BG - LOLS: LO Level Shells
Show transcript [en]
hey guys we'll be talking about lws lowlevel shells any anyone has an idea why it's called LOL you'll find out so I'm Lis this is Manish so we work for secured net I'm a penetration tester Manish is a security consultant and for this project I am a independent researcher but uh my company helped me uh bring this forward to you guys so what's the story basically the story is that I was trying to get a net cat shell and uh my colleague at the time gave me like a switch I was unaware that the switch was a layer three switch and I'm like well you need an IP right right well that's only an assumption the
hypothesis is that layer 2 can be used for a net catch shell but this would need to be post compromise so how exactly is that going to work well we made this meme for you to kind of explain it I'll give a couple seconds so the thought process um we'll need a MAC address and uh all layer 3 traffic is encapsulated in frames which means that um uh you will need an IP but uh what tools already exist that kind of accommodate this and uh there's a tool by the name of AR ARP exfiltrate that was made by Antonio Bia and uh he was able to exfiltrate ARP requests uh back and forth between uh two nodes and he
suspected that this is able to this was could be used in a in a C2 framework so in other words it's possible but with artart so when life gives you Layer Two make a layer two shell bottom line it's possible to encode information in frames but not through encapsulation so why is this such a big deal well the big deal is that layer 3 and above is highly monitored layer 2 is not which means that Communications don't actually need IP or port to work so how does layer 2 work well we have 802.3 8021 which is wireless and uh it work on the same frames or same frames same headers and um all all our
payloads all our stuff is going to be stored in the in the payload header of the frame um our broadcast to all to all to all nodes on the network using the fffff uh address um but other protocols can do the exact same thing there's no difference uh The Ether type is what defines the a protocol and an aana you can register your own ether type which we'll get into the next section ether types why are they so important during Defcon 31 Richard L he did a talk about this in his uh talk fantastic world of ether types and where to find them uh his talk was more about how to use ether types and how to
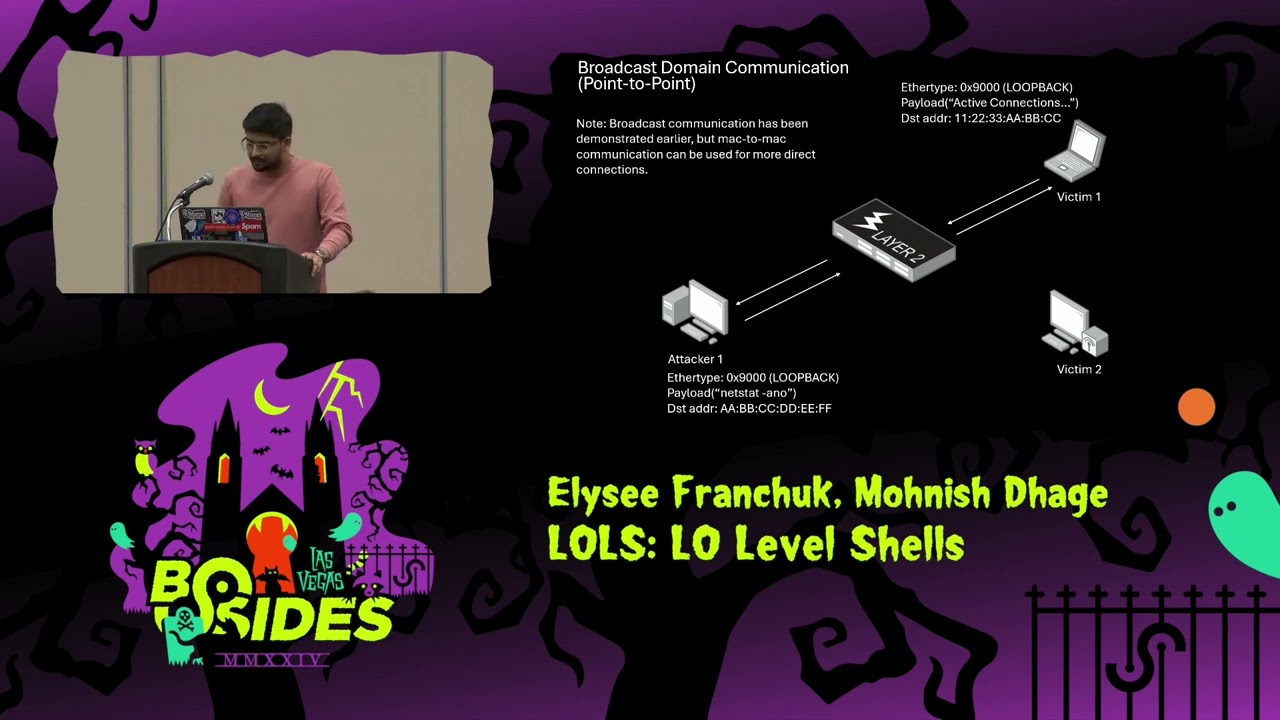
structure them to uh communicate with devices in our prototype we will not be using ether types specifically we'll be using them to blend them in to uh make it more covert so here's the payload uh we have 1500 bytes that we can work with so broadcast uh domain communication so as we all know uh whenever a layer we get a broadcast message sent on a layer 2 it gets sent out to all the devices that are connected to that switch so why is this important uh we we are we were trying to see if we could include netcat Powershell SSH commands in these broadcast domain messages which could be sent out to the other systems
that are on the uh on the broadcast domain so uh let's see what are the requirements and what the data flow looks like for doing this so the requirement as Alisa spoke this is a post compromise tool so we we are going to need initial compromise uh in addition to that we need Python and C to be available on the compromise system uh binary if you're using any thing uh for example netcat if you're using that uh we will need that and a ler of some sort uh so this is in a nutshell what is happening the victim is uh send sending commands via Ethernet frames and the victim is responding with ethernet frames back with the response so let's
take a look uh detailed look at the flow so yeah the attacker starts off by sending ethernet frames containing the command the victim node then uh decodes the frames ex extracts the command and executes it once the command is executed the victim node then again uses ethernet frames to send uh send the information back to the attacka node so let's take a look at a demo quickly uh for this uh before I jump into the demo I want to show the commands that we are running on the victim node we are running the script in listen mode and setting the attacker and session ID and on the attacker system we are running it in Connect mode again
setting the same attacker and session ID additionally we are providing the MAC address of the victim machine uh and then we'll be running Who Am ier command uh as uh Elis spoke earlier about ether types uh for the second uh section of it we'll be using STP as the ethernet type uh the code for that is 8181 let me pull the
video so yeah uh on the right hand side we have the victim screen using Windows which is connected uh in listen mode and then we are using uh the Debian machine on the left on the right uh to connect to the victim we are running who am I enter command and uh we have y Shar running in the background to capture the packets so as you can see uh the commands that were sent were using loop back and the responses that were received were using broadcast messages so now we'll take a look look at The Ether type that we spoke about so the only difference between the two commands is we are specifying The Ether
type this time around uh to see what sort of communication uh it it happens so the eer type we using it to blend in so again we'll run the same commands who am I enter yeah so let's take a look at the Y capture we'll Pro uh do the filter for 8181 so as you can see the commands were sent using STP this time around so yeah okay so is broadcast communication required absolutely not we could use point-to-point communication as well the reason why we chose broadcast for this particular example because uh broadcast communication is usually noisier and it gets sometime lost uh and like sometimes the security tools ignore those sir so to kind of prove the point that
communication not only can like we can tunnel uh layer three and above uh we're going to be tunneling netcat in the next uh demo which the Prototype does uh support uh this is the kind of diagram of what's happening I'm not going to go through it but uh basically we do the exact same thing the attacker sends the ethernet frame the victim receives it it then decodes it it sends it to its own loop back address where netcat is listening netcat can then run uh that command the response is sent to its own loop back address and then out to the uh out through ether uh ethernet the exact same opposite happens um uh when the victim is uh is listening
and this enables a two-way communication uh back and forth but this not only works on netcat this works on uh anything so here we have the attacker panel the thing that's highlighted that's where you type in commands for netcat I'll give everyone couple seconds uh the victim panel here what's highlighted is the actual uh netcat command uh on the right side of the screen that's the that's the tool that's being uh for L2 shell okay we're going to make EDR cry now
okay so on the right side or sorry left side that's where the L2 shell is we're opening up a RDP port or an RDP session to the victim machine now the reason why we're oh sorry the reason why we're doing this now is is to show that uh we have the initial compromise and okay that sorry about this we're having some technical issues okay so we have a EDR solution uh that's on the victim machine and the thread detected that's only netcat that's not L2 shell once an administrator um manually locks this up uh it will actually cut the RDP session uh what basically nothing will be able to communicate to that device uh on any
known protocol so that's what happened here however we have here the L2 shell that was uh initialized earlier we can still communicate to it via
Ethernet okay I'll just close that this is essentially what happened uh frames they do not uh get get detected and they are EDR IDs they allow it to pass through uh this is all the the loop back traffic that happens on the host and the victim uh it never it never uh appears out of the network so uh what are the limitations of this well obviously we got the broadcast domain and the frame headers they're cut off by the by the routers once they Traverse to different networks but uh we can bypass this with a Nick we can do Vine hopping directed broadcast from routers layer 34 application layer protocols uh out of band Bridges uh these are all ways we
can extand from one land to another uh M MLS networks uh this this works on MLS the same way that it works on any other uh ether type uh MLS circuits can enable that communication uh internal IC networks are very flat it uh it allows um this it it would be a prime target for this so uh we could also do layer to forwarding so uh if there is a victim machine that is compromised we could jump from one neck to the other one uh basically hopping the subnet uh we could also create temporary layer three layer Four Bridges with this uh basically accessing restricted subnets that could uh that could have like data uh data DLP preventions on
them so uh the use case that we can think of is a red teing scenario where uh or like a C2 extension basically where uh we are using this for communication between the compromised host so out of the six uh host that are here we are using uh three of them are not using the L2 shell so they are at risk of getting compromised however the ones that are using L2 shell they would be very hard to detect so now this is kind of the Grim part of the of the presentation uh detections uh unfortunately we will need layer 2 sensors we'll need to span tap the the traffic uh this might work on 80211 it works on 8023 so just regular
ethernet uh the entropy and size of packets they're going to have to be looked at uh the expected ether types for example if you have the configuration test protocol on your network it probably should not be there in the first place uh the only way to really know this is to Baseline things signatures uh good luck have fun it might work uh however this is only to detect common commands that they're unencrypted um Zeke might if it out of the box Zeke is not going to detect it and it's kind of expensive to to utilize um another detection is to inspect the loop back traffic if the te if our technique is used it's an
adjacent issue but it's good when paired with covert communication um it's not just a network or endpoint problem anymore so take a picture of this uh this is going to be how you detect anomalous traffic via Ethernet um now if the traffic is not anomalous it's a lot harder to detect so so here's the The Good the Bad and the Ugly for detections uh if it's ipv4 uh ARP or IPv6 ether type it's significantly harder to detect so the highlighted uh green that's all the detections with anomalies the above is basically uh IPv6 you can't really tell the difference so defenses vlans that kind of depends if you're only working on one nick uh isolated guest networks I
couldn't break through it through that one so it might be good uh there's certain limitations to it and Cloud environments it depends how Layer Two traffic is uh is implemented on them what has been in the wild um there has been a AP group Platinum that utilized so in their C2 framework however when I looked closer into it it seemed to use IP uh IP is not used in this prototype so it's similar but not quite the same so closing your marks uh this is not a vulnerability uh this is basically frames without structure are still frames um layer 2 detections only work for No One attacks DPI unless otherwise configured isn't really looking for this
uh wireless devices can communicate on ethernet Dev to other ethernet devices um Works in line so it's system Network agnostic as long as 802.3 8021 are supported um and has this research been performed uh I referenced all the people that have done similar research I haven't really found anything quite to this extent uh however there is a references page that will show everyone who uh did similar um tldr it's command control Focus uh ethernet transport agnostic uh there's ether type uh smuggling um this evades all most layer 3 to 7 IDs without disrupting other network hosts and uh how does everyone feel about Supply chains because uh that could be a problematic if this this is used as a
technique million frame question are adversaries using this I don't know but uh now that the ether cat's out of the bag what's next should vendors do more or is this a free-for-all so here are the references and uh big thank you to bsides Las Vegas and the security Community special thank you to Steve Porter Doug lease and Quinn Kramer for helping me and team make this
[Applause] happen questions any questions
sorry sorry which slide can can you come up to the microphone please sorry yeah the command to detect the traffic the TCP D oh I see okay yeah this is it this is only going to detect anomalous traffic this this won't detect uh frames that are uh properly structured and and basically that are made by uh not amateurs I don't
know um so I'm understanding this correct like I said this has to be on the broadcast domain the two the two Dev your victim and your aggressor have to be on the same uh broadcast domain right not necessarily it depends uh they can be on different networks but the actual communication it it happens on land but if if for example there's like multi Nick so you can jump from one network to the other okay this wouldn't work like if it had to go through a switch because it would like you said it would strip the uh I guess I'm what I'm getting at is um the value in this is it would ire uh your your um your aggressor You'
have to have some sort of if you wanted to use this as a remote attack you would have to have some sort of channel to get to it so this is post compromise so the consideration here is you already have compromised the victim machine you are already on the same network as them so it could be something that you use for pivoting for Co communication uh so it's basically sort of uh you could think of it as a C2 extension basically so okay but but both both of them would need to be compromised the victim and the aggressor so uh initially once you have compromised you would be on the same network right so from there you could
you could move on to a different Target who is in a different network and then you still have to be able to bypass the EDR to yes if if that is the case but the thing is Layer Two isn't monitored that no Layer Two isn't but in order to get the initial compromise yes yes yes so that that's that's the only consideration here initial compromise so yeah this is after this is post compromise U and it's for mostly for Co communication so actually now that I'm thinking about this a little bit where this might be a value is like if you're doing a pentest engagement where you actually get physical access to the facility and you somehow put a a
malicious device yeah that connects directly to the network but then you have access via some other yes okay yeah okay cool no not that this count what you guys done this is really cool thank you hello just checking my understanding do you need raw sockets for this to work or not I'm sorry do you need raw sockets to do this or not uh you so you need admin privileges so this requires Pudo but it does like raw sockets it would work on IP right but this would be pure frames so in a way yes okay uh have you considered doing this same type of payload but using um setting the protocol to be IP but just have invalid payload inside the
IP packet I didn't quite understand that sorry you if you're if you're making ra frames have you considered um having an IP having something that is labeled as being an IP packet but just with random content so we are not really using IP so it's either Brad broadcast or Mac to Mac okay hey are you going to be open sourcing any of the code you shut off today we're considering releasing this we we don't really know uh the impact of this right now but uh we're we're considering it uh raise a hands who would like this release so they can look at this we need a lot more hands than that all right thank you all right thank
you come on [Applause]





