it's basically base64 encoded Jason so basically for kind of its URL size basic stephane coding without padding which is very similar to basics before but you will see it's very some little details and the signature is also basically fun coded but it's not Jason so that's why your token kind of looks like a YJ blah blah blah blah a YJ blah blah blah dot signature so because it's the basics t4 of a curly bracket and opening curly bracket with a double code that gives you a YJ so really easy to spot on the
wire right you see like a YJ daraa dot a YJ data a dot it's most likely a JWT so I was talking about basically for you are safe encoding without padding the thing is that people use GWT for web stuff a lot and if you do web you know and you do like some GWT or web power cool you know but some characters really break payloads like a plus because a plus is a space encoded right and a slash or so can break like a tough for example because that's the way you delimit paths in a file system so GWT or real safe basically see for you all safe encoding without padding get rid of all
these characters that may mess up your GWT and also remove the equals for the same reason because that's the way to split between a name and a value when you have like HTTP parameters if you want to have fun you can read the errors at the bottom so the header contains the algorithm attribute so but going to tell the person verifying the token this is all you need to verify my token and here for example we're using HS 256 to say it's H mark we sha 256 it also contains a type here to select ok this is actually a JSON web sign ature so you have a little lot of different algorithm but are supported because JWT got
created at the time where people thought like crypto agility is pretty cool we're going to do something and we can rotate and change algorithm and stuff like that which now Noah days it's like a terrible idea if you designing system you don't want to be crypto agile because that's how TL has got done many many time anyway back to generality so this report a lot so H much air sa an empty curve eros a weave so I told you I'm not a cryptographer MFG one partying something so just like weird era say oh but eres a weave we're parting but same idea private public key so why would you want multiple algorithm or why would
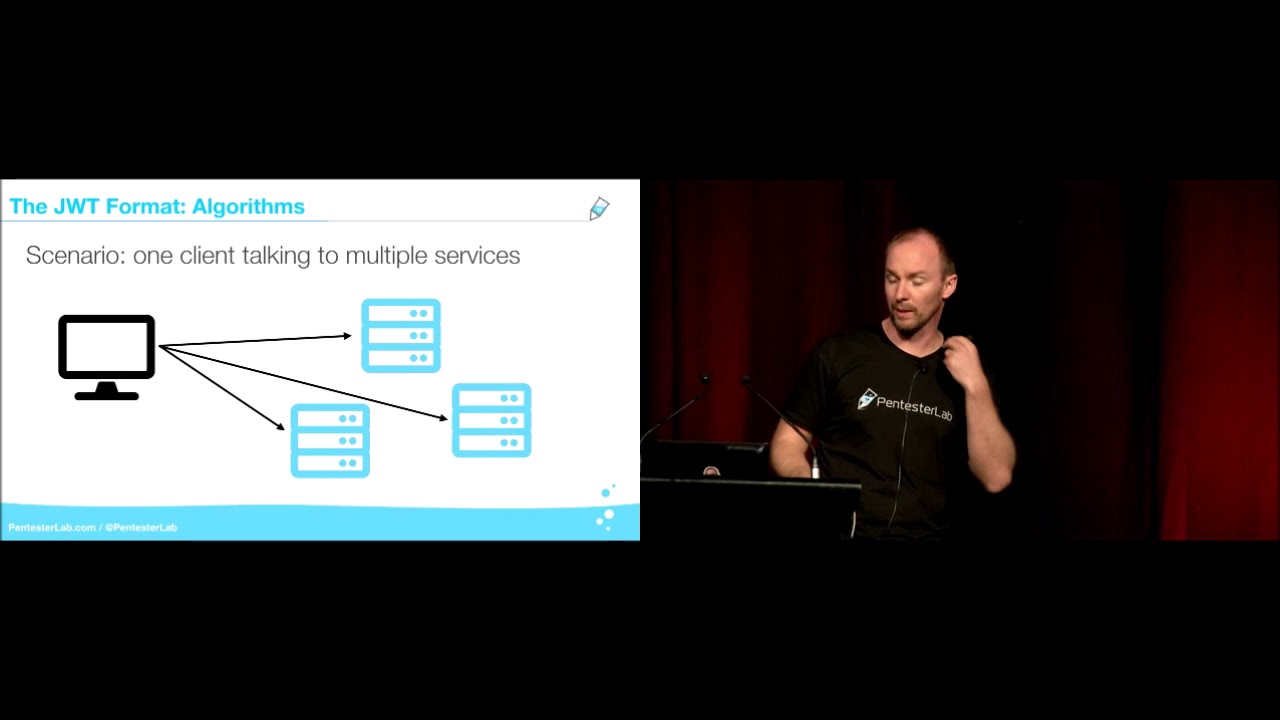
just like stick to H much because ethnic is good it's fast and it works imagine you have like one client and you're talking to multiple micro-services pretty common nowadays so if you're using an H mark every I need to learn how to use that thing hey every system need to have the secret to verify the token otherwise we're just going to say like okay I got a token but I can't verify it because I don't have the secret and you signing for nothing so everyone got their secret it's good until CEO comes in and pop one of the your system then one of the secret is compromised but since they all the same or your
secret are compromised so you back to zero you don't know which one of your system got popped you know but one is because your secret is compromised but you don't know which one that's why you probably want to use public and private key so what you can do is something pretty simple let's say not say stupid it's put the public and the private key everywhere but you back to bad scenario so you're not learning you're not gaining anything security wise if you're a bit smaller what you can do is just a being like of some micro services or API that are trusted like your authentication for example and only those services can issue tokens because
they are the only one with the private key and everyone else can verify the signature because we got the public key and if one of the system got popped and you lock it's not the one with the private key you don't really care people have a shell in your in your network at least we didn't get the private key so and it's a good thing as well is that you can even do that in the browser so if you need to vary use a token inside your browser to do for example a redirect you can you verify the signature in the browser with the public key because it's public and why aren't anyone everyone doing that so primary
that if you had like a really big scale RSA or elliptic curve is a lot more resource intensive and a lot bigger than just H mark and a lot more complex to deploy so that's why people tend to keep using H mark sorry so we did the header now we're moving to the payload so basically the payload is very 64 JSON of whatever you want to put you want to put a username you want to put rolls you want to put anything really like you can throw anything you want in the payload except you have reserved keyword called claims for example expiry so when the token is going to expired or issue out when the token was issued and you got
like few of those for example the subject audience GTI claim ID so it's just a unique ID per token so if you want to do for example ante replay people use GTI for that because it's unique per token why would people use expiry versus issue ad so imagine you have like a lot of micro services and some of them are like synchronous and you want them to trust the token for two hours you can use expiry but when you got this really slow micro service but process like a token every two days for this one you can say okay use issue at and only trusted token for one week and so this way you have this balance and
you can because otherwise you're I think micro services will I use the token and they already be expired so they don't use them so that's why it makes sense to use a bit of both so how do you create a token you take the header your JSON header your basically for encode it you take payload ubay 64 encoded then you can concatenate with a dot the header and the payload then you sign the header plus the payload that's important you don't just you could sign on either payload but you actually sign both when you buy 64 encodes the signature and you append the signature with a dot at the end and you got these three parts again
header payload signature how do you verify token so you split it into three parts you by 64 decode each part when you pass the JSON of the header and the payload and then from that you can retrieve the algorithm from the header then you can verify the signature so if you have an attacker mindset you can tell already but that's a lot of things you're doing but can go wrong before you even verify the signature so you're like basically for decoding data you just on passing data then you're retrieving data from bad Jason and then finally you verify the signature and last step you verify the claims to make sure like for example as a token didn't expire so yeah
that's a lot what can go wrong and it does keep in mind as well but multiple system can issue tokens like you can iraq if you testing like doing bug bounty or pen testing it's not because one of the token that got issued but one of the micro services is saying but we're all going to be signed so we need to make sure that every single micro servicing issuing token issues the right kind of token and token can be used as well or consumed by multiple systems so we need to test all this combination of issuer versus verify or slash user and all this system can use different libraries not Java Python Ruby so we can
have different behavior and we can also use different version of the same library so it's a lot of testing when you want to test your ability so when you're attacking GWT is the main idea is to bypass or jws to be precise it's the main ID is to bypass the signature so for example you're logged in as test and you want to become admin so you need to find a way to go around the signature mechanism it's really cool actually with the to screen because people don't look at me so sorry so the first mistake people are making is not verifying the signature so for example in JavaScript you have two methods to verify in the JSON web token
the default the most use JavaScript library you have two method you have decode and verify and they could one just get the data out whereas a verify actually checks the signature and a lot of people make that mistake they use the wrong one or they just do like a bit of the code of debugging put the wrong one and then forget to put back the right one and it's basically like you have signed token but you don't verify the signature so it's just basically you sending basically four encoded JSON string so how do you exploit that you get a token you temp you decode and temper the payload with the payload and when you send but token back with the
nuke we've the new data inside the payload and for example you can go from test to admin in just like to base 64 comment so as part of the algorithm I quickly went through like what was available and I didn't talk about this one the non algorithm so we have an algorithm that say like okay instead of using H mark RSA elliptic curve blah-blah-blah-blah-blah just use none don't sign the token and now in 2019 when you look at other what were they thinking but it's actually pretty common like it was the case in a tls/ssl at the time at the same time with null cipher so it's just a way to make things easy to debug and I think it was like three
four years ago but someone realized but a lot of implementation allowed this and you could just bypass or the sign token just using the non algorithm so what do you do you get two token you decode the header and change algorithm to none or non depending on those beside implementation you decode and change as a payload then you keep or remove the signature depending on the server side as well as the library sometime you need to remove the signature sometime you need to keep it so you need to try a bit of everything and you just in so we're gonna try for the demo I messed up last time so I got just a simple website I'm gonna register
Silvio what's your password see view again let's see plop okay so I'm logged in as Silvio now I'm gonna get a terminal okay people can see that okay so I'm gonna get it's very bright here I'm gonna end up with a tan so I get my token I copy it in VR I'm gonna okay so I didn't I it's jws algorithm HS 256 so I'm gonna copy that
what
and I got my new header and yep and then I gonna go to the end and I'm gonna keep everything so I'm not gonna modify the payload just yet because you want to try when you're doing this kind of thing you can you want to try one thing at a time so basically I'm just doing an HTTP request which curl because you can't really trust browsers to do the right thing so I'm currently logged in as Sylvio no one care because I logged in as Silvia but as soon as I and you can see that I remove the signature as well so now the token is not we are not verifying the integrity of the token so I'm going to
basically for decode the payload that's a bit better for people our thing and I'm gonna do the same thing I'm gonna D say okay now I want to be an mean oh I missed one thing and okay I'm good so if you can see here it's not it doesn't look really like JSON here right after the 44 it's because of the URL safe base64 encoding without padding if I add the padding so curly braket happier here because yeah it's like so basically for decoding just eat about part of the dollar so I'm gonna keep that part I'm gonna get back to my curl and hopefully
see you are currently logged in as n means the key for its kind of CTF II so you got a key when you solve an exercise but it's Sylvia Sylvia Sylvia I really like Sylvia as you can for retail already say about the one I messed up last time poof the prom is that it's actually the easiest one so another one is week secret so especially when you're using so you can have week every psyche but it's pretty hard to mess up like every say key generation those days hopefully anyway so the thing is that the signature of the secret is the secret of the signature relies on the strength of the secret if your secret is like five
characters it's going to be pretty easy to crack it and you can crack it offline with just one valid token so the good thing is if you want to attack like an application that you use JWT you get one token then you get that token and you try to crack it for six months with ash cut so you made one request and like legit requests right then six months later you get the secret and hopefully no one change it and you do another request and you now instead of being logged in as test you logged in as admin and you just made two requests and they both look legit because you don't you're not do it forcing you are you brute
forcing but offline you're not attacking the server and like sending requests and requesting you okay so it's really hard to detect so and basically as people say no logs no crime that's when you can tell that people are from lower enforcement in the room yeah can tell when CB in Canberra where more people here so basically and it happens a lot like for example that's just one kind of like framework around like GWT REST API Express and that's always said the JWT we just like okay if we are in production we're going to use the environment variable Jade ability underscore secret if we are not in production mode we're just gonna use secret and yeah
that's probably a terrible idea because someone makes a typo and just type like poor diction into the production and you in a lot of trouble so yeah you really want to use strong secret for that so exploitation you get to token you Britt was a secret offline until you get the same signature and then once you get this H Mac to sign the secret you can just create whatever durability you want you just signs of payload and send back to the application and you're in now we're going to go to the funny stuff algorithm confusion so the algorithm or the sender control algorithm used so when I create a JWT and I send it to
like an application me as a malicious person I'm gonna pick what algorithm is used because I'm creating the gel ability right so I can say like okay I'm you're gonna use none in the application you select Louie it's not 2018 anymore known is not supported anymore so we need to do better than that and it's application use H not for example we're going to check my token using the secret if we're using error say they're going to check but my check my token using the public key because you verify with a public key now if you try to look at the source code of this verification of this track it's going to say okay get the algorithm and verify
we've the public key thinking get so algorithm is going to return error say but what happens if gets algorithm return H much the application we select okay I'm going to verify the token the signature weaves a public key using H match and it's a public is public so you can put onto the get it so basically going to sign a token with the public key and manage to get through so you tell basically you try to talk and it has a receiver it's an H magnet an arrest service time not aracite air s 256 this time and since in the source code of the server application based like verifies a token with a private key thinking it's
RSA but you sending this is actually H mark you can get through so how to get the public key so that's what is a hardest part it may be available in JavaScript it may be publicly available for example in a mobile client you just reverse some of our client because they may need to verify tokens so we just we can get the public key or maybe in the documentation as well few good places to get it anyway we get the public key what we going to do is we get two tokens sign with RSA and we have access to the public key we're going to decode the header and change the algorithm to errors 256 and
when we're going to tamper with the payload and we're going to assign the token with H mark and the public key so I got another web app so you trust me I'm Ken register log in but I think the interesting part is not here
so I got my token I just removed the signature because I don't care about that part and I got my public key so just do two simple things so on one really important thing is I don't copy paste the public eye just like reads a file so I don't make any like changes with new lines and things like that and I say like okay I'm gonna say set the algorithm from eres a 2h mark by because I'm changing erase 256 to HS 256 then I'm going to change my username from test to admin and then what I'm gonna do is just do an H knock of the data so my new header and my new payload
and I'm gonna sign that we've the public key so if I again but value I remove the records just in case
so again using curl because hacking has to be visual visual localhost 18 if you wanna thank ya and you're currently logged in as I mean and the key is Kylie Kylie Kylie C okay so again as someone we really enjoy like applied crypto I find but a really really cool bug because it's like you don't need to be like hardcore in crypto to understand like what the problem is and why it works and how fun it is now again we've just ability people like to be crypto agile so some other this great idea to say like ah instead of our code our coding the key we're gonna use key ID so we can support multiple keys so
basically it's a header in so it's an attribute in the header of the page of the durability but say it's like okay you can retrieve that key from for example just a string so you can use that as a path on the filesystem you can use that as a string to match in a database and the good thing is that since you need the key to verify the token you're gonna do you're gonna if potentially with key IDs injectable you can probably put onto the exploit the bug in that retrieval of the key to bypass authentication or even get a shell so we get a sign token containing a key ID parameter we decode the header
and change a key ID for example to an SQL injection payload with ten pair with the payload and what we're going to do is instead of using the SQL injection to retrieve data from the database because that's pretty boring and everyone is doing that we're going to use this current injection to return a value that is predictable and that is going to be used to sign the token so [Music] so again
so but even simpler okay it's in taxi like I like anyway so here the idea is okay we got an heiress H mark token and we just sign it we've the value AAA and why we using a a because that's going to be the return value of osq an injection so what is happening is the application gets the token pass the header gets a key ID use that key ID to retrieve the key to verify the token but as part of getting that key we do an SQL injection and we say like okay we're going to return a AAA and since that's going to be used as the key to verify the token we don't assign the token with exactly
the same key again we get to token so this time I did not remove or say course
okay
yep and yeah we are currently logged in as admin because we put our username as an mean and the keys against Silvio because I'm someone with a lot of inspiration so just basically yeah since we have an SQL injection we can use that to predict to force application to use okey instead of the one that was in the database yep so see ye 2018 0 1 1 4 so as part of the sign token you can put in the header a key you say like oh this is a jws token this is sign using H mark obviously sign using RSA and this is a key but has been used to sign the token and obviously if
you server you shouldn't really trust that key because it's like I signed up token with that key so I'm giving you everything and you can use that to check that I really sign it with that key so it's like you put the key inside the envelope and you open the envelope and select ok over the key that signs the envelope that's perfect and yeah basically it's yeah and it was but if you look at source code but is pretty complex and we got like a lot of layer effects abstraction you can see how that can happen and that happened to Cisco in the JavaScript library so basically if it trusts embedded gwk in the header and
the good finger if you were using that library and never use jwk in your life you were still vulnerable to that because that's by default in the library so what you do you get a token you decode in tamper with the payload you generate RSA key to sign your token because you're going to use RSA and you add the exponent and the modulus to the header and use RS 256 and you sign the token because you got the private key and you say like ok I send the token with what by Ricky and check it with a public key but he's in the same token
don't freeze on me oh come on not again come on
I'm surprising the unlocking life anyway last time I managed to recover no that's gonna be the same thing as last time oh that's working this time Mike sorry people are gonna start believing that I do that on purpose to save time I swear I got enough content to finish so okay so I'm gonna do that demo later next thing why is my computer starting I'm gonna unplug it why it start because I may have something so when I start looking at JWT and GWS like few years back I read the RFC you know like everyone know whatever C is basically like people putting together rules to select to say like okay but our things should work when you're using TLS when
you're using SSL when using HTTP things like that so what I find is FC was with two parameters named JK you and x5u and basically yeah I know that it shouldn't because of a problem and I'm well aware of that I was very so and basically I would like which is amazing it's just a way to select all to the application go fetch the key from that web server I should be alright it happened before so got to deal with it [Music] so we will pro means that docker takes like hours to start but we should still be good if I can fine fine yeah so basically I read but like oh my god which is amazing we get like the
application to fetcher jwk there's gonna be so many bug in that like three four years of maybe not three forward two three years at least and at the time no one was using it and it was really disappointing disappointed I really need to get a new laptop okay eat something so yeah and so JK you is just short for jwk set you a hell and recently looked again at it and people start using it so basically the idea is you got to use your application and trusted server and you send an HTTP request as a user and the application gonna get this free if it works yeah get the GWT e past so header decoded passive editor gets a JK
you then fetch the jwk so the key used to verify the signature from a trusted server or from itself and then it's like okay pass is the gwk and then it verifies the signature using the JW k and it's an better response to the user so if you do like a bit of pen testing and a bit of bug bounty you can see like a lot can go wrong here like in this number three like oh so much fun so so as an attacker you send an HTTP request with the malicious GWT so that's it that's easy mode so it's going to pass the JK you and you're going to say like oh instead of going to your trusted
server you should go to my malicious server a lot better better keys better quality get V's not miss out and the server is going to get your malicious JW key and it's going to pass it and verifies the token you sent with your own malicious key and for people who are into that you can see as well but you probably got like a server-side request forgery inside the network of the application so what's fun but thankfully most people prevent value say like okay they should only be you should only trust some server or some website not everyone on the Internet so we block but just simple attack there's a really fun JavaScript implementation but fetch it but tell you
like okay this signature is varied I fetch the token but I don't trust these people so you still can do like server-side request for Joe inside the network and do whatever you want but but will tell you like it's not trust it's very but it's not trust in but turns out featuring URL is incredibly hard and people mess it up all the time so yeah we good first people using a regular expression we'd forget to escape the dots so trusted example trusted dot example.com you can find a bypass by just buying the domain domain trusted Z or trust an ABCD whatever you want example.com and that's how you can easily bypass this simple a regular expression so a lot of thing is
people you are using starts with an on paper starts with looks really good you say like oh I want the URL to start with trusted because I trust these people but if you forget the slash at the end what you can do is like HTTP trusted at pentester calm and that's going to go to pen test a lab that's not going to go to trusted because it's going to be like actually be client will think but but so username to fetch that data from intercom so that's pretty common like we've server-side request forgery another one is to select okay JW k /d wks the dot slash and a file you uploaded and since your plot is the key
you can just bypass it that way or you can find an open redirect or even better and a header injection we're going to get back to it our injection because that's going to be a really fun so we go back to like one two three we're fetching the key based on to the jku header but this time we got an open redirect and we're gonna use their open already right to say okay actually instead of fetching the key from the trusted Oh just so trusted server is going to return a redirect to the malicious server and this application will fetch the malicious jwk from the malicious server thanks to the redirect and when it's given you use
that many shoes jwk to verify the token and since you control the token and the senior and the key to sign the token you're in then even more fun so you know like I like when you do like pen test and you run burp and they find any header injection you find a header injection I'm gonna have to report it and when it's going to look lame I'm gonna have a low in my report and people are going to laugh at me that's gonna be terrible we're gonna make header injection great again so imagine you have like fetching of a jwk based on the jku header and this time you can't go our hole at all to your malicious server
because they got like huge firework nothing can get out blah blah blah and you're lucky you got a header injection I'm going to check quickly if yeah it looks like a doctor is started we are back in business
if you do demo it's always good to have a way to restart everything so you got to a heavier injection so that's when you get really tricky what you're going to do is you're going to exploit the hetero injection in your jku so you're going to use a header injection to return a full body with the key and the application is going to use that key because it comes from the trusted server because the URL starts with the trusted server and it's going to use that key to verify it's a token and you're in a jump to these okay so I'm going to quickly go back to the previous one to show what I can solve all of them so basically for
the previous one the one with the not Joe's a like Cisco not Joe's a bug you just basically you put inside the header a jwk weave so it's used for signature and you put N and E which has a public the exponent and the modulus or the modulus and the exponent of your public key and you sign with the private key and you send back to the server and you're going to get in but this time so we have a simple script so here we're just generating like a jwk somewhere else before we just like create we have a private key and we just say like okay we get the public key we put that in
some JSON and that's where the cool thing happened so here slash DeBerg is
maybe I went a bit too far sludge debug is your header injection so it's just going to basic way to inject in so header but what we're going to do is inject in the header and we're going to inject so the end of line to go to the next header when we're going to then we're going to inject like a content length to like create a real response something that looks like a normal HTTP response coming from the trusted server which is the same system and we're gonna inject everything and then we're going to sign exactly with the same key so if we run that we can see like oh but RSA key when I said they were bigger than
the H mark I didn't lie like that's that's one key so a lot bigger so here the first part which you probably can barely see is the header injection but exploited in a way so you can see like I'm adding like return and offline when the content length and then I'm adding like also Jason so I'm just using the header injection to create the response I want with the right jwk then I'm gonna put all of this in the header as part of the JK you hope no one got a headache from this and I'm just gonna say okay so this is really big token because you can imagine that you got like the food jwk
embedded in the JK you embedded in the header by 64 encoded and then it's Sangha versa and basically we become admin and yeah and the key Sevilla silver so basically we're using the header injection to just create the right key and since the header since the response come from the same server we bypass any restriction but maybe in place around like fire wording or URL starting with the right value and things like that another thing is as part of the RFC record I'll record out that you should avoid many in the middle and to do that you need to use HTTPS instead of HTTP because otherwise if you're malicious you just say like okay fetch bad key and if you can many
in the Middle's application and you man in the middle and respond with another key so the problem is that people don't owe some implemented get it wrong and try and chain but you ll start with HTTPS when they create the token which is good but you don't actually care what you need to check is when you retrieve the key over because again the person providing the jku is the attacker or someone you can't trust and we have control over that value so you should enforce TLS when you fetch the key not when you create the token okay conclusion so use strong secrets and key because but like the strength of your security relies on the strength of that
key don't store them in your source code that's pretty common but like if you have everything in your source code and one day one developer leave you need to rotate the key or you got the key so it's pretty bad posture make sure you have here rotation built in it's really hard to bake here rotation after you get an incident or when you need to do it like yeah that's when yeah yeah you really like in the middle of an incident to try to get it built in from day one reviews the library you key your peak because it's not because you're using just h mark that the library you using may not be vulnerable to other things
like the attacks we saw before make sure you check the signature because you will be surprised like yeah when I did that talk last time people were like okay actually we just took that to the source code and there was one of the services that was using day code instead of verified like we just dragged after the talk make sure you talk and expire because if you sign tokens and they never expire they're going to be valid forever so your only solution is to rotate so you want ready to have expiry inside your token and forth algorithm so don't let the client say like ok you're going to use H Mac today you're gonna use RSA
today just writing code but okay this has to be verified using H Mac because that's eight Mac we're using GWT are very complex and kind of insecure by design like people working in security and especially crypto hate GWT people can use potato which is a lot less crypto agile and a lot more secure by design because it's less permissive JWT library introduced very very interesting bugs so make sure you check for any if you do like code review pen test bug bounty or any security testing ready because yeah you're gonna find stuff and thanks for your time and you have any question
thanks about Louie folks do we have any questions at all questions yep there's just one up the back there Mike runners anyone else for questions Bueller yep all right that they thank you for that was so super interesting and some really good points about checking keys and so on when verifying charts one of the things that we used to see quite a lot is that when people would verify charts particularly things like ID - there might have been issued by another service they would get past all of these and do all these bits Rhett and that they get so excited at the end that forget to actually check that the token was intended for them yeah and so I
think that's yeah something that it's a real gotcha when you're using another service just make sure that it's actually been issued for yours and not for someone else's service good point thank you do we have any other questions at all all right fantastic talk thanks Louie all right let's humor hand you





