Getting Permission to Break Things
Show transcript [en]
well hello good afternoon I'm not an attorney so I guess that's why people are here as opposed to the other room right so what I'm gonna talk to you for the next I'm gonna be 45 minutes roughly if I have my time right is we're going to talk about getting permission to break things and it's an ensign on thing you come to these b-sides events right they tell you all these cool tools you use to break in this stuff right hopefully you've seen like the Ukraine and the break you know getting into those SCADA systems and basically it was a you know the malware they establish the point of presence they VPN in and they talk about some of the tools that
are in place there and they talked about doing a penetration test right so that you could test your system before someone else does let me first get a show of hands how many people actually do penetration test as part of your day to day work anybody nobody okay all right this this is how many of you hire penetration testers okay I see two or three hands okay let's see how many you hire how many hate penetration testers well you know that's that's actually part of why I made this talk was because people tend to hate the penetration testers and so in this talk I try to take a little bit of my experience and by day I'm the mild-mannered VP of
information services at a financial services institution I recently changed hats them and so now what I'm talking with vendors they oftentimes hate me because I'm asking for them for things in the contracts why because I was the consultant for several years I was the consultant that would go into a financial services firm or healthcare firm or utilities firm and they're bringing in me in for one reason and of course I really want to help them do the best thing like you know the best thing possible right and one of the things we learn is there's this this happy medium and the setting of ground rules and safe words like get out of jail cards and
you know what does the customer want and also there are some things in this talk that if you are a company who is contracting with a penetration tester you can keep these things in mind because your company that you're hiring may not know this or may not tell you this right and it's important so it's important for both sides to know this right I do adjunct instructors well online health information technology and I you know I have found very few certifications I did not like so cissp sort of hacker the I Sakura C is a CIS M and so and any statements here I have to have my disclaimer I'm not an attorney and I don't play one on TV also any
statements I make are of my own and not of my presence or previous employers so why can't I why can't I do a penetration test why can't I just go download this cool thing that I've heard about these sides this week well because you don't have permission that's one of the key things right sort of how to certified ethical hacker is that part of the ethics is that you have permission you have an explicit authority to do what you're going to do right someone's giving you permission to break things and if you do this without permission um it's going to affect your job security you know you're gonna find yourself demoted to ask to stay home possibly
permanently not going to another job and it's a very small industry really I think I see a lot of folks here that I've seen it like temple events and other piece sides events we know each other right we know what goes on right so why can't you do a penetration test here's the part we you know that actually the business is concerned about these last two bullets see there's this part where you affect the business of the customer and you know Financial Services I put an example up there that the teller when she takes the your money when you're making a deposit right the teller can't key in your deposit no big deal right they can do it on
paper I've seen them do it this is continuity but then there's the more severe diff scenario there whereas I as a customer can't even hand them cash because their systems are completely offline or maybe they only have an ATM and now I as a customer I'm feeling direct hurt because some pen tester took down an ATM machine thank coming from healthcare I used to love this in the covered entities into hospitals okay they would they would tell me point blank about this one here I have a patient who's going to die on the table and that's definitely and that's gonna affect the the patient's you know if I take off any of those monitoring systems or anything like that
so we need to establish the fact that we have to get proper permissions first we need to set the scope and the boundaries and and what is included what's not included right we need to get a bit of buy-in right and this is a bit of negotiation one of the key things is who can authorize it right yeah I could go to one person can do they really have the power to do it what is their scope of even dare Authority right if it's within IT have they talked to the chief medical officer that was a big issue right or have they talked with any of the other accounting departments about their processes that they're running and
you know do they have the necessary power are they working in that little silo right and is there communication between those departments do they know what's going on right did I know that your call center that your retail establishment was gonna take all these calls on Black Friday yeah if I pentester I should know I would probably not do a pen test of a retail establishment but as of what a week ago to like January 1st I probably would stay away from that because this is their peak business time right and so if I'm talking with IT I got to make sure that they've involved the other people in that as well that there's communication hey your systems may go
offline because we're gonna do this pen test and well okay why would they do that right I'm saying okay don't do a cheering Black Friday time don't you're doing the holiday season you know why they might we'll do it if they have an audit or contractual requirement and they forgot to do it so that's where you got to balance the need sometimes right one of the needs of the customer are they just trying to comply with an audit requirement or is it part of a contractual requirement does anybody here deal with the credit card data I think PCI compliance must have your scans done every quarter right a full pen test every year right by an
outside third-party right so sometimes I said that requirement that comes into place you have to do this pen test right other times I I've done one where it was just they wanted to win the most wired or something it was some you know high tech for hospitals so actually their need for a pen test was really low because they just wanted to check the box that said they had done one so what are their needs right and are they trying to be proactive you know if you were in the other room they talked about that pyramid Maslow's hierarchy of needs did anyone sitting in last presentation about the power crisis the power shutdown right Maslow's hierarchy of
needs I wanted to put this on the slide as I heard his talk because I was like you know what yeah there's that like basic requirement that if it's a contractual requirement that's like NASA's basic need I need food right and then you get into the higher levels of like it's an audit best practice versus it's proactive security going up much like Maslow did and that hierarchy of needs sometimes they're just doing a penetration test because they want to validate the remediation efforts in fact if they've been breached maybe that's driving their need for this pen test right and maybe that scope already tells you or maybe in the course of that remediation effort it helps you
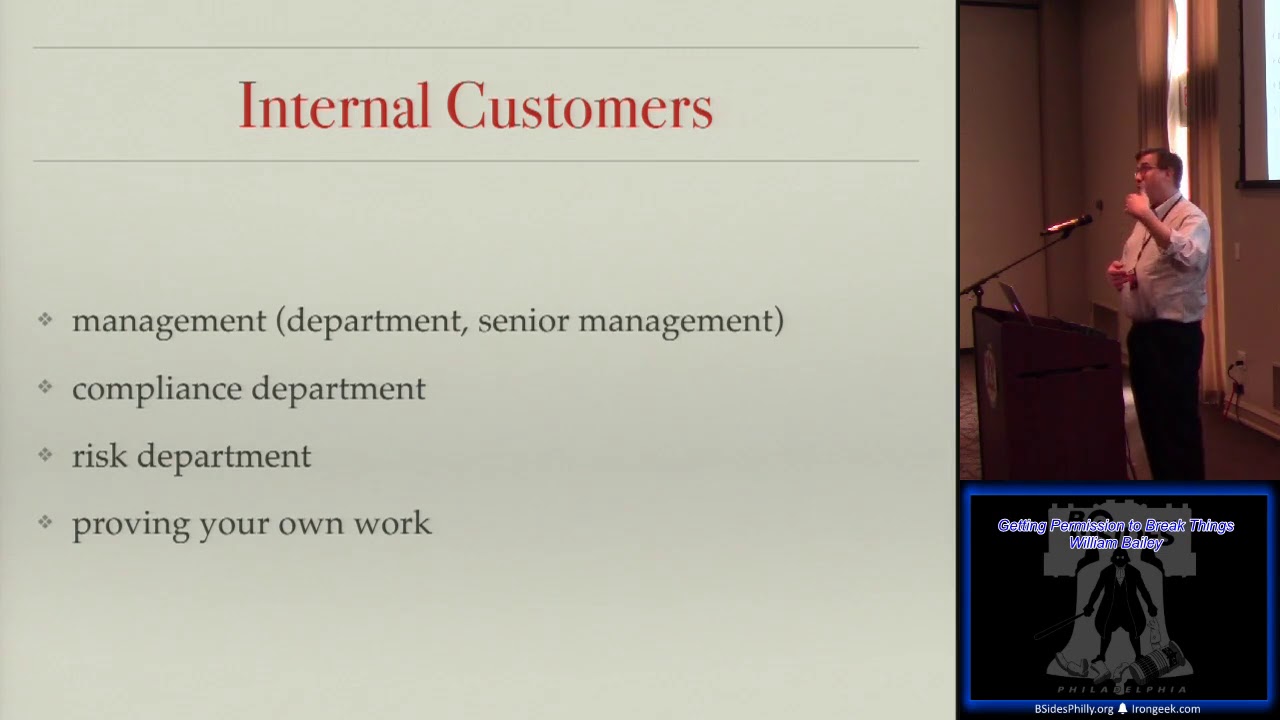
define what you're gonna include or exclude so the customers of a pen test you've got management within the firm right your management senior management i-i've known managers who want to do a penetration test and this will be the someone who's on the board of directors and they want to do that penetration test right other times you get the the management and he's kind of kicking and screaming their feet right who are those players what's what are their concerns he may be working with a compliance department he may be dealing the risk Department sometimes you are proving your own work right every so often maybe you've done all these new changes and you're gonna test your homework so who are those
customers right and the external customers if you're dealing with someone outside of your own organization especially those of you who are in a consulting role you have to make it a little palatable to them right actually we have to make it palatable to our internal folks sometimes too we have to sell them on the whole idea but how many folks work for consulting organizations or contracted type organizations service providers got a few of you here right okay I you know it's really cool to break stuff right that means you did your job right but they don't necessarily bought on with that right how do you make it sound like something they should do you know because you
don't want to just be that you're gonna do the pen test just because everyone else is doing it right so you know the credit card you know you have to do it because it's a PCI requirement that's contractual requirement we have to do it but anyone who doesn't have a contractual requirement how are you gonna make it palatable to them right how are you gonna make it sound like something that's a good practice to do right you know and what is you want to stay within their comfort let range / decide I refer their level of pain okay because sometimes there is a bit of pain in a pen test because it took the system
offline or you found systems that were out of date and now people have to go patch all these things right there's a lot that you found these weaknesses and controls set you're causing them so pain maybe you did cause an outage all right how many it's inevitable right you run a scan you think everything's fine and then you find out the printers have been spewing reams of paper right there's a certain vendor product that I used to have to babysit because that's what it wanted to do and I couldn't tell it not to really well so I just had to babysit it otherwise there'd be tons of paper all over the place and ironically that was
us real source of paying for them stop the paper so I'd have to babysit it and make sure you're on a paper wanna printer stop right what is their level of downtime you know do you have to this colors your hours work right can you do it during Monday through Friday 9:00 to 5:00 or can you do it at night right how are you going to schedule this to them what kind of system malfunction they willing to tolerate you know do they have fault tolerance meaning multiple data centers if you've got one data center that pains gonna hurt you a lot more isn't it versus if I took down a call center in Columbus Ohio they just
robbed my call to somewhere in Utah or somewhere in the Florida or something like that what kind of pain can the customer tolerate if I take a system down do they have another one to back it up but they could just flip the switch and go right so and with external customers we want repeat customers usually don't it's a lot harder to get the person to ask you to do work for you right and you like to go back in year after year after year uh you know it's nice to see new new hospitals new stores new credit card companies but it's also nice to see the old ones again you know it's a lot
easier to get your job done on subsequent years usually so you have to address the customers needs how many folks here actually write the reports anybody a couple people three people do we love the reports that come out of the tools no it's not really intelligent is it and that's yeah of course you get management right so one was an MBA and they know all about the business right they know all about your insurance field or your banking field or your retail field your manufacturing field they know all of this stuff and you tell them something about obsolete version of AIX and what happens there's that you know their eyes just glaze over they tune out
me right or what if you give them a report of everything oh my god I give up I feel like the Aflac duck you know with like five million holes in that boat right so you know sometimes you have to take that report and try to drive home because maybe you start finding trends and this helps a increase the customer satisfaction on this job right but also this is something you negotiate going into it like hey what do you want your report to look like you ask it upfront so when you get to the final and you're not guessing at it right you know what their important ports are you want to address their reporting needs I found
that most people don't like drinking from the high fire hose and I'll have to give you the full appendix of like 120 pages of every single vulnerability because you asked me to scan every single system but it's gonna be an appendix I'm gonna have a front section of the report it's gonna tell you sort of an action plan of what you can do for the one client we had about another 30 pages but then we had 120 pages behind that I said if you really want to drink for the fire hose because we had someone say they wanted it it was perfect purposely portioned off that way do you want to see every single system and
every single vulnerability here it is but we're gonna produce you a section of the report that you can actually take some action on and sort of give some intelligence to and the other thing I've noticed here if everyone has been a customer that's received a penetration test report and it says that everything's fine anyone get any of those no no no one I've seen them I'm like really I think to myself really you found nothing nothing did you bring my IPS tea and cookies too you know because well you know what happens I don't know we don't we have a tenable here and they had their product necess right I don't know if you Nessus next pose is the rapid evans
product that does vulnerability assessment you know if you don't tune that thing back and you just let it go full or on your network the IPS stags it and you get a nice empty report because the IPS takes you over right the so you really need to look at those tools and make sure as testers we're gonna need to give them a report that's good right so you know if we don't have permission it's unethical it's just yet another attack on people right and this would be the scenario I well I'm just say I remember one company that had somebody that took a virtual machine running Linux and they thought it was really cool to run a evaluation
copy of Metasploit Pro what was the problem with that nobody knew it was there right people started going what the hell is this how do we tell how the heck do we tell you verses from the attackers from the outside and she didn't win a lot of friends she actually was looking for work about three months later and it took her about three months but she was looking for she made a lot of enemies and and actually she didn't get a lot of positive results either because they shut her down before she could actually find anything so she started kicking this off it spewed all this noise out there and also because it was that she didn't have permission what
happened to anybody who looked at that report what did they actually see when they looked at that report that she said look see what I did what do you think I actually saw your little game on my network that caused me my network outage and I'm supposed to be happy with this so people that that thing that she put out there that partial report did they even look at it with a positive light at all no this is just evidence you attack your own network right she you know one of the things we see too is if when you establish a permission you start saying what systems and scope right if you don't have a
scope to find you have no end you don't know when this game is over you just keep going and going and going so when when you obtain permission this is one of the things we have to do when we negotiate this whole thing right what are the levels of it's not just can I run a pen test yes or no this is I get in one of the other key points here right the decision it's not just am I going to run a pen test what systems remember I said this an area of the call centers different sites right I'm going to limit myself to one site I'm gonna limit myself to certain types of systems
right what kind of attacks are allowed maybe and quite often we have to do in order to get full permission we'll actually negotiate where we'll do a vulnerability scan first see the systems that are out there then go back to the customer and say now which of these systems would you like us to scan right sometimes we have to do that we have to do that go back and forth right because maybe we found find something we weren't supposed to find and why do they care fragile systems the fragile systems right there look like the old systems that are not patched or there are ICS systems or SCADA systems that could affect key functionality what's you know
maybe you're not going to allow people to do manual scripting maybe it's all automated testing and that's all you're willing to do at that point right you know what what constitutes a failure of a system when do you stop right of like hey if I find XYZ information you know if I for instance we're to contact if I were gonna reach into an MRI system and I see an image do I try to go beyond that or do I stop right if I reach if I compromise a VPN endpoint is that where I stop right because at that point we have the assumption that I could continue on right do I get domain credentials and that's what
stop right you know do I say okay I've got domain creds we're gonna stop right now because it could basically be assumed I could get into anything else I want at that point and sometimes that's what it is right it's not just sometimes the customer will say hey I want you to go to attack everything but a lot of times it's just okay tell me how far you can get but at a certain point I'm going to tell you to stop we could just draw the conclusions you know and are there any legal issues with the data you're accessing right well what is this customer are there any non-disclosure there should always be non-disclosure agreements in place anytime you entering
movies I know that's that lawyer talk over there he's talking about non-disclosure agreements anytime you agree to a penetration test that you're not going to divulge any secrets you're gonna give the up you know they're going to receive the evidence there are some legal issues you need to be aware of like if you observe a crime a legal crime you may need to elevate that to law enforcement yeah confidentiality for these projects PCI you're accessing credit card data right anything you find on a penetration test is really that customers it's not yours there are privacy issues some of the regulations we have I asked like okay healthcare whose health care so we see HIPAA right how many work in
education nobody you would be FERPA because if you're dealing with student loans you have Student Information GLBA any bankers here so GLBA applies to you maybe PCI depending how the business is molded right are you publicly traded are there any Starbase Oxley issues that you have to be aware of this we're looking at these systems and privacy rules we have in the u.s. federal rules and then we'll have state rules and then we'll have local government rules and then we also have industry based rules so a lot of these like the and the FERPA they were based on a segment of Industry what if I was dealing with a company that has European customers in that system has anybody
worked in a multinational organization were you able to see everything for us and North America and Europe and Asia no you can you can see Hong Kong or you can
that's that's the way it's been I work for an organisation where we had a European counterpart and if my system accidentally picked up anything that was connected with anybody in Europe I was no longer allowed to do anything else with it and I had to just sort of hands-off because of the rules that you can't you can't exfiltrate that data across country lines we're seeing that cross boundary issues and he gets a little murky too with a cloud service provider can you pen test your cloud service provider definitely not without permission and probably not you know that's definitely that's gonna be one of those you're gonna have to get a sheet very very clearly right we had those
cloud various service providers you know can I attack the service provider why not because it's a shared service it's not just yours so if I do a denial of service on a service provider I didn't just test my own service I tested everyone else's and no one else can get to so I can cause outage for others so you know what's it's good we look at our types of networks you know there's that external right internet facing attack there's that internal right we see different results don't we different types of scope that we define there extranet do we need to serve do we need to get permission to to penetrate every single desktop in their environment what do you
think some people say yes yeah I've had clients like that yep yep scan them all scan 2,000 machines you know what we find actually if you sample them pick a random sample so they'd sit there and they'd be like yep I want you to scan all of these machines why am i do a phoner ability scan on all the machines okay that's fire but then we would go into a penetration test face I say you know what I'm all I going to do like certain floors or I'm gonna pick a random ten systems in each one of those floors actually because I don't need to take the full time of affecting all of the systems remember that pain point
with the customer if they've got 20 machines and you limit your tests only ten what does that mean for the customer for the business processes huh it's less painful because they could go use together ten systems right you know it's always fun when they have Norton the Symantec protection suite right the host-based intrusion protection software what does it do when you try to pen test it or even vulnerability scanning it just comes up tons of popups right and it's like what could you do about that no this is my job I have to do it right this is part of that getting permission and that communication right so if you're working with the IT team they
would need to talk to that department to make sure they know hey by the way if you see any popups on your screen this is a good time to go get a cup of coffee because it's one of those things right you get the tons of popups for like five minutes and then it's done right and if you try to fight it you know it was hard to get work done anyway it was actually funny one of the customers were sitting there in the room or like yep we know this is gonna happen and they were like hey I can't access my application yep we knew that was gonna happen because you're getting all these pop-ups and
because we're saturating the network for that you know for that one department but you know it actually is 12:30 why aren't you at lunch so they making sure folks know and actually that's why I put this point here about statistic or judgmental scopes um you could do like a statistical like ten percent sampling right or twenty percent and you could just say I'm gonna take twenty percent of the machines just at random right kind of like the way I do a phishing test sometimes I'll just take a whole bunch of users and I'll just set them phishing emails and I don't care what department you're in and I don't care if we failed a previous test and
I'll just take a random statistical random sample other times I will take a judgmental sample what kind of things do you think I might put on a judgmental scope to include an append test certain departments any other idea what else what might you do for a judgmental scope where your make taking your cherry-picking systems oh yeah oh yeah I was gonna say the secretary of the sea level there's a prime one right that's a judgmental scope you say you know what I'm gonna pick like a couple staff workers a couple power users and I'm gonna like I've gotten tons of DLP error messages from these five people and they're always going to these weird websites yeah I might want to look at
that system right I might sort of take some opinions and go I think these systems are gonna be a problem so okay so yeah departments or groups see if I say Department I just hit everybody in medical I hit everybody in a branch right but judgmental gets into that you know I think this system is a problem I see a system that says Windows 98 so I'm gonna like sample I'm gonna use those as my sample right and when you start looking at other devices to remember the printers and you get like the reams of paper coming out of I might do one or two but I'm not gonna do the whole fleet right I might do your
credit card printers you know the instant issue devices the register printers I might do part of your phone system right because phones these days are voice over IP right used to be oh who cares it's just a phone I don't know maybe there's a way to take to actually leapfrog from the phone system into the production network because they have this handy dandy jack on the back that connects to the network some of these other devices though you know that we have to watch out for certain pitfalls check printers and instant issue you know credit cards debit cards you know the manufacturing controls a lot of that hardware wasn't designed to require authentication or encryption and if
we're if we're attaching to something on a production network what's it gonna do the manufacturing line right the scalar notice if our critical infrastructure protection right biomedical devices this is a really tricky one because most vendors say you are never ever allowed to patch them so it's kind of weird I can do a penetration test on it and it's useful maybe to see what's out there but I can't do anything about it so it's one of those things I'm like yeah I'd like to do this but I can't patch it unless somebody's willing to cough up money for all those new machines or segment them to another network but I want to be careful because remember these
biomedical devices I had to be very careful I was if I was working in a hospital I want to make sure that their IP addresses are set up properly right and I need to know this going into it because they might give me permission to to scam like the patient rooms right hopefully they've segmented their network so that the biomedical devices that are connected to patients are not in the same IP ranges and I say hopefully because I've been on that test where you ran a pen test and we found that there was no segmentation and thankfully we just started with the vulnerability scheme and as we started seeing results came in we're like hey we're gonna stop some of
these machines because we're seeing things we shouldn't see out there right and we don't want to affect patient care right so so just because you have permission doesn't mean you run them over either multifunction devices you cause denial of service where they can't do legitimate turnouts right wireless access points don't want to cause an outage there again you know catastrophic failures these are the ones that you know we want to avoid these right and when we're asking for permission we should include these kinds of questions right what are your core systems right then if I take it down today are going to cause pain what's gonna stop you from taking care of that customer right it's
it one of those things where I'm going to saturate all the buffers and it looks like it's running fine but then tomorrow morning it dies so if I had those kind of devices on the network as a tester what I'm asking permission what would I do I'm gonna make sure that hey I'm gonna scan this system but make sure you got somebody who's able to come in and reboot that system right make sure you can give it some extra monitoring attention after the test and that's part of that like hey we're gonna do this if you want us to work on these core systems make sure you've got your tech support handy because you don't want to
be on that phone at nine o'clock and you call the 800 number for your tech support and you hear that message that says we're sorry but your agreement is done title to you to premium support because that nagger down so we also want to be careful of when the VP or the VP are affected why did I put that in quotes like that remember that secretary of the the c-level executive she's a very important person for he is a very important person right there's that person who's gonna make your life really really difficult right why did you affect me well if I had thought about the communications beforehand hopefully they know it's coming right that's why that communications getting /
getting permission and making sure that everybody knows is to make sure that VP is aware of it and can be somewhat understanding because it's sort of like it's almost it's a little bit like that you get a jail card because at least they knew it was coming nothing should happen but this is one it's gonna happen and if it happens you know and it'll be temporary so like that one department where the system's went offline we caught up we said look when this happens it's going to be five minutes you know so we knew okay any time we hit any of these types of machines it's gonna be five minutes tell your people when it starts to happen go
get a cup of coffee because it'll just be gone right you want to make sure that the staff can serve your customers your clients right so like you don't want someone in the middle of like I'm trying to think like a mortgage closing right that's a stressful time and we deal with that you've got to the closing box and you've got people sitting there like antsy at the closing table because to buy their house right where's my documents so you don't want to take down the system that prints all those Doc's out you want to make sure they've got that you know anytime you know you're like if you're doing payroll probably a bad time to look at an HR system for a
pen test like the day of payroll should wait and least until the paychecks are cut and so when you're asking permission be aware of that like hey this could be a catastrophic failure so I want to schedule it and I want to minimize the hurt from that now what is allowed well if you have a course system like the core banking system we don't test on a production system and SCADA systems you're not supposed to test on SCADA systems either what do you do you test the test system and in theory the two should be the same I'm just crossed right so make sure you have your tech support on call this is a key thing when
you're when you're negotiating these rules of engagement make sure you know where tech support is right make sure your Tech's are on all right then I'm gonna call the guy right when I call my tech person you oh I'm sorry I'm out with my wife and kids or you know I'm putting my daughter to bed you know it doesn't really make me feel all warm and fuzzy right oh man I was in the middle of something I'm not on call you know when is what do you belong to test does it have to be after hours make sure these people are available right I've had other clients that said you have to do it during
business hours Wow okay if you insist you know but work within the customers guidelines right sometimes you have to be client supervised that actually was the one I was sitting there he was here and I was here and he was keeping an eye on the network from all the network monitoring tools if he saw something he didn't like he had the authority to pull the plug at any time look that was his comfort level if I took down a system and he noticed the adverse impact he had the authority to pull the plug and that's okay you know I agree to that these are the terms and conditions right this is part of my permission
so this of organization what are we looking for right do we want to see a clean report you know and what does the management want to see are they just trying to mean a checkbox to say they did it right is this a compliance based on it a couple things we should watch out though for is that a penetration test should never be something that's an evaluation for the current staff that's not a good way to get permission you know they're obviously the staff doesn't want you to find anything because they're gonna get it evaluated on it so they're gonna they're not going to make your life any easier and it's just it's not going to again it's gonna be off
this piece of butt you know garbage report so hopefully the the management he's doing this for the right reasons right it should not be for the evaluation encourage staffer systems I mean there are certain things they look at like patches right and if you could tell your team to patch patch patch patch and then you do the scam you find tons of unpatch systems well and that is what it is but this shouldn't be the only metric is that one of the key things I think whenever you're doing a penetration test it shouldn't be the key factor for there for the staff evaluations definite failures you know if you failed to meet the client's needs you've got to
get you know when you ask for permission to break the system to scan the system your report has got to address their needs so this is you asked what their needs are they give you permission and you deliver a report because that's also part of that repeat customer cycle this is part of that cycle of coming back again this is not something you do once and done you're gonna come back and do these again as we're pen testers we we shouldn't deviate from scope right if we find some surprise systems out there we let them know hey we found these out here and you didn't tell us they were here right but we're not gonna go scan
them automatically I as a contractor wouldn't want to do it because that's global time and I don't want to waste my time the customer maybe they don't want to scanning those systems maybe they're fragile - they didn't tell us they were there right you know crossing over the line we definitely don't want to say hey this is really cool like we think this is cool in front of the client you know that there's that image that a lot of times folks have the pen testers it's like johnny i hack stuff I'm really cool because I hack stuff but the business folks don't really want them what do they care about they care about what's the risk to our systems right am
i meeting my contractual requirements right not am i doing the cool thing change there but our call to action whether we are hiring the pen testers or where the pen testers ourselves is we need to start somewhere because just coming out of that talk and any other talk you hear about half of these breaches if it's not physical physical security related or end-user related it seems to be patch related right it's sort of like we can go those three pockets so we've got to do voter ability scans and penetration tests right have to we need to when we come up with this agreement of what we're gonna do we have to stay within the lungs oh man I'd
really like to go to attack that no wait until you have permission wait until they give you the go-ahead on okay and you know you'll have that get out of jail card sort of I have permission to do this when you're doing this so like you know if I was in the basement of us facility running these tests and someone came knocking on my door yes I had my letter of authorization all right was that a question back there I thought I saw a hand raised set the scope and pace to what the customers willing right as pen testers we shouldn't we we have to push them a little bit but we shouldn't totally run them over right
because this is painful for the customers but shouldn't be but it is right because we all think our systems are secure and you know some progress is better than nothing it's one of those it's like you know I've been on these we're okay only do a vulnerability scan and don't actually penetration don't actually do a penetration test until I say it's okay I'm like wow that really kills it right cuz you know the difference between a vulnerability scan and a penetration test vulnerability scan I see what your weaknesses are with a penetration test I actually go into those tools and I try to purposely exploit them I purposely send code I try to escalate my privileges so make
sure that you stay within those lines stay within those guidelines right because for some organizations even getting a vulnerability scan out of them is progress because they don't want to admit to that they've got like 4,000 vulnerabilities across the enterprise nobody likes to hear that but at least if we can like make some progress right yeah that's a start somewhere and try to move in the right direction and we want to make sure they don't retreat so we've talked a lot and I know that's what 45 minutes pretty much where we said we were going to be I wanted to make sure I left some time for questions and answers any questions I don't know
let's see I said the wrong word didn't I cuz I said what is your favorite color and the key is to have one to make some progress pick a color that's your favorite color so blue I'll stick around for a few minutes if anyone has any other questions otherwise thank you for attending
you





