Modemsploitation: An Overview Of Security In Cellular Networks And Modems by Amit Vitekar

Show transcript [en]
so uh very good morning to all let's begin with the first talk of the day um this talk is going to be more about security of cellular networks and modems which are present in your smartphones your cars your iot devices drones and what not my name is amit viteka i'm a cyber security master student at national college of ireland i have a two plus years of experience as security researcher into hacking electric vehicle iot devices embedded devices my most focus is on security of cellular networks i have worked on security of gsm lte 5g somewhat and most of my time i spend reverse engineering and exploiting embedded and iot devices i'm also interested of something i mean
i have a special interest in awkward science too okay so what's this talk going to be about first things first we'll be looking at an overview of 4g lte network to just get a basic understanding of how cellular networks work then we'll try to fit in how does modern play important role into communicating with cellular networks and then we'll be talking about security features in the cellular modems we'll also be looking at the case study of what of different vulnerabilities that i had reported and then we'll talk about machine mitigation techniques that can be used by different vendors okay so this is what a basic 4g network looks like the ue is basically user equipment
we call it this a smartphone this could be a smartphone this could be your car which is connected to a 4g network let's say tesla or it could be an iot device it could be a drone which is connected to a cellular network the enb which is basically the cellular tower also known as evolved node base this is your cellphone tower through which to which your smartphone communicates this tower is connected to the mme mme basically stands for mobile management entity this is where all the security stuff happens all of your uh encryption keys are stored here everything and the enb talks to the mme directly these are mostly connected to fiber optics and various
means all of your ip packets are routed through s gateway okay so most of whatever you're browsing let's say you're browsing facebook everything all of the data flows from s gateway and the job of the pdm gateway or the p gateway is to allocate you ip as soon as you turn on your smartphone and your data so pdm plays a very important role in all this all of these things work interconnected with each other right from your smartphone to your pdm gateway that is how your data flows and then you are able to browse the internet so now the question arises where do cellular models fit in and why do we need them so just like there are rfcs for various
community various protocols so for web and tcp and stuff there's a consortium called idu international telecom union and it has a different sister groups i would say one of them is 3gb so 3gpp is responsible for laying out technical specifications of how the network should be architected how the architecture of the network should be how they should be deployed and how it should work so specifically when it comes to your smartphone vendors your routers your electric vehicles and whatnot they have to follow this specification to design the modem chip and a firmware running on top of this chip which is basically an rtos with different different tasks it makes sure that all the 80 commands
which are being executed are being translated into different um basically commands and being sent to the nearby cell phone tower over rf means this chips are mainly available in your mostly found i would say in your smartphones in your routers and even your electric cars drones and whatnot so our talk will be focusing mostly on based on this chip as i said a baseband firmware and cellular modem contains 3gb specs and it is implemented in from an rtos also sometimes it has been found it is available in the form of embedded linux or open source linux systems so these are some of the security features that are being you know are given by various vendors
uh what today i'll be talking mostly is about quechtel quechtel is one of the biggest biggest vendors in modern space and telecom space and they use qualcomm's architecture called as hexagon hexagon has a very different architecture a very different instruction set reverse engineering hexagon chip is very difficult because they are not arm based they have a very different way of working and executing so there are four protection techniques that are given by this different different vendors one of them is jamming detection so if let's say you're traveling somewhere and you lose connectivity to your cellular network basically your phone is offline right you cannot call anyone you cannot use the internet or do anything now this is in the case when you're
roaming let's say there is some white noise or disturbance present in an rx spectrum this causes the smartphone to get jammed and there is jamming detection in these chips specifically when they are used in electric cars and drones and stuff in smartphone apple does provide protection from jamming but i'm not aware about with other vendors like samsung and oppo or something like that the second protection technique or mechanism in this provide are this vendors provide a pseudo based station attack direction which is basically deploying a fake gsm or ld network and forcing your smartphone or your device to connect to this cellular fake cellular network so again depends on different different smartphone vendors some of them provide
protection some of them don't then there is a private apn attack so mostly in electric cars and drones what you would find is that apns used are very different from the aps that you find in your smartphones or your iot devices they are not just that you create an apn go to your settings open as create an api and type in the name of your api and save it and your data starts flowing through their network that's not how it works usually they have a user password mechanism but when i have what when i've been tested couple of uh evs uh in last two years i haven't found any of the security mechanisms being induced
and this is something has been advised by a lot of modern manufacturers and it's even present into 3gb specs that a username password combination should be used to authenticate let's say a car or field of cars to a cellular network and the last thing we will be talking about is an 80 command one ability attack so this is basically a hardware and a firmware based attack in which if you reverse engineer the modem you find serial communication ports let's say uh universal synchronous real-time communication serial wire interface swi and once you get access to this you access the internal firmware or your time try to dump the firmware you reverse engineer the firmware figure out
what 80 commands are being there and then you try to manipulate the city commands so these are some of the protection techniques are provided by vendors against these various attacks so one by one we'll be seeing how we can bypass this technique even if the protection mechanisms are available and what measures should different different oems take when it comes to protecting the devices from attacks specifically to modems and cellular networks okay so how is this going to be done what is the lab setup and everything so most of this stuff that i'll be talking about will be done in an isolated environment you can consider a faraday's case something like that or a room which
is isolated from external networks we'll be using a software defined radio so all of those who don't know what's a software defined radio it's a radio which is in which you can listen to any frequency or you can transmit any frequency and stuff so we'll be using usrpb200 for deploying our 4g network which will act as a pseudo based station i will be using hack rf everybody knows hacker what is hacker it's pretty famous uh it will use it for i will be using it for jamming the network gps proofing this mostly has been used when it comes to spoofing your apps like uber and all this stuff where you try to manipulate the destination that you're
trying to reach and sometimes just get away with it at zero cost you can get a ride and later on we'll see how a usb total converter can be used to just talk to the modem over uh swi interface so let's begin so to bypass the jamming detection the first thing is that we need to figure out at what frequency is your smartphone or your target device communicating with a nearby cellular network so this is something this is called something called as ear fcn eu absolute radio frequency channel number this is specified in the 3gbp specifications uh you have to do some reconnaissance you need to run uh your hack rf or usrp uh with
your custom gnu radio script and start listening to various gsm frequencies if you stay in area so let's say in india we use basically use frequencies on a gsm of 900 megahertz and that is where every region or every state in india has been allocated a specific ar fcn and then you have to just look it up and try yeah oh is your device listening at this here fca uh i have tested this and over a smartphone and even some other ot devices also the target device uh which was kind of a telematics unit or using jamming attack i was completely able to disconnect it from the legitimate circular network and in further attacks uh we'll see how we can use jamming
attack to force a device to disconnect from a legitimate network and connect it to a fake network and then get all the data traffic flowing so this is an erfs calculator that you can find on screenwave so let's say after reconnaissance you find out the frequency your frequency is 2 1 4 this is where you see a huge bike using a software defined radio you just go to this here i've seen calculator type in the frequency and you will get the afc number or let's say you figure out in your fcn number and just click on the frequency thing this is available on it's an online tool you get to know the uplink and downlink so 2114.20 and 1924
or 20 these are the frequencies which are basically being used by your device to communicate to the nearby cellular network what you need to do next is to jam the downlink frequency that's the tricky part so this is the script that i had been using now this software over here on the left side uh which shows some blocks interconnected and everything this is gnu radio gna radio is an open source uh software based on python and python and c plus plus you can use this to generate different waveforms and you can transmit and receive data over the air and a lot of stuff especially if you're a communication student this is a tool you should be playing with a lot
using a cheap rtl sdr after jamming on the right side as you can see there's a symbol that's a semicircle symbol which shows that the frequency has been jammed and some of the other other slides you can just slide it to various frequencies and increase the rf transmission power to lower or increase the power of jamming remember do not jam too much as this could cause the device to be completely disconnected and go into a very different state where it will not even try to connect to any other cellular network and just remain idle this is some this is a kind of a security mechanism being provided by a lot of vendors especially some of the very
great israeli vendors i've seen this they're doing it's a very great security mechanism and it's a very nice way to you know detect oh someone's trying to hack your device over cellular network you know just sit there don't do anything let's quit let the hacker do his thing we wait for half an hour 45 minutes nothing happens then we again try to go and try to connect to the legitimate network that's the way it works okay now this was the first attack now this jamming attack that i described we'll be using this to deploy our pseudo base station attack why would i do this thing is as soon as you power on your device your
smartphone your iot device or even you start your car it knows what frequencies are nearby being used by your cellular company because this data has been is being transmitted by your telecom operator to your device and it's resides as a cache into your modem so it directly will go to go and try to connect to those frequencies through jamming we force it to disconnect through those frequencies once you understand what those frequencies or what those ear f sense where and then at the same frequency or frequency just a different offset we deploy our fake network with uh all the fields like uh mcc mnc mg team z so what are these fields uh mcc stands for mobile country code so
when you're sniffing you can come to know what is your mobile country cover then mnc is your network code so mnc is unique for each and every telecom operator let's say vodafone has a different mnc and then three has a different terms and somewhat mg is your user's unique identity over cellular network it stands for international mobile subscriber identity so let's say you are coming you're going from ireland to u.s and let's say you're on vodafone so how do they recognize for you're from ireland or you're from norway or you're from india or india so mg is your unique identifier it helps you recognize oh this guy is coming from here we need to provide him roaming services we need to
provide him data packs data services and so when you're in your home country so let's say i'm currently a subscriber of some telecom operator here in ireland so i have been assigned something called as timzy so tmz helps me helps the telecom operators to locate whether i am going from dublin to car to call away where am i exactly your telecom operator has every or log of whatever you are doing where you are roaming what services you're using so timzy comes into the play when you're in your home network or you're roaming in your own country or let's say european union mg is global wherever you go they know that you have gone there you are there for so much
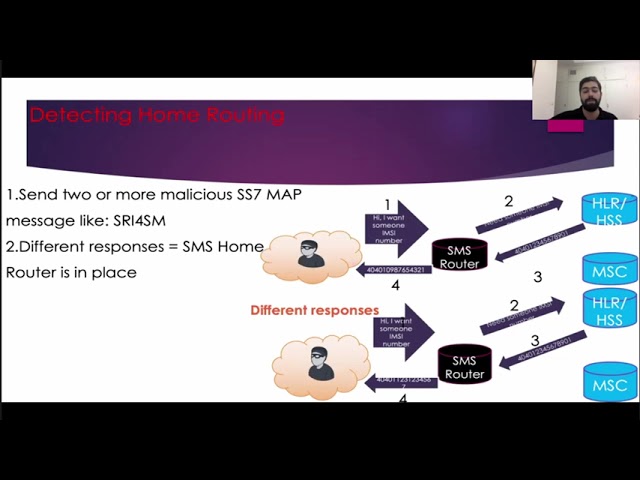
time because the telecom operators over there they send data back to the your main operator and they are always talking to each other using ss7 or different protocols okay so we deploy of cellul uh pseudo fake cellular network using open source deploy deployments like srs lte for 4g network this is a very famous or i would say of one of the best deployments of available right now for 4g networks and open bps open bts is old it's now deprecated the main there's no more maintenance going on but it's still one of the best choice you can also go for osmocom it's an amazing 2g implementation if you have a software defined radio in case of 4g now comes a big trick the
big hurdle in 4g networks in 4g we have something called as private keys these private keys are basically used for mutual authentication in gsm in 2g and 2g networks what used to be that let's say you are a subscriber of a certain certain telecom operator and you try to go into your settings try to connect to a different operator there was no mutual authentication you could actually fool different operators to connect your device to the network in 4g this is not possible in 4g you have to share something like hashes of your private key to your telecom operator then that hash goes into the management entity and those hashes accompanied oh this has is present in my database this
guy belongs to my network let's give him access if this does not happen you won't be allowed to use any of the services and in in such situations so let's say you are using a commercial mobile operator sim card these sim cards are not going to get connected to your fake network because you don't have the private keys of those sim cards right so what do you do well gsm does not use mutual authentication right we just force the device to switch back to gsm and tell it no 4g network is available here please switch back to gsm it falls back to gsm on gsm there is no mutual authentication the device connects to your fake network
and starts sending data all the way or you can use a programmable sim card cismo com is one of the best windows to do this and after this off after analyzing all these stakes and you have you are done with your entire setup then you start jamming and you jam you keep on jamming you're jamming until and there's a device connects to your fake network and then it starts throwing the data so this is my test bed that i had used a laptop for with wireshark and my 4g network deployment a smartphone for test purposes this smartphone was basically used this smartphone and the target device connects to the usrp so that's the usrp which runs your 4g network the
smartphone on the target device uh connects to your network the smartphone the reason why i use a smartphone alongside with my target device is because on smartphone you can see different statistics of how what data rate is being coming on and you know what other characteristics of your pseudo network are able to be variable you are able to see because if you try to do the same over let's say an iot device or electric car you won't be able to see all these things a smartphone rooted smartphone with some amazing apps uh can give you a lot of information about this so this is what you get once you start sniffing and once you deploy it and
the what whatever messages you get so over here as you can see the one which is highlighted rrc connection setup complete attach request pdm connectivity request so these are some some of the initial steps that needs to be done in order to you know uh identify a device and connect just like we have tcp handshake there are some handstands that need to be done in cellular networks after which the identity is confirmed and then your granted request as you can see below yeah so authentication response security mode command and then cipher message begins this happens in very later stage encryption begins at a very lateness before that whatever data whatever basic communication happens it's all in plain
text this was a big flaw in 4g using this flaw you can easily study oh at what frequency is a cellular network running what is the base station id how you can even track users how many users are connected use or to the specific cellular network or that specific cellular power which is nearby in your vicinity those are very sophisticated attacks and you need a lot of great radios to carry out such research so at below uh sorry below you can see here mcc says return india or the reason why i have uh you know masked this information because this is all very crucial information and anyone can use this information to deploy the fake network
so that's the reason why i have masked i don't want to get into any legal troubles mcc is india india has its own code i have done this i had carried out this research work uh in pune a city based out in maharashtra of india then you have an mnc so mnc what is what tells the network or which network are you in that's what it is and then it also tells the state so where it says maharashtra so it's a state in india then you have mma group id so remember i said mme is the one who manages all of your authentication and integrity and cryptography stuff once you know your mme group id
you can track users oh this user belongs to this group id his encrypted key resides over there and if you are able to break in physically mme you can get access to the private keys don't do that then you have mme code and then you have timzy so these are some of the very crucial inform and this is all available in plain text you just need a rtl uh rtl sdr and bioshock just need to pipe it to irish and wire would dissect this things for you so once you get all this information and you study all of these messages one by one one by one now what attacks can you conduct using all of this information downgrade
attacks as i told you because in 4g it's very difficult to force a device to get connected to your 4g network because of the hindrance of the private key not available you just downgraded you just tell the device you know hey right now over here in this vicinity there's no 4g network running please go back to gsm and the device will be sure if there's no 4g available and go back to gsm but uh gsm has one issue there's not enough bandwidth over gprs and edge network that's a big issue so the second thing is using the list of nearby area of cns or arfcs i was able to perform a redirection attack this is
one of the most biggest flaw in 4g this was revealed and it has been fixed in 5g networks now so the thing is using your pseudo base station network you can tell a device if he is trying to connect to your network that you are not allowed to connect to me but yes i can give you access to my gsm network and tell him the frequency of my gsm network the smart the device goes and connect to your gsm network this is a huge flaw it should not happen i mean you're tracking you're tricking anyone you're taking users to connect to a cellular fake cellular network and this has been fixed now in 5g specifications
then once the target device ue is good is getting uh it's connected to your pseudo network you can obtain all the ip packets whatever data has been flowing back into the internet and your device and everything using this you can use gps spoofing if you know how to do that let's not get into that that's not the topic right now sms proofing you can even manipulate the 80 commands once you have access to the hardware let's say in next uh slides will come to know how we can combine all of these attacks and create a very big supply chain attack and compromise the device completely okay this is something that is the data you will find in your fake network once
that device gets connected and has been fooled okay so i have masked the ip addresses where it's connected to over here you can see gps log vehicle info sensitive credentials blah blah blah this all is a malform package it's a packet data this goes to the cloud the ips are hard coded of the cloud into the device's firmware you are just sitting in middle it's a magnetometer attack a device getting talking to the cloud you're sitting in middle you're watching observing all the data okay now let's say over here there is lighter to the longitude you do a gps spoofing attack on the device you see the change in nitrogen longitude here now if this was in case of an electric
vehicle let's say you have a app which shows where your car is right now it shows uh uh it might show where you're connected to and later on it will change your location you won't be able to figure out private apn attack so as i said apn settings are present in your smartphones uh these are pre-configured if you have a smartphone in electric vehicles and all these things uh it needs to be configured so when you buy a vehicle and all these are pre-configured by your manufacturers this is how if you are using a 4g network this is how you would set up a uh apn so first you go to your settings of cellular network scan for the network in
this case the name is 90155 this was the name given to the network set up a private apn so srs lte tells you to set up a private api so that your data flows to the network very easily once you create this you just put to under to put the name name is srslt that's it nothing else see your username and password combination is given but we don't need to use it okay and this is in the case of smartphones in cars and iot devices you need to have this combination otherwise security is compromised and this is the bandwidth i was getting on the after it was connected to my network and the final vulnerability that we will
be talking about is 80 command so uh cellular communication relies heavily on the baseband modem or the so-called basement processors in the smartphones and they are responsible for all the cellular communication that happens baseband modems are nothing but they are where they are they execute 80 commands and make sure they are communicating through your antennas to the nearby cell phone tower i was able to successfully been able to sniff the baseband communication from the target device and analyze the live communication between the device and the smartphone i was able to acquire a sms and call information i'll just show it how it was yeah so this is how the attack is carried down this is a usb to ttl
converter uh this is used to connect to the interface or swi or ui interface of this device and on your terminal or laptop you get to so you you get all the information if you want to know more about this just go to smoke they have explained great in depth once you are set you have set up all these things i have used tool called qc super so this is basically a python script which once your hardware setup is complete it interfaces your laptop and your target device and make sure the communication is happening between them synchronously and then you can see and then you have to just pipe this data wireshark live and decrypt the traffic
so you have to pipe all this data to wireshark this is some this is this is how you start getting the data from your smartphone uh baseband yeah this was the thing so this sms's are usually encrypted in this case i was able to get you can see here zero four six zero one four is the otp for transaction of this this this otp is added for 15 minutes from the request please do not share with anyone well you just shared with me so i know what the otp is and we were able to use this otp to make another device subscribe to the service and i mean a huge blog and why are we able
to see this in plain text because we are logging everything from baseband remember sms is coming from your cellular tower to your smartphone from your smartphone it's going to your processor processor is decrypting it we are reading those decrypted messages no need of encryption you don't deal with encryption at the hardware layer everything has been done for you from the application your kernel and everything you are reading directly from the chip okay what are the mitigations so along with jamming detection i i feel that vendor should also provide driving prevention mechanisms for pseudo base station attack it is advised to use a two two factor authentication and for private api attack it is better to whitelist necessary ip and request
made by any other ips so there's only specific ip addresses the device will talk to also one can ask the telecom operator to provide username password combo for a pin configuration this will improve your security and in case of 80 comma vulnerability it's better to disable serial communication ports or pin outs and execution of system level commands or serial imports because sometimes modems give direct access to their linux interface and you can just execute linux commands and make system changes questions
[Music] yeah yeah does sorry does the phone not then just step to another frequency it tries to so in that case you have to keep on jamming that's what i said you have to keep on jamming and jamming and jamming at some point it just stops looking for it and then once you know what is the frequency the smartphone is likely to connect to after jamming multiple frequencies you just deploy your fake network at that frequency it tries to go back to that and it's connected to your network you don't need to do anything else that's how you fool the modem anything else any other questions
okay okay okay sure so thanks thanks a lot