Lessons Learned from a Bug Bounty Operator
Show transcript [en]
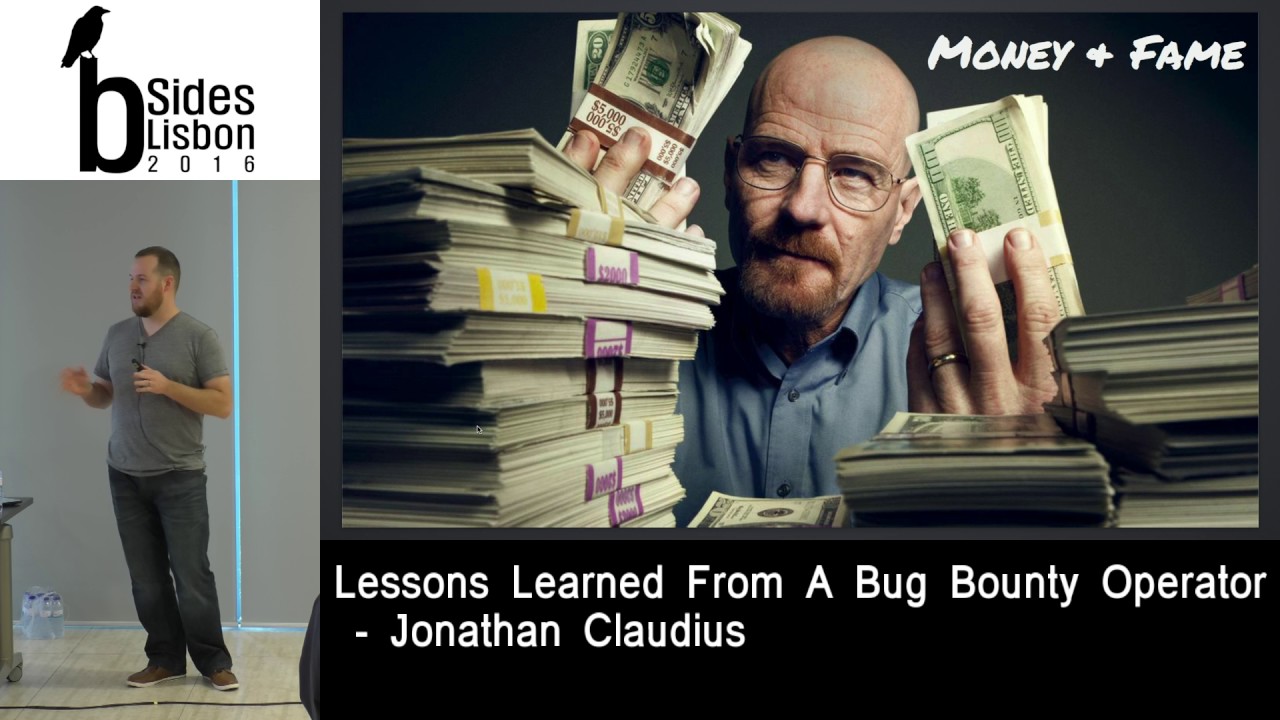
got audio all right well as we said we'll be talking about lessons learned from a bug bounty operator today a little bit about me first i joined Mozilla about a year ago I hit my one year anniversary about one month ago so a little over a year and I've been in the IT and security space for about 15 years doing mostly offensive work but I've also done some defensive work as well appends has sort of been a specialty of mine and it's been an exciting time for that at Mozilla I'm the product owner for security assessment so I spent a lot of my time doing risk assessment vulnerability assessment throughout modeling exercises and most importantly penetration testing
so those keep me pretty busy but when I'm not doing those things I'm working on the Mozilla bug bounty program working with security researchers day in day out file fielding bugs that are coming in for our products and services working with development teams try and fix those vulnerabilities and getting researchers paid for their contributions yeah I think that's about it for that piece what I want to talk about today there's really two main things that I want to hit home two things I'd like to leave you with one is if you're going to be operating a bug bounty program what are some good techniques that you can do to really make your program work well
and then also if you're considering as like a security researcher wanting to participate in a program as a bounty hunter here are some strategies for you to do that better at least what am I seeing from bounty hunters that are really successful in our program there's a couple background bits of information that i'll be sharing with you before we get to that point but that's what i'd like to leave you today so fundamentally what is a bug bounty program what is the bug bounty when i think about this topic I think about how I want to explain this to my parents they don't understand anything that I do when it comes to security so I have to
think about how I'm going to relate to them and how am I going to bridge the gap to help them understand what this thing is can I get a quick raising hands for those of you that know what a bug bounty is or participated in a bug bounty okay how about half well the way I think about it is they just go to the root of the word you know what is a bounty in this case I think about it is when you were a child you have a pat a dog cat whatever and that pat runs away or you get that pet is lost you think about one of the things that you would
do when you need to retrieve that animal you would go to the community to ask them for help right because you only have yourself you can only be in so many places but your dog or pet might be you know miles away so what you do is you write up this reward and you say my pets loss I need help here here's what the pet looks like here are the details about the fact is how you get in touch with me here's how you let me know and help me retrieve that animal well when I think about in terms of bug bounty programs in this case the puppy in this case is security vulnerability we're
asking other people to help us find something or engage in the community to get help finding something that we couldn't find on our own and the way that organizations do that is by describing public intent to pay security researchers running security bugs in their platforms it's not an engagement it's not a consulting engagement where have a very clear task this is an open challenge to the world to say please come back on our stuff we'll pay you for security vulnerabilities that you find that are impactful for our products and services and the way that we do that at Mozilla much like other organizations instead of providing that piece of paper that we would nail to like a telephone
pole or plaster all around town we put out a public website the basically says here the here is our intent here are the guidelines for how someone would participate in our program and the reason why we need to do am I getting feedback okay so one of the reasons why we describe the program in the way that we do is that if we relate back to the puppy scenario with your lost pet we don't exactly know what these bugs look like we don't exactly know what the bugs are if we knew we'd fix them ourselves so the reason the goal for the bounty program is to ensure that we provided enough guidance to get people involved
to know that they are actually finding things that we care about and also give them some sort of sense that they're actually going to get paid the end of it is actually going to be some reward for participating in the program so i want to touch a little bit on history when we grab some water first because i'm being dry so a little bit about bug bounty history if we think back to 1995 and netscape was one of the first bug bounty programs out there providing bug bounties for bugs found in netscape and when that organization ceased to exist and was purchased by AOL the browser source code was open sourced and translated into mozilla organization
eventually became Firefox but at that time Mozilla was basically one of the early bounty programs at the time and Mozilla sorta sees itself as one of the early pioneers about bug bounty programs that's at that time there really weren't a lot of other bug bounty programs out there and what we've seen is over the years we're getting more and more people participating in bug bounty programs more organizations creating their own bug bounty programs to get help on security issues that they couldn't solve on their own we even have it organizations out there like bugcrowd the organization actually created this diagram I slit from their website in hacker one that are more or less like facilitation engines my phone is ringing
there are facilitation engines for helping organizations that don't have the resources of the set up to create their own bug program on their own so these organizations specifically bugcrowd and hacker one and those alike are really helping make bug bounty programs extremely main straight so a lot of organizations are running their own bug bounty programs working with the community helping reefs are getting help getting help from research researchers that they get paid for finding vulnerabilities in their products I turn this off and I just go no audio you okay well it's really irritating I step on you guys to all right this one all right well I'm going to continue on I just was hoping that maybe
we could solve that so why would an organization run a bug bounty program why is it becoming much more popular for people to start participating and creating their own body programs to get researchers engaged for me it's it's pretty simple but some organizations might say well I don't want to run a body program because I don't want to put myself out there I want to put my software and in the meat in the limelight and have it the risk of finding vulnerabilities in being an embarrassment so I think a lot of organizations think that way but there is reasons why organizations are successfully getting bounty programs and using them within their within their security program so the first thing at
least for me at Mozilla one of the one of the most important things to us are securing our users so when you think about the value of a bug bounty program I think about how is it going to protect my users and eliminate security risks within my product in this particular case we find that it really does help reduce some of the zero-day risks that we have within products so we if a security researcher is going to find a bug in our product and they're gonna they're most likely going to find bugs and products like software vulnerabilities we're going to a gurney exists at least we're providing them an avenue to work with us and get rewarded
and paid through an approved approved channel and if we do that we provide that Avenue we really do reduce our risk of someone going out there and just going for publicity stunts on a blog the next one is community Mozilla is really keen on creating communities and getting people engaged in our products and services so as part of the bug bounty program we get to tap this huge pool of resources of security researchers that are interested in our products and willing to help us find vulnerabilities in those products and in a way everyone sort of brings their own piece to the puzzle like everyone has their own experiences and background and having all this put together it really does
help us find security vulnerable using our products and resolve them quicker than we would have been able to do if we didn't have a bounty program the other aspect of this is confidence it's twofold it's the confidence that you have in your product and showing that you feel you've done as much as you possibly can with the resources that you have to fix find and fix vulnerabilities in the product but there's more to that it's also like a maturity thing in the sense that you feel comfortable enough to be able to put yourself out there and say as an organization that you're mature enough and willing to compensate security researchers to help you find and fix bugs and you're open to that
discussion and you're willing to participate I can tell you that as a person at Mozilla that evaluates products and services that we would use within our organization the other aspect to this is confidence in other people's products that I'm purchasing and using is there any way to kill the sound all right okay I can see you guys all wincing in the end the head back right background so we'll keep going so why would you want to participate in the bounty program so this is the other side of it we have we have a program we've decided there's a reason to do a bounty program but what about the people that want to participate in our program why
do they participate in our program one of the motives for them and one of them I don't know if you would all guess this but for me this really hits home for me as like a as a hat as a self-defined hacker a lot of people participate in our program just because they're curious they want to look in those dark spaces they want to take something put it on the bench take it apart take all the screws out of it lay it on the table and understand how it works so we get a lot of people that participate in our bug bounty program they submit security vulnerabilities to us but those people aren't seeking bounties so a lot of
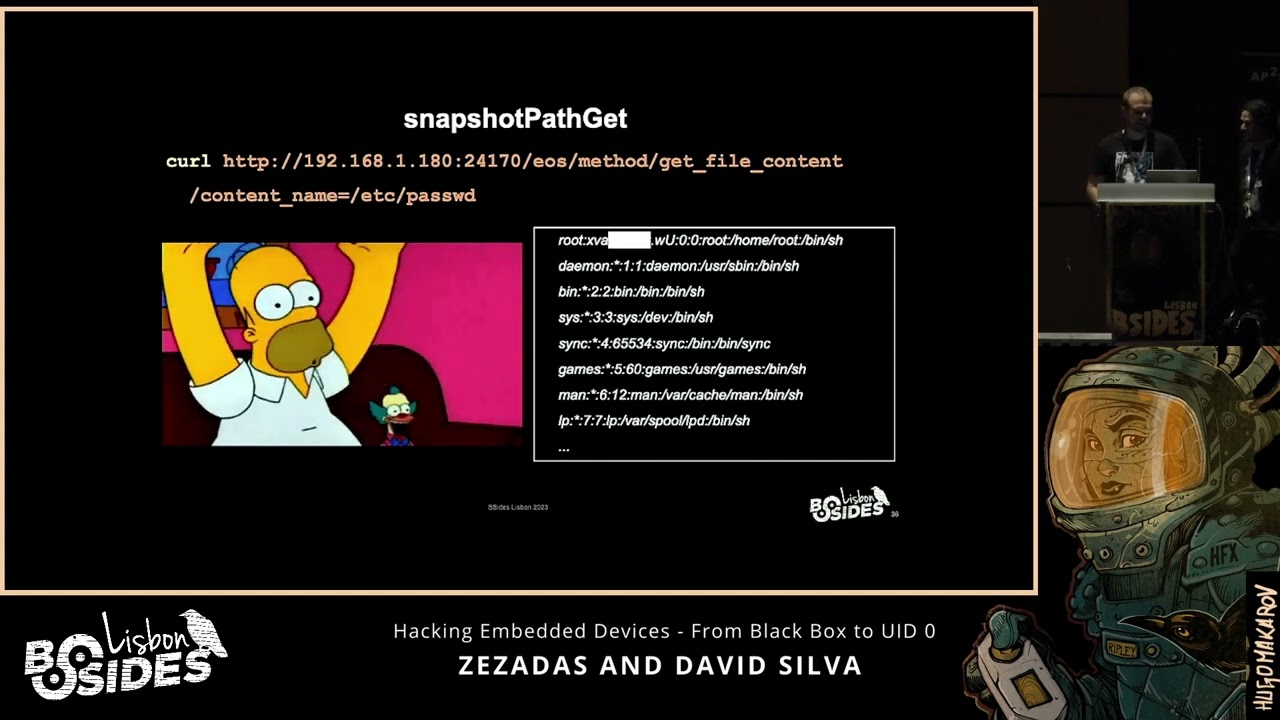
cases they're surprised when they receive a bounty you know that they're being engaged to provide payment for something that they didn't think they were otherwise gonna get paid for so that's one big one the next one I think is going to be pretty obvious is money a lot of people start making a lot of money doing bug bounty programs bookbinding programs started off as like single dollar amounts small dollar amounts hundred dollars thousand dollars and nowadays you can pull easily not easily but you can pull bounty numbers as the high is hundreds of thousands of dollars so people are making full time living making submitting bugs to these bounty programs and it's become a big
business and I think over at least in the last couple years we've seen a lot more people coming and working with us that are full time values the other aspect of that is Fame a lot of organizations provide Hall of Fame pages to indicate those researchers that they've worked with that have really helped them and done a lot for the program and researcher the gamma fication of that like making it a game to try and be on the top like to be the best security researchers really identify with that and they want to be on the top they want to be the top ten on that particular program and that also translates to career development if you
are the top on that particular program you can you you have something on your resume on your CV that really differentiates you from other people in the market and as far as it also to career development we have a number of people that work in our program that are college students so they're people that are just starting to enter the market and they don't have these skills yet so they they have their classroom activities but in addition to that they using the bug bounty program to really cut their teeth and start to learn how to operate on a on a scale that major organizations want to compensate them for so in some ways we use the program
to identify top talent that we want to bring onto our team and want to bring in to bring bring in house and full-time full-time make them part of our team so that's just a kind of the beginning stage here to get us started some of the reasons why someone would run a bounty program why bug bounty programs are important this is my indicate to segue to the next section into how do we run a good bounty program and I feel like that's something that we do well at Mozilla so I feel like I feel pretty good that we've got a lot of those aspects within our program today and there's always times where we're really
trying to improve on the program we're trying to look at it from a bunch of different angles to make sure that we're being competitive part of this is getting mindshare from security researchers if we can be an interesting program to them we provide enough interesting targets for them we've got their time and interest to come play on the program so one of the big things that I think is really important about having a good bounty program is working with a bounty committee or hot establishing a committee within that your team that would help govern that program and we do that at Mozilla we have a group of about five or six people that meet every week and we discuss all
the existing open bounties what the risk levels are and if the risk levels are high enough whether that person is going to receive a bounty so these people are like your mind shares so if you want you want highly technical people and you also want people that are going to be part of the organization so they understand the products and services that you're offering and they understand the impact if one of those products or services have a critical vulnerability that would impact the its abilities to deliver to a customer so that's one aspect of it the other aspect of that is doing bounty triage it's really important to one have a bounty program but it's really detrimental if you don't
respond to researchers in a timely way so in this regard the important aspect here is to get to that researcher as soon as possible so they submit to us we have to maintain an SLA to work with that researcher within 24 hours so they're not submitting a bug to us it goes into a black hole and then they hear from us from six months and say hey here's a bounty doesn't work that way in our bounty the way we operate it were responding people within one business day in some case for responding them within minutes of submitting that generally depends on availability of the person that's doing the triage but the important thing as do
in doing triage is not necessarily for you to fix the vulnerability and get that person paid immediately immediately the issue is for us to assess the impact of that particular vulnerability to the organization because if the impact is really high it means that we need to rally the troops we need to get people involved and we need to be part of that discussion immediately and start getting all the people in there to fix the vixa vulnerability and get that thing sorted out you'll see on some of the slides here as we go through that I've including examples one of the things that we do at Mozilla is that were really open organization so whenever we
have a process or a technique or a thing that we do you try to share that openly with community so that you can look at it you can critique it you can help us improve it or you could use it for yourself if you're operating your own bug bounty program here are some tips and things and how we do it we do a daily rotation so there's a single person like myself that might be on any given day when a vulnerability comes in I'd retreat eyes that vulnerability and work it to its completion and then the next day we switch off to another person and the reason why we do that is because bugs can come in at any time of the day
so we don't want it we want some that tree has person to be fresh ready to go so that when that vulnerability comes in they're ready to rock and start working the issue the other thing that's really really helpful and having a bug bounty program is establishing a severity level or severity levels a ranking scale if you will for how you're going to assess vulnerabilities it can be as simple as this just high medium low you can have interim levels you can even have it matched your existing wrist process within your organization if you talk to someone your organization the risk organization they might already have an established set of criteria it's really important to standardize those and in
the sense that when it comes to the bounty committee assessing given vulnerability for its impact the organization housing or house that person going to eventually get paid we're doing it in a pretty stable way so like remote code execution this particular piece of code equals this it makes those conversations with the bounty committee when they're assessing whether or not a boner ability is going to be paid it makes that process move a little bit smoother so it adds grease the wheels if you will i also have an example of our severity ratings here below you're welcome to look at that on your own see what we're using I think it's not so much an important that you
use our scale because even this slide right here is not our own it's just that you establish the scale so that you can set a bar for payment and we set our payment around like the middle of the road about half way so that when people start hitting that that that threshold is starting to get paid and if they find critical vulnerabilities they're going to get paid absa stantial amount more money another thing that's important about running a bounty program is an operator is that you have to acknowledge the people that are participate participating in the program when someone submits a bug you want to always thank them regardless of whether or not you know that bug is going to be paid or
whether that bugs a duplicate or whether it's not even a bug at all it's important to make sure that we're validating the folks that are coming in and participating in the program so they even if they struck out that they can come back and they save some dignity they're not feeling embarrassed that they submit something that didn't matter to us if it wasn't really important to us because we do value their contribution and it's important that you do that because those are the people that are going to come back and participate in the program and probably find the most interesting bugs and a case where a bug is awarded a bounty I'm a firm believer that it needs to be paid
out as soon as possible and when we do that we really we start a feedback engine with that that individual and they get an indication that we're serious about security vulnerabilities in our products and what ends up happening is when we do this and we we execute on this quickly we end up with like a flurry of that that person if they're new to the program they tend to really work with this a lot so it's like someone's first time in the program they say meta bug to us we immediately pay them and then it's like six or seven more bugs right after that so you can really really dry participation by getting a successful result under the table that
person knows you you're running a serious program so patience so this is the not-so-great part of a program sometimes when you're operating a program you get these great bugs and they're perfectly documented and you have exact POCs and everything's perfect this is not that case so there's take cases when we get offensive language we get misunderstandings about the circumstances of a given bug and i'll gather speaker going on scroll again we get ransom videos of people trying to explain the bug to us and it takes you to like the 29th minute before you actually see the bug that's always exciting we have demands for payment and just straight up like disrespect and I'll get into one or two more examples
of that later as we go I think it's important as your if you're operating in a bug bounty program that you keep your patients are that I'm sorry that you keep your cool and you keep it professional there's people have thrown all kinds of terrible things my way and operating the bounty program in some of the bad submissions and it's important for us to just sort of keep cool work through it try to stay professional because there's times where we've taken someone that was like a really bad submitter like someone that's just driven us nuts and in the bounty program it's like 50 bugs in one day they're all low risk and they don't matter to us
particularly and we've been able to convert those people just by being nice and staying patient with them and working for the process and educating them about the things that we're looking for so I think that's a really critical aspect for operating county transparency and openness I think as Mozilla this comes really easy for us because we operate in the open on a lot of the stuff that we work on I think the important part here is to have a process where you can communicate what the program is and how it works but I think it's also important to involve security researchers as part of the workflow and solving the problem so what we do at
Mozilla is we use this system couple of zila it's just a ticketing system when a bug comes in we obviously have to keep it private until we fix that vulnerability but while we're working through that vulnerability the researchers engaged with us we have the developer engaged we have myself or one of the other triage people involved so we're all working together trying to solve the same problem in the same workspace so there's no additional communication there's no I tell this guy and then I got to go work with this guy it all happens in the same bug the security reach a researcher sees that we're actively working on it and it really helps in a lot of ways to prevent
that sort of case where someone saying where is this bug like where is it in your process are you working on this is this important to you in a lot of ways it just says right up from the get-go that that it is important to us we are actively working through the issue and they're part of the solution and we all we also do is we take that full conversation like everything that we communicated about when we're done with the bug and it's fixed we'll open source that buck so you can see the full discussion you can see what the development side you can see what I said you can see with the security research
you said and for me that that really really helps show other security researchers how we work and it also gives them indications as to where we might have other problems in other parts of our software that they can go and attack and get bounties for so in a way it's like little breadcrumbs we're sprinkling around about where our problems are which is which is bad right we have problems but the other aspects of that is the it gives other people good indications as to if we didn't solve the problem completely here's another place where you can look and we have in cases where we thought we thought we had solved an issue security researchers saw a public
a bug that had been recently publicized and said what about over here what about this application and it really keeps us honest in a way I feel like that's a really helpful part of running your program this if there is anything that I say today about running good operate operating a good bug bounty program this to me is one of the most important thing and it's not the public aspects of it it's about taking the feedback that you get from security researchers looking at them at a higher level and trying to identify friends of bugs and why your wire faced with these certain bugs and trying to develop guidelines and procedures to really start to catch
those bugs and knock out entire class of vulnerabilities and we've done that I've got a couple links here I don't think it's showing up very well but we've developed TLS guidelines for SSL we've got developed guidelines open for openssh as well as our web count our web security guidelines so those things really helped us take entire vulnerabilities or classes vulnerabilities off the map
sorry guys uh it stopped when you open the door thank you yeah so developing these programs are developing these guidelines really helped us make our program better and anytime you're operating in program if you're not looking at the issues that are coming in and trying to identify trends and common issues that come back to you over and over and over again and trying to fix them at a higher level you're missing value in the program like you're leaving you're missing stuff that would be really really important to to advance the program and what we see with our program is that by doing this we're not dealing with the same bugs year over year we tend to have like a wave where
like if cross-site scripting was important earlier this year we've addressed it with CSP and specific technologies we're basically that bug classes guns so now we're off on to some other tangent I'll talk a little bit about that in the later slides as far as like how to do a good bounty hunter bounty hunter on how you can sort of chase along with us and make it effective for yourself I guess that's a good segue into that aspect of it let's talk a little bit about what we're seeing with good bounty hunters what are they doing what what are they doing that's so different that the differentiates a good bounty hunter from a bad bounty hunter and I don't mean to
say that there's any bad bounty hunters but there's certainly levels of experience and quality that we experience in the program and I want to highlight the ones that we really enjoy the first one I think is pretty obvious if you're going to submit a bug to a bug bounty program you need to have a POC you need to have a proof of concept that demonstrates the bug I we get these i would say on most submissions i think this is pretty obvious what we don't see on some submissions is safe reproduction steps which i think is really important for for when you're submitting those bugs to the bounty program you know if your if your pocs throws a shell to your
remote machine it doesn't really bode a lot of like goodwill the people that are operating the program like okay you're trying to throw shell on my machine great so these are the sort of things that are interesting I don't think people consider them as issues but for me it's important that we're providing a safe way of communicating so in a lot of ways if you're giving me some proprietary format as additional steps that I need to do so if you can give me something as tax and make it clear and you can demonstrate the bug with and just with a picture and show it to me usually it helps sort of move things along quickly what up what I
think is also important here is that you also want to describe why it's an issue I think a lot of times when we're doing technical security exploit words we think about the class of the vulnerability and why that class is important but it's really important to understand the potential impact of that vulnerability to the organization if you can connect as a bounty hunter with an organization's impact and in back to their bottom line you are going to get better bounty out of that out of that program you can draw that connection for them that they wouldn't otherwise been able to draw on their own you can really do a lot of crazy things the yeah and it
really does help with an impact assessment if that organizations doing like full-blown risk management they plug it into their risk process and they see that this is like the highest risk on the radar the other thing
you
back to the bounty program and then also write a blog post and put it on Twitter the same day so these are sort of like expectation building things that you want to look at the program and understand like what's acceptable for the program vuze when you open source open source that buggy in submit to the bug bounty and maybe same exact day before the issues triage basically zero dings so it doesn't really help us I mean it helps us let me know but we're a little bit i'm eight ball at that time so it's really helpful to sort of be up front ah the other thing pay attention to eligible sites get a lot of sniff
folks to us in like custom code application that's listed on like someone's personal blog and their wordpress blog or whatever and it is not part of our program so you love to the exhaust a lot of effort a lot of time without reading instructions and the pine bugs but they find bugs and things that were not once pay on that are part of our program so if there's one thing that you think about what far as instructions make sure that you look at eligible eligible sites or eligible properties and in most organizations and most program programs going to make that clear the other thing to consider is the book classes that organizations care about there's some bug bounty programs
don't care about like entire classes of certain vulnerabilities and we have we have pieces where we've seen where people will like exhaust as much ever they possibly can on a very specific type of exploit and like yeah that's definitely yeah it's a wiki you can improv it so those are the sort of things that we see out we do have a fact for our web bounty for when people are trying to learn this things like the image that I linked to you in the earlier slides there's a link to it later if you want to check it out and see what guidelines we have with our program uh this is an underrated one as well a lot of times we get people to
participate in the bug bounty programs and they feel like they should ask questions or just simply don't this is a really good way to get good information about what's important to us and I think the big part here is context if you can understand that an rce and this particular application is extremely important to us and our CES other application means nothing to us because it's completely isolated and completely segmented from our infrastructure that's important information to know and it might help you as a bounty hunter target some of the work and some of the sites that you really sweat your pie mom's time is precious so you can find ways to save time and really target your efforts
keeping you can get more success powder ah see Oh in addition to this one of the things that we find a lot a lot of good bounty hunters work with us on is that they find a vulnerability or they're looking at a public bug that we've already disclosed and publicly disclosed in figs and they find other classes of bugs in the same place so in case were like there's a input validation mug and we didn't do a good job of actually solving that issue we solved for the problems that that was that was presented in bug a and good bounty good bounty hunters me look at that bug and said I wonder if they did this or I
wonder if they look at this this aspect of it so if you think about of it like incomplete hatches really interesting space we have a lot of money on us that do very very well just by looking at bugs that we fixed and maybe not completely fixed ah so fine s be very interesting category ahhh so scared both classes this one's a fun one for me because it makes my job more entertaining uh you know I've seen dozens and dozens and dozens of cross-site scripting vulnerabilities they're great and will pay for I'm totally then I'm not interesting to me but they're interesting the organization they're interesting to search properties than they have in this particular space
we find where but bounty hunters can be like specialists in a very specific type of vulnerability and especially in cases where that vulnerability is just not really well understood it's now well document it's not a bug class that other people are looking for and we see bug hunters develop entire tool sets around these obscure vulnerabilities there's like a really hard for organizations to really get the hands off hands on and because of that they do very very well on the bug bounty program and one example that I'll actually do a little bit more in a bit what's Hospital something may take over vulnerabilities sounds really bad I've region have you heard of hostile subdomain takeover
vulnerabilities okay so like for it this is good so this is actually a really simple own ability basically what it means is you you've taken DNS for a given web property you've pointed it at a shared hosting provider but you haven't claimed the V hosts on the shared hosting provider meaning that anyone that wants to show up on that vemos provider can claim that the main arbitrarily and just take over all the content for that particular domain so the impacts really bad especially if that pioneer provides SSL as well so not not only from skoo content and content over about to get it we'll talk about that a little bit but that's a really interesting one there's dozens of others
and if you can find your way as a bounty hunter into one of these niche faces not only we do well in our body program but you probably did well another bounty programs in spa so in a way you can take that one vulnerability and maybe sort of make the rounds for other organizations and you can really clean up how do we see another body hundred to do that this one that again now that underrated one I feel like these are extremely simple but they are key characteristics that define our good bounty hunters who are not so good climbing Mount Hermon just remember that like when you're when you're working in a bounty program the
person that wrote that code is eventually going to hear about that dude everyone who the prime fix it just remember that when you're submitting that you're eating respectful and you're not gonna sort of talking down have you missed this it's fine i mean it's not my work that you criticizing book i feel like when we get when that message is delivered to a developer they're much more likely to fix the issue if you're nice about and we work you know as far as a mozilla bounty our developers and security researchers are working really really closely together so if you're if you're coming you're coming at someone really hot about them screwing up well we're going to put you right in front of
that person so if you could be nice about it you can build a relationship with that person and sort of build some goodwill to get things started and it really sort of helps move things along and and I one of the other things that that you're doing by being nice is that you build a lot of goodwill with the bounty so if you know if there's a number of levels that that you working through with a value kilogram book from initial value verification of the bug towards the impact assessment all the way to bounty approval if you're nice and you you built up a reputation those wheels are going to get smoother we're going to know that you're this guy that
you can trust your code and feel confident that you're not trying to swindle us you're not giving is bad at pio sees the book shows other machines or whatever um you really do some interesting stuff here and what we do for people that are extremely nice and that are helpful and what we define is like good bounty hunters for us they really help us shape our program like we asked them for info you say what's working what's not working is this is this a good way to handle the bug is this should we be doing something different and those people we really we tend to ask the people that are extremely nice and not the jerk so
surprised so if you want to talk a little bit about sister and a little bit water to the park Union we're doing on time let's play mixed lining say so what I like success story um there's a guy about a new Griffin Francis out of Australia he's one of our what I would consider one of our grade boundaries and I want to share a story about a bugged with e submit that I i ended up triaging it was kind of fun and it just talked about subdomain takeover hospital something take over so this is gives you a sense for how impactful disposed was for us so it affected 50 domains so single to suck me take over we were able to take over a
single to me that's one to me this kind of found did he of them if he amazed that we had dns pointing to be health provider we're in the process of setting something up what we had it completed the sad yeah and this is basically in the bug its public bugs you can go up punch that mug in and see the full details of how that dog is free out how we worked with them how we were able to solve it and you know what the end result was even the domains that were affected in this case what was happening is we were building an app framework it was going to be based on github dada i
oh you're not familiar get hugged iOS basically github pages so the idea was is that you would host the application on yeah and then we would be able to deliver that education to Firefox OS and you know everything just sort of for it well that was an idea or something or prototyping and b7 the DNS names in advance to sort of get things going what Brandis realize is that our different found was that we missed a very important step of setting up that which is the establishment of the cname in an ISA github though this is how you claim of ye hose so get up Diana they have a single server our own money servers but
like a single bit stood up and then when it comes in it looks at all the repositories it looks to see who playing I give it to me and that's how they would serve content so if I don't have this file what ends up happening is our boundaries that are in this case was able to go in and clean all those domains and stand up scenes and make his own projects under that name so what happens is is that when you resolve one of these domains above any of the domain to be shared with us he can fully control that content and all he has to be is a github user um so again but families are interesting in
the sense that you handle traditional vulnerabilities cross-site scripting sequel injection all the sort of basic stuff but when you get into tight obscure vulnerabilities it's really interesting space because organizations just aren't prepared for it they don't know all the nooks and crannies of all these different obscure vulnerabilities there's generally not a lot of tooling around it in a case of something we take over there's really poor tooling around all this stuff meals providers generally don't do any verification of the media claiming so what was really great about this is that this was the first bug and up many that we work through to try and draw all the addresses within organization I'm sure if you do any sort
of like any sort of virtual hosting or shared hosting providers within your organization this might be something to take a look in to see if you have old dns records that are pointing to those deals providers or if you have dns that's pointing to wild part sir that's a if you're interested in that sort of stuff talk to me after i can tell you also it supports covers about wild part search at any rate what I feel the reason why I chose this example example is this is just one example of the beginning of a conversation that we have at the security researcher and from there we found tons of tons of more vulnerabilities after working with in
having a successful result so in my my vision if you look at this bug you can see this is an example of both of us doing the right things and for me when we do the right things when vyas found the operators do absolutely as much as we can to try and remember what the incentives are for the people that are participating in the program and if you as a bounty hunter can think about incentives of an organization and why they operate the dining program in the first place they're going to be a lot more successful and if we can take it there's a gap between developer conversations / you researcher conversation if you can
do anything to close that gap they're going to be more successful about anyone or just plain and simple and those are those people that we really want as part of our program and those people that we do operate with on a daily basis successfully to help secure a lot of our application so for me it's just so for me that's a really important aspect of it that was the goal of my presentation was the one that you win how to run a hit up operation or how to operate a good bounty program or hopefully I'm giving you some indicators of that also for those the other security researchers looking to be participants in about even
trip hopefully I gave you a couple tips and tricks that you can use if you want to start participating if you're interested in participating in Mozilla bounty program from dr. me after I'd love to talk to you about to find out which are interested in and maybe we can get a conversation going apt bootstrap that's really all I happy you guys so yeah I think some time for questions so glad the speaker's calm down into a much more from the operation side so that shot at the beginning control over companies yeah it's obvious that s concrete love the organization something even fortune 500 so for those of the organization to be really easy golden are they on the opposite with for the
researchers but of course so we can get what from your experience what's the number of internal resources that you think you did not who said if I certain amount call you coming in I think it depends on what your volume is I can tell you that Mozilla we have about the web bug ready tired i think it's like 42 properties that we have ineligible which is I think a lot greater than most organizations out there a lot of organizations really really tightly scope their their bounty program it's got to be in this application this curse of the minute it can't be any of these classes own abilities we operate a pretty wide open one so I feel like
remarks those in the sense that we deal with a good amount of input from people and Mozelle are not big company where 1,000 people which is still good size but we're not like a massive giant we operate the triage game with about five people and the ricotta and I didn't cause you too yeah with with a one-day as allies what's the ratio between two and four boys it depends on the researcher very very much researcher centric so like if the researcher comes in they read the program and they like they do the steps though describing they tend to be really successful right off um I think we do get a lot of submission they're like waste all my voice to you
to get rid of there's always lots of knowledge if it's probably causality I feel like they pay a property of mike maybe but half the submission to come in maybe more so I feel like we've got a good a good balance what happens with researchers that like what I would classify is not good researchers they don't take the last long because they're not being successful it's just one of those things that they're only willing to try to so long they go on doing this stuff and then every now and again you get a couple researchers that are just trying to cut their teeth in things and we try to work with them but it's like
if they're not successful they're going to peter out pretty quickly so it's like that's why I think it's really important for for people that are interested in value programs to get success early on because it's going to help feed the you know feed that hunger to play a while any other questions actually is it ok Vito ever you say it eighty percent of the price on the research parents would submit a 10 on the well it's already spread more widely well there's some that are really successful it's funny that you say that because from a quantity perspective really really successful researchers tend to throw a lot of things in the wall uh every most everything that are
good researchers submit almost all of its days because they've done their homework it done they've looked at our guidelines them understand what we want I don't make great interesting question or more I machine is the same food researchers that are submitting the majority of your book malin bottom I wouldn't say that that it's the majority they're probably maybe ten percent of the overall like are really like regular people we probably have like ten ten people that are just like pretty solid that are mostly participating all the time and then we have like a wide range of other people just kind of popping in so oh hey you know there's new motor billion in tonight's easier yeah here's
your something to chase down pizza any other questions sir do I may evoke the peak eight oh yeah we do do you have a lot of duplicates mostly bugs that are in the process so like it's surprisingly enough and it's priceless me to this day we do get like a what i would call birthday attacks where someone you know we go so long without anyone finding a given to owner ability someone finds it on a monday and then some someone else like completely unrelated submits that bug on Tuesday it's like how we went that long and like to write next threes on there it makes you wonder like these guys working together they're like what's going on but yeah so we use the
ticketing system so in a case of bugzilla it's really simple for us to like oh that's this bug resolve I would like to think that we have more but I think we have such a wide scope that we support that generally people aren't tripping on each other for duplicates so if the issue is an issue we're going to work through to completion and the idea is that we're not going to see that but again and this is especially the case when you wipe entire blood classes off the mat those are really helpful so it's like you know you deal with it for so long and like all right we need to find a real solution to this
problem how much I'm relying on your program for your own internal coverage of the applications and how much do you know we are internally need to make sure so I so he joins us all about a year ago to help kick-start their program during offensive testing so I'd say it's getting to be greater I think me two years ago they were lying on more I'd like to rely on it less and have it supplements just as a fair warning do not use my granny is the only thing that you're gonna do for security ah yeah you definitely want to make sure that you're finding a balance I think of the bug bounty program more of like the CP net
so do as much as you can with the resources that you have and if you operate a bug bounty program you're going to have a sense of whether or not you're keeping up with things if you find yourself just like paying bounty after Bonnie you're just like throwing a bunch of money out the door I have the same properties over and over again maybe need to reassess the strategy I want to percentage-wise you can address all my mom i would say i would say we think of it like maybe like an extra FPE or blue FTEs any other questions that's generally like we're with payouts happen all right well let's all of ya you