Cyber Risk Management for Florida's Critical Infrastructure by Dan Holland of Arete Solutions

Show transcript [en]
sorry well in addition to the uh the intro there I wanted to expand on my uh my background and how I ended up in the GRC realm you know starting on the Coast Guard we did risk assessments and and debriefs after every evolution so it was a very natural transition for me to uh as I got into the the challenging and dynamic space of cyber security to continue to hone my focus until I I found this this world of risk management just recently completed uh an engagement that went really well with a uh a healthcare organization here locally and I was fortunate to surround myself with just the the best of the best some really incredible people that you know
operationalize what we're going to talk about today so you know when I came across uh you know the 800 series doing some casual reading like we all do right as as practitioners uh you know the the 839 really was a Eureka moment for me because I recognized those four components and my goal here today is to simplify uh what can be considered a very complex uh function right it's really a family of processes that we'll be discussing uh Bruce schneier gets uh uh credit for the the quote here you know complexity is the enemy of security you know I also like expert dystra's uh Simplicity is a prerequisite for reliability one of those fundamental uh first principles
that I I hold dear so again we'll we'll talk about some terminology uh we'll we'll get into the the four components of the 839 and some things that I've learned along the way about how to operationalize uh those components and then uh for those that are in the critical infrastructure space I got a few slides talking about the Statewide risk assessment that I'm supporting right now and why I think that's important to uh villain but just so I can get away the land you know pretty pretty small group here so uh who's who's student who's a student right now just here to uh to learn and and chat okay who's a practitioner okay and uh working in critical
infrastructure those 16 sectors okay appreciate you for being here any uh any military DOD bye we want to make sure I'm I'm tuning the uh my comments here to the uh the maternity of the room uh we'll start again with that basic terminology just so we're all on the same page in order to have a risk have to have both a viable and active threat capable threat actor and an exploitable vulnerability so [Music] in the presence of a threat doesn't mean that we necessarily have a risk we need to have both in order for there to be able the uh cbes that are out there the national vulnerability database has some 200 000 vulnerabilities listed just last
year or 25 000 were added that works out to almost 70 a day but less than 10 of those are actually exploitable the exact number is uh uh I'm not going to quote anything that I've seen I don't know that we you know it's a changing number but it's a very small percentage these vulnerabilities even critical vulnerabilities these uh vulnerability standards are lighting are even exploitable so again I'm exploitable this does not exist and this is important as we talk about risk management because we don't do security because it's it's fun and Business Leaders like to invest in security we do it there are risks that the organization has found unacceptable that it has to be
addressed uh so determining the likelihood and uh and impact of those those risks is something that we'll talk about a little later as we talk about assessments and and how to respond to them but uh why we do risk management just like we talked about why we do cyber security is to manage risks why we do risk management is because our resources are limited if we had unlimited resources unlimited expertise unlimited budget we would just do security so we can take it to the nth degree and there will be no business Interruption and everything would be motivated and working perfectly well right um is the people working on this that had all the training and versus they
need but that's not the reality for anybody organizations are operating in very highly complex and interconnected environments in these same programs changing so leaders have to recognize they have to make explicit well-informed and risk risk-based decisions in order to balance the benefits gained from the operation that they're considering with the risks that one of those vulnerabilities will be exploited to causing harm to the assets or people or operations that they are trying to move forward on so that Balancing Act for decision makers is constantly what they're weighing and it has to be exploded it has to be understood a good decision so those key questions that we're going to talk about here and why I think the
the 839 of those four components is such a great model how much risk is it you know where is that line between acceptable and unacceptable the return what response is reasonable right response has to be reasonable but what does that mean it's unreasonable then it's considered negligent the no leader wants to be found negligent for not doing what would later be considered reasonable so we'll talk a little bit about what that means that key challenge that I want to talk about highlight is how we measure and communicate risk to those leaders who's responsible for doing this the answer is everybody all levels of the organization uh nist uh prescribes a three-level approach which which I found
very useful at the organizational level the Strategic leaders uh making those long-term decisions uh at the second level you've got the mission and business process level those division heads and the department heads and managers of the organization and then finally at the system level at the bottom of the pyramid you've got your Hands-On folks doing the administration and management of those different systems applications uh that the business relies on and again this is a multi multi-faceted family of processes that require the involvement of the entire organization uh and what the the nist describes here in their Flagship publication they call it 839 for managing information security risk this was the Eureka moment for me coming from the military I recognized
the oodle Loop in it is anybody familiar with uh with Boyd's oodle loop from the Air Force all right observe Orient decide at when you're in the in the cockpit of a fighter plane uh in a dog fight you are constantly observing orienting deciding and acting and that's something that they they coined in the Air Force to respond to a very Dynamic situation like a dog fight and it structured their thinking and their approach in the cockpits that they can make good decisions and react to new information as it came in so I I see this starting with the framing which we'll talk about of course the assessment the response and the monitoring of that risk that's our oodle
Loop in cyber security right that's the the family of processes that we apply in a structured and rigorous rigorous way in order to make consistent decisions about out how to treat our risk across the organization so pause here really want to steer this image into your brains I I love this picture uh and and again it's it's straight from that Flagship publication so this is not according to Dan Holland this is according to uh to this uh special pump for managing information security risks so uh we'll break this down here in the coming slides now the first component the risk framing this is uh this is the key part that so many organizations skip as they start an
assessment they don't put that foundation in place which defines those guard rails that the organization is supposed to operate within we call this the rest of frame and it produces a risk management strategy that has and addresses some very uh critical things that define the terminology and uh and includes the expression of security and privacy risk tolerance which we'll talk about a little bit more the risk mitigation strategies how the risk is going to be uh address room mitigation standpoint the risk assessment methodologies and what the criteria are to define those terms what is a critical mean what does the high mean how are we going to treat this um and on ultimately how the uh the
approaches to monitoring risk over time are going to be addressed so this risk management strategy lays the foundation for and addresses governance and compliance right our assumptions our constraints it's a it's a comprehensive document but it is foundational to doing governance risk management compliance to making informed decisions about how we treat cyber risk I like to use a a car analogy here and I apologize you've probably heard more than one car analogy today but I can't help myself the risk appetite and risk tolerance are such key terms to understand and to Define clearly and there's a lot of organizations that have uh either used uh broad or or unspecific language or not even bothered to try to
document this at all because their their leadership doesn't want to sign the the dotted line saying this is what is acceptable to me this is what is unacceptable to me because it hasn't been communicated to them in in terms that they understand so if we're cruising down the road and it's a 70 mile an hour Zone on the freeway here like most of the the Florida freeways are the 70 mile an hour limit is there for a reason it is what the government has deemed reasonable for uh driving on that road right however I think all of us have driven on a freeway before in 70 miles an hour is not uh the typical flow
of traffic especially in that left lane right so there's some room between that understood an explicit line uh uh speed that is tolerable for the Orcs or the appetite of the government with the tolerance of those police officers who are going to make a decision about whether or not to point they're going to pull you over for going 80 85 90 right circumstantial right because in the rain that police officer might pull you over for going 75 if you're driving recklessly and they see some things that they don't like they've got that ability to respond to information and to change their risk tolerance based on the circumstance however sunny day little traffic 10 15 miles an hour with the
speed limit I've not seen too many people get pulled over in those circumstances so clearly the risk tolerance uh is up to the individual discretion of that officer and our mission here is to codify that and communicate it across the organization so that folks understand where that line of risk tolerance is because beyond that point is unacceptable to my leaders therefore we have to do something about it right we can't uh accept unacceptable risk from reported directors and and taking that off off the plate off the table is really that first key step to being able to effectively respond and manage these risks so the key questions I think to determine the risk tolerance is compliance viewed as the goal or the
bare minimum standard because compliance could be where you draw all your risk tolerance line and say anything you want anything that is non-compliant is unacceptable to us or certain critical systems uh you know I don't think that compliance is optional but we sure treat it that way in this space right in the government which certainly you know our Regulators would argue that compliance isn't optional but we exist in a world of risk waivers and exceptions of non-compliance and that's just a reality that we all face because business operations dictate that we need to perform certain things and if controls aren't in place then Soviet will have a plan to address them but maybe maybe not right it all depends on
the maturity organization that we're working for how might versus tolerance differ across different departments based on the mission the nature and classification of the data what are they trying to accomplish they can have a great it could be a very low risk tolerance circumstance around highly regulated information and systems OT networks you know if you're an electrical grade company Phi data if you're a healthcare organization you know you want to have a a stricter set of controls around those sensitive and critical systems that around non-critical systems because it's inefficient right but risk management gives us the structure to approach and address those issues so cannot overstate the importance of clearly determining and expressing risk tolerance and having
the senior leadership the organization document that so that the rest of the organization can respond accordingly knowing where the left and right boundaries are that we're operating Within so fundamental so important and missing at a large majority of organizations that I speak with you know examples of maybe ineffective and effective you know what does this mean what does this look like I can give some examples I think that vague terms like severe critical substantial uh don't do us any favors because we can say we're not going to accept uh risks that are deemed to have a potentially severe impact on our operations but if you find something different to everybody in this room right so again that risk management
strategy that we get in the framing should Define both terms but who often is missing so we need to talk about how we are going to better and respond to risk via the risk assessment which is that that second component that we're going to talk about next uh I'll save my thoughts on risk modification versus qualitative uh like I'm mentioning after we've got that Foundation that frame in place then we are conducting an assessment there are many forms and and to conduct a risk assessment right again there are penetration tests you know the ethical hacking there are vulnerability assessments those constant scanners that are piloting and searching for those known vulnerabilities there are qualitative assessments against certain
Frameworks the desire security framework is a very common one for our critical infrastructure the uh the quantitative assessments right where we translate this into business terms that the uh the the financial and non-technical audience are more comfortable responding to and making investment decisions against all these are our methods of assessment that are determined in the risk frame and that strategy and we're going to say this is how we're going to assess this is the frequency and then here we are conducting the assessment this is where we identify determined disseminate and update continuous monitoring right those threats uh vulnerabilities the impact and likelihood of these occurrences so they can conduct these risk assessments at all levels of the organization right
that pyramid back to it we conduct assessments at the organization level at the business process those system level assessments are key and often skipped over because people say oh we did an annual assessment set at the organization and we we surveyed across the department but really getting into that application specific assessment and helping Define controls for that use case is is key this has to be done at the different levels of the organization and communicating uh the risks of the chain and informing those uh investment decisions that they're trying to make we've all seen these these matrices right these these heat Maps uh the one through five so the red yellow greens um the risk uh equals probability times
impact is how we communicate through risk assessment uh the severity of the risk so you know some of these uh these images are are self-explanatory but uh everybody's familiar with this right we've all seen risk communicated and reported this way it makes us in cyber security kind of feel like this the when we're taking these uh these matrices to the uh the board and expecting them to be able to respond and understand what we're talking about it's not fair to them because the the key problem that we are uh trying to address is inherently complex and difficult to understand so I don't believe that this is sufficient well I think that we can do better and
it is on us as security practitioners to do better in how we communicate risks assessments are not an exact science right it can't be Douglas Hubbards is one of the fathers of risk modification of the author of how to measure anything in cyber security risk and he defined measurement as a reduction of uncertainty based on one or more observations right and if we can express that quantitatively it put translates it into a universal language what the a severe an expected risk in the top right corner means to or the analyst that is making that subjective assessment is going to be different than another analyst with a different set of experiences and backgrounds right so it's very hard to use these ordinal
values and communicate consistently because we have different analysts different perspectives different criteria you don't want to go full risk quantification uh you know there are other methods to to measure severity one that I've I've used and like is is dreads more uh damage reproducibility and a few others exploitability uh to identify you know you assign uh a zero to ten score for each of those five components and then you can say Okay a critical finding to our organization is a thread score of 40 to 50. and a high is 30 to 40. at least you've got some structure and some uh defensibility in how you assess that risk and rated the severity of it the art of the possible I'm showing this
because it is possible and we can model risk quantitatively and do some really interesting things like overlay any insurance limit to the impact class it's expected to pay to show what the uncovered risk would be for a certain scenario so again taking that that threat-based approach and modeling what the first and third party financially intangible risks would be what the possible Financial outcomes would be in expressing not on a law succeedance curve I think is the superior way to communicate to Executive leaders about the risks that they're facing because now they can calculate a return on risk mitigation so that's the key it's like return on investment if we have 200 000 of uncovered exposure because of ransomware
scenario based on these assumptions very transparently and the ciso is asking for ten thousand dollars to mitigate that risk and the residual risk that we modeled after this ten thousand dollar control is fifty thousand dollars and you can do that 150 000 of risk mitigation the ten thousand dollar investment math right a CFO understands that Boards of directors understand that it's on us to translate the severity of what we were up against and what we want to do about it and in terms that they can respond to so back to the risk framing I think that the superior way The Best of the Best in Class way to express risk tolerance is quantitatively for these systems that are critical to
our operation we are not going to tolerate risks that expose us to more than 10 million 100 million dollars of risk it's going to be very circumstantial as intended uh you know the one thing about this that often is brought up is had quantify loss of life right if uh we are now in critical infrastructure seeing real life scenarios where folks are um dying because of the result of cyber attacks awful uh these stories and uh up in Georgia and helped the hospital we're A life-saving system that a baby was hooked up to uh it was taken offline by an attack in in the child lost their life uh so we can't qualify that right
um what we can't quantify is is reputational damage and the impact uh what what uh downtime is forensics uh you know the impact of all of these uh individual components that add up to a certain uh model of risk so again I think that uh that Quant is is the future the way to go and it's incumbent upon us as practitioners to uh to do the extra analysis when we are conducting our assessments and communicating terms that they can reliably and consistently respond to that's their component right this is where we are left with Clarity we've got our risk frame we understand what the guard rails are we understand the risks and whether or not they are acceptable
to the organization and now I've got to make a decision the decision based on understanding and we're only left with four decision Pathways when faced with a risk we can accept it we can avoid it we can transfer it or we can mitigate it the mitigation is where we're doing cyber security right this is all cyber security but cyber security operations that first line of defense and my friends The Institute of internal Auditors three lines of Defense model GRC really exists in that second line of defense where we are helping the first line prioritize uh their actions and activities because resources are limited and you know those those different perspectives those different uh functions uh support each other very uh
seamlessly in a thoughtful way that third line of defense would be internal audit for that model so definitely recommend from an organizational structure standpoint thinking of it in those terms the final defense is where operations exist I.T and security that's where the work is being done to administer and apply these controls second line of defense is informing um the the risks in the prioritization of those so you know this is people that skip to this this part and and the vendors outside you know that make the tools would love for you just to skip to this part because they've got the answers to everything right uh you know their multi-factor authentication they're they're Sim their their EDR MDR
Services all of that is going to solve all your problems but we all know that that's not the case because it depends which threat we're talking about you know what's more important authentication or logging you know is a question I like to pose to folks and they say well you know they got opinions about one or the other but the truth is it depends you know if we're talking about an Insider threat scenario the authentication controls aren't doing much for us uh because the presuming those folks have access uh in in the authorization to get to the sensitive data that they are a threat to uh so in that case the logging control would clearly be the the one to prioritize
that will have numbers mitigation so um again a consistent organization-wide response according to the risk frame is what we're driving from here and the fourth and final component is that continuous monitoring so there's you know for all four of these components there are 800 series Publications that I I recommend to uh you get into uh you know risk assessments 830 or 800 154 for data Centric threat modeling here it's uh you know for continuous monitoring it's it's 800 137 and this describes a six-step process that um really maps to the the four components that we're talking about but this is at the system level where we're continuously moving through space and time as circumstances change uh you know
trip wires that require additional assessment either time based or event-based uh if a new leader comes in to the organization it doesn't just have to be a technical uh change in configuration but say a new leader comes into the organization that has a different risk tolerance than their predecessor well now we need to go in and conduct uh additional assessment to make sure that we are still within the bounds of what is considered acceptable according to our risk frame so that's the uh the adaptability here in in the continuous nature of what we mean when we say continuous monitoring uh you know that term is going to mean different things to different systems and different organizations but the the
frequency is sufficient to support the risk-based decisions that the organization is trying to make so taking a step back saying okay what is appropriate here at what frequency do we need to do this at what frequency is reasonable why do we need to treat this in an ongoing manner what are those bounds that's what we're aiming for here again with the broad-based uh approach to risk management and based on these very simple four steps that each are a family of processes unto themselves and done by dedicated uh and you know committed experts to these functions third party risk fourth party risk uh you know is also a key part of this we're not just talking about the systems
that we have in production the open systems theory of organizations is what I prescribe to we are uh permeable right and information and systems are interconnected not just within our walls which are virtual now and and varying degrees but also reliant on those third-party and fourth party systems this all kind of comes back to GitHub right in the open source community in a lot of ways uh so you know this is again not an exact science but a function that is absolutely critical of organizations to commit substantial resources to uh performing in that ongoing basis so the key takeaways before I get to the uh the Cyber Florida slides and ask about that assessment is
we need dedicated experts to do this and to do it continuously at that frequency that's been determined uh because our resources are limited and they have to be prioritized we can't just go with our gut on this stuff as smart as uh many of us are as the organization scales and matures the leaders need that decision-making framework and process to do it consistently over time governance and compliance framing that that first component that is so key it reflects our mission those internal and external requirements regulatory statutory contractual but also the culture you know different leader this is a human problem this is not something that we can just look to the 800 series and copy paste and uh copy paste between
different organizations because it reflects the the human element uh the culture and the tolerance of those leaders in their pursuit of digital Innovation and transforming the way they do business weighing those things against the risks that they introduce because every one of them expands our attack surface and makes us more vulnerable but we continue to do it right so it must be worth it right I mean we're doing it so uh we've got to understand what is reasonable what's required of us and respondent Court uh that you know really covers that third piece about the boards and the leaders determining and clearly expressing that risk tolerance and then finally how we measure and communicate risk has to be consistent across the
analyst team that's doing the assessments they have to have that structure and it has to be communicated in the language of the risk owner because the CSO doesn't own risk at these organizations they can't their risk advisor now that's the role of the CSO CSO is in the room I mean am I am I wrong you don't own risk do you uh it's it's something that that requires a culture shift in education because they look to the CSO to own the risk they want to see so to own the risk again liability and accountability and whatnot but that's just not the job uh so it requires uh in order to get them to assume that responsibility and to
make informed decisions we have to take it upon ourselves to communicate in terms that they understand moving on for the critical infrastructure State of Florida is conducting a Statewide risk assessment on the governor's border to gain an understanding of where the what the risk profile is for the different sectors of critical infrastructure across the state it's the first time this is being done uh and it is incumbent upon all of us you know to participate so I'd love to share just a little bit of information about this if you are unclear if you are operating in critical infrastructure here are the 16 sectors according to uh what what sizza and uh sisa um you know what they put out and uh and
based on White House guidance so the State of Florida legislature uh has has hired cyber Florida to conduct this assessment and they've got until June 30th to complete the world war working with uh miter uh fdme Emergency Management the Idaho National Labs regional consultants like myself uh to engage with the the critical infrastructure folks and put their minds at ease about uh the the confidentiality security of their responses and what this is going to be for the State of Florida just uh yesterday closed the grant period for 30 million dollars uh to respond to risks so references back to the 839 did they do that in the right order you know right in the middle of an
assessment period we're going to release and close the grants period to respond to it right uh we'll get it right next year though um it's uh it's you know a work in progress but um cyber Florida if you're not familiar is hosted right here at USF it's a tremendous uh non-profit organization led by General Frank McKenzie who just retired a four-star running centcom um marine and he's running the show uh and they're they're moving on a lot but uh so a lot of fun being flown from Tallahassee into cyber Florida to perform a variety of functions for local governments critical infrastructure and other stakeholders I work very closely with them in my non-profit realm on the
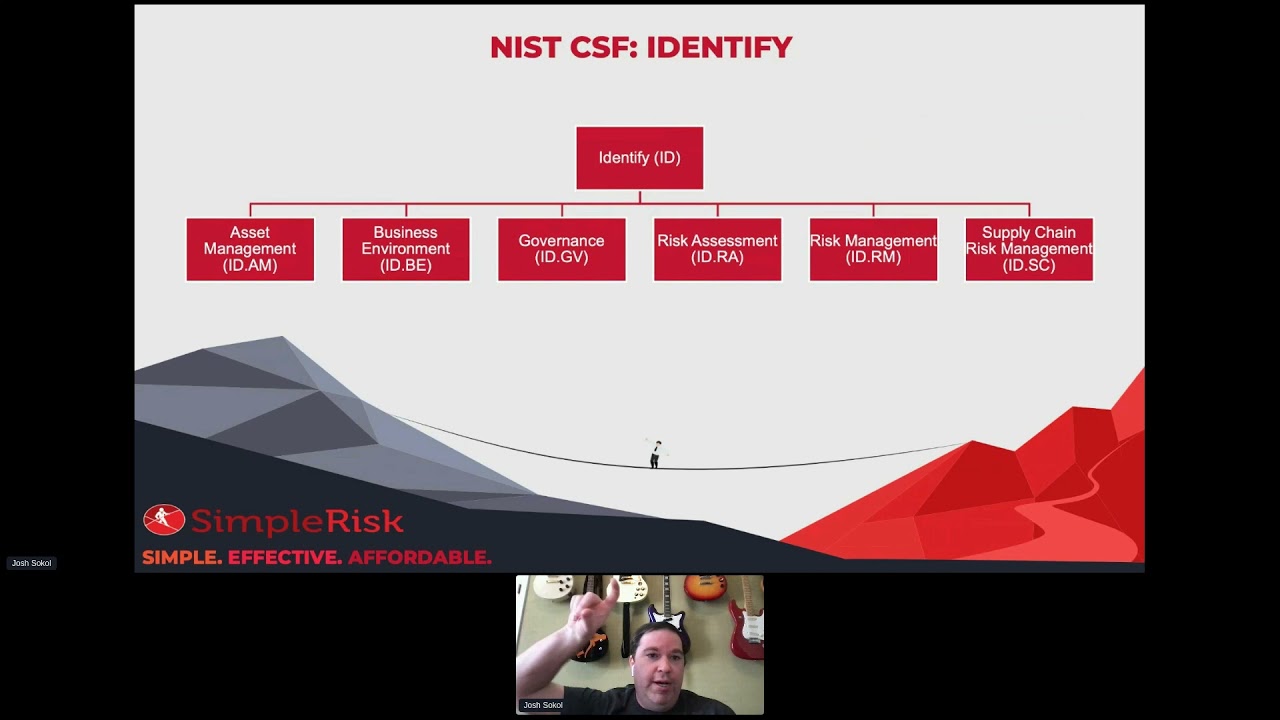
K-12 front we're hosting 400 students next week and on the 12th and the White House is coming down for it so a lot of momentum a lot of uh productivity in this K-12 space in the workbook and uh and and continuing education Workforce Development so cyber floor isn't doing uh tremendous work and this assessment is so the cyber security framework is the uh the framework of choice uh it has been paired with the ransomware Readiness assessment uh bringing the total number of questions to about 150 for this assessment but it is a self-assessment and they decided not to use a maturity model for this first year so it's just yes no or n a it is uh not
a super heavy lift um especially if you already have that Baseline uh to perform but it is a a valuable set of reporting that you get at the end out of that free cset tool which this is cyber Florida's instance of the cset tool the cset tool is what cisa uses when they come out and conduct assessments usually for local government agencies but it's a uh a familiar tool for folks that work in that state and local government space and one that is uh securely um supported here by USF uh and and their their I.T team as where your responses will be housed and I can share more information about that uh if you're interested in learning about the uh the
the confidentiality and and purposes of this but the call to action for it is to complete the assessment right to uh to get the legal support uh to get this into your workflows and uh please address it um because the governor and the legislature are investing uh quite a bit in cyber security and we need to keep them informed they need to understand what your operational realities are in critical infrastructure so this is our Avenue to communicate so that they can establish that risk frame uh you know respond to their risks and continue to monitor them on uh on an ongoing basis so this is the the state's attempt to put that Loop into practice
uh across the uh the sectors that we all rely on as as Floridians you know if the grid goes down if our hospitals are offline then taxes very deeply and very personally so with that I'd love to open it up to any questions or comments and we can talk about the foreign the 839 we can talk about the Cyber Florida risk assessment or whatever else is on your mind space between this and why are we extraordinary we pick seven states okay so on the assessment why is the state uh doing this at the state level there are National level uh assessments yeah so the the MSI staff that holds up into the center for Internet Security
CIS uh has been for 16 years conducting a nationwide assessment of those local government agencies which they route to the Senate Appropriations Committee which unlocks the federal funding this is the state's level to or attempt to essentially duplicate that effort that program at the state level so state level funding for the state level assessment Federal level funding for the national assessment the code for USF we're supporting this effort um this is the first thing of its effort in the state Florida is trying to be a leader for the other states to follow and so that's why they're doing it here there there isn't there doesn't seem to be this kind of effort that we know
Department of USF if we were to sell cset assessment would we send it to I think if you do their cset assessment it goes to um cyber Florida because they have a specific set of questions that are much easier the cset itself is very comprehensive I'm sorry I don't mean to take over your talk I'm starting to get a little hoarse so he said itself is expensive and has a lot of different um uh Frameworks to choose from and questions that's way more than 150 questions so this is very specific for this effort you or someone inside before and be the contact for for office the department to connect I think it's cyber floor and
that's that's uh they retained me to uh to support this so I I'll give you my card and be happy to answer any questions yeah
uh risk mitigation strategies such as you know there's like culture paradigms record like shift left right that's something that's been kind of tossed around where you're moving risk management responsibilities out from csos and leaders to maybe more practical you know business owners and directors BPS such and such is there any efforts kind of within your experience whether it's within the Cyber Florida or just in general for other clients to where you're finding a another change in the culture Dynamic of how you execute or how you're communicating risk at a maybe a middle tier as opposed to you know board level and sea level Executives is are you finding like more adoption strategies with that absolutely the
beautiful thing about this is it applies to any step of the software development life cycle as well as the it events with with Enterprise architecture and it informs uh how how those systems are are modularized and built together what's that operate model look like so absolutely the the further left we push this the deeper we embed our partnership with those other apartments and engage in operations the better we can communicate things into their terminology right across different departments so but at large you are seeing kind of more of a gravitational pull towards that absolutely yeah the csos have been maturing um they they know their stuff now and they're Business Leaders first uh technology leader second saying that that ship more
and more so um describing Trends here but also you know that that Bedrock uh approach that that we both continuous monitoring is uh something that I'm saying adopted uh quite frequently but or the immature organizations that are just starting out that have a three-person shop I talked to a fair number of those as well you know okay I know I don't need to conduct an assessment I know I need firewalls good virals you know I'm not saying do this uh you know put this structure in place if you are not there yet because at the end of the day policies don't actually mitigate risk right they have to be implemented you have to have somebody responsible for implementing
them if you're just trying to keep your head above water deploy that that you know that that antivirus tool on your uh endpoints higher higher mssp to monitor your network those core fundamentally and multi-factor authentication there's a bunch of core controls that are Universal and you don't need to think too hard about but uh when it gets beyond that points then this this structure I think is the right order and that's just my opinion I think you know invested you know resources are limited invest in those things that you know or common sense that you have to do uh to bring the risk down to reason what you think is reasonable and this will help tune it and what's that go
forward look like as the organization scales it starts adopting an Enterprise mentality thank you what kind of shifts are you seeing as more companies adopt loud in the whole governance role sure again specifist lawyers um seeing a lot more lawyer fees right uh reviewing the contracts specificity in the contractual language about the the shared responsibility is is key right those those contracts have to be explicit and it has to be within the risk frame of the organization so um you know in Cloud's tough um there's a lot of automation that we can do though uh from a GRC standpoint with Cloud systems automating that evidence of collection piece you know Integrations with GRC platforms into these uh these Cloud systems allows
us to get that real-time visibility because these Cloud you know providers will um patch systems and and change configurations that work compliant and we're secure and now we went back to a default configuration and well now what was you know compliant and secure in our risk frame of Tolerance yesterday is now not through no action that we took directly so in having that real-time visibility those Integrations is key as organizations mature uh to get that automated uh functionality but also that real-time visibility into those those changes part of your assessment what what what's the maturity level of operations being able to have effective governance model it's all over the place and I think that that National cyber security strategy
was more political posturing than than uh specificity but their implementation uh strategies coming out here shortly um I I expect that and I hope that we reduce the bureaucracy uh that's responsible for regulating critical infrastructure but I'm not holding my breath on that I expect uh that we will continue to uh leaders will continue to do what is mandated of them and not a thing more but as those SEC changes come into effect Boards of directors are required to have cyber expertise I think that this is trending in the right direction it's just taking longer than we would like because we understand uh back to that nuclear bomb picture you know with the aliens what the risks are
uh we understand that again on us to translate it but the the requirements uh to to put the structure in place are present in and growing do you have any feel or there's a the Florida legislature passed into law and a requirement for local government organizations within Florida to align with a cyber security framework are you seeing actual problems toward that it needs assessments defense
assessment this is our basis you know we will progress against this at the local government level but uh the MSI Sac has 16 years of of data that they've been compiling they do use a maturity model and their report is very helpful to see those Trends across all state and uh geography generally though there's been a lot of great money flowing to those local government organizations uh states are and the federal government are rolling out direct Operational Support they're saying hey an IRS to be your sock onto your network it's a little big brother for my taste but it's an option um so there are more and more of those services that are available to our our
critical infrastructure especially those sltt State local Territorial and tribal uh organizations did both the time any other questions really appreciate the dialogue thank you for your time thank you foreign