Clicksploitation: How Fraudsters Exploit AdTech & What You Can Do
Show transcript [en]
Hey everybody, thanks for choosing this talk. I want to say up front, I'm super nervous. That way I don't have to think about it the rest of the talk. If you've read my bio, you know that I've got a colorful history in cyber. But what's relevant today is that right now I help small businesses in the cyber tech and advertising realm. And so the story begins. What if I told you the next botnet attack targeting your organization isn't actually after your data. It's after your marketing budget. You might think that sounds crazy. If you had asked me a year ago, I would have said the same thing. That's nuts. It all started when I was helping a
small home inspector business run a Google Ads campaign. Um, they started getting form fills and leads. They were ecstatic. They started calling those leads. And one gentleman they contacted said, "Hey, I didn't fill out a form." They're like, "What do you mean? Is this your name?" "Yeah." "Is this your email?" Yeah, well, this is your phone number. So, how did you not fill out the form? And he's like, "No, I didn't. And I'm certainly not interested in your home inspection services because I'm in New York." And we're like, "Okay, that's kind of odd. Um, maybe this is just a fluke." But the same thing happened again twice in the next week. So, it wasn't a fluke. I started to dig
into it and what I found digging through my Microsoft session logs by the way on the right that is Microsoft clarity. Love it. It shows the users actions across the platform. Anyway, I watched the bots and you know how I knew they were bots? They were clicking 45 times in the same location. It wasn't even a button. It was a dead click. like these are clearly bots and the reason that they do that is to show engagement so that the the advertising algorithms Google is using doesn't detect them as an anomalous click. So anyway, I found bots there's foul play going on and I reported those cases of the odd botl looking traffic to Google.
Google came back and told me, "Uh, no, that's not fake traffic. We already filtered that out." Uh, yeah, in fact, they do filter out some fake clicks. They they weren't lying. Um, in fact, for that ad campaign, they had filtered out 8.33% of the clicks already. Bots were still getting through. And since Google wasn't going to help me because it puts money in their pocket. I'll talk more about that later. Um, I started to have to dig in to it more because again there's definitely mischief a foot. So I route all of my web traffic through Cloudflare. This is not an advertising plug. Cloudflare does not pay me. In fact, I use their services for free.
Anyway, um, yeah, I I had to plug that. So in the web application firewall um I turned on the logging of the traffic and started looking at everything about the web requests to see if I could recognize what made these bots. And the first one that I recognized was around the host field um and around the refer. So the host is where they're going. The referer is where they came from. Thank you. And for the referer case in mind, it was none. If the referer is none, that means they directly went to the page. But how? On an ad, they have to click to something, right, the ad to get to your page. So, it should be
impossible for the referer to be blank. Um, so that was one thing I found in common. Um, the next impossible condition was even a little bit funnier. Again, this was looking at the entry URL versus the exit URL. And the entry URL just showed the plain URL. The website showed no additional query um, logic added on, but then they would go to the Google ad URL. The only way that could happen is if they were clicking on an ad on my website, which why would I run banner ads on my own website to direct people to the same website? I wouldn't. This is another impossible case. Um, but they were trying to blend in, get past the
other uh W firewall. Um, so anyway, those were the two big anomalous type things I landed on for most of the bot behavior, but we still haven't gotten to the part about how the bots were getting these people's information and submitting it in the forms, right? Because it's not like they were making up fake data. This was the actual user's phone number and their email. And to understand that a little bit more and how they were getting past my standard capta checks on the forms, we have to talk a little bit about how advertising works. Advertising works this way. A web master has a website that gets a good amount of traffic and they say, "Hey, advertising network,
I'll let you pay me some dollars to host your ads on my website." It might be search ads. It might be banner ads, but they're getting compensated. At the same time, you have advertisers who want people to click on their ads. And so, they go to the advertiser network and said, "Hey, please display my ads on websites." And then you have the exchange. So when the ads are run and depending on the strategy um both the website owner and Google are going to get compensated for views, impressions, clicks, conversions and obviously those values depend on the campaign type. But just know that Google is always getting a cut and it's the much larger cut and
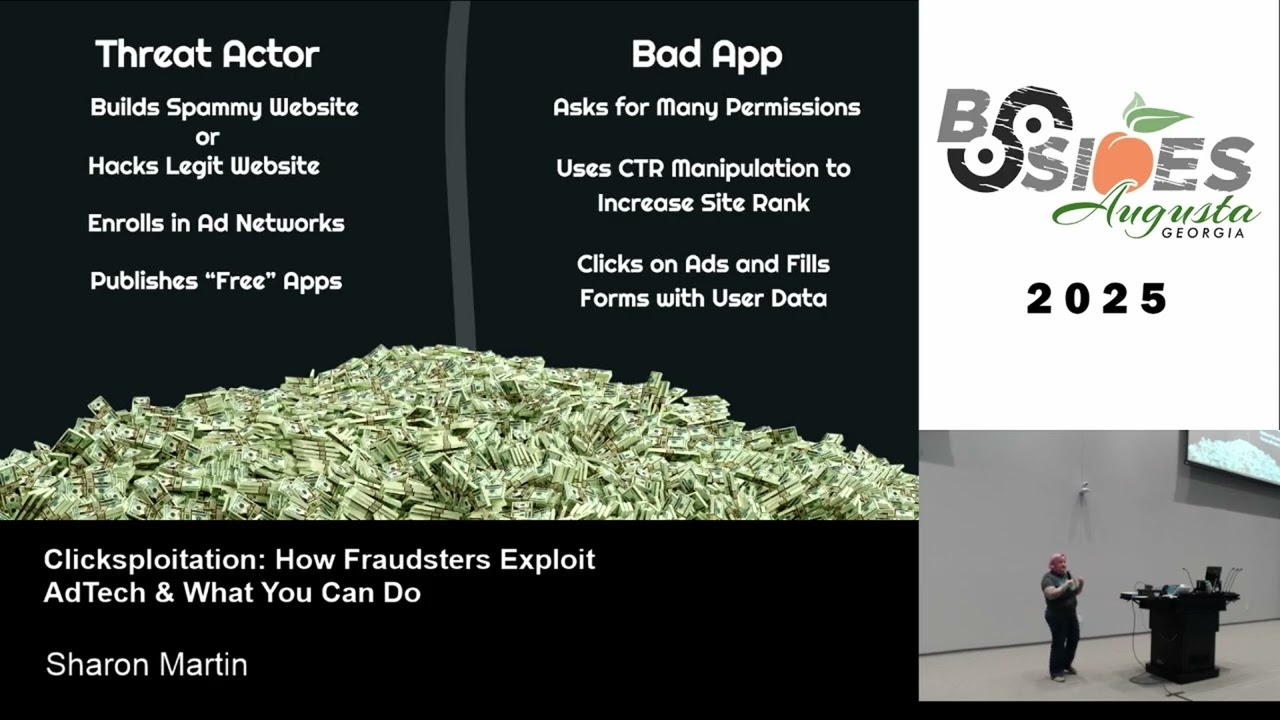
the website owner is getting a cut. Fast forward through that. You know, that's how it's supposed to work. Let's talk about how it was really working. How it's really working is this thread actor is either building a legitimate site or they're co-opting a legitimate site. In other words, I mean, they they hack websites. And by the way, an aside, they hack WordPress sites all the time. I make good money off of fixing WordPress sites. Um, and so they will enroll that website when they hack it into the Google advertising network and do nothing else. And so you'll have these poor small businesses who come to you and they're like, I can't figure out why Google ads
are showing on my website, but I don't want them on my website. It was hacked. Okay. So anyway, they've hacked a legit website or they've made a legit website. And this the content on these site is typically content people want to read. Um, it's typically can be controversial, can be forums. There's a common pattern where you have to keep clicking to get through multi-pages of content and on each page that you click on, there's another ad displayed. And so this is known as clickbait. Like they're click baiting you. They want you to just keep clicking um on the ads. Anyways, so they're trying to maximize their ad earnings on that site. The next tip is
they publish a free app. No, notice my emphasis on free. Nothing is really free. So they publish this app and when you install this app on your phone, you know, you wanted to play that free game and it says it's paid for by advertisements that you're going to get displayed. Congratulations. you have enrolled to be a bot in their ad network. Um, and I'm only half joking here. You notice how your phone gets really warm when those ads play? I'll tell you why in a minute. Um, anyway, when you install that app, a lot of times it requests maybe more permissions than you would think. It's will request like location permissions. You'll see it request permissions to view your user
profile so they can get your email. Sometimes they'll even ask for phone permissions, you know, like because they want to be able to pull your phone number uh or they'll ask for your contacts. They love to ask for your contacts because they're going to fish those guys later. Anyway, um while you're using that device and you're going through the ads in the background, it's making more ad requests. The first thing that it's doing is called CTR manipulation, click-through rate manipulation. So it is searching for a keyword that that malvertising or it's not really malvertising site but that clickbay site should rank for and it's going through the Google results till it gets to it and clicking on it. And when it does
that when the increase of a CTR rate causes the site to rank higher. So that's why we say CTR manipulation. But the second thing they're doing in the background is of course once they get to that site, they're finding your ad and they're clicking on it. And then they're taking that data from that user's phone and they are filling it into the form. So that's how you get legitimate form data. Anyway, uh you're probably wondering at like what scale this really happens. And by the way, this is taking money out of business's pockets, right? Because the there are people paying for these ads. That's why it's called ad fraud. this is a form of financial
fraud. So anyway, uh between 2014 and 2016 was an early example of an advertising bot at scale. This was uh called Medbot. It's because Alexander Zukov, he had a bunch of co-conspirators. They were using they created their own advertising network that was called media methane. And at its peak, this campaign was producing 200 to 400 million video ad views per day. And they were faking that using over 2,000 different servers hosted in the cloud. And they had bought over 650,000 residential IPs in order to fake location. And because video ad views have a relatively high CPM, that's from $3 to $36 per CPM, it's estimated that this setup was earning them three to five million in ad revenue per day.
Maybe I got into the wrong job, folks. I'm just just saying. I mean, that's that's a way to earn some money. I mean because I thought hey maybe it's just a couple thousand dollars which makes a big difference in a third world country but no3 to5 million a day and that was back in like 2016. Um anyway that got shut down but the way that they were doing it is they were spoofing domains. So they were pretending to be Amazon but they were typo squatting and then you'd go to the site and it would look like the marketplace. I mean they were they were pretty into it. But the next example we have is called vast flux. This was
discovered in 2023 by the researchers at human security. At its peak, there were 11 million phones that were running one of over 1,700 spoofed apps. So that's like when you go into the Apple App Store and you look for Microsoft Authenticator and it's not Microsoft Authenticator that pops up. Same dealio. They are spoofing the apps. There were over 120 targeted publishers and it was resulting in 12 billion fake ad clicks per day. Um, that's just plain insane. But here's the hilarious part. in the apps that they created. So you had to view videos, you know, to use the free app, they would actually when you were viewing a video, they had 24 more videos that were hidden
underneath the video you were viewing. So each view of a video was actually getting them views of 25 different ad videos, increasing their ad revenue. And again, I said, why is your phone getting hot when you use it? Well, that's why. because you're not just viewing one video, you're probably viewing 25. Um, so anyway, if ad fraud is this bad, the next question is, how much total is going to be stolen this year? Do I have any guesses?
>> 12 billion. 12 billion. Who else? >> Okay. Okay. You know what? You win. You win. I'll tell you why. What's the actual number? >> So the actual approximate number that will be stolen is 44 billion this year. So that's why I say you win. Great guess. Um and by the way again this isn't just targeting big businesses. It's targeting the little guys too because everybody is running ads and so no one running advertising is immune to potential click fraud. Just a couple more statistics for all you nerds in here. They say that nearly 30% of all digital ad clicks are fraudulent. Each click is costing advertisers about $3.32. So let's say as an advertiser you're
trying to get a 100red clicks a week. Well, think about that number right there. And then approximately 60% of the invalid traffic that's detected by Google, remember that screen I showed you where they were detecting 8 point something% of clicks. So approximately 60% of that is definitely associated with botn nets. So that's of the what they don't they know. And when I say botn nets, I mean these are the same botn nets that are doing more malicious things than just the ad fraud because this is, you know, almost on the side of legitimacy, but not quite. They're stealing money, but they're doing it in almost a legal way. And so going on to what these um attacks
are doing with these bots because like what else are they doing with these bots? They're doing this thing called malvertising. And I bet you're very familiar with malvertising. That's when these fraudsters are using that same ad network and they're popping up ads that do things they shouldn't, covering up your screen in virus alerts, leading to malware droppers, uh, trying to get you to download their fake antivirus, uh, software. I specifically hate these because they result in panicked calls from users to the help desk because they can't get them off their screen. They think their system's hacked and that's what they're designed to do. And so, you know, this is what most people think of when I say the word
malvertising. There's actually a sneakier way though to use malvertising. With ads, you can granularly target by industry, location, or even uploading a custom list of emails and phone numbers to match against. It's a very tailored ad list. So, let's say you wanted to understand what devices and operating systems a certain organization was using. Well, all you have to do is advertise. on your landing page. You're just collecting the web logs, seeing what user agents pop up in those web logs when they click on your ads. And then, you know, for a bonus quest, you could try to get them to download your free PDF guide that pops a reverse shell into their corporate network. That's malvertising.
And so, you're literally spear fishing with ads. So, so when your IT admin is like, "Hey, we need ad blockers. Please listen to them." Anyway, um there's also the risk of hiring a shady ad agency. You know, they advertise exceptionally low rates. You come back, you have these amazing numbers from them. You know, it shows like, "Oh, yeah, you had a 60% CTR. You had 25 conversions." But you as a business, they're like, "Hey, I didn't get any phone calls. I didn't get any form fills. Uh what's what's going on? And you know, in some cases, they may actually be working along with these bot farmers and hiring them to elevate the statistics to make the website look
better. But honestly, they don't even have to do that. If you advertise, the bots will come. All you have to do is run ads without taking precautions. And again, that's why you hear businesses and they'll say, "Hey, I tried advertising. It didn't work. It was too expensive. I got nothing out of it. Well, you can thank the bots for that and for inflating the price of your clicks. Um, when you're running Google ads without taking click fraud prevention measures, you have a few possible goals to choose from. You can choose to go for max impressions. The result is you get as many bots as possible to view your image or video. You can choose max
clicks. uh you can try to maximize the number of clicks against your ad and end up with a maximum number of bot clicks in your budget or you can choose max conversions and get as many fake lead form fills as possible by the advertising uh bots. And this is only half choking like there are true ad campaign goals that are max impressions, max click, max conversions, and all it seems to do is feed bots and I'm frankly tired of that. So anyway, um let's talk about if you are the one running the ads or you're working with someone running ads, how do you know that click fraud's happening? Um if they come back with a
really high click-through rate, meaning like 30% of the users are clicking on your ad, but no one ever makes picks up the phone or fills out the form, that is a uh smoking gun right there for ad fraud. because if that many users are interested in what you're advertising and they're not going through your landing page, either it's broken or it's a bot. Um, the next one would be conversions during when you don't run ads. So, a lot of times to save money, you'll run ads during business hours, 8 a.m. to 6 p.m. That's when your company is around to answer phone calls. Let's say you start getting form fills at midnight using your ad campaign. That's
a bot. That that is fake. Um, obviously we talked about the high rate of dead clicks on your landing page. Um, that's a more than a smoking gun. You have bots there. And then my favorite is your landing page gets traffic from China. It's not published on the web, but they're coming from China. How do they know about your page? You weren't advertising in China. How do you prevent click fraud? You use a paid service. Um, they're pretty cheap to set up. um but they can be expensive to run or you can use a web application firewall like Cloudflare. I'm cheap so I use Cloudflare. And to give you an idea of what happened when I started to add
Cloudflare rules, you can see repeated requests to the same IP happening in quick succession. So what happened is the bots I forced them through a a interactive challenge meaning they had to solve a capta to pass. They couldn't solve the capska, so they just retried hoping they would get past. And of course, they didn't. They would retry on an average of four to six times before failing out. And I got to tell you, this made me feel so good staring at the web logs and giggling because they didn't make it through and my ad campaigns finally started to perform. I can share in more detail, but basically, I built it using the five rules you're allowed to set up for free
in Cloudflare. um where I allow the ad the good ad bots through I allow what I know is good referral traffic and then I start filtering and sending through different cachk types again see me after this if you're interested in them um but let's talk about the more important thing right I already talked about the how to prevent click fraud how do you prevent your users from clicking on fraudulent ads well it's the same thing you do best security practices anyway Use ad blockers. They're really do help. Um, you should prevent the users from installing an unauthorized web browser that you can't manage. You want to run EDR antivirus protection on the endpoint in case something gets through. And
please, for the your sanity's sake, don't give the users local admin on their own boxes if you're the IT and you can avoid it. If it's your system, you know, there's a subset of these things you can do, which is use an ad blocker, make sure your computer's up to date, and make sure you're running up to-date antivirus protection. If the malvertising hits you, you get all those popups, reboot. It'll say not to reboot, by the way. It'll be warning, don't reboot. Reboot. And finally, the next time you're going to download that free game in the app store, just remember they wouldn't be giving it away for free if they couldn't make money off you somehow.
Watch those phone permissions they request, too. Just say no. Any questions? [applause] What's up? Oh, I have one more prize to give out, by the way. So, uh, who remembers the name of one of the different ad campaigns I talked about? The bad guys. >> Uh, you who was the other one? >> Oh, I think he got he he got a better one. Yeah. Sorry. Sorry. You got it. You got it. I'll get you later. All right. Any questions, though? Legit legitimately. Cole beans will ping me afterwards if you want my CloudFare rules. And other than that, thank you very much. [applause]





