BSidesIOWA 2015 Keynote: Cyber in 2015 - The New Buzzwords that Matter by Ben Johnson
Show transcript [en]
Thanks for having me. Uh, I'm Ben Johnson. Uh, here to talk to you today about modern cyber defense. Uh, the new buzzwords that matter. We all probably are sick of buzzwords, but they do have their place. Uh, excited to be here. It's my first time in De Moines. Uh, my wife's actually from Debuke, so I go up there once in a while, but I've never been over here. uh good friend of uh of Ken's there. Um I'm not the sprinter if you're familiar with the 1988 Olympics with the sprinter who did drugs and lost the gold medal. Um but there you go. So uh you know we'll try to keep it uh moving pretty quick. I know it's early.
It's 8:00 or 8:20 or whatever now. Um but please make it interactive. So uh I also wanted to say this is the first time I've done this talk. I just threw these slides together for for this presentation. So I really want feedback. I'm excited about it. Uh but it is the first time so you know there's always tweaks that kind of stuff. So today I just want to go over uh you know just some stuff that you can take away right I do work for a vendor but this is absolutely not a vendor pitch. Um so we're going to go through goals real quick. I'll tell you a little bit about my background and maybe you know why you
shouldn't just you know run away screaming saying this guy's an idiot. Um we'll talk about those buzzwords and then takeaways. So the goals I want this to be interactive. If you have something to contribute, something to ask, please do so. And I al also want you to do some contemplation, some some thinking. How can this stuff apply in your environment? Some of the things I'm talking about are probably years of years ahead of where your companies are or uh at least, you know, it's just going to be really hard logistically to get there. I hope not. But, you know, a lot of what I do is talk to companies and I know it's a hard
problem to get, you know, funding, get it on board, that kind of stuff. So, my background, I started at NSA. Um, on the left here, NSA and Mante. After NSA, I did some uh work for multiple three-letter agencies and uh Department of Defense. That's why I went to to Mante so I could do more than just NSA. Um, I put it in red because I was really doing offensive things. Uh, stuff that I would have done for free. Uh but I happen to get paid for it. And uh by offense I mean um use your imagination but stuff that took executive orders to be able to do. Uh now because it requires uh high levels of approval. You
can't really do that in the commercial world. So as I started moving through my career into uh Chyus um you know we started doing more defensive things right trying to stop foreigners stop bad guys. We came up with the idea for Carbon Black, formed that, went through the whole roller coaster of building a startup, getting funding, and then being, you know, selling our company to Bit 9. And now at Bit 9, I'm chief security strategist, whatever that means. Um, but basically, I kind of act like a CTO. I travel around a lot. I did 40,000 miles in the first three months. Uh, so I'm on a lot of planes. I got platinum status already. Um, but I meet
with a lot of customers, a lot of lot of high-tech companies. uh every vertical, energy, uh finance, uh Silicon Valley. I spent a lot of time out there. Um so I hope you have some good Q&A because I've talked to a lot of really cool companies. Um I went to UC and Hopkins in case any of you have connections there. I always like uh building relationships. Please, if you feel like there's any value to us having a relationship, add me on LinkedIn or follow me on Twitter. So does anyone think we're doing a good job? No. Good job. Does anyone think we're winning? How about that? All right. So, we're on we're on the same page. So, you
know, there's this thing of, you know, cyber resiliency, being able to withstand an attack, you know, basically taking a punch and keep going. Um, you know, a lot of problems are also when we're doing uh monitoring, when we're doing incident response, when we're doing cyber defense, there's a lot of thinking like I think this is the case or I think this is malicious, but not a lot of knowing. So that's another problem. Uh we often have too much data, you know, alert fatigue, just, you know, millions of alerts, millions of events, that kind of stuff. And then how effective are we as humans? Security is about humans detecting and responding to breaches with tools to support you,
right? It's not about technology doing all the work. It's about humans doing the work and hopefully being more effective because of technology. So that's something to think about. So the first buzzword and this is actually multiple words right but risk hunting. So is anyone here doing threat hunting? Okay maybe a little. So threat hunting is a little bit more advanced where um you're not just you know responding to alerts. You're not just looking at a SIM. You're not just scanning for IoC's. You're actually mining data. You're actually hunting. But my uh sort of passion here is we got to move beyond threats. we got to move to risk. Risk is a higher level uh concept than threats, right? Risk is
actually threat plus you know what's vulnerable, what assets do you have, what are your countermeasures, we got to think about risk. So, you know, when we're too focused on compromise and things like indicators of compromise, you know, we typically aren't really focused on improving our posture. We're trying to put out the fire as fast as possible. We're trying to clean up and just get back to the next alert, but we're not really focused on where the problems will be. We're focused on where are the bad guys now or even just mass malware, that kind of stuff. And that's too hard to keep up. There's too many bad guys. And it's a lot harder to know what bad behavior
looks like than what risky behavior looks like because of intent. I can say, you know what, this guy keeps being the first one in my environment to hit new domains or to install software. Okay, that's I'm gonna define him as a risky user. But malicious or, you know, bad behavior is much harder to define. It's like credit card companies. How do they detect fraud? They don't look for bad. They look for known good like a fuzzy box and then once your spending goes outside that box too far out of your profile, you know, they profile all of us. Then they call you and they say, "Hey, are you actually buying something for a dollar in Singapore or whatever?"
Right? So, we have to think about that as we're doing our uh strategic planning, but also our day-to-day operations. And there's this notion, you've probably heard it if you read blogs or or talk to analysts. A lot of times we're the firefighter in the in the cyber defense world, right? Something's going on, we're trying to fix it. But now we're trying to move to the beat cop who's also responding to 911 calls, you know, cyber incidents, whatever. But he's also out looking for problems, getting to know his environment, right? If you think about the cop out on the beach, but we can't stop there. And this is what I'm talking about risk. We got to move to a fire
marshall as well. Fire marshall is going to go and say, you know what, this structure, this is going to cause problems. Or if this thing breaks right here, it's going to collapse and kill all these people. Think about that in your environment. If something gets compromised, some part of your network, some segment, if this machine gets hit, what can happen? Think about risk. So, you know, just to give you a few concrete examples here, and I already mentioned some of this. What users are being the first to hit a domain you've never seen before? Who's opening all these attachments? What happens if someone just walks into your company and plugs into the wall? What access do they get?
A lot of times, the security team doesn't know. And you know, we've done back when we did some pen testing uh commercial work, we would just go set up an interview and then say we have to go to the bathroom and then just plug something in the wall and say, "Oh, I don't feel well. I'm leaving." We literally did that all the time. Do you know what access we would have? Maybe, maybe not. Um where, you know, where are the misconfigurations? You know, there's plenty. Even with a a small company, there's plenty. But large companies are chaotic, you know, organic environments. And ultimately, I I don't know if you Yeah, this dot works, but think about
what can an insider do if they're on this system or if they're on this system or if they have access to this data. What can they do? That's where you really have to focus your your attention because the bad guys will become insiders. They'll get credentials or they'll land malware, you know, just one little fishing email and they've parachuted over your perimeter if you even have a perimeter. So, you got to think about that. So, we have to detect and respond quickly. But we want to get ahead of the game. We can't keep up. We don't want this anymore. We don't want bombardment, right? Just getting crushed by bad things. And oh, by the way, a lot of companies don't even know.
Probably you guys have seen this. Like you don't even know what's going on because you don't have the visibility, right? So you're probably getting crushed and it's like you don't even know that you're being bombed. But we don't want this to happen. So again, we want to be able to conduct risk hunting. That's where we want to get to. So, a couple other buzzwords I'm going to talk about are trying to get you there because how can you conduct risk hunting if you don't have time? If you're too uh too burdened with the number of alerts, the number of fires to put out, false positive, etc. You could never even think about risk hunting. Hardly anyone
raised their hand of threat hunting. And to me, that's not even advanced as risk hunting. Now risk hunting is uh part of compliance a little bit but it's usually not a very active ongoing thing. You know to me risk hunting is you can take a person in your environment and they go and look for a misconfiguration or um you know machine A should not talk to machine B and as soon as they find that you act as if that's the compromise. You say okay crap what if someone exploited this go do an instant response. I hope we get there. Not many companies are doing that. So buzzword number two, analytics. This is really hot buzzword
right now. It's not necessarily new, but it's it's it's much hotter 2014 2015 uh than it was 2014 2013. Um going to RSA tomorrow for the week. I'm sure every company is going to be saying analytics, right? And analytics, there's a lot of definitions for it. You probably have your own thoughts. Um, I have my own definition which isn't necessarily the same as you, but I think you'll you'll understand what I'm talking about. So, what is analytics? Lots of things, right? Like I just said, but to me, it's extracting data, extracting extracting value, extracting intelligence from data, from relationships among that data, right? But really, when I boil it down, it's about comparing current behavior to historical behavior and
comparing current behavior against other current behavior. And you boil it down even more. It's about finding things. Signal versus noise. Where's the signal in this noise? And when I talk to some uh customers, especially the ones that are kind of have their stuff together, they're actually trying to figure out what story does the data tell, where do they have to apply their resources, where does their budget need to go, where does their strategy and planning need to go, what story does your data tell? And analytics helps with that. So when you talk about analytics and comparing behavior, comparing events, if your environment is like this versus this, guess which one's a lot easier to do analytics on, not this, what's
normal? Where's your baseline? How can you find anomalies? How can algorithms pick out what's normal? How can even humans pick out what's normal? And I was just in India and experienced this chaos. Um, so you got to think about this. You got to work with it. You got to lean on it to clean up your act. You know, base images, network segmentation, all this simple stuff, which I know is not simple in practice because of merger and acquisitions and just new machines coming online. You got to get the, you know, ship a product or keep the keep the lights on or whatever. I understand, but you got to at least try to get here. So to give you a few examples of what I
consider just simple analytics, people might not even call these analytics, but I do. Are you just recording every time net.exe is run or something similar that might be abused by a bad guy and probably not used that often in house? Are you watching when PowerShell is being used? Even simple stuff like are you mapping which user logs into which machine? Why is the domain admin on that HR person's box? Well, it's probably not the domain admin. It's probably some bad guy. And then other stuff, too, like is it Dropbox.exe connecting to dropbox.com, or is it some unsigned binary running out of a temp directory named xyz.exe? So, there's a lot of stuff to think about, but some of this stuff is
really how you catch malicious humans and, you know, malware too, but malicious humans. And it comes down to, you know, visibility and analysis. You've got to be able to see these kinds of events or this kind of data before you can start pulling out anomalies, looking for patterns, comparing behavior. If you don't have any visibility, if you don't have any data, you have nothing to do with analytics, right? And so, uh, real quick, this is a passion of mine. It's a whole separate talk just on advanced threat hunting, but the bad guys truly live off the land. And what do I mean by that? Well, malicious humans especially and and especially like state sponsored or
advanced, you know, like cyber crime mafias, that kind of stuff, they get credentials and then what do they do? They live off the land. They use FTP, they use PowerShell, they use command shell, they use Robocopy, they use all these tools that are built, and that's just Windows. Mac and Linux, other other Unix style systems have tons of utilities. They can do everything they want. compression uh you know SCP all this stuff they don't need to drop malware they just log in and use signed Microsoft or whatever Google whatever binaries that's how they do their job and they're they they do it well so they blend in target everyone still likes picking on target you
probably can't read this but attackers mostly use general IT tools procedures and protocols seldom did they use hackers specific tools and malware. Now, they put up RAM scraper malware or whatever, but it got on all the machines through the the the system administrator tools, the software distribution mechanisms, said, "Hey, install this on all our point of sale systems and then collect the data and then just use FTP to go out." Just literally FTP all your credit cards. So, it's occurring all the time and analytics, right? Just show me where net.exe is running in the command line. Okay, all this crap that's not useful, but then all of a sudden, even with a human eye, it just jumps out like, "Hey,
someone's adding a user here and someone's mounting a share." Even just simple recording of things like net.exe or other tools like that, you might start finding stuff maybe insiders abusing things or just uh mounting shares you don't think they should be mounting, etc. or or malicious humans. So, analytics, again, this is this is really how I think of analytics. You might have your own definition. buzzword number three and my favorite and oh by the way I thought I think analytics is the number one buzz word of the year. I think orchestration is number two. Risk hunting's I'm not sure where that's going to fall but remember we're trying to use analytics and now orchestration to save you time so that
you can maybe get to risk hunting or threat hunting. So orchestration anyone hear much about orchestration? Anyone doing orchestration? Awesome. Um, so you can also think of it like automation, integration. Um, I I like the word orchestration and I think that's really catching on. Um, you have people like DARPA saying, "Look, the attackers just have to find a single flaw. Defenders really have to try to predict, anticipate, and deny every flaw. So the economics are not in your favor. Not in our favor. So, it's through automation, through computational power that we can hopefully level the playing field or maybe even get ahead. Although that's that sounds a little crazy right now when we're completely not
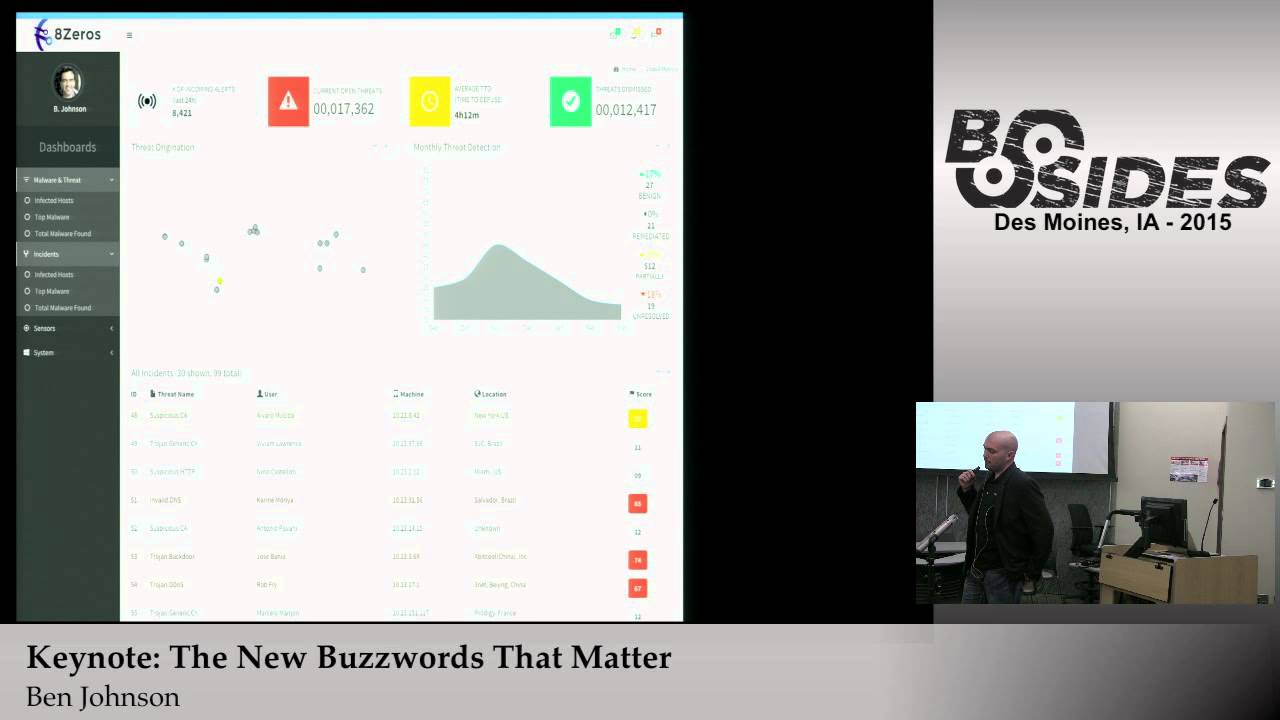
winning. So, you have all these different parts of your stack. You're trying to protect, you know, identity or, you know, users, uh, user accounts, etc. You're trying to protect data, trying to protect systems, trying to protect communications. But all this stuff is related and all has to work together. And to put it another way, and I don't know about your spending or your stack, your security stack, but you really need stuff on the endpoint on your network. You need some form of analytics and you need some threat intelligence. Buzz word of last year. So you need all this stuff to work together. And you have companies, there's a bunch of them now that are coming out. This isn't our company. is
you have a bunch of companies that are coming out with it's kind of like SIM 2.0 where it's trying to give you a single pane of glass where it's incorporating all the different you know detection alerts from your different uh products and solutions but then it's trying to pull in context when you get that alert and it says hey this malicious binary connected to that IP in that domain does that alert also tell you like when the domain was registered how often that that IP is hit in your environment what user account is that user on vacation um where is that user sit Uh what else has been seen in my environment related to this? Are your
alerts saying that? Yeah. Well, I mean that kind of basic message you just illustrated there really fails because I get that particular type of binary. Most of these attackers that have sophistic
that are really clever are not even the same binary. They are switching to multiple types of binaries from multiple IP locations that are completely distributed. There is no rale that can be easily very hard. So those kinds of modalities of only will give you low hanging fruit. They won't do anything. Right? So it's it's also it's also about um showing what else is occurring in that time frame. What else are those machines doing that's related? So I agree that IPs and stuff change, but a lot of times attacks will hit a bunch of boxes at once and they will use the same IP at least for that one attack like that day, right? And then they might change. I was
saying actually don't do that. Okay. So um so but it's still all about pulling information together. when you're responding to an alert, do you have to go paste your domain and do a who is or things like that? Having all this information at your fingertips, but not just not just pulling information together, but being able to talk to systems in your environment that can take action. Oh, this thing's bad. And according to multiple sources of thread intel, yep, I'm sure it's bad. Okay, let me go banan that hash. Let me turn off that switch port. Let me send off an email. let me uh and automatically enroll that user in fishing training or whatever. So orchestration is really
what I'm talking about for that stuff. And you're seeing especially companies like in Silicon Valley where literally 80% of their security team are coders because all these products now have APIs. So just put coders to it. You still have analysts, but put coders to tie all this stuff together. And now you're starting to see companies come out with actual products. It's like a correlation engine. Right. And this is what I'm talking about with orchestration. So, you know, really trying to unify your products. A lot of you buy different products. They might have a connector, they might not. I'm a vendor. Full disclosure, we we we provide uh connectors, but you know, it's it's 1 plus 1 equals 2.2 2.5
uh when you have an integration, but it's really the dream is 1 plus 1 equals 3 or four, right? So, these two products, if you have them both, it's better than just, you know, the sum of the parts. So trying to do all of this stuff. So you know and I I mostly talked about this but pulling together different sources of information so your humans don't have to spend time on this. What's the geographic location of the IP? That should just show up in your alert. What purpose does that user have in the organization? Because that's context you can use very quickly. It might change the severity of the alert if it's the sea level guy or if it's a
you know entry level person. It's about data understanding, not necessarily data volume. So you might have a lot of data volume. If you can boil that down to better understanding, you can have tons of data, but the humans only look at a little bit. That's the goal, right? And orchestration feeds analytics because you're pulling all this stuff together. Analytics can feed into orchestration, but orchestration can feed into analytics. It pulls all this different information and then it does some analysis on it, some algorithmic um decision- making, you know. For example, you might detonate a binary, see what domains uh it connects to, and then a human has to go do all this extra lookup. Where else is this uh
domain C? Where what is the who is information? Who registered it? And then again, you have to manually go take action like banning hashes, blocking IPs, sync, holding domains. Guys with me trying to automate some of this stuff. really try to get 1 plus 1 equals 3. Automatically take action. You see a bad thing, hit that endpoint, isolate that machine from the network until you're really sure that it's not malicious or until you can reimage or whatever. That's where we're going. Still need humans in the loop, absolutely, but there's a lot of actions you can take that are automated. That's that's really what I think about when I think about orchestration. So, analytics and orchestration feed each other and
they're both outputting risk. They're trying to surface risk. could be actual threats or it could just be risk. This is risky behavior. I'm not sure if it's malicious, but you should look at it. So, takeaways, go watch this keynote if you haven't seen it. Bruce Schneider doesn't doesn't even work for our company, but I love this talk, right? 2014 blackhead keynote. Response is the closest thing we have in it to dog fighting. I just love that. Makes us dog fighting school, right? Um, but you know, it's about udaloops. This notion out of the military. Whoever can observe, orient, decide, and act the fastest is going to win. Well, if you don't have visibility, you're not really observing until
finally something says, "Hey, there's an alert. Go look." It might take you too long to orient. If you don't have the right context, the right uh you know really the right context around that event, how quickly can you make a decision? Are you orchestrating everything so you have all this information to make quick decisions and then act? We just talked about maybe quickly banning IPs, banning hashes, uh calling user real quick, uh taking a machine off the off the network, that kind of stuff. If you can't move that quickly, it's going to be a losing battle. And that's really where we are right now is the bad guys move faster than we do. They often get into these
environments. They map out your environment and they know it better than you do. That's the reality. And you're trying to go through this, right, the NIST incident management life cycle faster and more effectively. That's the whole goal. But really the goal is to go through this before there's malicious intent, malicious activity. Try to go through this when it's risk and it's not actual threat. That's the goal, right? Risk hunting. Go through this. Try to fix problems before they're actually exploited or taken advantage of. So, I talked about a lot of different things. What are the underlying themes? I I basically mentioned them, but feedback loops. Something uh suspicious comes across your network, can you validate it
with endpoint or vice versa? something runs that's strange on your computer, what does a network device tell you about it? What does DLP? What are all these other security products you have tell you? What does threat intelligence tell you? And ultimately, it's about saving humans time. We are all understaffed. We all spend way too much time on stuff that's not really useful, doing manual lookups, chasing down uh some malicious binary came across the wire and detonated, and oh, it's really bad. Oh, but by the way, it's destined for a Mac and it's a Windows exploit. You should spend zero time on that. Maybe if you have time, you want to go reverse engineer it or whatever, but you should
not jump out of bed. You should just know that, oh, that's not going to matter. So, uh, to to give you an example to think about, a lot of times we're looking at data like this. Individual events could be binaries, could be URLs, whatever. Just individual events like in your SIM or or log mechanism right? A lot of them basically look the same when you start, you know, to do your analysis, but it shouldn't. You shouldn't start there. You should have stuff like thread intelligence, stuff like reputation information. I'm going to start on the dark red at least because I want my humans to be more effective and have better priorities, right? So, I'm going to
start with the red. At least someone thinks that's bad. But don't stop there either. Make it relevant to your environment. things like prevalence, frequency, how often is this occurring, right? That's where again really where analytics comes in. If it's very frequent and thought to be bad, well, either my threat intelligence is wrong or I'm screwed. But either way, you're in a better spot knowing that. But finally, relationships. This is where it really comes together. If some unknown binary starts running, but everything it does is known good, prioritize that below some unknown binary or some new binary running that's doing some things that are unknown about prioritization, saving humans time, right? Focusing your time on the stuff
that actually is risky or a threat. So that's where we were. This is where us as an industry are trying to get to. Doing some good things, but you know, there's still always more work to be done. And a real concrete example is, oh, SBC host ran. Oh, great. Eight run on every Windows machine. Or if I tell you SBC host was spawned by an unsigned binary under a strange user account and made network connection. I'm going to jump out of bed on Christmas to look at that. So remember orchestration, analytics, risk hunting, remember the goals. Hopefully we can get a little bit of discussion. I think we have a little time. We started late. Get
some Q&A and discussion going right now. But think about how you might apply some of this in your environment. And I want to tell you a a true story. After the Home Depot breach, I got a I got a call saying your credit card was compromised. And it turned out they used my credit card at Target. So it was like the cycle's complete. And a true story. It was I don't know just just strange coincidence, I guess. um questions, discussion, comments, please. Yeah. So, I'm totally on board with everything. Um so, kind of bringing it to relationships and everything, but the point where I'm having trouble is kind of defining what is that behavior? How
do I define what is and I I know there's some patterns that obviously stand out, but at that point, you're kind of just finding this endless So kind of how do we take that further? Yeah. So um I'll repeat the question for the the video or whatever. So the question is kind of it's hard to define known bad or it's hard to you know define what bad is. And that was kind of one of the things I talked about earlier was it's easier to define risk like risky behavior than malicious behavior. And it kind of comes back to the thing about the credit card companies. They don't know they don't know what bad behavior looks like. Yeah.
Sure. They basically blacklist some merchants and stuff around the world, but they profile you into this fuzzy box and as soon as you your spending goes way outside that, then they call you, right? So, they're looking for known good and then as soon as it's outside of known good, then they call you. So, um I I think you need to do stuff like, you know, so I'll just ramble for a second. Uh IC's have marginal value. There's four billion IPv4 addresses. If you're looking for a few hundred IPs, that's not a very good ratio, four billion possible, you're looking for a few hundred. Um, it's a little bit better odds because you might, you know, have
subsequent usages of those uh sites or whatever. Um, uh, but you want to automate looking for those. You want to automate looking for strange behavior that's typical of malware TTPs like running out of temp directory or unsigned binary trying to manipulate some Windows service, things like that. could be signed binary, but it's signed by some little software vendor that got hacked or whatever. Um, so automate some of that, but then just start looking for abnormal behavior and trying to again flip it where you can put everyone into remember like the NASCAR thing. If you can try to get closer to a base image, like less drift, less entropy from the base image, then you can start saying, okay, there's
enough consistency that anytime there's a new process no one has ever seen before or a new connection no one has ever made before, that's infrequent enough that I can look at that. So that's that's kind of my advice there. Yeah. Why is the US governmental cyber infrastructure not actually carrying it actually defend the country from cyber threats? We are all here as private industry for the most part but my understanding is the department of defense was supposed to be country and yet we get invaded continuously from outside of the country with these threats. I specifically hate about this with no response at the NSA 10 years ago. We could easily determine the NSA database we had for
our own infrastructure or they could stop coming in the first place. Yeah. So I think it's duty. So Why are they doing something? Why are they lazy? Why are they sloful? Why are they not opening their oath to protect the country? So, uh, so the question is kind of you you heard it. I'll say it for the the the recording. Um, why isn't the the federal government especially um and Department of Defense and intel community doing more, right? Like if your business gets bombed, they're going to respond for you. Why is there even a threat? It's more I think it's more of a political issue of trying to um apply too much federal oversight and um
whether it's real or not, the invasion of privacy is still a huge like battle, right? The whole privacy versus security. Um yeah, I I don't I don't know. I don't know exactly. Um I mean there's a lot of like NSA is swamped with overseas stuff, right? Um and they're really focused more on overseas. I know they do listen to phone calls and stuff, right? Um uh it's a it's a completely valid question and I think we all have the same question. Why isn't and I think the government is moving to do more. It's just slow, right? Like it's just slow. They're starting to pass legislation, but even that which you'd think everyone's on board with is a little slow. Um but I
think we will see the federal government having to step up more at least in terms of um sharing intel uh you know doing some blocking that kind of stuff. Um, but I think they're still for a long time going to stay hands off on your corporate security and a lot of attacks come from within the US like you just bounce off an Amazon box or Rackspace or whatever, right? So, um, well, I didn't say it was a perfect solution. No, no, no, I know I don't. Yeah, I mean I was at a like I worked at ISP some years ago and it was the simplest thing you could imagine. Somebody hacked DNS for a Chinese ISP
and they their mail exchange records to the barracuda boxes at our facilities that was in our data center and obviously you're immediately down that much traffic that's false your systems we have no idea why we eventually obviously cut off the data flow but just that basic level you're supposed US government had that visibility on the border routers to see that traffic coming to the United States. They could have stopped at the border. It's an invalid form of traffic. There's no there's no way from China.
Yeah. There's no privacy involved privacy. I think I think the really are like a duty in their analyses. They are just not doing their job. They step down and people that know what they're doing. Yeah, I think I I mean I think it's a taxpayer money.
No, I I hear you. Let me uh let me take some more here.
The statement was he wants NSA to stay out of enterprise.
We could talk government after blue shirt here. What does this look like? These three buzzwords. what can they look like in terms of an implementation within an organization? So, so the question is what do these look like in an implementation? Well, risk hunting is more of having the right access to information to have a human go look for problems and it could be automated a little bit, right? Um, but it's really like I'm going to go find where our misconfigur like it's it's really the hunter mentality. I'm going to go find where we have misconfigurations or like figure out what boxes can talk to each other but shouldn't. That kind of stuff. So that's more of a human thing. Um orchestration
is um there's you know it's kind of like integration and automation. So some coding, some scripting um but some vendor provided tools that kind of stuff really just pulling together you know even just simple things like you have a next generation firewall that detonates things and you have something on your computers they should talk to each other like you detonate it and then in your alert it also says oh by the way not only was this bad destined for Ben's machine but it ran just saving time right. Um and then uh analytics is also like kind of collecting data and there's a ton of new companies and products that are saying analytics and you know I'm
not saying they're not doing it but um they're younger so it's you know it is a hard problem to take all this information process it find anomalies another buzz word that I didn't talk about is machine learning if you go to like west coast Bay Area it's like everyone's third word out of their mouth is machine learning um but it's really about finding anomalies and then like remembering those and then you know improving your algorithm based on that almost like AI, right? Um but it it all comes down to these are more concepts and trying to figure out how you can apply these with your tools, with your people, with your skill sets like programmers or whatever. Um that's
really where implementation is. Yeah. Um so with regards to analytics, there's always going to be some users that are really really hard to profile. One that comes to mind is developers. Uh I have and I'm sure a lot of people here have worn the developer hat at some point and even very large corporate environment developers look really sketchy just when they're normally doing their job. Um be that you know random Python scripts running day in day out port 22 connections to random Git repositories on the internet to pull something down. Um how would you tackle the problem of profiling a user that's very hard to profile? I still think they're easier to profile than you might think. Um but
yeah there's definitely so the the question is there's developers and other people that are very dynamic right so it's hard to profile um you can still restrict what they can do so yeah you can go to anywhere on github.com anywhere in github whatever like allow them to do that but if they go to other sites they have to get permission or whatever I understand there might be workflow issues or or um effectiveness where if it's takes too long to get to a special repo then they're going to not do their job well or throw a fit. Um, but you can still figure out like, hey, they normally run Visual Studio, they normally run PyCharm or whatever,
Intelligj, pick your tools, right? So, they start installing all this other stuff. It should be infrequent enough that you can go say, hey, why are you installing this? Or make it so you can only install stuff that's out of a shared directory or some sort of approved installation folder. Um, and just again make the process fast enough so that you need approval. Oh, I can get it within 10 minutes or something. So yeah, it's harder to profile, but um I think it's easier than you might think. And none of this is like easy. I mean, no one's raising their hands when I ask who's doing this stuff, right? Um but it's it's not impossible. And then I guess sort of a followup to
that is how do we balance trust against that? Because at some point there are users you need to fully trust. You need to fully trust your domain admin, CIS admins. At what level? where do you feel that should be higher than what we normally do or where yeah so the question is kind of trust and especially people have like root or domain admin access that kind of stuff um think about feedback loops when they make changes does it get logged somewhere does it get audited that's you you have to trust your employees you have to keep them happy um but you're there's a huge push uh kind of globally but nationwide on insider threat huge push all these big
companies have official like budgeted programs on insider threat they're trying to figure out what tools or what processes can do that. The government has said, you know, each uh department or each organization has to at least be making progress on insider threat because they're like Snowden and stuff like that. Um so you're seeing a huge push and it's a hard problem to solve. But um ultimately if you're at least doing feedback loops and saying trying to profile like okay the domain admin should only log in like account should only log into these four boxes. If it starts logging in elsewhere either someone's lazy or it's compromised or whatever. So um you do have to have
trust but you do have to do some sort of monitoring some sort of auditing as well. Question I think we have a few more minutes. Yeah. Where do we draw the line? I have to solve. I think there should be some things that each person
gets draw Obviously our personnel need to put in businesses and tickets for minimal things that are no threat and then it slows down our business processes. So the question is where's the line drawn be between sort of openness and enforcement or lockdown right hardening that kind of stuff. Um, which is funny because that's what our company has to deal with all the time because we have two products and one is about watching all the time and letting you do anything you want. And I'm not trying to be a product pitch here. And the other one is about enforcing and like locking it down. So literally like every customer I talk to has like that question. Um, and
uh it's it's cultural fit first of all. Um, like I see places in the West Coast where they're like, "Dude, we could never block a process. Like never stop someone from installing. I just want to see. I just want to know." And so it really visibility, another buzz word more from last year, but um visibility is key. So like maybe you give them a little bit more um uh freedom to install stuff, but you're you're literally, you know, recording and being notified every time someone installs something. And if that's too voluous, maybe you you filter out like signed by Microsoft, signed by Google, signed by whatever. Um so that's really where some of the analytics and
automation come in. Um but I don't know, I was a coder for forever. I still write code, right? And like the number of things I actually install like daily or weekly is like zero basically, right? Like over time maybe I need a new IDE or new package I never had before, but it's not like all the time. Like it it kind of the question like it sounds like there's a lot of dynamic activity going on from these users, but really if they can't install stuff except for a specific day or a specific directory or whatever, um I still think most of the time they can get their job done just as fast. Few more questions, discussion.
black shirt. Yeah. You loops like a fully automatic solution. I don't think that's a feasible solution. Um but then I also believe that the machine should do as much as possible. So you can kind of lower that threshold. You don't have to throw your senior analyst at it. You know, a junior analyst can still figure out what's going on. But I'm kind of concerned that there's still too much data. Can the human are we going to cross that threshold of what the human understanding so much these graphs are getting so big? Yeah. So it's um so the question is like there's there's too much data. We still need a human in the loop. Um when does it just become
overwhelming? Um so again it's boiling it down trying to automate. um uh like uh this one company in Silicon Valley um let's just say they probably stream a lot of videos and and shows to you and stuff. Um they literally each of their alerts because they do all this cool orchestration stuff literally their alert has a recommendation. So, it's like, oh, based on all this, here's like a score. Here's a recommendation, reimage or kill these processes or whatever. But a human still makes the decision. And then it has all this information like like this is where a lot of these themes came from. Like, oh, it's this user. Oh, by the way, they're on vacation this week, so why is that
box receiving something? Or um this is the domain, here's the country, here's other attacks from that country or other connections from that country we've seen this week. Um, so trying to boil it down, but really if you can get it simplistic enough so the entry level guy can at least figure out if it's worth escalation, not necessarily make the decision. Just try to filter out stuff that doesn't meet a certain escalation, you know, threshold. That's really where you have to get to. So I guess my question is, do you think we'll always be able to do that or are we going to reach a point in the future where we can't boil it down? Um, I think we're actually going to get
better at boiling it down. I think we're really bad at boiling down. It's like those dots. We're all like these black dots right now and the entry- level guy is like I don't know what this is. Like um you know it's just some random you know like google.com is being alerted on and stuff like it's like I've seen that and I'm like why is that alerting like that's you're you're not good questions over here. Got to be more questions. Come on. Yep. So I was fired and they chose
tools which is great.
Another thing I hear all the time. Sadly there is no silver bullet for that either. Um the question was I've done a lot of good things, have pretty good posture. How do I convince upper management that it's not enough or you know to actually implement what I laid out as a plan? Um so boards are waking up, CEOs are waking up. Um you have some big companies where literally every time their board meets like half of their board meeting is about cyber threats. Um on the flip side it's about risk. So, um, I've had really large companies say, "Look, my my CEO, um, said,"I don't care if it's a tsunami or a cyber attack. I just want to figure
out where's the risk and how do I mitigate it?" And so, we all think like, "Oh, cyber attack, they have to be focused on it." But no, there's like all these other risks to your business, especially global businesses. Um, but I think showing how you can implement it relatively painlessly or quickly is, you know, part of the problem or part of the solution. you know, um, showing that you're gonna provide some sort of measurement, right? If you don't measure it, you can't optimize it. So, saying, look, we're gonna implement this and, oh, by the way, in three months, we're going to provide you these metrics. Now, metrics is a whole another can of worms that could be good
or bad. Um, showing you how to you do that. And then, um, trying to put it in terms of saving time and saving money. Um, you know, it's hard to use scarewware and stuff like, hey, if we get breached, it's going to be $5 million or whatever. But the news kind of does that for you. So, if you keep it a little bit more specific to like, hey, look, this new product we come out, if if it if we get hacked, then China's just going to produce it for a nickel and cost us $100, right? Um, I don't know. So there's no there's no silver bullet there, but trying to make sure they understand the risk at least and
then show simple things you can do to at least improve a little bit or maybe a lot and we can talk more after too. Final questions, anything? Come on.
So, what is the most unusual thing you can talk about that you do with the NSA publicly? This guy likes the NSA. Um, actually knew General Hayden, too. I, you know, I was nothing. Uh, you know, I was a entry level guy, but um I don't know. I don't know. We did a lot of interesting things. Uh, it was during Iraq and Afghanistan, so there was a lot of work. Um, a lot of supporting the war fighter. Um, I don't know. Places like that really make you grow because you can't just Google for the answer. You might even not even have internet access. You might be in a closed environment where you just have to like figure out how to,
you know, break something or, you know, install something covertly or whatever. Uh, and you just have to work your butt off to figure it out. So, you really grow as a person or as a, you know, as a professional. you learn all these skills and you might be doing some Windows thing or Linux thing, you know, one day or the other day and then you might be doing a Cisco thing or um looking at some specific application or doing some reverse engineering or stuff. So, it's it's pretty cool uh work and there's a lot of it uh going on. Um I know that wasn't really anything of substance, but um it's pretty cool. If anyone's
interested, there's a lot of work in cyber, both offense and defense, uh in the DC area. You couldn't really answer that very details. What is your favorite agency out there? My favorite is actually a four-letter agency called JC, Joint Special Operations Command. I'll just leave it at that. Look it up. It's awesome. Um, all right. Any other final questions? Uh the one thing I want to point out is we have a hard problem. We have all these tools but a lot of times it still comes down to your culture to human error to human or you know user education. Um so remember uh analytics orchestration risk hunting but just all I want you to do is think about how can
you get to some of this stuff like how can you think about this when you're procuring tools or when you're building out your team or when you're putting your processes in place. Last chance. Any questions? All right. Thank you guys. [Applause]





