CISO Panel | Ransomware Response: Pay or Fight?
Show transcript [en]
all for coming and thank you for your patience. We actually have one more panelist that is on his way. So if you uh Larry Whiteside Jr. So when he gets here, he'll probably come in. In the meantime, we have Mark um Hardy who's pitch hitting for us. So if you can't tell the difference, we're the same height. I mean, what can I say? Yeah, but we have a real we have an interesting uh um agenda for today. So, usually what we've done the last few years Oh, sorry. What we've done the last few years if we really brought in really great CISOs and we've done a Q&A and you guys have been great and how
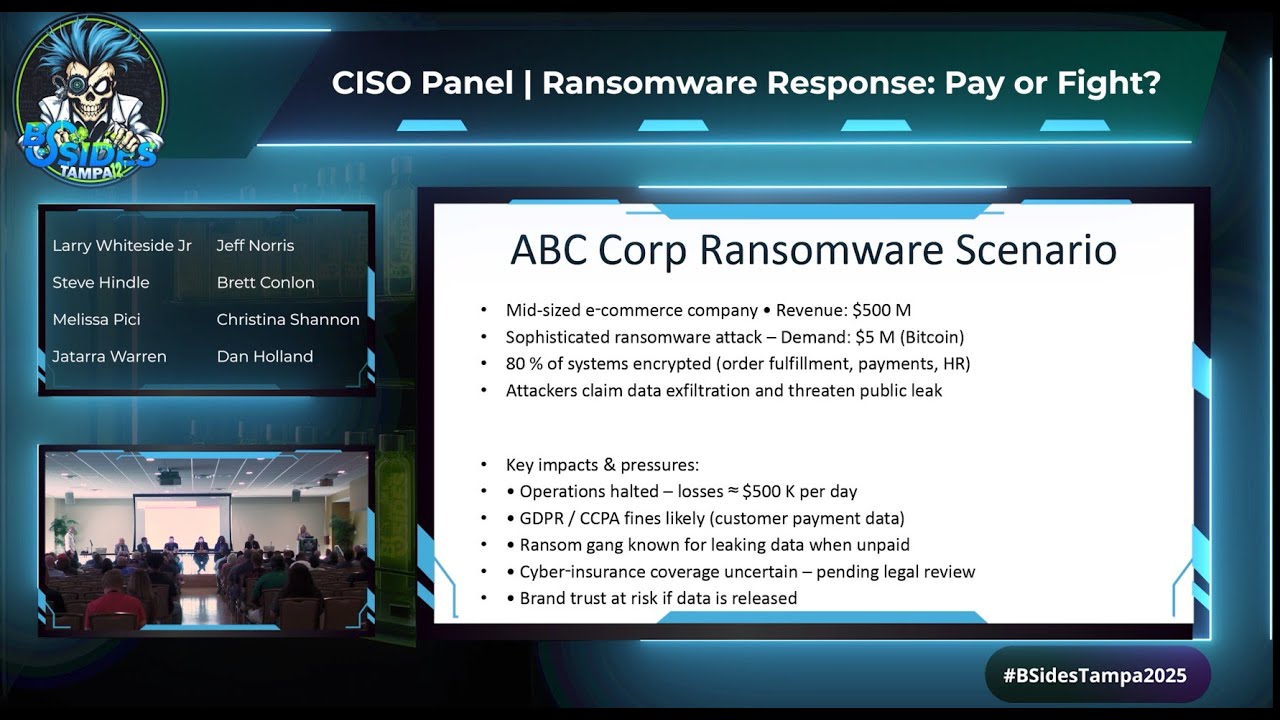
you've interacted with us. This year, we thought we would, you know, um twist it up a little bit or get a little bit more creative and do a ransomware scenario. So, what we decided to do, if you look up on the screen, you'll see we're going to basically do a face off, um, where one side of the one side of the CISO panelists are for the ransom. The other side of the CISO panelists are against the ransom. Um, and you may say, well, does a CISO make that call? The CISO normally isn't making that call. Um, it's really a business decision. Um, Larry, there's Larry. He finished his head shot. the real Larry Whiteside. Everybody,
for those of you who don't know, he went to the free headshot area and want to get his resume and all that. Yeah, proposes you. I said, you know, we could look each other eye to eye. We can, but I don't have all this. Yeah, I think that's that's where the similarities end. Gar and Mark, you're welcome to hang out. We just have to share a mic. Glad to help out. We get to share share mic. We're good. So, and we'll do introductions here in just a second, but um just wanted to tee up what we'll be doing, right? We'll be doing a ransomware scenario where, like I said, um you'll see up on the screen. Um it'll be for a
midsize e-commerce company, ABC Corp. Um and then, you know, it's a sophisticated ransomware attack where they basically want 5 million um and Bitcoin for payment. 80% of your systems are encrypted. uh order fulfillment, your payments, I mean it's e-commerce, right? So customers can't make orders. Um and then you know when you think about the key impacts and pressure um you know it's 500,000 a day in terms of the risk impact you have leaked some data um most or if you don't pay the ransom you have the risk leaking data most likely. Um and then you know ransom gang is known for leaking data when unpaid. Um cyber insurance coverage that's not certain. and we left that a little bit gray. Um,
and then you know your brand trust at risk if data is released. So the big question that we'll be discussing today is should ABC Court pay the ransom or not pay. And there's there's a a piece here that's really really important for our panelists. This is a hypothetical company. And so what you're hearing today is you're hearing the panelist's opinions based upon this hypothetical company and the hypothetical scenario that we're walking them through. What you're not going to hear today is the positions of the companies that our CISOs and our respective panelists work for. So again, everything's hypothetical. Everything's going to be based on the scenario and based in the moment and not reflective of the
organizations that everybody here works for. And yes, lawyers made us say that. So, I would suggest that before we get started, let's just have our our awesome CISO panelists do a quick introduction. Uh, say where you're from. Um, and if you want to say maybe an interesting hobby. Yeah, you start. Go ahead. I'm I'm not on the panel. I don't even know why I'm here. I'm Jeff Norris. Uh, I am the chief technology and information security officer for CE Coast Bank located over in Steuart, Florida. Uh, so interesting hobby. Uh, I've been playing guitar for about 35 years. So that's kind of like the hidden talent kind of the thing I want to do in my spare time. So thanks.
Do you have any spare time? Rarely. So you don't play the guitar very well then? Well, actually I do. There you go. All right. My name is Dan Holland. I'm the deputy CISO at Tampa General Hospital. I've been there for about a year and been living here in Florida for over 10 now. So, it's great to and kind of wild for me to be on this side of the uh the stage since I've been in in those seats uh for for many of these side. Fun hobby. Um really don't have a ton of free time in this. So, I I haven't been able to develop any musical talent. I'm really trying to see how much I can get chatbt
to take over my job, but something that's keeping me awake every night. Um I'm I'm Brett Conlin. I'm the CISO at American Century Investments and uh I had a lot of great hobbies, but now I have three kids and they don't let me do anything that I want to do. So, between this and the kids, I don't have many hobbies. So, I'm a little different. Um which you'll find out soon, I'm sure, as I start to talk. I am Melissa Peachy. I am the global GRC director at Cineverse. Uh prior to that, which has only been three months, uh for the last 20 years, I've been the head of IT audit. So, I'm going to come in from a business and risk
perspective. As far as interesting hobbies, it's probably the fact that well, I haven't done anything lately, but I do musical theater. That will become very apparent. Good afternoon. My name is Jerara Warren. I'm the deputy CISO at Mosaic. I've been at Mosaic for about four years. I've been in this role for about five months. Interesting hobby for me. I don't know if it's interesting, but um I just recently got into gardening. So, I'm out there trying to grow some vegetables, but uh it ain't going well so far. I've only got one cucumber. So, if you guys got any tips for me, uh please please find me after this. Gardening excitement in the front row. Did you see that? Yeah, I they got very
excited. Anyone? Let's connect. Hello, I'm G. Mark Hardy. I'm the host of CISO Tradecraft. I've been told I had a face for radio and I am not Larry Whiteside, by the way. He did make it up here. And so also in terms of hobby, I just bought last month a pizza oven and I am in the process of learning how to make pizzas. Yesterday or two days ago I made four. One of them was round. Two looked like an amoeba. One looked like some other I'm getting there. But the point is if you like fresh pizza, make friends with me. Come on over sometime. You can help me make some mistakes. I swear I've seen that episode of the
Amazing Race recently. Um Larry Whiteside Jr. Uh apologies for being late, but I refuse to miss my barber appointment. Um uh 12 years in running, right? So it's a thing, right? Uh every other Saturday. Anyways, um I am currently so I'm the president and co-founder of a company called Confide. Um we literally just help CESOs be better, right? Um through technology and services. But uh I've been an eight-time CISO, CSO, CTO across a bunch of different industries. I've been in this industry for a long time. From a interesting hobby standpoint, I don't know. I do a lot. Um, you know, I'm a huge diversity advocate. Um, my wife and I run multiple businesses and I've got seven children. So, between all
of that, uh, my time gets pulled in a lot of different directions. So, of which the two youngest ones are in the back. So, I've got four college graduates now. One that's got graduating next one more graduating next year. And then I've got the seventh and eighth well soon to be seventh and eighth grader in the back that I'm trying to get through college as well. So, I think the two in the back wanted to stand up and say hello to everybody. Oh, I would love that. I would love that. Give us Percy, stand up, stand up. Welcome. And I am going to apologize in advance. Larry, your kids are going to learn a lot of new interesting language.
Some of it they've likely heard. Well, I'm Scottish, so we'll see. Uh, Christina, do you want to give your introduction? Yes. So, Christina Shannon, um, the CIO at Kick Consumer Products. You think of Kick, it's the off label, uh, brand of bleach. So, if you go to Publix, you buy Publix bleach, that's probably us. Um, or if you buy Clorox pool products, that's us. Uh so um former CISO um done that role a few times. My favorite hobby is uh I probably it's probably more of a zen thing. Uh I like I like uh timing moons and tides and going and finding seashells like um Santael is probably my favorite place in the world to do that.
But Madiraa Beach is pretty good too. Um okay so with that um we're also going to try to make this a little interactive. That might be a little bit hard, right, while we're having the discussion, but we do have a few polling questions. So, if you want to participate, then go to where it says you can just go on your phone. Um, it should be right there, poll. Uh, Christristina Shannon 979. Um, and you should see the first question. I actually just put this one up here so that way I could show you guys how to get on there. And as Christine said, this is this is this this intends to be a lot of interaction and a lot less of a
lecture. So, I'll keep my eyes on y'all. By all means, raise your hand, shout out, make your intentions known if you have any questions as we get through this, as we get in with our panelists. Yeah. And we already So, I'm my name is Steve Hindle. Uh, but a lot of people call me Stitch. I've been a CIO and CISO. And just like Christina, I'm now the CEO of Simple Security where we are democratizing cyber security for small medium-sized businesses all around the globe. So that's enough about me. Uh favorite hobby? Um I'm a competitive shooter. So I I get involved in a lot of precision based shooting competitions. There you go. That's it. That's really
interesting. Don't piss him off. It is my It is. You mentioned zen and you mentioned gardening. It's my zen and my gardening. It's a mind game. So it's it's I was like that's good. Um you guys are already doing awesome where you are already answering the first polling question. So I thought before we started our debate and our discussion on you know for or against we would have a pre-debate poll where you know ask the audience if you guys are advising ABC Corp what's your initial recommendation and you can see the results as you guys are entering them up there. It looks like so far and it's really interesting because you do have a there is a disclaimer on the
on the do not pay right. So, I've as as being a a former head of security for a big public company, um servicing about 700 of the world's most well-known brands, um I've been in two ransomware scenarios, myself and my security team. Um in one scenario, the business chose to pay. In the second scenario, the business and company that I was working for chose not to pay. And in each one of those, recovery and getting through the process was key. in both of those scenarios, but a business decision on each side. Um, so this is really interesting because we're we're seeing that not a lot of you are thinking pay the ransom, right? The FBI thanks you
for your service. Yeah. And I guess raise your hand. Has anyone seen like the Coinbase news, right? I'm wondering if any of that's like influenced your decision. I saw that and I was like, h I was telling them earlier, I was like, a little bit of that's badassery. A little bit of that is I don't know. Tell me about it though. So it's it's important to understand what Coinbase did, right? So Coinbase Coinbase had theoretically a $20 million breach, right? Where where hackers requested $20 million ransomware payment from them. Um they verified that they had some data and Coinbase, the CEO, came out publicly. He didn't respond to them via the channels they connected with him on. He literally went
and posted on LinkedIn publicly his response to them while he also informed the community of what had happened. And instead of paying them, he chose to put out a $20 million reward for anything leading to their capture. Right. So there's it's you should go read it. It's fascinating. A number of us have probably put post out about it, but it's a fascinating um example of how to respond. I'm not saying it's right or it's wrong, but it's an option. And I love the way he did it. And I don't know if anyone's here, but like the 8K, too. Did you read their 8K? No, I Their 8K is fantastic. They summed everything up in 750 words
or less. Like it was it was straight and to the point. Um, and that's publicly available, but you you if you haven't read it, you should go read it and you should watch what they're doing. So, the important thing to realize is Coinbase is a public company. Um, so transparency is key. uh you can't be defrauding your investors in the eyes of the average investor by something by an event that is not considered material. So in doing so the SEC have developed a lot of requirements and if you go public you have to produce this operating statement that tells the world hey this is all of our dirty laundry. don't invest in us if you've got any brains and then investors
then choose to invest in you, right? Um but it has to be transparent and the 10ks and the 8k filings are part of that. The public company I worked for when we had a cyber security event and we chose to pay the ransom, all of that had to be disclosed so that the average investor could make an informed decision. And so in any form of ransomware event, as our panelists are walking through this scenario, you have to consider transparency is key. The SEC filed against four companies last year. And when you look at the terms of um the civil penalties for not communicating transparently, you're going to recognize some of these names. Uh everybody here recognizes
Mimecast, right? Mcast cyber security event. They were fined $99,000. Checkpoint, you're familiar with Checkpoint? They were fined $995,000. That's a fine on top of all the costs of recovery. Unicus 4 million, AAA 1 million, and Ashford 115 grand. So, it's important to note as Larry said, what Coinbase did, they took a very transparent, very open approach to avoid post incident litigation. We will get into post incident litigation later, Miss Shannon. No, I was going to say um let's get started. The way that we'll do this is that each um so this side is going to be the side that is for paying and then our four CISOs on the other end will be against paying and what we'll do
is we'll have each CISO you know take a few minutes uh state your position and you know think about you know how that impact how paying or not paying impacts you know your compliance your customers you know all all the considerations that you make when you're making that decision. Um, you do you want to you want to start or do you want to kick it off or? Yeah, let's kick it off. So, I'm going to I'm going to turn over to our our against guys. Um, so initial outset based on the information that Christine's communicated to you and what you know, your initial your initial stance, your initial assessment, right? Because we haven't reached that decision point.
your initial assessment now and as the leader and the expert to the business what's your recommendation to your fellow business leaders your CFO your CEO your legal counsel what's your position going to be I can start off I think uh right at the beginning looking at just some of the elements here and I' I'd like to hear from some of the others um some of the assumptions that you want to make is that you do have backup platforms in place right that those have been tested in some form or fashion so that you should have some kind of recovery or resiliency option when this occurs, right? Obviously, there's been a breakdown in controls. You've had
something happen. We don't know whether the cyber team has been performing any runbooks to try and mitigate this to any extent at that point. But then you have to start looking through what are the the repercussions here. So on this side in terms of not paying the ransom is still trying to find out what's going on. But in the back of your mind and what I'm looking at in here is um We've got likely a threat actor who's already exfiltrated the data and there's usually known instances where even if they we do pay the ransom, you may or may not get the key to unlock it and there's still no evidence that they're not going to
release it and hold you accountable in other ways. So, those are the things that run through my mind in terms of counsel back to the team uh and others as we we exercise kind of this conversation. So as we as we go down for for our next panelist over here, I'll put it to you slightly slightly differently. The same question. How much are you seeking external help uh from um externalmemes, vendors, third party council, breach negotiators? Are you going to engage them? Are you going to contact law enforcement? How are you how are you looking at it from that perspective? It really depends on the team we've got in place, right? What is what have we trained for? What have we
trained on? Right? Because you know, practice like you play. If you're not running through these tabletops, if you're not going through the exercises, you don't want this to be the first time that you uh are thinking about these things and responding to them. So, some of those decisions already being put in place should already be in place. Those decisions about the procedures should already be tested and validated, right, with the team and the partners that we need to pull in. So, it's um really situational and circumstantial. You know, where we're at on the the timeline here with uh where we're at in the response. The only thing that I would add to your comments though is by paying
the ransom, not only are we not sure if we're actually going to recover our data and it's not going to be released, but how often are companies that pay the ransom then hit immediately after because now it's known that you pay, right? So, it's not an isolated incident. can't look at this myopically and just say this is the only scenario we're going to have to deal with because if you're a known payer of the ransoms then you just put a huge target on your back. Okay, next panelist. So when we look at that how are we looking at it as well from the uh perspective of financial loss and insurance? Yeah. So for us right this is we plan for this um
since we're not going to pay we have cyber insurance. We brought in our our our third parties that are going to help us recover. We've practiced our resiliency because we know we can come back up. And um you know, from the macro level, you know, you're putting a lot of faith in some criminals who have done some nefarious things to trust them that they're going to uh you know, honor their word, which we know that they have shown examples of where they don't. So, we're not going to pay that. We also understand the risk of if we did pay um and that group ended up being on the OFAC list, now we've contributed to terrorism, right? And so now we can't uh
bank in certain areas and then you're going to get spanked. You got it. So we're we've chosen not to pay. And then what we're going to do is focus on our resiliency efforts and we also want to send the message out that um this is not the place you can come to and get get some easy pay from. So that's our stance on it. So this side of the shop then as before we pass it over to Christina's side of the shop um this side of the shop is firmly taking a risk averse decision against making that payment. pretty confident in their abilities to restore and recover without relying on honor among thieves for the bad guys and
the threat actors. Yeah, I'd also add I think um we also have a heavy reliance on our crisis comms, right? So in this scenario, how we communicate to our stakeholders and our our employees is going to really make or break how we are perceived in the public. So massive bonus points over here because the difference between incident response and incident management and crisis management is the way in which you communicate. So first panelist to mention about communication. So that's very good. It's key. It's it's more important how you handle it internally sometimes more than externally. Making sure that all of your employees are in sync and that you've got a a kind of a playbook to go from and you've rehearsed
that in advance. So that's it's almost more important than the external comps. Sometimes anyone who agrees to pay is probably part of the bad actors. So now let's go to the pay side. We get 10%. Everybody gets paid one way or another. So I I'll start just real quick and then I'll you know hand it over to our esteemed uh CISOs. Um so for me it's a midsize company and it's e-commerce. So downtime is I mean every every second a customer can't place an order, right? You're not just impacting your profitability, you're impacting your reputation, your reliability. Does that customer want to come back and shop with you or are they going to go somewhere
else? Because now they're probably scared if they can't reach your website, right? Or they're like, "Oo, what's going on there?" But if I think about it from a just a pure financial standpoint, if you're $500 million company, um your your capabilities and your controls probably aren't that great. Meaning, when I think about um security postures and in Fortune 500 versus a $500 million company, it looks very different. And I know cuz I've been in both. Um, and and I, you know, in e-commerce, you have to really you're focused on the customer. How do you keep the customer coming back? And by day 10, you're at that $5 million ransom, but you've probably lost all of your customers. So, if I can't
recover in a day, I'm probably paying the ransom. So, that way I minimize impact. I minimize data loss. I understand the risk, but I think the um of of paying, but I also think that the risks of not paying seem greater. Who who wants to go next? Larry, I'll let you go. You just go down the line or let the ladies let the ladies go first. There you go. So So I'm realizing I'm probably actually sitting literally in the middle of this in a GRC position. It's the life you live, Melissa. It's the life you live purposeful with the audit background. So you know, it's kind of two camps. You have the as as they
mentioned, it's a matter of do you have a robust control environment that's in place? Do you know that it's effective? Do you know that it's you can you can pull an MGM and say screw you, we're just going to shut down. We're going to recover and we're good. or do you pull a Caesars and say we probably didn't have the controls in place and we need we're losing business. So it's and it's also going to be a matter of what is the business and who is the threat actor. If the threat actor is one of the known larger threat actors that basically has an a thieves honor that says once you pay we'll give you back what you're
looking for, then paying it is possibly a smart thing to do. Some of the smaller ones that are out there, however, um if you end up in a change health care situation where they paid and then all of a sudden you find out it was subcontracted, the the subcontracting firm didn't get, hey, we still got your data. We're going to ask you for a second ransom and oh yeah, we're going to release the data anyway. So, it it really is going to depend on exactly what the scenarios are. You know, what is the risk? Not even to reputation anymore, I think, because I think everybody knows it's a when you get hit, not if you get hit. So, everybody
expects it nowadays. But the loss of business and how much am I looking as if this is going to truly just say, "Hey, my business is now shut down and there's no recovering from this then." Yeah, I would also look at what is the cheapest way to potentially if I shut my business down and just completely restarted again, is that even better? Um, can I s also like for for the the reputational side is probably driven more by how you responded, right? It's less about what actually happened to you at that point. Yes. Right. But that's the business reput that's the reputation of the business. What one of the important parts that you said is the reputation of
the threat actor that is so critically important in gaining some understanding and insight to that so you know who they are and what their reputation is because to your point there are some that it's known. It doesn't matter whether you pay them or not. You're not getting the data back. You're not going to get the proper key. So you would make that decision to not pay early because you knew who the threat actor was. But in this instance only being a business that's valued at $500 million in revenue, right? You're losing 50k a day in 10 days. Like you are half million 500k is a lot worse. So in 10 days though, right, you've basically lost a year's worth of
revenue, right? So at that time timing matters, right? And so you're making a business financial viability based decision, right? It's you may not even look at what controls you have in place. You're going to first go to what is the viability of the threat actor actually giving me this data back. That's enough because the amount of money that I'm losing on a daily basis is going to make me not make payroll as a business. And if I go out of business, it doesn't matter anyways. Yeah. And even with the additional fines, I would say that I know everybody needs to jump in is I remember when I was taking my master's degree and everybody's like, "It's the
right thing to do. You're just not going to do it." Yeah. That's not how that works. If the cost of paying them and getting my business back up is less than it would be to deal with anything else, that's the cost that I'm paying because that's the easiest way for me to get out of this and to get back where I need to be. So, it's it's an it depends, but that would be the reason for paying. Absolutely. So, they've covered it already very well. I'll just add I'll go back to our uh parties over there. They they said that they were sure that the backups were there. So, just like they're saying, if we're not sure that
the controls are in place that are going to bring us back up quickly in this scenario, based on what we're seeing, like they just said that the revenue is going to start um calculating very quickly in 10 days, then we need to come up very fast, right? So, that's going to be the first thing that we're going to look at. They probably don't have backups in this scenario. And so if and even though this uh this gang says that they are uh known for not paying, it's still a risk that this company would probably consider just because they need to come back up operationally very fast. And one of the things to look at is that
we always thought about ransomware as being attack on availability. But if you take a look at the scenario with the GDPR and CCPA fines, it's an attack on confidentiality. In addition to getting your information back or not getting any information back, you're concerned about being disclosed. Now, as Larry had pointed out, definitely the reputation of threat actor and you can usually determine through a little bit of back and forth. My buddy Mailware Jake has said he's done so many ransomware negotiations, he kind of knows the people on the other end. He's never met them. He probably would uh never meet them in person, but he understands their personalities what they're doing. And there is a bit of an honor among thieves
because think about it. If everybody gives the data back, then the next person will pay the ransom. But as soon as somebody starts screwing around with that system, it doesn't work. So when not Peta came out, I thought a bullet was going to be administered in Moscow only to find out it really wasn't ransomware. It was just disguised as ransomware. So what do you do from a business perspective? We've taken the hit. Our controls failed. Our precautions failed. Our operations are down. And so from that perspective, we already se have three strikes against us. If we understand that the reputation of the threat actor is such that we have a high expectation of getting our data
back and they stay quiet then also we take a look at the fact to say what's our production run okay how much is going to cost us to recover independently and then you still have the reputational risk as well as the regulatory risk of okay we didn't pay them they don't give us our data back but they sent it to the SEC or they sent it to the state of California saying oh by the way and now what'll happen is some of these ransomware oper operators will say, you know what, our fee for recovering your data and protecting it is just slightly less than the regulatory fine you would have to pay by your government. What a deal. So this is
this is really important. What you're hearing up here is you're hearing a lot of conversations around risk and risk is just uncertainty. So everybody here is leaning on their expertise and leaning on their partners and their subject matter experts. For those of you that aren't particularly familiar with the ransomware kill chain and the organization of ransomware gangs, it's all malware. Ransomware is malware, malicious software, whatever it may be. But it's turning more into a cyber extortion um environment where it's not necessarily always about exfiltrating the data because the bad guys have realized that takes time. It's like Tom Cruz Mission Impossible. There's laser trip wires being set up everywhere by the CESOs and their security teams. And
the longer they're in the environment poking around trying to find their data, they're going to trigger something. Alarm bells are going to go off. Containment will trigger, they may get rumbled. So now the bad guys are actively taking a stance of business disruption. So this becomes a business continuitybased event to stop you from generating revenue as our panelists have mentioned. So now ransomware is a distributed organization. It is organized crime, right? We all abhore, I hope, everybody in this room, the idea of the hackers and bad guys being hoodies in basements, right? Because that's us. That's not necessarily the bad guys. The bad guys are working like a cartel. And if you're familiar with organized crime and cartels, then what
you've got is you've got people that obtain access into organizations. Those are your access brokers. They will then say, "Hey, I've infiltrated ABC Corp. I've got a back door. or who wants to buy it? And they'll sell that back door for about five grand. It's not a lot of money. So, so then another group will buy that and another group will start to push that access further up to say, "Okay, we've now got the access. Let's develop the malware or deploy the malware into an organization." And then you get your deployment and your payload trigger. And as we see here, ABC has suffered from a payload trigger where they have ransomware encryption and data exfiltration. That all starts filtering
up to the point where the bigger a threat group is, they start to demand bitcoins and ransom. That's not the same guys that got the access in the first place. And if a CISO is not buying themselves time to close that door, if you don't find out how the bad guys got in, the door is still open and then you get your second ransomware event, even though you've already got through your first one. You've already been paid because you didn't effectively close the door. So there is honor among thieves as we've had mentioned up here as well. The interests are if you pay they will support you and they have some of the best customer service in the business to
be able to support you and troubleshoot you. Your incryption keys don't work. Let me help you. I'll escalate that to my supervisor. Yeah, try calling Microsoft and helping with their platform. Good luck with that. I spent 25 years in the customer service industry working with Sykes in the beer can building downtown. I can tell you that they have some of the best customer service that I've ever experienced in my career. Chat bots, you name it, it's out there. So, you're dealing with sophistication depending on the threat group. Which is why, as Larry mentioned, as Gart mentioned, depending on the threat actor you're dealing with, they're either going to uphold their end of the bargain or they're not. And the chances are it's
because somewhere down that chain, you haven't closed the door and they still have access. Let me throw one more variable in there is that a lot of these groups will be open to negotiation. What they ask for their $5 million, that's an opening bid. That's an opening bid. And often you can find out that about 70 to 80% of these can be negotiated down and sometimes quite a bit depending upon who you have negotiating for you because as they say, some of these thread actors have already run the other negotiators like, "Come on, I know exactly what you got the last three times. This will work out pretty well. We'll throw a little bit extra in there." And if you take a
look online, you can find some narratives about companies and uh people I think it was the economist perhaps or I can't remember what the publication was. The guy last year he was a ransomware negotiator and he talked about how he was able to get it from 5 million down to about 130 grand. Yeah, I was going to say they they have cases where it's been like millions asked and tens of thousands paid. So I think one of the things you have to look at too is what the role of cyber insurance is now playing on this as well. because as cyber insurance policies have come up, they're not going after companies, they're going after those insurance
policies, right? So when they know that's out there, that's actually what they're looking to hit. So if they get a company that doesn't have cyber insurance policy, it's one of those things of you have negotiation, it's like what are you going to get out of us, you know, and a a company this small, you know, it's already said in our scenario, we're not quite sure where our cyber insurance even sits. So if they find out you don't have that, that's one of the things that's actually escalating. I believe if I remember my statistics correctly in 2022 the average payout was about 300,000. In 2023 that went up to 1.83 million and in 2024 2.78 million. And if you look at the increase
in those it is the increase in the cyber insurance industry and the and the policies that are coming out that are making those larger not just the fact that companies are paying out. So the insurance piece is is a fantastic point and and before we pass it over um Anne Newubower, if you're are familiar with an she was the former US D national former US deputy national security advisor and in October since we're throwing around dates in October last year at the counter ransomware initiative conference held at the White House um the White House's policy and statement on this was and I quote some insurance company policies for example covering reimbursement of ransomware payments incentivize the payment of
ransoms that fuel cyber crime. This is a troubling practice that must end. Cyber insurance is the youngest insurance piece in the entire industry. It's not been around long since 2015. That's a very short time when it comes to insurance. They're still developing. They're still growing. They're still learning. They're still putting the policies and practices in place. Your insurance may not pay out because they may there may be legislation. There may be directives passed at some point in the future that says all this stuff about telling companies not to negotiate with terrorists, not to pay ransoms. There may be a change at some point that says, "Hey, you we're not going to allow you to pay ransoms to these criminal
organizations and we're going to make that in and of itself a crime." So, um, Missouri's got a bill going forward, I think. I can't remember if it's passed or not, where that's another thing. Our headquarters is in Kansas City, Missouri, and you can't pay So, it sort of removes the uh problem for you. You're not allowed to pay and therefore now you have to um base it off your insurance and recovery practices. Those of us in the GRC profession like those laws because it means you need more people like us and and those like me hate them, right? Because here's the deal. Deciding to pay or not pay is a business decision. to to have the federal government or any
regulatory body make that determination for you, they're not going to bail your business out. So, if you're a health care entity, which I was a CESO for a big health system, and you decide and they tell you you can't pay, but you've got people on the operating table who are dying in front of you because you can't get systems operational, that's a business problem that the federal government is making for your organization that potentially put you out of business and cost tens of thousands of lives. There's also some items in the cyber insurance piece. Melissa, I'm glad you you kind of brought that up. Um, in dealing with cyber insurance, they may also have capabilities to engage a
different organization to handle the ransom negotiation as well. Yeah. Yeah. The recommendation from all parties is you do not negotiate yourselves. You also don't pay the Bitcoin yourselves. It's separation by degrees to avoid OFAC penalties, etc., etc., because you don't necessarily know who your threat actor is behind. Are they Are they North Korea? Are they Iranian? If so, doesn't matter. If you pay them, that's an OFAC violation and you're on you're on the hook. You're in deep And all those things have to be You should already know that. You should already know who's paying that. You should know who's doing the negotiation. Um, and then the other thing is you should already know from whoever's paying, how much are they
willing to put up before you actually get them the money. So, I might not have $5 million sitting around for me to make that payment, but they have to have that $5 million ready to go, right? Um, because it might take me 10 10 days to actually get those funds ready to liquidate and sell. So, that's another thing that you have to ask that that company that's going to be paying, like what do they have on reserves that they can pay right away that they know you're good for. And to be clear, all of these relationships should be set up well in advance of an event happening. If you are waiting for an event to happen to
then go figure out who these conversations are going to happen with, you're dead. Like, just forget about it. Shut your doors, right? like part of your when you go get your cyber liability insurance you should think what partners do they recommend to their other clients that do all of these different types of services they typically have a couple that they will offer and say these are the ones go have conversations with them whether it's IR plans whether that's ransomware negotiations you need to be having all this set up and uh conversed about upfront yeah the the panelists that you've heard up here have made the made the statement several times which I I can't can't do anything but reinforce
which is you've got to know as much as you can in advance. You have to have your playbooks built in advance. You have to have as much of the decision making in advance because deciding in the room on the fly in the middle of an incident is not going to do anything but hurt you. And as Larry mentioned, your insurance binder is critical. It will tell you who you can work with and get paid back for their services. Because if your if your insurance binder says they only will allow you to use CrowdStrike on Mandian for forensics and you decide to pull in your buddy Bob from down the street, well that's not covered. Doesn't
matter how much Bob's going to charge you. It's not covered under your insurance binder. You then have to negotiate on the fly. And you can get them added fairly easily. Yes. If you do it in advance. Let me add one more term for everybody understand. Of office of foreign access asset control. Basically, Treasury Department will list a whole bunch of baddies and if you send money to them in any form, you're considered to have violated federal law by doing so. Yeah, that's that's jail time for whoever made that decision. Yeah. I'll just add the good thing too about having like he's saying the the crisis management plans defined and all of that and kind of knowing what your options
are is like since I'm on the pay side, I'll play this. you can actually begin, like they're saying, negotiating and starting going down that line, but in the meantime, you're still trying to come back up. So that so buying time is also very important in here where you may start having those conversations. You may start trying to engage your insurance and all that stuff and and even, you know, starting having someone else start talks with them. You may still not decide to do it because now you've maybe bought enough time in some scenarios to actually come back up before you have to make that decision. I'd like to challenge something that Larry said a couple minutes ago about
the role of government. I don't want to derail the whole panel about the role of government, but I think it is their job to consider the greater good. Right? If you add up the impact of cyber crime across the nation or globally rather and compare it to the gross domestic product of nations, it's number three behind the US and China, right? So I think it is the government's job to consider the greater good the impact that this is having on all of us and go after the incentives right and and outlaw these things. So I think that's polyianish sorry government employee people get in the government for themselves for the most part the Mr. Smith goes to Washington was Frank
Copper movies from the 30s and 40s. Sorry I'm getting a little bit jaded as I get older. Old Jar means I'm older. Yeah, I'm getting a little Yeah, I was a a former employee of the British government and I worked with the the British intelligence community. Um, and I've led kidnap and ransom negotiations in the continent of uh Africa and South Africa and also in Asia. And when I say kidnap and ransom negotiations, I mean KN&R, which is human life on the line and uh and at that point, I don't mind telling you that it becomes less of a business decision. It becomes more of a personal decision. These things cannot take personal emotions into account.
Nobody's dying here to this point. We're an e-commerce company, right? So lives are not on the line. When you're healthare, a little bit differently when your executives have been kidnapped by a gang as they arrive in country and that gang is sponsored by the government of that country and so they're being held in order to extort money from you in order under the guise of paying some kind of madeup tax stuff. That's where you've got life safety on the line. It's a very very different decision. Exactly. And just like he just said, even if the regulators come out, if the business determines that they need to do that because that's the best decision for that business, it's very
likely that that's still less having the fine from the regulators than it would be having not moved forward with the decision. So they have to consider both. I I I'll say like um I think the government's doing a better job. I mean, I'm former FBI. I we at that time did have a very black and white view. They're they're doing a much better job of there's no more black and white view of like you can't do this, you can't do that. They're doing a much better job of building those relationships, understanding where the business is coming from, but they'll always have an understanding of a bigger picture like you said of there might be there might
be forces at play that just the private sector is not aware of and making those decisions can hurt can hurt far worse than you really are are thinking about. So all of those things come into play and I think that they're coming back now trying to say we get we probably came in a little bit too hard on the black and white either you know you don't ever pay but I think they're hoping for a seat at the table. One they have a treasure trove of information that might be able to help you get out of it and two they do have a piece of a bigger play there that they might be able to um provide
you insight to. And and reality is if um they are uh if if you're a larger company and you you're starting to see this more, they're they're being more public about it. Um there's a lot where they're starting to jointly take down bad actors and and and they need the private sector's help on that. So I wouldn't be so quick to just write them off. I think there's a lot of value they can play in there. In addition, any OFAC fines that would be levied for something like this, it depends on how you engage your regulators. So the key part is being transparent with all parties including your regulatory bodies because they can come back and sanction fines,
cease and desist orders, anything against you. I came from the financial services background. However, how you handled it and if you're transparent with them can either reduce those fines and in some case eliminate the fines because you've made them partners in driving that through. So yeah. And so I I'll agree with everyone here. They're a lot better today than they were, right? But back in the day, and I'm saying back in the day, like mid 2000s, it was a very this is the line type thing. And they were not trying to work with private business, right? Really awake now. 100% 100% agree with you. It's very black and white. You don't very black and white. And so they're they're now
doing a lot better because they recognize that we're all in this together. and and being a former military officer and having run information warfare at the Pentagon, I I get that there are always bodies happening and movements happening that the regular everyday person won't have any insight to. But now it's starting to get better, but we've it's been a long road to get to this. Yeah, I was just going to say completely agree with what I hear the panelists saying in the sense of transparency matters, right? You definitely got to involve the regulatory or you got to involve, you know, the FBI, you know, depending on type the type of incident, right? That'll tell you who you need to
involve. But the sooner the better. I mean, if I Brett and I were talking before this uh where, you know, we were talking about, you know, the Solar Winds case or we were talking about also the Uber case, right? Whether you agree or or disagree, I mean, I personally disagree with the CISO going to jail. Like, I don't think I think there's a lot more decision makers in a company than the CISO. Um but you know in in the case of Uber and um yeah Joe Sullivan it was more of a case of he wasn't transparent like they you know they stopped the bad actors. They didn't leak any data because they got um pretty much
they signed that got the NDA. They figured out who the threat actors were. Um but then you know after I mean they they weren't transparent. They didn't tell they didn't uh you know share that information and then I think another organization got hit right after that by the same criminal gang. So, let's be clear, it's all about transparency because again, as a public company, right, we're we're talking about big business as well. As a public company, you have to be transparent. And if you as a CISO are getting up at conferences like this and you're telling the whole world publicly recorded streamed on YouTube, if you're telling them your security controls are absolutely topnotch, the best A1 level security,
you patch everything within 24 hours, there are no vulnerabilities in your environment. I'm the CISO for ABC Corp. Thank you very much. If that happens, that's going to sway the lens of the average investor. The average investor isn't big huge stock brokers. This is like your mom and pop shop. They're going to say, "Well, Joe Sullivan says the security is absolutely great. I'm going to throw a ton of money into ABC Corp." That's fraud. The SEC will come after you and you will go to jail. So, let's be clear. I'm against CISOs being jailed, but I am absolutely 100% against CISOs talking on a public stage and swaying the lens of the average investor. Transparency is key. Yeah. And
one other thing to consider is you look at different liabilities, regulatory risk, financial risk, but there's also the legal risk. And so what happens, you get opportunistic law firms. They're waiting for that next 8K to drop and they're just going to file a lawsuit. Even if it's totally without merit, you know, give us a few hundred,000, we'll go away. They're almost as bad as the ransomware operators in terms of their ethics. It's just they use a different thing. They use the courts instead of Bitcoin. It's it's as if by magic. So Gmarks teed that up. As Larry knows, I was up in Washington DC two weeks ago. um under a deposition and uh I work as
an expert witness representing defense council um and postbach litigation. Thank you Gart for that cue because postbach litigation is a $51 billion industry because the ambulance chasers the corporate ambulance chasers are going after organizations that have been breached getting a whole bunch of people together who feel a little bit disgruntled about it and launching class action against it. So false breach litigation, the only way to protect yourself against that is by learning from those lessons and being transparent and fixing the problems you identify in the first place. Let's ask a quick question. How many people in here have received, hey, join this class action letter, right? They're right. That's that's what we're talking about right here. That's a
51 billion business. Now, what percentage of that 51 billion you think actually goes to the consumers that were impacted? No. 20%. Three. Three. Lawyers eat up the rest. 3%. I actually did one of those things many, many years ago. It was a law and they, hey, you lost money in the stock, blah, blah, blah. I finally got a check for three cents. Literally three cent check saying you lost a few hundred bucks. I cash it just because it would cost the money to process the check but after that I didn't sign up for these you just cleanly G mark is so punk rock I love you man so I wanna I want to slightly pivot but still go back to one of the
things to think about and this was something okay this is going to sound like a weird question just go with me how many of you guys in here have ever had to deal with termites anybody okay good so I took over my parents house a while back and found out that we had termites and we had to tent in order to get rid of them so in my case we I look at as I had to pay the ransom We had to get them out. We're going to tent it. The Orcin ransom. I like um and so then it was like, okay, now I'm paranoid of how in the world do I make sure that this doesn't happen again. So
now we're going to put in controls. So I put in perimeter stuff. We have a, you know, an annual check. Great. We fast forward. Everything's good. You know, controls are working. And then all of a sudden, I'm I'm sitting in my house about three or four weeks ago, and I had bought these awesome bar stools. Love them. And I'm like, "Mom, why are you like why is your makeup on the chair?" She's like, "That's not my makeup." And I'm like, "Well, what the flip in the world?" And I finally realized it kind of looks like powder. And I'm like, "Are they wooden bar stools by any chance?" They are wooden bar stools. Um, unbeknownst to me, a threat actor that I
was not aware of, something called a powder post beetle that I had introduced into the house. My pest I call my pest control. I'm going to call in my, you know, auditors. Hey, come take a look at this. What is What is And they're like, "Get get them out now. Get them out." and we're going to hope that they haven't made it into anything else in the house. And so I it's I use that as an analogy. I was like, man, this is a perfect threat actor scenario analogy. Insider threat now introduced by the CESO. I like it herself, right? Because only to find out that, you know, I didn't know powderpost beles can actually live inside wood for years
before they ever come out. So it's like a freaking Trojan horse just sitting there waiting, you know, to time bomb off on you. The sales of wooden furniture in this audience went down. Yeah, but it's one of those things of how in the world it's like how in the world do you make sure that you have closed every single possible vector of an attack? Even in my house, it's like do I have it's like, oh, there's a hole. I got to go fill it. Like IKEA and the plastics industry, thanks you for your service. So, it's it's one of those things of it's having the tight controls in place. That's the point I'm going is
even when you have controls in place, there's still always a risk of something else happening or a new threat actor being introduced or a new threat vector coming in. So, it is a constant thing to stay on top of. And every time that scenario comes up, one time it may be, hey, we paid it. The next time it may not. So, it's not a one-sizefits-all, onesize, you know, um, answer to this or by scenario. It's going to change for the company. Yeah. Even this company, even though we're on the pay side this time, I'm pretty sure our GRC director is coming behind us saying, "What are we going to do to make sure that next time
this doesn't happen?" So, we're expecting companies to continue to mature. So, even if you do it one time, it doesn't mean, and it shouldn't mean that it should happen again. And if you do the right thing, right? And also don't get but don't think just because you came in behind it that you've closed every possible entrance that's coming in. It's still going to be a risk that exists and continues. You have to love Jara for pulling this squirly panel right back on track. I love that on the scenario. I was just going to say let's hear from our audience. Uh rank the risk for most to least worrying. Uh it looks like prolonged downtime is what you guys
picked. I completely agree. uh data leak second reputation loss third paying criminal question for the audience based on these results how many of you are in a technical role or have been in a technical role for your career okay non-technical just because All right okay okay all right all right it's interesting because the top two here are predominantly technical right I mean that that's that's really interesting I'm just curious as to whether you think that swayed your um your position as opposed to down at the bottom you've got regulatory fines paying criminals reputation loss. Um, yes. Yes, sir. I'm coming. So, on the first one, even I raised my hand for the prolonged downtime because
even though the language is technical as downtime, I view that as loss of revenue. So, that's that's how I interpreted the first line. Fantastic. Good. Yes, ma'am. kind of say the similar um thing because for me I kind of put reputation loss under or reputation loss is your data leak and your prolonged uh downtime right in my eyes. Um for me that's saying hey you have customers that can't access your site they're not going to come back reputation loss. uh you see that there's a data leak and why haven't you guys told us or I'm uh I'm seeing my information floating around that's reputation loss um but on top of that um I would like to hear from you if there
is the sort of threat actor that's saying hey we have your data how are you going to ensure that this data is correct because I have been in situations where the CTI team has come to us and they're like hey we're seeing accounts with uh credentials online but those people haven't worked there for like three years, right? So, are you are you sure that what you're paying for is current and actual usable data or are these uh things that they're just sort of making up? Because it did say 80% of the things are encrypted. Are they actually taking actual things or are they just putting in BS because they can't? when you get So I think so I think that
goes back to right when when this type of scenario happens there's like I said some hopefully some type of crisis management team that's being enacted and there's an insight um incident response plan that's being enacted where somebody's going to look for what's really happening to validate this information so that before a decision is made hopefully that the the leadership team has all of the as much as we can accurate information to base that off of. So, if the incident response team comes back and say, "Hey, wait a minute. I I'm not sure that what they're saying is legit because I've went back and we actually do have something else going on or maybe we need to be less concerned
about this because our investigation has now revealed this, we may change our approach." So, again, we need to buy time. We need to buy time to allow our incident response teams to do what they have to do before we make that final decision. Absolutely agreed. You want to validate what was exposed. So Steve brought it up at the beginning of the cyber killchain and some of those in your incident response plan. Hopefully you've got folks that can run parallel to find and validate what was Xfilled and then at the other time trying to close all the back doors and finding all the command and control components. So it's key that you're able to evict them
and then you're able to close that but also find out what was taken. So buying time is those components. You have to assess those and that goes into that transparency and materiality in determining what was going on as well. Gentleman in the back. Hey, Joey Hernandez with Sofos. Hey Larry, great to see you here and and I know there was another person talked about their background in military. I think one of the things that we learn in the military is exercising and I think what balances some of this what people have said and having the fact that folks raise their hand from a technical standpoint is going back and exercising. What you heard today from this panel is really
critical to understand where everything plays because the problem is we don't we forget that the adversary has a say in what we do. What we've seen from the incident response process is that very often some of the threat actors will go into the files and they'll find out specifically what your insurance policy says and they'll see what that level is, what you're willing to pay and that's how they understand what you're going to be able to negotiate to. So it's good to remember those key things that hey here's what we have in the plan, here's what we have in the playbook. For the folks that focus on the technical side, go back and say hey we need to do an
exercise. We need to focus on getting all these people, even getting the cyber uh insurance folks to come out and play, some of your vendors to come and be part of your exercise so you can work through the scenario as the team up there said preparing way in advance of this actually occurring in your environment. Yeah, I would say so yes, you should always exercise your technical, but your more complicated stuff is going to be the exercising of what has to happen across the organization. Who does what, when, where, and who gets to make the decisions. So uh technical yes and that should be done on a regular basis but um I think a lot of the times where you'll
see it fall short is you don't see it exercised across the organization and that is where it's really going to jam you up. Your cyberinsur will usually provide some resources to do an incident tabletop across your organization. So depending on your insurance the binder but they don't always mandate it. That that's the challenge. They may provide some of those resources, but they don't mandate it. Like, as an executive leader, you have to have an executive tabletop at least once a year. You would be amazed at how inept CEOs and CMOs and CFOs are in understanding their responsibilities during an incident. They their role when they come in, they're like, "Oh, we had an incident. Hey, CISA, what are you doing?" No, no.
What are you doing, sir? Like, ma'am, what like this is what you need to do, right? you've got to go to the press, we've got to contact the outside counsel. Like there are all of these steps that they like we often take for granted that because they're CEO or chief CFO or whatever C in the organization that they automatically know all of the roles and responsibilities that they have to do for every scenario and that is far from the case. So, as it relates to incidents and incident response, you must must exercise this with them on at least an annual basis at a minimum. What I do when I build out these tabletops is I
make sure that one of the key decision makers is on an airplane for several hours and their Wi-Fi is out, so you can't reach her. And they say, "Well, only the CEO can make that decision. You can't reach her. What are you going to do?" In five hours, the place is going to be gone. And so, when you add those little twists and turns into the playbooks, you force them to go back and say, "We need to change our policy." and procedures to adapt to these contingencies because we didn't think of them and if you get somebody who's writing a tabletop who thinks of these things it'll force you into uncomfortable positions and go fix
stuff. Go ahead. Um these are great insights. Thank you. Uh my name is Virali. I have two questions. Uh the first one is to uh to extend uh the scenario a little bit where um the clock is ticking, stock took a nose dive and a business made a decision that we are ready to pay the ransom but the CISO couldn't find the back door. Uh it could be anywhere like uh you know you might have a subsidiary or a bunch of subsidiaries that are part of your parent company which you didn't pay much attention to. You trust them so well because they are part of yours and could be that's where the attack originated from. Right? So anyway so
what would what would how would how would CISO react or how should CISO handle that situation if if you don't know how you are breached. Yeah. if if you if you don't know that you've closed the door and kudos to this gentleman because he's the first person in our panelists and the room that's mentioned third party supply chain risk. So nice job. All right. Yeah. So how how if you haven't identified the back door, if you haven't confirmed that you have contained the threat so you can move to eradication whether you pay or not how are you going to address that? So I I think the main thing is as we're going to go back to
everything you guys have been saying about your tabletops and everything third party needs to be included in that where again it's a risk scenario. What do each one of these open vectors present as a risk and do you know your open vectors? That is not a time to do that at the time of the incident. The time to do that is to engage for those that do have compliance teams to come in or your audit teams and say hey we need to be able to know all of the various places where that's what a risk registers for. That is what you should know that. And quite often um I will say you know GRC and audit can get
downplayed because everybody thinks they're superfluous. Everybody needs security but you know it's one of those things of ah maybe compliance isn't as important but compliance really does play a very key role in the organization to help um the ma management prior to it getting to audit. Audit is your last line of defense. Your compliance teams are the ones that should be in there setting policies, working with the sysos, working with the organization and bridging those gaps to ensure that all of those things are there and ensuring completeness and accuracy. It's one of the things that um that it's an audit term that comes with it which is how do you know that the report you pulled down
is complete and accurate. How do you know that you know everything that is sitting on your network? And if we go and pull our network and you don't know what it is, okay, great. You don't know what it is, but now who's doing something to find out what it is? not waiting for the event to happen but going ahead and doing all of that proactively. The incident response on the uh kind of thirdparty side cuts both ways, right? So in the ransomware event here, you could potentially have extranet connections to your business partners, right? Um they could be infiltrated. It could come back through those channels. So your incident response team just can't look at your
own firewalls and figure out what the heck's going on. You have to look at all your B2B VPN connections and everything you have with your third parties because that malware could traverse both ways. It goes through there and then if it traverses to them, you're on the hook and you're accountable for some of those as well. So, if you don't mind, I'll I'll jump on that. Um, first ransomware incident where the organization I was with uh paid the ransom, um, we were collateral damage. Uh because the organization that was first hit was Chub, the cyber insurance broker. Uh look it up. It's in their SEC filings. So I'm not telling you anything that it wasn't public. And likewise, we were
public company. It was in our SEC filings. Um but Chub was hit. They were breached in their Malaysian data center. I worked with Mora Caliando, their privacy officer, and Dave Cow, their CISO. And we had Chub employees in our site. So it was our customer that was hit. And because they were in our site on our network working with their representatives in our organization, guess who got hit next? So it just goes to show from a third party perspective. We were the third party, but they introduced it into us. So it does work both ways to to the gentleman's question and to our panelists, I'd love to just skip it down the line to be able to say third party
components. What's your what's your considerations and and take each one of our panelists? So I've mentioned it, you know, at the at the outset just kind of those connectivity partners. Um, you're always dependent on on some other party to provide services. So when we look at it from a compliance standpoint, we're always interested in not just third parties, but in a lot of cases fourth and fifth parties is that those go through. Now, as everybody started to do SAS services and everything else, it's looking at those through the lens of how they're both protecting your data and if there's connectivity. So, I think it's the it's behooves you to understand where your data is and then how you're
directly or indirectly connected to those third party vendors. Next panelist very passionate about the third party risk management issue. I it's approximately 60% of our you know exploited vulnerabilities are coming through third parties as a collective right so definitely should be in our the top of our our agenda uh sure that to build on that I'd like to point out the importance of the contractual agreements right and how tied off we have gotten at TGH with our third party risk management assessment process and our contracting to make sure that the configuration and the terms that we agree arecept acceptable from a risk standpoint to the hospital system are reflected in that contract. So that that's our our lever,
right? That's where it actually becomes a commitment. So it's not understanding that we are talking about ABC Corp here just before we before still ABC Corp, but I mean it's it's something we're very proud of and I think it's a best practice, right, to tie off with legal at the contractual level for every third party system. And then of course the continuous monitoring of the risk profile. I think it's the business decision that we're talking about here with whether or not to pay is not the business decision maybe we should be talking about. It's it's whether we're going to invest in these things upfront so that we can reduce the likelihood that they happen. Right. That's where we
need to help the business understand what they're up against. I was just going to say, Dan, to that point, I'm assuming you also would include in that contract negotiation with the third party um liability coverage, right? Liability caps are negotiated in in the quantified output of the risk assessment helps inform what that liability cap should be. So, communicating in those terms is is key for that process. The echo chamber you're hearing throughout, I hope everybody is recognizing this, is proactivity, right? Proper planning prevents everything you see here, right? Um, so really important. We're talking about being proactive. We're talking about as much of this being in play prior to, not during. So yeah, let's let's quickly
keep it moving. Yeah, go ahead. I have nothing to add. We have the same processes and that's what I would recommend doing. Get that get all that all in place and then have a way to continuously monitor those vendors. So one of the things I'm going to bring up is not just where your connection points are, but one of the things we have to start thinking about is who and the vendors actually have access in your system. not from a who exploited a credentials but what if the employee in the vendor is the person doing the exploitation when you're looking at things like what happened with no before where they ended up with they found them
very quickly but when they had a operative from uh North Korea a remote threat a remote foreign worker who all of a sudden is getting access into can you imagine hiring a remote foreign worker from North Korea right um but what if your vendors you know vendor A that's you know working with us and they have and and who who is to say that they haven't flipped or they weren't a secret person in it. I mean, it's it's awful to think you have to be that cynical, but that's one of the risks we do have with third party access. So, that's one of the things of understanding what that third party is doing to to make sure not
just the connection points are secure and such, but also what are their hiring practices. Now, sorry, very good point. Yes. So, going back to the scenario, um, so in this particular case, if there so obviously we're now in the phase where we're obviously investigating. So hopefully we have those contracts in place. So for this scenario, we should be bringing those up, trying to make sure that legal is engaged. I think it said that they were engaged because they were looking at the insurance and everything like that, but also from the third party perspective. So if we do run across uh the event that there's a third party involved with what we're going through, then we need to make sure that
legal and corporate compliance are involved so that they're reaching out to them, that they're being involved into our um into our response. Who who is your biggest third party risk by name? You know it. It's Microsoft. Who's probably next? Salesforce, Amazon, wherever you happen to put your data up there in the cloud. Can you as a small or medium-sized business or even as a large business go to Microsoft and demand an audit of their facilities? You cannot. And so as a result with a third party risk is a little bit your number 5,96 in the queue. We'll get you. Exactly. We'll get to you. It's like Beetlejuice, right? You get your number, it's like this long now serving number
11. And so what comes out of that is you find out is that to manage it, we have to rely on third-party sources for third parties. For example, Black Kite will go ahead is, you know, not just name dropping, but that's one I'm familiar with where they will come back and they say from all the publicly available data out here, here's a scorecard on this particular vendor. Do you want to do business with them? It's kind of like the Better Business Bureau. They're great. Speaking of cyber extortion, yeah, it's the same idea. Well, and because I have had to fill out these forms as a CISO where they have 240 different questions about what about
this and they're always different from every supplier. It's like, can't we standardize that? Yeah, we cannot. So, I I want to go back and more directly answer his question because his question was aligned to, okay, you're going to pay the ransom. You're prepared to pay it, but you have yet to find Well, you're prepared to pay it, right? Well, we're prepared to pay it, right? So, but we have yet to find the actual source of the breach. Understand that that is a long trail. Sometimes you may never find the source. You're going to find a lot of breadcrumbs that got to the end result, but you may never find the source. So, as that's being walked,
all of these things are happening simultaneously. Sometimes you may find it before, but at at a minimum, you've got some sort of forensics team that is going down the path of looking at all the breadcrumbs that got left that led to the breach. And as they walk that back, three months later, they may find it was a third party, right? But along the way, you have a responsibility as you're checking in with that forensics team to start shutting down the bridges where they left those breadcrumbs to fix where those controls were broken. Narrator's voice, it's always a person. 80% of all breaches are as a result of human error. We have a question down here. Oh, yeah. Go ahead. Yes. How you
doing? He cannot ask a question. Um, so what if you hire a marketing agency and they're they have multiple vendors. How do you what's the proper way to get that third party? You mean the fourth party? Yeah, the fourth and fifth and everything like that. What are the the how's that conversation normally go with the market? It's prescriptive, right? You you most likely have a vendor process that goes in and talks about what happens at the fourth party level as well in your contract with that third party. But you have to be careful too at some point. um it has to be their decision who they're using and based on that or otherwise you're being
prescriptive and telling them what they can and cannot use and then they can come back and say that we had to use that right I can tell you that from the external auditor's perspective what I am starting to see in the industry is that they are starting to ask now those questions more of the companies of how are you managing your third party risks and how are you managing your fourth and fifth party risks y whereas before that wasn't really part of audits we are now starting to see that come into the surface organization control reports um as well as some of the financial audits. And ABC Corp is a is an e-commerce company and PCI has had this
since um version three where it was requirement 11 and then into requirement 12 where it was like have you validated that your third parties are compliant because therefore if they're not you're not compliant. Right? So it's it's been there a while. This is not new. Um the hardest part is uh trying to get those third parties to disclose that. Right? So we can go through Dan mentioned a little bit about kind of the best practices. We do this with our company as well as here's a checklist of the things we want and those are some of the clauses that we're going to demand in the contracts up front. Disclose all your fourth parties. It's a little
easier said than done, right? And it depends on whether the vendor that you're working with is also in your industry and recognizes the regulatory pressures that you may be under. So it it cuts a lot of different ways. It's and sometimes comes down to a business choice and who's going to perform the best service and whether they can comply with some of your regulatory items, your security components and other items and what risks you're willing to take. I was just going to jump in and say uh this is actually ties to everything we're talking about. Maybe not the third party, but we're talking about if you don't know what the root cause was of the breach, um you know, what do you do?
um looks like within the first 24 hours of ransom, most of you have said, "Hey, what you're going to focus and prioritize on is you're going to figure out root cause. You're going to try to contain and investigate, do forensics." Um and then 3% of you said you're going to restore operations in the NE in the first 24 hours. So, I'd like to hear um does anybody want to share why for the audience? How many of you were desperately trying to find option E which isn't England in the 1966 World Cup final? It's all of the above, right? Yeah, that's a good call out. Feel like doing a John Burger and shut the camera down. Um
from a previous uh bides, but uh basically negotiation with the attacker. Um, if a uh basically it becomes a nation state and you have a uh F3 EAD kinetic opportunity, go for it. Yep. Anyone else want to weigh in on uh this one?
Warhead on a forehead, right?
Can't you can't really do that in the private sector. It's frowned upon. It's a little hard, right? At the bar, we may ask about that and have that conversation privately, but yeah. No, we'll just call in Iron Man.
First, I'll lead with number one. Attribution matters. Uh, but in absence of option E, uh, I think the most logical conclusion is B because you can't really do the others without first investigating. Yes. So, hang on. Go one more. Sorry. Thank you for Yeah. And know so I think I was one of the first to answer pick B because um when you were talking about who's technical I'm pretty technical and for me if someone got in they might still be in and these are active worms or viruses or whatever you whatever they are and they might still actively be doing danger. So, I'm thinking why worry about all the other stuff? Make sure whatever is causing danger stops and
then you can worry about the cleanup later. And your traditional incident response, preparation identification containment eradication recovery lessons learned at Pickerl, it's exactly what 94% of you get an A. Yeah. And this is the cyber security team is option B. So, they would be the ones mostly contained with that. Um the other options up up there are really like the business leaders. So if something were to happen like this, you'd probably have like an incident response team responding to the incident and containing and maintaining and reporting up to leadership and then the leadership teams across various departments are probably doing the other items. So there's some things that are going to be done in parallel. But really
importantly, everything you see here, you've got you've got a a complete division of function. Um restoring operations it right. Let's let's really get down to it. They're not gonna they're not going to stop doing what they're doing. Security is containing and investigating, right? Communicating with your customers and regulars. If you're not doing that during an incident, then you're already in trouble. And then negotiating with the attackers. All of these things are separate channels that are being undertaken. But you should not be pulling people away from the containment and investigation to communicate with your internal stakeholders or your customers. You should be splitting those responsibilities and chains to be able to do option E, all of the above. And I
want to add a word to that though because and in this company as I'm sure it's when there is a confirmed incident, not just simply because we think there's something going on. It's once there is a confirmed incident does communication start and not before that. The last thing you want to do is cry wolf. Right. So So I I I want to I'm going to get on the soap box for a hot second. So, how many people in the room are CISOs? Raise your hand. Okay. How many people in the room want to be CESOs? Okay. So, so, so no, but but I I knew that was going to be the statistic. So, and I want to bring
this up because of this one scenario I'm about to go through. So, if you notice, an incident has been confirmed. What team is executing trying to contain the incident? The security team. Right. Okay. Now, the risk that was likely exploited, do you think that the security team had identified it? Possibly. Okay. Do you think that the security team had any choice in whether the company chose to mitigate it or not? Nope. That's the CISO and that's the problem. the CISO can identify all the risk in the world. If the business says no, it's fine. We are still ultimately responsible for it because when the goes down, we're the ones who are up in the middle of the night with our team,
with the incident manager. So, understand the role of the CISO. You don't have the control that most people think the CISO does. We do not have the control. We are the ones following up on the back end. But when we our teams identify the risk and we report it up to the board and the executive leadership team, they then tell us which ones they are willing to accept and which ones they are not. Yeah. And really really importantly, Larry's making a really valid point here, especially for those of you in the room, no matter which stage of your career you're at with aspirations to be a CISO or similar, right? Christina and I have both been a CIO for for different
companies and different sizes of companies. The CIO is the older component in the boardroom. The CISO is the younger component in the boardroom. It has for decades been a business partner and a business enabler. Security has often been seen for the same amount of time as being a cost center and an inconvenience. Don't be that CISO, right? And a blocker, right? the the the office of no as it's been often called, right? So a CISO is because I said so, right? I mean, that's not what you want to be, right? So it's important to understand that. And even if you become a CISO and you are great at being a business leader and a business enabler,
helping them to understand the value security has to enable their business unit to generate revenue securely. You still have no control. At the end of the day, the business makes the decision, you have to live with it. So, a lot of people there's this glamour associated with the role of CISO because it's the top of the food chain in cyber. Yeah. You're all rock stars, right? Everybody up here, right? Yes. Well, but it it there's a lot of this that happens that people just don't realize about the role. So to talk about careers real quick too, you'll al you you will also start seeing there's a new role that is being created that's coming up called the Bisso and that is
specifically to ensure that security is taking it does not stand for The B is not It's business. Okay, it's business. It's the business information security officer and that's what they're looking for is someone who is going to straddle that line between what security needs and what the business needs. um you know security wants to install everything but it can be an impedance to the business. So getting someone in that can understand that and say hey how do we hit both scenarios you're starting to see those come up in the organizations as well and I'm in the process of deliver building building out and delivering a biso training for one of my clients and their besos are dual-headed
that is to say the controller is a boso in the finance a vice president of production is a boso these are not people sitting around with something that they need to do these are very busy executives that we're trying to help them understand sufficiently enough about cyber security that they can help shape the culture in their business units and because they have that authority of their primary job they can go ahead and influence them because I ask people usually two questions. How many people in your organization can screw things up with a computer? All of them. How many report to you? Almost none of them. And as a result, as a CISO, what you have to learn are
influence strategies. You cannot rely on positional authority. You cannot rely on being able to say I'm the captain or this is my rank. You must do it. Rather, you have to have a way of influencing not only the people who are doing things but the executives who are making the decisions and ultimately as Larry had said the board to try to convince them that this is a risk you probably should not accept. This is one you should either mitigate or a sign off for insurance or something but just don't live with it because it's going to come back and bite you. Right, Christina. The only thing I was going to add to that was I think uh I think the beast was a
really good point. I think it also too it depends on the organization um and the level of maturity, right? Um if you're at a financial services, you know, many years ago I was at Raymond James. Raymond James has a BISO program. They've had one for years. But if you're at ABC Corp 500 million, you're probably dealing with the general counsel. And I found that out the hard way. Um I was at one of you know in a CISO role and we had an investigation and I immediately engaged u who would be my IR partner uh firm and I had them uh they were engaged. We had set they had our logs. I mean they were working triage and my
general counsel came and uh we we had to switch who we were using to who the general counsel wanted to use. That was a hard pill to swallow. I was a little younger uh a little more feisty maybe than I am now. So he heard about it. But uh you know that was a good lesson for me looking back that it really is a shared um I mean incident response it's shared. It's not just technical. It's not just getting the bad guy or you know knocking out the threat. It's you know how do you handle the business side and who are you working with? And the more you the lesson learned from that was you
know doing those tabletops doing more upfront so that you know next time that wasn't a surprise to me right I knew who to engage and who to be involved with. That's a great point because um we've mentioned insurance a couple of times if you do have cyber insurance. Um you probably want to be working through with your council and engaging them first in any incident like this because if you don't they're going to reject your payment all 100% of the time. So in a lot of cases they're the ones from the panels they were talking about. They're going to dictate in some cases, depending on what it is, who you use and when you use them. And here's the reason
why your insurance won't pay out. So, I work with several different cyber insurance vendors as an adviser as well. And the reason that insurance doesn't pay out, the top reason that a cyber insurance vendor doesn't pay out, 35% of unpaid insurance claims are because there are poor detection and prevention controls in place. The next one down is 25% which is policies not being followed. You say you do something and you don't. It's so much better to have no policies and do whatever the you want rather than to have a policy and not do what it says. Um and then you get into limited coverage, third parties, and errors and emissions. But the top two, poor controls and not following
your policies, which um which are the GRC and internal audit hubs. She's loving that. She's like, "Yes." All right. We're going to in the interest of time, we're going to move through a few polling questions here as well. We've kept this pretty open. If you do have questions, please by all means raise your hand rather than getting into a full and if you have questions for the CISOs and you want to get those out, make sure that you ask those questions, too, because we're at that point. Um, I say while this one's populating, yeah, I'll I'll get out here. Hang on. And I'll throw in a quick ad while you're waiting. You want to hear more about
CISO stuff? I got a CISO tradecraft podcast. shameless plug, but it's free, so I'm not making any money off of it, but I got 233 weekly episodes out there. So, go look for it and you can add to your knowledge base. So, an interesting question I had, I don't want to get too far into it because this might turn into a whole thing, but so I'm a security researcher. I do it as a hobby, so I put out writeups of bugs I found after they're patched, of course. Um, but something I saw recently, there was some article somewhere, I forget where, uh, but there was like a YouTuber who had put out a YouTube video just for educational,
like, oh, here's how people make ransomware in Python or whatever. And someone was like, "No, you shouldn't be talking about that. We shouldn't be putting that out because that's how real people get hacked." So, I'm just curious, what are y'all's thoughts about people who put out resources which talk about, okay, here's what hacking looks like and here's maybe some tools, but obviously don't use that for evil or whatever or people who put out writeups after they've been patched or like how long they wait or do they put it out like immediately after and I know corporations they don't install updates immediately. They have to make sure it works with everything. So, how do y'all handle that and what are your thoughts
on people and how they disclose that? Yeah. So, uh, let let's go this way up up up the panel. What are your what what is your opinion of security researchers turning around and going, "You got a bug. I'm going to publish it." So, honestly, I think you have a very particular opinion about this. Yeah. So, so here's the reality. I I think it's a part of the ecosystem. I think it's a needed part of the ecosystem because at the end of the day, I think there are many organizations who wouldn't do if somebody didn't sort of push that button on them. So, I think it's something that's needed. I like the transparency. What I don't like and it's
an unfortunate aspect of just humans is people are taking that left damage humans, right? So, so they're misusing it in a way, right, that they shouldn't. But I think holding organizations accountable, it's a good thing. It's a good thing actually for just society as a whole.
Yeah, responsible disclosure, right? We're talking about responsible disclosure. But even if it's un even if it's irresponsible disclosure, here's here's the reality. The majority of these breaches or the majority of the issues that are found in some of these software, I am pretty sure uh some of the software companies knew about some of them. I'm not going to say all of them. But it's also impossible for us to develop a software or technology and understand every scenario possible in which it will be used. Don't forget it's not a flaw, it's a feature. Right. Don't say the word bug. Right. Right. So, so but I I think it's a balance. But I think people doing this openly and
sharing it, I think it's a good thing. I just ultimately do. And there's a concept of responsible disclosure and we talk about that like how many days you wait Google had that at zero day. Quick history lesson in the year 2000. I was with a company we did the first vulnerability summit. We invited people from all over to come up with the first set of rules for how do you release information about that and I was running it and I thought it was a little bit of fun. So I had one guy named Steve Lipner who ran security at Microsoft. So I sat had sitting next to him a little kid named Rainforest Puppy. Now, if you
remember RFP, what he had done is he had discovered the directory traversal vulnerability in IIS and so you could go up and out. What was kind of fun is people went around the room and introduced themselves. Hello, I'm Steven Lipner from Microsoft. And the guy says, "I am Rainforest Puppy." And the look on Steve's face was absolutely worth it. It was priceless. I'm waiting for a Homer Simpson moment like you. And he just looked at him and he like, "Why do you call yourself rainforest puppy?" and he looked up at him and just blinked his eye said what judge would put a rainforest puppy in jail. So that was this is all a true story. This is a true
story by the way. And so anyway he came out with after that meeting you know he came to the RFP RF policy where he took it and ran with it for himself. But the idea is what the idea of responsible disclosure says the information should go out. Vendors should be given an opportunity a reasonable time to answer it. Not 12 hours before we throw you out of the country or becau before we go ahead and we whack your software. At the same time, however, if you fail to go ahead and patch in that, that's on you. It's not on the researcher. Yeah, I have nothing to add. I agree with what they said. So, I um Larry mentioned it. It's
part of the ecosystem. Just because I mean if if you have people that are finding the bugs and even publishing it, if we didn't know about it, whether it's bugs or bombs or whatever it else it is that you're going to learn, somebody's going to know how to do it. Somebody's going to need to know how to undo it, right? So therefore, it is part of the ecosystem and it's whether or not we capitalize on that ability to go out and use them to say, "Hey, we know these other people are going to publish these things. You know what? Let's follow them or let's help them because that's what we need in order to make sure we're
safe." The bottom line is risk exists. How are you going to mitigate it? So, um, responsible disclosure for it for people who are showing how to hack online. Um, I'll just I'm just hopeful that there's going to be more good than bad, right? I think everything that we put out there, you can look at AI meant for good, it'll be used for bad. I think there's ethical hackers. I think there's people who need to understand how malware is built. They need to reverse engineer it. They need to help protect us. So, I'm all for it. Yeah. You know, we've been preaching about transparency all day, right? So, can't contradict ourselves now. And better at that than,
you know, the nation states that are also putting a ton of effort into security research and are sitting on these things. I'd much rather have it out in the open. Yeah, I'd concur with everything that's here. And I think the hardest part to your point is the companies that find out about it in terms of how you mitigate that risk or assess it internally and quickly because what happens now is the things that are being known exploits and those types of things or the the quick disclosures, the world of AI and the world of Showdan and everything else, those things are being exploited at a record pace. So e even if we thought we could patch it within 48
hours, somebody's probably exploited or at least tried to poke you with it in 24.
Yeah. Yeah. And the good thing is we have hopefully thread intel programs that are, you know, we have internal people that are looking at the same stuff that other people are looking at and that they're familiarizing themselves with it so that like she said they're, you know, developing the how to not do something right from what they're learning out there. A question. So, thank you for bringing it bringing up AI because this is the one of the, you know, an hour and a half without Before you jump in AI, one second. Does anybody disagree with this order? Because if I think we've already talked about this one, so I'm going to move it to the next
question in a second unless somebody wants to comment on it. If you want to comment, I'll leave it here. That's what I'm saying. Okay. I'm going to move this to the next screen after this gentleman asks. Go ahead. By the way, I'm not going to ask a question on AI. Uh so I'm going to flip it on its head and say I I believe that this problem will not be solved by AI but uh uh with all your experience right I would like to I would like to pick your brain on how you convince the board. I mean we talked a little bit about uh all the protective you know controls that we want to put in place and uh I mean when
you walk into the boardroom there is a finite amount of budget and cyber security is definitely not the top one priority for majority of the organizations. So I I'm I'd like to know what are the techniques that worked for you to pursue it you know to push this forward and uh I don't know I always ask for like 10 resources and get two so that's what I follow but I would like to know your from your experience. So Larry's already mentioned it twice and I support everything that Larry said um around influence because that word especially if you're coming up in your careers and you haven't really understood the importance of influence and the emotional capital that you need to have
the money in the bank the trust if you haven't built that start building it now because influence is really important for getting that buy in. So getting buy in. Let's let's go down the let's go down the panel because I know we're I'm looking at my clock and we're looking at time. So quickly as far as getting the buy in. Okay. Quickly. Oh boy. All right. Sorry, Larry. Quickly. I know that word's not in the Larry dictionary. The the the biggest thing is know your business as well as everybody in the room. If you don't understand exactly how you make money across the entire business, even though you're the CISO, you need to understand business almost
at the level of the CEO, CFO, CIO, like you need to know your business. Knowing that and then understanding the cyber impact on that so that when you communicate to the board, you are helping them understand in a dollars and cents term the impact to the bottom line based on cyber initiative. So when you're walking in there with your risk register, if they ask you about a particular risk on that, you've got a way to equate what the dollar signs are to the risk, right? For the particular business unit, for the business as a whole. The second thing is you need to have a friend on the board. And when I say a friend, I mean a mentor, someone
that you can dialogue with, right, outside of the boardroom who is going to you can send slides. You can say, "Hey, this is what I'm going to talk about this where they're sort of helping prep you." All of this ties to relationship and influence. The biggest thing is in is is relationship across the board. If you walk in there and they don't know who you are, you're never going to get anything. But if you walk in there and you have built a relationship with at different levels with each one, right, but you've got a relationship around there and you've got a reputation that precedes you, your ability to influence the room is way way easier when when
you're in a boardroom, just really make sure you understand what quickly means. Yes. Yes. Understand understand concise. Yes. The only thing I wanted to add was uh I agree with everything that we're hearing. Uh sometimes I would say especially if you're a newer CISO, you might not know how to translate technical risk to business risk and talk in business terms. I completely agree that if you can't figure that out, then what you're trying your ability to influence is going to be deeply hampen. It's going to be it's not going to be as good as it would if you know that. So if you don't know that, CIO knows. Completely agree. You you partner with folks. But the other thing you can do is
I mean before there was the chat GBT of the world that's an option today. You could go to chat GBT and you could say I'm in Xindustry. What are my what are the top threats in this industry? What are my talk top attack types? Right. That used to be in the Verizon DBIR. So that still comes out every year and it's a data data breach investigative report. Right. It's this week's podcast. Yeah. Oh, okay. Well, um, when I was, uh, much earlier in my career, I was trying, you know, I I I wasn't at a level of maturity where I really, um, I probably didn't know it yet, but I didn't really, um, I didn't know that you had to really
care about the business. I just assumed when I first took the first security role that everyone cared and they should care because that's the right thing to do. Well, they don't. they they're so busy themselves that you have to figure out well how do you talk to them about cyber in a manner that about something that they care about and I would just say you know whether it's partnering or whether it's you know today's world using chat GBT to figure out what are some of the things they care about or even you know going back to the Verizon DBR there's a lot of sources out there that can help you p identify what would be the crown jewels for this
organization or where can I get a start right so that they give me the time a day because when you're talking to a CEO you'll hear a term sometimes called What's my so what? Right? I've heard that in a few stops. And and at first it sounds kind of rude. You're like, uh, what do you mean what's my so what? And all they're trying to say is, I've got five minutes for you. Spit it out. Tell me what I need to know and tell me why I should care. Right? And you can use research and use your um peer groups and partners to figure that out. And just remember, there's always option C. And option C, no matter what you're
presenting, is do nothing. What happens if we do nothing? You will be asked that question often. You better have an answer for it. So, so one quick thing, one thing I've done in every CISO role that I've had, I'm sorry, just I just want to share those with everybody, right? Go for another. So, so is every business leader I knew how they were bonused. I met with them on a regular basis because everybody wants to make money. They are always bonus based on how their business unit does. So I met with them on a regular basis when I started with the company as the first CISO as a second whatever it was as that CISO. I would go in meet with every
business leader across the globe to understand how they made money personally, right? Not just what their business unit did did but how they make money because that people want to be incentivized. And then I would create a story a message so that when I met with them on a monthly or quarterly basis of the things I was doing that was going to help them make money. And let me summarize that in one talking about money and all of a sudden the pay the ransom just jumped. That's really interesting. Cyber is the business of revenue protection. Yes. Just remind yourself of that. Cyber is the business of revenue protection. And if all of your communication with
board members and executives stems from that fundamental understanding, you'll be as successful as this gentleman here. A lot of our audience have places to be and places to go. Jara. Okay. I'll make it very quick. Everything that Larry said, no. Um, but he did cover a lot of it. I'll just add and kind of emphasize what he's saying. It starts before the audit committee meeting or the board meeting. So everything that we're doing outside of that prepares for when we walk in there that the relationship is already built. And then I'll just add we're talking about business acumen, understanding the business, also knowing how to speak that language of the business. So even if you understand the
business, but when you get in the room, someone can still tell that you're a technical person, then you're not learning enough of how to actually speak the language. So you also have to do that as well. Um I will say being being an auditor, you learn very quickly that you have to do everything through influence. That's your only choice. But I would say if you're looking for things to study personally, pick up a book on psychology. Pick up a book on sales techniques. Um, pick up a book, Steve's going to kill me a second, grifting. Um, written by the White House ethically. Um, all of those things are how to influence people. They're not something
that you're going to learn in a technical book. This is all about Larry mentioned, everybody's mentioned it. all about relationship building and it's all about knowing that who your audience is and know you're trying to sell them on your um needs by making sure you're meeting theirs. Simon Sina, start with why. Yep. It's a it's a fantastic book. Um we talk about books. Uh start with why um because everybody has a why. I have nothing to add. That's all perfect. Yeah. In influence and confidence. You asked how. I'll add to speaking the language of the business. The factor analysis of information risk. The fair method is a way to quantify these risks. It gives us the ontology to you know put
that impact and probability equation uh you know do our risk analysis and then and put it into financial impact terms. The other thing I'll add um and I speak to our board regularly also understand the purpose of the board. The board is a fiduciary duty and they protect the shareholders. So you're part of the management team. So when you're presenting things, be confident. Your your metrics better be damn right. Right. And then you also better be able to explain it. And then when you present the challenges that are there, have an answer. Do never present a problem to the board that you don't have an answer for. You will paint yourself in a corner each and every time. Don't bring
problems, bring solutions. Correct. Be able to explain the why. Firmly believe in that. So when you can speak their language and the why it means something to them, that's it's gold. So it looks like most of the room still stuck with do not pay the ransom. Lost our side wins. I was just going to ask, is there anything that you guys wanted to ask? You went out of business though, but good luck with that. We got about 14 minutes. I know many of you trying to get to the closing keynote, but is there Yeah. If there's something you want to ask, go for it. I want it. So, as CESOs of the ABC Corp, you have
just gone through a ransomware event. You go before your board. What is that next program you champion based on the fact that the board is now listening because you just went through an event. What is that? You get a bigger budget. You've got a period of time. you're you're you're you're if you've ever worked for someone who has been part of a breach or if you've experienced the breach, the entire conversation shifts and it really will be what do you need and what isn't there? Um what are the priorities? and you're you're it's all going to go back to what you've already been saying, but now the checkbook's going to open up and you're going to start getting there and
then you then you're going to have a new pressure which is delivering in a short period of time all the things that you've said that you need to get done because don't forget you're going to be on I mean it should all be prioritized based on your risk risk assessments assessments. So keep who here likes memes? We all like memes, right? I'm not talking about the dank Sesame Street memes. Leave those things alone. But if you like memes, there's there's the there's an always been a very very prevalent meme. It's it's directly relevant um to what our panelists just said. Cyber security before the uh cyber security budget before the event. Cyber security budget after the event unless
unless they have been part of a breach. Yep. It it I mean I've come in and watched where someone who's been part of a breach joins the executive team. Specifically, if it's a CEO or CO, the conversation changes immediately. It's this isn't big enough. this like fix it. But you have to be careful. There's something called a halflife of awareness. And the halflife of awareness of an executive with regard to a cyber breach is about 3 to four weeks. And after 3 to four weeks, something else has come up. They can't get the shipping in and out. There's a tariff over here or whatever. And it decays like radioactivity. So you ought to have something in your back pocket at all
times just in case a breach happens. You can pull it out, put on the table, and say, "Press hard, sir. You're making three copies." This is a purchase order. I think it'll stay longer than that. Just like toxic waste and just like nuclear halflife. The moment you have a second incident, the first thing you're going to be asked is why didn't you unfocus after the first incident? How come we're going through this again? Yep. I would call that a career limiting move. Very much. I have I have seen at the board level where someone like they we were we I was coming as a cyber adviser and they were the CISO was asked a question of like
what would change if you had this or what would change if you had this and the priorities kept shifting and so to the board that's saying we don't understand what our actual risks are. If I give you five million, the first five should still get done plus an additional five. Not now my first five just changed. And that's what we were watching happen. And it's like we don't really understand what our risks are. So we need to take a step back. Learn about return on investment. Learn about it because every single dime you spend, you have to be able to show the return on investment to the business. So and I I was going to go there. So having a
breach in your organization is great from a expanding your checkbook, but it's also great in having a spotlight on you like a like you're in a rest of your life as well because you literally they are now watching. We just gave you an extra $50 million for your cyber whatever it is you said you need to do so we don't go through that pain again. the reporting that you're gonna have to do all of that. I got brought in by a board as the CESO to fix a breach that they came off of. So, they hired me in. I had an empty an open checkbook what for whatever I wanted to do. However, the level of reporting that I had to do
for that was unlike anything I'd ever done before because they wanted to understand how every penny was being utilized, the value was going to bring, and how it was going to ensure that that didn't happen again, which wasn't a thing, but they that's what they felt like we're giving this money, we're opening this checkbook because so that will never happen again. And I constantly had to tell them, listen, this is not does not mean we will never be breached. We are putting controls in place. We are right doing the right things, but it does not mean that we won't go through another breach. And it probably took three months of me saying that month after month after month
before they realized it. Remember about what assessing risk is all about. It's around probability, likelihood, and impact. And by putting controls in place, you are reducing the likelihood and you are also mitigating or minimizing the impact for when it does happen. Hopefully, you make it less likely, but when it does happen, you're going to reduce the impact. And for for the upand cominging sisos and that are in the group and others, compliance and audit have always often been seen as enemies to the business. They are not they are your partners. Yes. If you get a really good team, that's what they're there for. you're not in those incidents alone. It's not on you to figure it out
all alone. Utilize those teams to help you figure out what it needs to be able to prevent it. That's why it's called the three lines of defense. So, and you know, outside of an incident, you know, the best thing that's ever helped me get the biggest budget I needed, compliance, a compliance team. I partnered with them and got the biggest budgets I could ever ask for through working with them and creating a cohesive strategy that I could go to. Just give your auditors stuff to do because if you don't, they'll find stuff to do.
Okay. All right.
So,
well, take take just take security out of the equation. Everybody's at odds if you think about it, right? The CFO's job is to spend as little as possible and make as much as possible. And sales will tell you you need to spend money to make money, right? And then your IT team is saying that I don't have enough money to to build the cutting edge stuff. Everything comes down to what we all set up here before is your relationships, your ability to influence and how you influence. And ultimately that's going to come from do they feel that they that um you understand what they're trying to achieve and that through what you're trying to do it's going to ultimately
help them through what they're trying to achieve. If you can't get onto a common ground which it may take some time but if you can't get to that common ground it's not going to work and and it's not a security thing. It really is across the board. If you don't get to a common ground with your auditors and with the with the with the internal audit, external audit, with the compliance teams, you're going to have problems. There's people who sit there and say, "Audit, stay away. You don't know what you're talking about." Right? All that's going to do is create a friction of I'll show you what I know that I know what I'm talking about. I'm going to find
everything. Versus, I do need money. Audit, let's partner. This is where my controls are. This is where I'm worried about. can you go in and look and make sure that I'm not being overreacting or that I don't have the appropriate budget. So, I think with everything, it's going to always come back down to your relationships and your influence. And it's no, I mean, as you move up in your career, how do you get your team who's been beaten down, who gets unrealistic deadlines to deliver and be happy and find that balance, right? It's going to be your influencing your relationships. And let's be honest, Oh, no. I was just going to say people won't work for you until you work for them.
That's one of my favorite like leadership sayings, but it kind of applies here too. Lead with a handshake, not with a fist. Yeah. You have to recognize too that sometimes it's not the business. Sometimes it is just individuals you're coming up against. And that becomes a whole different story. But if you're looking at a well a well-run business, it works like a clock. Every cog fits right in and it and you know it works until you get the one that's timing is off and it's slightly skipping. So when you partner with them again, you sit down, you mentioned a unified vision. if everybody's got a unified vision of understanding all the different needs and it's gota that means a give and
take. It's compromise. Um it's it's the art of influence, but it really is sometimes sometimes then it means as you're partnering together if it's an individual that's causing the problem and not the business, it's a matter of using the information that you have to show that's what the issue is and then again mitigate that risk in the way that you can. That often turns into a self-solving problem. Uh we got we got two questions so bear with me. Uh, Christina, if you take this lady, I'm gonna go to this gentleman. His hand up first, so I'll go over here. Yeah, I was just going to say in that scenario, I usually try to make it their idea, the
thing I'm trying to push. So, the influential thing, like work with them and make them have the idea, become a partner, but if you kind of feed it to them slowly, they they bring it up and then they are a champion for the thing you're trying to do. Great. Well, um I don't really have a question. It's more like a closing remark, which kind of fits because we only really have four minutes. But first of all, I just wanted to I love that. Look at the energy being brought by this lady. So, I just kind of wanted to first of all thank all of you because we've got like 10 wonderful minds up here as
well as all the wonderful minds back here. Um, so we're getting a little bit of insight of really how much of the business aspect you need, but also like the technical mindset too. Um, so from what I'm hearing, a large part of this is communication, but whenever you're dealing with prior to or during or after an incident, you really have to understand where uh what everyone's end goal is, right? So like the stakeholders, they of course want to keep their money, but you also want to make sure that your customers are happy, right? Because there's no customers if like you don't have a good reputation with things like that, right? Um, and I guess also going to teaching what
security is because if you Oh my god, I have seen people who don't know how to use a computer and I'm like they've been along they've been computers for long enough time where you should know how to control C controlV at this point but you know to each their own right control Ver what could be wrong right so there are a lot of people who still don't know the age of technology we're in. And especially with AI, things are changing even faster than sometimes we can even comprehend because like five years ago things were like, okay, things are changing maybe every year, but now things are way different than they were last week, right? Um so for us to kind
of or for you to kind of teach people what we're up against is a very big um barrier. So, I know that all of you guys have a very big job um ahead of you. Um and also putting things in terms with they would understand. So, instead of saying, "Hey, we've got we've got a breach," kind of say, "Hey, you left your phone in your back pocket and then you went to walk out on Bush Boulevard in the middle of the night, you will definitely get your phone stolen, right?" Um or like in Italy, right? Like you always got to keep that thing locked and loaded. Um maybe not in Italy, but you know, But um and also relationships and
influence. So you kind of have to be like an allstar where you have to kind of understand where people are coming from but also still being able to get your point across. So I just wanted to kind of wrap this up and say that you guys are just like amazing with all all the different alleyways that you have to deal with. Um and yeah, so applaud to you guys. So can I can I just can I just ask what's your name? I'm Kelsey. Kelsey. Kelsey is going to be moderating the next CISO panel here at Bside. Give it up for Kelsey, everybody. Come on. I just wanted to add that Kelsey, I have been doing the CISO panel, it's either
my fourth or fifth year because I started with you, right? So, fourth year. Uh, and Kelsey, I think you've been here all four three years. Three years. And and I could so it's awesome like when you see someone's growth, right? Because Kelsey's first year she was going, I don't know about this security thing. and and Yeah. Yeah. Yeah. Okay. One minute to go. Sorry. Okay. So, my whole Aren't you just shutting us down? It's my time now. Okay. Okay. So, I actually started um coming to see you guys at Bides uh like three years ago, right? So, this is my third year. My name is Kelsey Klesiastri. I graduated here from USF uh at in cyber security.
So basically three years ago or two years ago now I came um to listen to you guys and I basically had a question because I had I was going through an interview process where I felt as a I'll say it black woman I was being told by the by a person on the interview committee that they did not see me as an engineer. So basically I had asked a question to the panel and saying am I correct in what I'm hearing? Like is this a lack of my experience or is this something that they're saying because uh a lack of EQ on their side and flirt. Anyway, um so that's sort of how this all started. And then last year
I guess we kind of met up again. And at this time last year I had just quit my job. Didn't know what I was going to do next. I actually I actually took a sabbatical for like four months traveling around the world. Um went to like 15 countries and actually I had quit my job without even knowing if I was going to get hired anywhere ever again. Um but literally a week before I left a company was like hey we'll hire you and you can also work wherever except





