Preventing digitally sourced patient harm: managing cyber risk throughout digitally-enabled medical devices' life cycle
Show transcript [en]
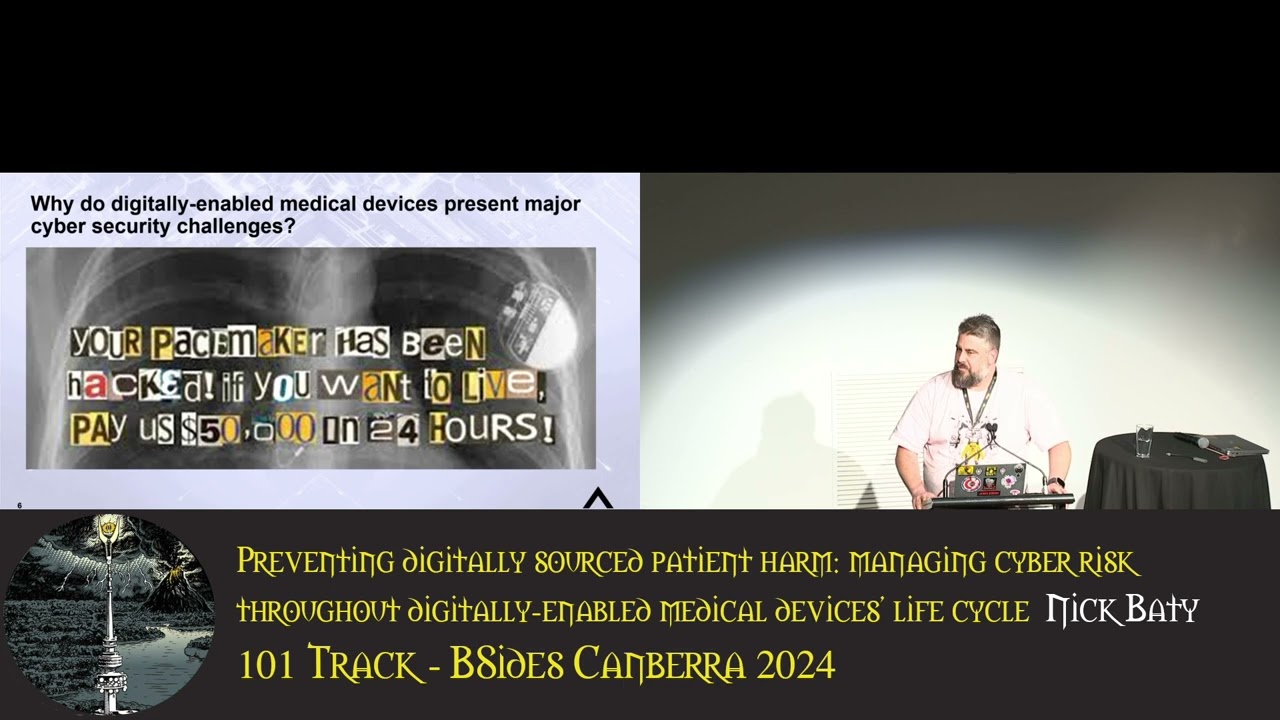
we have Nick baky uh and he is talking about preventing digitally Source patient harm managing cyber risks through digitally enabled medical devices life cycle super important topic really excited to hear it [Music] [Applause] thank thanks very much for having me um as you can tell by my accent I from the other other Island um but I was um in a moment of weakness I was invited to come across and have a talk um so that's why I'm here um so I'm talking about digitally Source patient harm or is I often like to call out how your wearable will kill you um so little about me I um I live in dened so anyone been in New
Zealand know where denan is it's basically we fight off penguins and polar be on a daily basis no not really but um I'm lucky enough to live there I work there full-time remotely for Bastion who are based in Wellington and Orland um foolishly they basically decided right we going to keep them the South isand cuz he's just no good any else um but this is the reason I've done this talk is because it's kind of made up of my hair pulling cringey moments cuz I had a lovely long flowing beard and lots of long hair when I started working for the Ministry of Health and after 2 years I am the shattered husk of a man
that you see before you um not least a which because I was going around hospitals and GP clinics and um looking at all the machines that go ping and going there's some problems here with how people do things and as I talk to more and more people where they be clinical engineers or it professionals or Hospital administrators I said you've got some challenges with this technology there and they're like why I said because if it's not managed it could will kill your patients o that's not good so um but the problem is it's not well understood and it has the greatest propensity generally speaking to cause significant harm so there's big old question marks and I
guess that's what I'm here to talk about today and a bit of a call to action so a little bit about me um I was the chief cyber security adviser at the Ministry of Health in New Zealand for a couple of years and my official title and responsibility was Raising New Zealand's cyber security maturity in the public and private Health sectors and I was the only one that did it so once I got to lunchtime and I'd done that job I found something else to do with my time and then um I decided that my wife is denan girl I will move down to denen and G work for um for a managed service provider so I joined the Dark Side of
The Fast and became a principal security consultant and fooled them and then prior to that I work for the agency that shall not be acknowledged otherwise known as the ASD equivalent in New Zealand so um yeah we do do that sort of stuff too but my claim to fame and your respect you got any campar here I do my Master's Degree at a&u so I have a very soft spot for the city in that particular University so um it's great I was here for the fires which wasn't fun but you know that was a thousand years ago so what we're going to cover off today um what what is a device and it's not necessarily what you think it is
what are the threat actors and motivators what are the challenges associated with medical devices today what's the current posture of medical devices in generally um what's are the recent compromises you can't have a cyber security presentation unless you have some good War Stories um what's a life cycle based approach implementation and adoption and mix steps I should acknowledge um but ahead of time I had to have some therapy prior to this cuz the TJ and Australia does it very well and everything part of my national being having to acknowledge that in a public forum here was really painful so I'm actually having to work on that but um certainly the TGA and working with acsc
um have put together some really good guidance and for both um the industry and also for consumers around how to take a sensible approach towards managing uh medical device security and it was basically on that basis that a lot of the things we see here today so let's have a pted history so in New Zealand bless us the medical device um uh definition is based on legislation dated 1981 so when Adam and I was a boy and basically it's related to the definition of a medical device in that context is any device instrument apparatus intended to be used on or for human beings for a therapeutic purpose so really specific definition really specific in Australia
you guys are considerably better because you've actually got a really clear definition both in terms of things like surgical mesh but also electronic Technologies both in terms of implantables and other Associated Technologies to terms of delivering therapeutic care but what's also really great is you have what you have 15 essential principles as part of it um I love the principles you guys do it's kind of like the warrant of Fitness rules the road if you don't follow this you're going to die um so essentially a good at least half those principles is based on what they call Quality and insurance so it gave very clear legislatively B guidelines for how device manufacturers and device operators need to manage and operate and
oversee and govern this technology so huge difference which is why I was like Mega in love with the TGA guidelines like how can we you know push it across the ditch um but as we kind of see some of the guidelines and things excuse me of things we're seeing in terms of what is a device aren't necessarily what you see so wearables like this they're known as medical devices CU they have they particularly some of the algorithms and programs um they have what's they're now classified as what's called software as a medical device so algorithms and for the clinical diagnosis of things like apple Health Google Health other applications associated with performing diagnostic functions clinicians are
making clinical clear decisions based on that information so so don't bother fudging your running scores when you're out for a run cuz the doctors will give you the wrong medicine so just bear that in mind um and then you've got things through like um infusion pumps operating theater stuff um you start nanot Technologies all sorts of implantables so it's not just the Pacemakers it's almost anything that has a therapeutic um process so it's almost it's almost the sky a limit and the digital Health industry in New Zealand Australia is evolving so quickly so you know recently was the evolution of public cloud and the role of um web based and cloud-based hosted applications now we're seeing AI
being actively used and diagnostic decision making and what the implications are for that so basically I'm like Johnny Five and Scot going to be in my doctor next so we're stuffed so was working out what we do next oversight New Zealand Australia as I say bless us um we have got um there's an organization a government agency New Zealand called pharmac who are essentially responsible for procuring medicines and medical devices in New Zealand um and they responsible essentially for setting out the terms and contractual conditions um I may have had some robust conversations with them in a past life where I explained what the GD care was around this particular issue and they didn't align with My
Views I'm not sure why um but essentially their view was we buy medicines and we are a procurement agency but I say well if you have the ability to influence commercial outcomes therefore you should be putting Assurance standards into those contracts and actually compelling those vendors to apply a duty of Care at the beginning and they went no that's not our job and I said why never got a decent answer what you do have in Australia though which is great um you've got the the goods Authority and they govern actively and closely both what what industry can bring into Australia but also in terms of How It's deployed and what the throughly support looks like so again
woo for the West Island which is awesome and in New Zealand we've got the one database which is a fairly old website that says it's all volunteer based and when I was working with the medical device team in the Ministry of Health I'm like cyber scurity what are you going to do about it I said and and they were fantastic what they did but it was kind of like cyber SP with an S right said yeah yeah so we're going to work on that basis but you know what is it the thing what are the things that um you know keep you up at night and causing problems so ironically although medical device is not OT and it's not it and
it's going to smash together um it's actually a lot of the the the threats and exploitations are very much the sort of things we normally see as a matter of course in other domain so remote access exploitation why because they can but the thing is is these devices are not designed with security in mind and it's not that they're making a deliberate decision to avoid security and many cases it just doesn't occur to them historically they're getting a much better now but certainly in the recent time in the recent past it wasn't a course of action they normally proceed CU putting encryption in place slows down the time for product to go into Market putting additional layers in
there can create a really bad user experience for doctors or for um out health professionals or for healthcare consumers so if there was anything that was impact on the functional outcomes and the user experience was bad and sometimes um when you s these things you look at these things they're like well what's the likelihood of that happening and of course me being a GC specialist by the way GC specialist at hacker con yay um it's actually a case of these guys here are kind of going well what's lik that happening I'm going to likelihood risk let's do the sums on that one so maybe likelihood is low but the impact's going to be pretty catastrophic in some
cases um so you know remote access exploitation wireless access compromise so anytime you see someone walk around the hospital with a mobile phone their hand you're like what are they going to do to me um outd of software and firmware I think I've told some my colleagues the story but I've been into hospitals in New Zealand where there was a brand new MRI machine that had hardcoded credentials of admin and password at SS w0rd and operating the system anyone want to guess how old it might be XP thank you XP so it's brand new and it's broken yeah good capital investment that and then they've going to segregate it and they're going to manage it and then
it's like I don't have time for this cuz invariably Healthcare High teams are massively overworked I know they'll be the same here and they don't have necessarily the technology and capabilities cuz they're like it's a network device it's like and then often they can only be upgraded um through someone flying from here um with a removal meteor and going if I plug this in here I'll up data I'm going not on your life but then that than the is the only option because of course the vendors control the ecosystem so it's like that brings a whole new determination to supply chain risk I tell you that for nothing um and then you compromise host Network so you'd see
medical devices being compromised which would mean they jump from that other parts of your network because of course every single network is never flat and is entirely segregated all the time I'm right yes I am um compromise host Network so it's like the thing that's going to keep you alive is going to kill everything else there's something fraud in that I'm sure there is weak access controls sometimes to no access controls hardcoded creds no authentication cuz why cuz it's expensive and it's difficult um terms of um why it happens financial and political game there were um you know I saw you know media at the time who remembers prob might in the health sector Fields remember the sing
Health breach maybe five or six years ago huge part of the Singaporean health system was breached massive amounts of Pi was gone they determined one of the key targets that was the singor and prime minister's Health details so let's take a sledgehammer to the tiniest warn up possible but that's what the motivation is um gener disruption yeah ever tried to work within a hospital it time I'd like to do some critical patching the cve is nine find a good time to take a hospital offline it's not going to happen that's why cookies donuts and lots of beer are really good between your security team and your it guys and the chief medical officer unless you have that
conversation you're not going anywhere inal property theft why would they want to steal my stuff because they can um reputational damage m it's not name many names but you think of a few medical device providers and and developers over the years that have had major sort epic failures it's like yeah do I want to buy that stuff sometimes you don't have a choice but you know it's high stakes you know there's a lot of money in this sort of stuff to harm individuals increase personal credibility because you know you want to have the Swagger cuz you were awesome so it's kind of the way it is so why do they present major security challenges well for those of you are
devs in this audience prepare to cringe so things like Legacy operating systems software incompatibility between systems leads vulnerabilities such as misconfiguration and security holes you know most of the patent and software libraries are open source so it's hey Keys the kingdom thank you because end of the day we want to share and grow and develop and all that sort of stuff um lack of you know software updates medical devices themselves as I said don't have basic security in place it's like you know teus what 0.1 you know not quite like that but it can be feel a bit like that at times and um many times the challenges are also on the basis that you know things one of these Solutions
are web hosted so it's like you've got a web application on these devices here did you pinest it why would I want to do that okay and when you get a pin test oh I'll get to those findings when I get to them so why don't you pay in the first place that's an entirely different philosophical discussion but yeah and as I said they can be used to attack other sections the health sector's organizational Network um sorry I've got a note to you cuz you know I'm I'm I'm a man I can only process one thing at a time so just manage that as they go potential harm to patients and users from adverse medical device um security
events so those of you who have been in hospitals you might generally when um nurses and doctors mainly the nurses are dispensing meds on the ward they'll have what's called a px machine looks like a little filing cabinet with a computer face in there so what they do is when they scan your barcode on your arm to get these get the drugs to make sure you are getting the right drugs you should be getting um they'll then replicate that in the PX machine and it pops a little drawer out and says hey this is the drugs for neck but then these machines themselves can be compromised so I'm going well if I can compromise the patient information and sees that he
needs this particular drug and not that sort of particular drug and it causes issues with there you know this is where the high levels in health sector becomes to do with integrity and availability it's kind of like well because the nursing staff wouldn't know anything other they got absolute trust that this all going to work and then they'll get the drugs and then we find out why there's a problem and because that's the biggest challenge with these is because it looks and feels safe they assume it is and that's a reasonable assumption to make but it's someone who might have committed you know executed an ICU fitted with a bit of stuff or messed with the backend protocols all of a
sudden you've got some very serious potentially life-threatening life-ending consequences on your hands then of course there's you know the slightly less a boring issue of patient data being compromised and stolen in screets you know that's often when you're going going for the cloud-based applications the backhand and the clinician sitting somewhere on a beach in feiji going oh just P that stuff there and before you going that's not what he actually should she he or she actually did so it's kind of like the man in the middle attack on steroids and sometimes as well and one of the biggest challenges there's just a simple lack of awareness amongst different parts of the health sector of the
challenges these produce andless I look on a life cycle perspective um which is why I'm a big fan of that um they looking at discret parts and it's really difficult to work out how how it comes together CU you know my view cyers secur as a team sport no one sits on the bench everyone plays the full game coin it here no one else can take that phrase but that's very much the case of where it has to be so one of the juicy stuff what is actually going on in this space why is it so problematic so the challenge really here is that um we've got different classes of medical device there's a this is from a study I found
just before I came over um from 2003 2023 state of cyber security for medical devices and Healthcare Systems it was a joint report done by some re security research organizations in the States along with the um Health ISAC so we're finding that you know up to 82% of devices carry outd operating systems and bear in mind these operating systems aren't always necessarily that easy to um to um work with or adjust because of course remember what I said about the ecosystem the vendors set it up for them to work on it's not intended for the guys who actually operate the diverse is necessary to interact with them they're just supposed to make the buttons go
ping so the it guys who inherit this go yay lots of fun there as you say it's difficult to update them so the fact that you can't always do it over the air you actually got to do it manually with media is quite challenging and again you can't change um you know Bob's dog at password type thing for credentials you kind of stuffed with that but then if you look a little further we're looking at the types of classes of medical devices so when you're starting to get into um some of the class some of the um some of the class three ones like pacemakers heart valve you know heart valves are impliable devices or
anesthesia machines class two you know that that gets a bit binary excuse the profession gets pretty real in terms of actually this isn't the theoretical conversation anymore this is something that can really happen and um it can be pretty alarming and that's what I'm saying most people don't understand this sort of stuff can potentially happen and then when they look at they're going we should probably do something about that but it's very difficult to do something about that by yourself so I sort of put things in a slightly more contrast you're looking at things like implantable cardiovascular defibrillators or sercal theat type stuff so these are the products the number of products that were assessed on
that study and these are the number of vulnerabilities like medical monitoring Telemetry like blood pressure glucose monitors K machines 129 vulnerabilities out of 89 products so multiple products have got more than one vulnerability in there and some of the cve scores um you know 78 and that's of so um it's pretty gnarly stuff and then again type of stuff we're seeing in terms of the types of vulnerabilities we're seeing the import validations improper authentification um recall notices cuz I don't know if anyone knows about in the healthcare system to get a recall to actually execute properly there's a hugely detailed process there's be checks and balances there's quite a legal involvement in that sort of thing
there so it's not a trivial matter at all of course the companies have to do it you know they're concerned about market share and what it means them reputationally so not a trivial activity at all terms of uncontrolled resource consumption um any number of things so again these aren't academic issues and again which are the devices that are most um you know see most secure which means when you go to the hospital you never look the same way again so that's an infusion pump on the far left there that's the one that sits beside the bed and pumps the IV through the IV into your Canon then you've got ultrasound machines um for mums and bubs and the
like but not always but generally patient monitors medical dispensers that's the machine I was talking about before um gate internet gateways IP cameras although why you have cameras inside the W is an entirely separate conversation I'm quite that we not yet um Pax machines and computerized so the Pax machines and the dcom workstations what they are is the pack server is when you go to to get a c CT machine CT image or an MRI image all those um those high resol and images which ultimately you know create after to pyes of space they're stored on pack serice sometimes on Prim sometimes in the cloud um and then you've got the dcom workstation which is actually the workstation the
Radiologists will work at and observe and make the diagnos decisions of the oncologists now the reason I've got a a little red star there and this is a great one is when I was the Ministry of Health about a year into my time there we received a notification from I think it was from caer and from the M team that the dcom base Cod line stand the B the source code or the base standard for for rendering the um D comp images they found a vulnerability of 7.8 I think it was almost up to eight edit globally and they had to work out how they were going to encourage all the healthcare providers to properly patch
and overcome that um vulnerability there were also instances that they identified that attackers had exploited that vulnerability and had gone and maliciously altered some of the clinical images so we potentially had clinicians making what they with clown sound clinical decisions are maliciously altered imagery so again when they're placing absolute trust in their technology and that sort of activity can occur um it boggles the mind you know inaccurate cancer diagnosis or anything like that could have potentially occur so that's kind of the vector we're talking around for some of this sort of stuff um that always makes everyone go it's it's it's great in terms so in the last s a few years we've seen um which should be no
surprise to people we've seen an almost 7 to 800 in% increase in cyber attacks on the health sector globally since 2021 um the industry has experienced the highest average percentage of attempted intrusion in 2022 has been the healthcare sector and int internet of medical things devices have seen 123% increase in um vulnerabilities and potential exploitations in the um in the last two or three years as well because not that well understood if you can access them in their public internet facing which in some cases they have to be for the purposes of um vendor support and the like um that you know they're not well understood and then you've got people the ecosystem within the the
business doesn't know how to interact with properly on it and they've all got different parts of responsibilities and these issues like you know in 2022 the PT PTC exceeded age and desktop server high levels of vulnerabilities and these to do with I think there was some dispensing of some um medical um drugs thing Bluetooth low energy vulnerability cuz those in the industry remember a few years ago Bluetooth there was some ongoing um exploitation issues and vulnerability so they're finding that a lot of these devices can't accommodate the more modern version of Bluetooth so they're now stuck with low power energy ones where um you can go past and just potentially recompile the code setting in inside um these devices
in fact um I Heard instances of stories um Dick Cheney had a um had a you know had a pacemaker and they were concerned that someone would get close enough to him potentially alter the um imagery and and the details there as well insulin pumps W to cry porry on PX machines anesthesia delivery machines barnab Jack at kiwi as well he was did some really interesting demonstrations if you look up his details that can be quite good now on the home stretch so the challenge as I've said there it needs to be a team- based approach to device safety and Effectiveness and a partnership based approach so device manufacturers farmac M safe TJ in Australia tat AA
which is our equivalent to some of the Australian digital Health Association territory and state governments and central government all working together to apply knowledge leadership and stewardship so understanding how can we deliver this how can we deliver these outcomes that make sense but the big challenge is is culturally speaking it's not well understood um the challenge is mainly it's not understood by our health system it's not understood by the procurement teams that well and everyone's stretched and everyone's stressed and no one actually kind of works out which problem it is there's also a serious lack of cyber security professional capability certainly New Zealand within Health sector procurement and oversight there's just enough not enough smart bodies to go around in that
regard the lack of capacity New Zealand particularly and potentially in Australia as well commercial impairs when cyber security cyber secur is expensive and difficult and makes you makes it a more difficult thing to deliver to Market slows that down and of course also the size us on Australia's digital health markets are really really small for some of these providers when you consider their used working in Asia or in the states in Europe so if you make it too difficult for them to move into these markets they just won't bring the technology here which means the you know patients miss out on some of this life-saving care you know so I guess in the home stretch what are we going to do
about it providing practical and collaborative support so if you do not working with health secr agencies that are involved in the space support them encourage them to ask the right questions help divise these questions for them don't say that's a real problem you're saying well I know you got to deal with this and it's complex let me help you encourage responsible behavior there's some really good user guidelines from the Department of Home Affairs here in Australia along with TGA around how to manage iot complexities securely um there's a lot of really good guidance out there it's really easily available and it's all free and again engage with those Healthcare Providers make them aware of the stuff Provide support
encourage them to be go on a journey with you and particularly work with the procurement teams and understand how the different system fits together and encourage them to ask effective risk Discovery questions because the end of the day it is a team sport and the end of the day we're all working for patience and that's me thank you very much for your time I appreciate it





