I had no idea what I was doing but now you do
Show transcript [en]
well thank you for the introduction um yeah i am uh aaron rubesh my presentation was going to be all over um i just kind of threw the name out there i figured it fit with what i'm going to present to you guys um i knew i didn't know what i was doing but now you do and so the gist of that is basically i learned security the hard way i got into it um when i was younger uh unknowingly really and i just started you know going through online resources and going through the the fire hose like like was mentioned in the previous prison presentation and really trying to learn everything on my own and there is a lot
of information that comes from that and so i i told myself if i could ever help anyone else learn security i hope that they don't have to go through the massive amounts of information like i had to just to get to where they want to go and i and i hope that this this presentation really helps to clear up kind of what it is that you should know getting into security what are some what are some uh i guess technical goals that you should try to achieve um going into your first job or or going into school or just just setting for yourself if you just want to do it as a hobby you know what are what
are some of those technical goals that you should kind of prepare for um when you're really trying to get into this stuff because it is a lot there's a lot of different tracks in security there's a lot of information to go through and it can be overwhelming to someone and i i truly believe that if you have any type of knack for technology you can do well in cyber security um but the thing that scares a lot of people is just the sheer amount of information um in the stuff that i guess a lot of people expect you to know if you look at any job applications and stuff out there you see all of these crazy requirements for
everything and it's that scares a lot of people off when when really you you can get by with with a lot less than what's uh than what's required so i hope i hope this presentation really serves as a is a good starting point for for someone getting new into security that wants to make this their career um and if you if you've been in it for a while maybe maybe it'll serve as a refresher maybe it will kind of um remind you of some of those skills that you kind of put to the side and you didn't pick up on that that you should get back into so a little bit about me so currently i am a software developer i
am not in a security role per se but i previously was a penetration tester and i worked on an application security team i live in houston and um so i guess one of the questions might be is why is this guy talking to me about security if he bailed from security um i didn't bail out of security i whenever i learned security i also learned programming at the same time i taught myself both skills and i i feel like they they really go hand-in-hand because you wouldn't have the insecure software if you didn't have uh or you wouldn't have the security vulnerability if you didn't have secure software um people are a portion of that but
you get the drift um in my in my roles as a uh as a corporate penetration tester one of the things i noticed um was that the tools really suck uh well i hated the tools i hated using the tools and um i always thought that that's that's some place that could be improved greatly so i looked for a company that was doing security tool development um and i joined them and now i'm helping build uh security tools so still kind of in security but more of a software dev now i started off with security really before i really knew what i was doing um i used to play a lot of video games like like mo
like most kids um and i really wanted to be better than others at those games but i didn't want to put in the work so i started developing automation tools um cheats hacks exploits i started making brute forcers for some of the games i played to break into other people's accounts do all the stuff that they uh that they worked hard for um yeah sorry if that ever happened to you i don't do that stuff anymore um but to do that i had to learn basically reverse engineering how to um how to debug an application that i didn't have source code for read different variables inside the memory uh and then call different things um
that i wanted to do or that i wanted to automate and for brute forcing it's same thing as you know um john the ripper does or other other password crackers and stuff out there um but just developing that from scratch not really knowing that that's you know kind of involved in security it wasn't until later on when i started college that i actually saw those skills that i was using and said hey this is actually a pretty decent um pretty decent career avenue and so i i jumped on that train and i got a degree in uh computer information systems and i focused on security as like a hobby and all the tool sets and stuff on the side
and that's where i got to where i am today so um yeah so i basically just want to get into like the skills that i see that are valuable for someone getting into security that i really in my experience my my couple years of experience that i see like my peers insecurity lacking it's pretty crazy that um that a lot of people in in this field now and i know there's a there's a lack of talent um but there's a lot of people who who don't have some of these basic skills and it's it's it's sometimes not a tool issue it's sometimes just a lack of the fundamental knowledge um and it will lead you to less you know
false positives and then better reports and stuff like that so uh the biggest thing that i always tell people to learn when you want to get into security is networking what is a packet how does it traverse a network how does a switch switch the switch the packet to you know whatever devices how does it how does a router work how does a firewall work um just basic like network plus ccna level networking knowledge um it's it's really crucial in this field um you have so many so many exploits and stuff that happen remotely now or the all the good ones anyway or ones that you can basically use from a remote perspective that you can
use to get into something that you don't have physical access to and to do that you need to know how how you know those devices are communicating on a network level what uh what type of protocols are being sent um what that looks like whenever you whenever you take a uh packet sniffer like wireshark tcp dump something like that and you export the the pcap and you and you're reading it you know what is that what does that information mean and then how can you edit that information to get it to do with do what you want you take some of the some of the network level exploits out there right now um that are just you know uh basically
at the protocol level you know editing different fields in a specific protocol that's going to make something some device on the other end communicate ineffectively or cause an exploit and you you learn how to build that stuff yourself so really you know how to read a pcap is crucial what the network devices do and then how do they do them how does the operating system do networking how does your linux machine route packets how does it assign ip addresses to different interfaces how does uh how does the iptables firewall work um if you've used something like pfsense before how does that stuff how does the packet filter and bsd work um and really the best way to learn this
stuff is to you know try to build your own router you can do that with just a uh you could set up a linux virtual machine set up a couple other virtual machines with it and you can build your own network turn on ip forwarding and there are some iptable rules in there and you can actually have a functional router that you built yourself and without really needing something else really getting into the stuff and actually playing around with it you're going to learn a lot and it's going to make you a better a better penetration test or better uh blue team if you if that's what you want to go into about a purple team
player um it's really going to really going to make you stand out more when you when you're able to analyze this information and and really know what's going on the uh second second skill set is is operating systems um really you need to learn how to effectively use windows linux and mac um i used to just completely bash on windows wherever it uh wherever i saw it um i never i never liked using it i hey i just hated it but really once you once you really get into it you know windows is everywhere and it's something that you need to learn how to use effectively you need to learn how to do the things that you want
to do in windows because you're not going to escape it and you really need to turn that into something that you could take advantage of so by doing that you know you can more effectively discover exploits on your own you can more effectively execute exploits um and execute uh different penetration tests and um assessments and stuff like that so uh along with those skill sets you want to learn how to like troubleshoot and inspect the operating systems you're working on so just figuring out okay what type of processes are running on this machine what type of services are running on this machine um what type of uh what type of applications are listening on different
ports you know when you when you when you run like an nmap scan on a a networked device you're used to just you know tossing a couple flags into an nmap into nmap and then running it on a running it against the machine and then seeing what what ports are open what what it thinks is there right but how do you do that from from the inside right if you're already on the machine you want to see hey maybe something's listening on something that i didn't pick up from externally what what may be listening here that i can that i can find that i can maybe take advantage of um how do you find what tools are available maybe
you are on a machine and you're trying to find a way to pivot somewhere else how do you do that without knowing what's available to you on the machine you're working on maybe you have a c compiler installed maybe you only have bash available maybe you have python installed what can you utilize to help get you to the next machine that you actually want to get to um and that's really the only there's multiple ways to learn this stuff you can go for like an a-plus or something like that or read through those books but really it's going to require you to just install some virtual machines or solid on physical hardware if you want and just
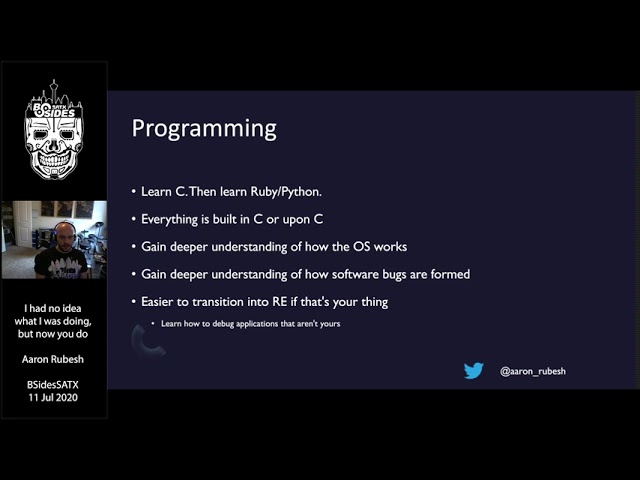
get into it and just start playing around with the stuff and really and really learning how all of the stuff works you know set a goal for yourself say hey i want to set up a vulnerable web server and you learn how to create a web server or on linux or maybe windows and you host a vulnerable one or maybe you um add some like known exploit exploitable configurations of that stuff and you set that stuff up on your own um to to figure out really how how the whole process of uh how that works um third skill that uh that i see really um a lot of people lacking is just a general programming sense of programming
knowledge a lot of people want to come to security that they and they don't really want want to program that much they want to run some tools run some they want to run some scripts and just analyze some output and that's fine um if you want to do that but if you but i feel like if you really want to want to learn you know what you're doing learning some programming is is going to be crucial to that i always say learn c and then learn something like ruby or python and that's because everything's built on top of c operating system kernels are built on c most of your tools on linux are built in
c most your tools on windows are probably built in dot net now but a lot of them were built in c um and really everything you want to do on an operating system on any operating system you can interface it through c if you want to build a packet sniffer you want to create your own packets to send across the network you can do that and see yeah you can yeah there's python libraries and stuff available for that as well but you have everything available to you already if you're using c um by doing that you know you gain a you gain a deeper understanding of how you know other applications on the operating system are actually using
those libraries as well whenever you whenever you kind of learn the low-level programming the system level programming like that and you understand kind of the linux apis and the windows apis you understand that how how other applications out there are always going to be using the same function calls that um that you would be using if if you wanted to write a program that did something similar right and you can use that to your advantage you know that an application that's communicating to the internet or to some other networked device is going to have to create a socket it's going to have to then send bytes across that so by knowing that you can you can understand that um
that if you go in and you actually look for where it's calling those functions you can actually see okay hey this is what data it's sending this is how it's sending data maybe if i can intercept that or rewrite what it's uh rewrite it what it's sending i could discover a new exploit or i can um i can figure out another way uh to get it to do what i want um it's things like that that you that you start to understand that that software is really um it really is what what you make it to be and even if someone else made it you can still do what you want with it if it's on your
machine and this is uh this this leads to a more easily tran more easy transition into like reverse engineering if that's what you want to do um preferably that's that's the stuff i enjoy uh debugging applications finding my own exploits um and doing stuff like that is is kind of what what i'm mostly interested in and that's that's where i think uh you know the low-level programming stuff really helps that because you're actually able to analyze what those uh what those functions are what they're doing in that application physical networking and not like you know just cabling up stuff but actually growing your community whenever you have a stronger community and a larger community of people who you
can reach out to you're going to just you're going to have a better baseline of knowledge to begin with because you have people who you can more easily ask questions to that can tell you either yes you're doing this the right way or yes you're doing this wrong way or you're looking at this the wrong way um they can help you uh get out of the weeds with a uh uh with an issue that you may be you know uh wrapped around into too much that's not really going to um to get you anywhere faster than you would have done it on your own um i like to say it's it's good job security um
and not in a sense that hey you're going to stay at your current job for for a for a good long time but it's better job security and knowing that you have people looking out for you i can't almost i mean it's got to be every day you know you see on twitter in security twitter anyway that um you know someone's saying hey i lost my job here's a resume and then you see you know 30 minutes to an hour later people helping them out and having four to five job offers in a day i mean stuff like that that's really that that you get from having a good community that you don't get otherwise
and i learned this you know in the past couple years a lot better than i did before because i was always kind of the guy that wanted to take everything solo i always wanted to figure it out on my own and really try and just do it do it myself i always wanted to figure it out my own and never and never really take help from others and i've had to i've had to struggle against you know thinking that way and get out of that mindset and really embrace um having a larger community and um really communicating better with others and contributing back to communities invest in the education of others you know don't just if you see someone asking for
um for help with someone or they or someone wants um want some assistance doing something don't don't think that it's oh that's uh that's too easy for for me to really care about someone else will help them you know or maybe maybe you're afraid of being wrong when you're trying to help someone um or you see someone just struggling with a with a certain topic that you know a little bit more about um you know just take five ten minutes out of your day to just help someone out help help at least lead them to the right path um and not just and not just ignore it it's gonna make you feel a little better about yourself
and it's gonna help the community um as a whole um because we're all we're all a community we're all we're all in this together we're not we're not fighting against each other or anything um you know the more the more people we have investing back into into the education of others the better and more uh more knowledgeable our community will be as a whole um radiating on what was said in the in the previous uh presentation as well you know attend ten more conferences attend the local ones if you have uh b-sides locally um unfortunately the houston one isn't that great i don't think um but uh but you know attend attend on a couple
uh you know a couple cities away you know fly out of state and go to a different uh go to different conference um go to go to some of the larger ones go to small ones um you know just just find other find find ways to go out and meet some people you never know who you're gonna meet and uh and what type of knowledge they're gonna have and what what type of uh what type of opportunities that it might present you um another school skill set i like to uh i like to add in here is don't just learn a tool learn how to learn how it works don't just you know get on a windows machine
and run mimi cast whatever you want to do to try and get some passwords right learn how that tool is actually doing what it's doing um because chances are that whenever a tool like that gets fixed there's going to be some code changes around where that where that tool is hitting and if you know that code is changing in a certain area you can also use that to your advantage of finding ways to get around what was changed and by knowing what what kind of type of areas of an application you're already targeting uh it kind of reduces the time it's going to take for for like a new x-ray to come to come about or a new way of uh
or a new way of um of executing and getting the same functionality is gonna it's gonna come about so um you're going to uh you're also going to discover a lot more ways of of doing the same thing um i like to say you know uh whenever i wanted to get into like wi-fi hiking and man in the middling right um everyone just says okay go go buy like the pineapple right but you don't really need that you can do that with just a raspberry pi and a uh a wi-fi adapter you can do all of that you're on your own just by learning how the tools actually work um and making you know a more reliable
product or making something that you know you can rely on your own for instead of having to rely on a specific piece of software hardware it will also allow you to um to contribute back to other tools so maybe there is a tool that that's really popular that you like using or one that's just you know that's not very popular that's uh that you like you lose using and you want to help them out and you want to contribute something that you found with it you know you can contribute back to that tool and make it better which is going to then go back to making our community a more knowledgeable more knowledgeable community so a lot of uh a lot of people al also
ask me you know how do you get all the hands-on experience um how do you go get the first job that's you know saying hey i want you to have uh you know five years of splunk experience and um and uh you know knowledge of firewall systems and um and different ids ips's and how to write you know the most intense uh snort filters and stuff like that so um you really it it sucks that that employers would ask a newcomer um to have such experience but that's really unfortunately the the place we're in right now um and really i'm not saying you don't stand a chance if you don't try to create that hands-on experience
yourself um but it will make it more likely that you'll you'll get an opportunity from someone like that and there are some great there are some great employers out there that actually invest in your education and um and don't care that if you that you know everything off the start but there's also a lot of crappy ones out there that are going to want you to have that and it just in my opinion um if you're not kind of the person that's that's that's going to rely on just the employer being a good person um really you know it doesn't hurt to go out and create your own hands-on experience and in fact it's going to
make you a better more knowledgeable security expert by doing so so i always tell i always tell people you know build out a build out a full-scale vm network like act like you have a production environment that has a you know a database server a web server a couple application servers maybe an email server you can build that all out in vms now on moderate hardware and just try to just try to just try to attack it and see see what you can find see what you learn in the process of just setting all that up it's going to make you it's going to make you a lot better just just by going through that process
launch attacks on networks that launch attacks on like your built out networks anyway that really allow you to not not have to just hit a vulnerable machine so maybe you were used to doing like ctfs like hack the box or doing uh the vulnerable vulnerable machines or something like that and you are used to just spinning that stuff up and launching an attack at it and just going crazy maybe try putting a firewall or something in between that or maybe try putting an ids between that so that whenever you're trying to attack those things you're not just going straight for the vulnerable machine you're trying to get past other obstacles along the way um and the reason i say that is because
99 of the time it's never going to be as easy it is is in a ctf um or or any of the other challenges out there like that there's always going to be some type of security control well not always there are some places that don't have it but it more just expect there to always be some type of security controls in the way blocking your blocking you from doing you know the exploits you want a lot of people come in here thinking you know i all i have to do is run these these couple scripts um i'm going to then be able to uh be able to you know exfil some passwords and then
and then i'm going to be able to pivot on to the next one and you're not because you're going to have an entire army of devices actually blocking you from doing what you expect and that that throws a lot of people off um because they're not used to dealing with that so actually spin that stuff up you're on your own and practice it and then you know a great way to test if you know how to harden systems and harden your networks uh something that i did a couple times throw out like a a open ftp server on the internet and just you know see what hits it see how long it takes for malware to get dropped on it
um then try to add like some security controls to that and see if you can harden it further and keep prevent that stuff from hitting it do the same for like a web server have some you know database set up and just putting it on the internet is a surefire way of having someone scanning you and someone trying to hit you within probably 20 minutes um i think it's the longest i've gone of putting something online and not having anyone hit it yet is probably about 20 minutes so um do it in uh find a find a cheap cloud hosting provider and you know spin up a five dollar droplet somewhere and spin up a server
and just see how long you can go with uh uh without getting hit or um and trying to make improvements to that and try to prevent that from happening so
you





