Training with Raspberry Pi

Show transcript [en]
we're good i was able to hear myself so good morning i'm actually amazed that so many of you are awake and functional this morning was anybody here you made it into the room i'm counting that as functional function is a there's a great as a gray scale it's got a gradient there so we're all good anyway i want to thank you for coming out this morning thank you for coming to the conference and supporting b-sides dc hopefully you'll actually have a very enjoyable conference learn some learn some stuff here i am nathaniel davis i'm one of the organizers here with b-sides but just to assuage any fears i still had to go through the call for papers process and
get evaluated like all the other speakers so even though i'm wearing the staff shirt i did not get any preferential treatment so just wanted to throw that out there but yes this is my talk uh training on with raspberry pi so a quick little background about myself and how i got into working with the pi so i started off in information security as a policy analyst i got brought in because some people i knew thought i actually understood tech it just kind of happened that way so i got in and they're like well we need somebody who can do policy work so i started doing a lot of the policy reading and i realized that
i was generating some just really boilerplate crappy policy i didn't understand what was going on with the issues that i was supposed to be helping the company secure against so i started looking into a lot of the stuff and got to the point where i do realize that to be able to actually write quality policy i needed to be able to actually understand what was happening on the network some of the vulnerabilities i was hearing about that we were trying to write to secure against i had no clue i could just say well let's just uh let's just put up this firewall rule and okay maybe this will work i don't know so i found out that i needed a way to
actually practice some of this and learn some of it so i started looking for things and the whole quest to actually find this information and have a way in which i could safely practice is why i developed the range box and the range box is a raspberry pi training platform and i'll get further into it and i just want to caution people i recognize that for some people this is going to be really high level it may be stuff that you already know so for some of you that actually get bored with that i have turned it on the range box is active uh so the ssid is live fire so if you want to go against it feel free
uh there's also a where's waldo uh kind of scavenger hunt hidden in there and the reason behind that as you see seth is raising his arm in the back cheering about it i'll get into the reason behind the where's waldo in just a little bit but there's also a catch the catch is it resets after a set period of time so if you're working against it just be knowledgeable of that when i gave this talk in vegas i actually had a prize associated with it nobody bothered to try and do the challenge so if you successfully get it let me know i'm looking for a specific phrase that's associated with a picture that's hidden in there
but if you don't i'll tell you about it after the fact but if you get definitely get it let me know and we will continue on so the range box itself what is it well in this whole process of trying to find a way in which to practice i realized that there's not a whole lot of good information out there for people who are looking to practice their skill sets somebody who is new getting into the field you start looking at it and you find these really complicated hacks that people lay out step by step but if you start looking for entry-level work there's nothing about it how do you actually train people that's one of the
problems that i've realized in this industry is that there is no methodology for people to actually train or practice that that doesn't include hey your neighbor's got insecure wi-fi go up against them because they're not going to report you i've and i've actually had somebody say well why'd you build this you don't you don't need to do that especially when everybody's doing insecure stuff around you it's the principle of the thing this way well what happens if you actually have the one person who set up something that's actually a honeypot just to try and catch capture you just looking to see who's doing stuff just because they're bored and that's kind of their job so
that's part of one of the requirements for the actual range boxes i needed something that i owned something that was inexpensive that i could actually work with and that's part of the reason that i chose the pi as a platform i also needed something that i could see both sides of it so if i'm going against it from one aspect i still need to be able to get into it from the other side to see what's happening make changes tweak some things so that i'm actually aware of both sides of the platform and so as you see i've got part of the reason i was making it is just the lack of information the whole risk associated with
production systems and the fact that since it's my platform i can go in change things and i get to the point where all right i've done this enough times let me move on to something else let me remove this component drop in another one in place and it works if you're trying against a production system or somebody else's system that they actually own you don't have that freedom you can't alter it without them noticing under most circumstances now why a training platform i talked about the legal environment anybody who's been doing any sort of security research knows that it's a very very questionable area right now sometimes you get people that come after you just because of the terms of service
violation you end up with other things where where they're looking at it going well you've also violated this rule you violated that everybody's heard of the computer fraud and abuse act i'm assuming either that or you've all fallen asleep already so anyway but computer fraud and abuse act it's from 1986 it hasn't been updated to any it's gone through a couple of updates but it doesn't actually actively cover all of the things that we're doing now it was written for a much simpler technology time then you've got federal wiretap laws this is a wi-fi platform now google just recently lost one of their appeals and there's actually talk that from an article i found in
september where people are now considering a class action lawsuit against google if they can prove that their information was captured by their little the google maps camera cars so they tried to say that no we're just looking at this so we can enhance our maps but for the most part supreme court court of appeals we're saying no you intercepted protected communication without the other party knowing so now they're they ran afoul of wiretap legal issues then you've got individual state statutes that also help tie in with a lot of the wife the wiretap stuff some some places say as long as one party in the conversation recognizes that they're being reported you're okay others say
nobody at all so depending upon where you are you're going to run into different legal circumstances but one of the great things about it and eff actually makes this comment regularly you own it you opponent it's your device how can you violate the terms of service if you created the terms you set your own terms the other thing is this makes it very very easy to use the whole range box platform i've got it up on sourceforge right now you get in and i've got the image it's a four gig image all you have to do is download it unzip it write it to a just basically dd to a sd card plug it into your pi and you're good to
go as long as you've got the other components and i'll talk about the other components you need a little bit further on but one of the great things i did with this is i made it repeatable it's randomized every time it comes on it changes your wifi passcode so it's not like you're working with a a router or something where you have to go in and change your passcode every time you want something new because you're eventually going to get to the point where i remember why am i even going through all the hassle sure it's two minute process but even still why go through that hassle if you just want to get to the next step
so you get to the point where this forces you to do it it forces you to actively work at it the other thing i realized nobody had done this there was nothing out there that actually had a random wi-fi setting sure you had a couple of honey pots that would actually change some things on you but for the most part it wasn't something that would come up change your passcode and be stable long enough for you for you to use it and then change the next time you needed to use it so why the pie it's a very very powerful cheap platform right now you can get them for less than 30 bucks once you start adding in
additional components that's required to build the range box you're looking at 75 or less on average to actually build it so it's something that you can put put together for relatively inexpensive have quite a bit of power it's portable you can take it pretty much wherever you want to but the real reason i had it on hand i'm sure i could have built it on a desktop and then i would have lost the portability factor but i had a pie sitting in a box that i'd been waiting to use for like six months and i was like hey let's do this so what does it actually take to make the range box itself and one thing i
want to point out i have this nice shiny aluminum case the case itself cost me more than all of the other components combined it's a cnc milled aluminum case it's fantastic i beat the crap out of this box it lives in my and my bag i take it pretty much everywhere so i can just play with it when i get bored so you don't have to get the shiny case you don't even have to have a case at all because it is a pie if you're just going to keep it in the location it's something simple so don't assume that for this whole 75 price tag that i mentioned that you get the case as well
just wanted to clarify that but one of the things on it is for the pie you'll need a wi-fi dongle i am running just wep 104 right now so it's very very easy but again this is a training platform it's a practice so you have something that you can successfully get through there's more than enough talks that actually deal with wep and how to actually break web you can find tutorials all over the web on it once you actually try and get things to work on on that is a completely different story but so once you've got your wi-fi dongle then you actually need to turn it into a and to an access point we have host ap
you're also going to need a dhcp server on it just so that anybody that does connect if you're trying to use some of the advanced stuff on there because not only do i have the randomized web but i also have from owasp their matilda suite which is a host of vulnerable web apps uh yeah web applications and so that allows you to practice a whole bunch of different things your cross-site scripting sql injection a lot of these things that you hear about regularly so the lamp web server required to actually make some of this work so the key randomization code and one of the big problems was i had to do some system configuration changes to
actually get everything to play nice together now talking about the wi-fi dongles you need something that has master or ap mode compatibility i know the arthuris chipsets do that that's one that i personally like there are others that will work so on the device right now i'm using one of the small dongles i'll actually hold it up it's this one here this is a netgear n150 model number wna 11 yeah 1100 it's a personal preference but it's what i have everything set to work off of right now i haven't done a whole lot of other work i do have a micro usb that i've been told works i've messed with it a little bit however anything that's running the real
realtek chipset the 8188 cus needs heavy customization i know um i think it's 80 max actually did some work to be able to set the set that chipset into at into master mode but it required a specialized and customized version of host ap that i'm not running if there's enough interest in that i'm willing to help somebody actually get that set up but it's something i have not done yet because i only have one but i've got a system that works for me so it's something that i'm absolutely willing to help with if you're interested please talk to me after the fact so i mentioned about host ap hosting host ap is great because it's really really easy just
some mild configuration changes to actually get everything up and running there is a problem when you're trying to actually accomplish this it's designed for static configurations it's designed so that you turn it on you get the same thing every single time i didn't want to do that so i had to actually find a way to work around it one of the problems is that the config file doesn't actually accept any system variables so you can't tell it hey i want you to read devrandom and write it it won't let you do it you can't specify a key through that process so i actually had to find a way to get around these limitations created by the
config file so a couple of modifications writing some custom scripting that actually runs when it boots up is the way i got around it and so that's what i did so number one here is actually the point where i don't think any of you can actually see that so if you're interested i can pull it up a little bit a little bit later on but what it does it does a check it looks to see whether or not a config file already config file's there scrub it just dumps it then it actually builds a fresh config file so the second one is where it actually generates a key it's just a simple call to deverandum yes i know that it is not
actually a qualified random key generator but i'm not looking for something to provide security i'm looking for something i can break so i've had people ha ask that i've got heckled from a couple of people that have made comments about well it's not a secure key generator not the point the point is to be able to break it so three actually is where i start the whole creation of the file it's just a simply cat the rest of the information that's in the bottom of the file off to a config file so that it's there when it runs just real simple really crude fast code because i did this on a whim really so i just messed with
it for a little while and i got it to work i know that there are better ways to do it and that's actually one of the things i'm looking at doing later on and it's actually on my list of eventuals as i improve this and so arrow number four is just showing you where the key that was defined earlier gets written into the config and then processed i talked about having a dhcp server obviously it's going to be easier than doing a manual config every single time it makes it so that once somebody gets past your wep portion that they can then associate with the device and then be able to move on and do the
web-based aspect of it one of the things you have to do is you have to go through and make sure that you configure your dhcp so that's broadcasting on uh wlan zero if you don't actually do it it's going to try and put it out on the rj45 port on the pi and you'll never see anything and you'll beat your head against it for hours i'm not saying i actually did that but hey it happens just gotta make the other thing make sure you assign a subnet speaking from experience i yet again multiple hours lost because i forgot a few little tiny things i mentioned some of the challenges that were associated with actually pulling
this together boot order boot order is incredibly important in this aspect because you're trying to create a config file as it's come as it is being cr as it's booting plus by default all your demons load concurrently as you get into as you get into a specific run level you start seeing that your demons are running concurrently so i actually had to go through and force host ap and dhcp to wait until i'd actually created the config file so i actually had to create a make config daemon put it in there in the proper order so that it would read through and then come up otherwise i'd get dhcp failure i'd get host ap failure all of
these warnings and yet again going why did this happen next thing network traffic so it's great i got everything up and running i've got this i've got this broadcasting wi-fi id that's broadcasting in web but i'm not getting any packets one of the little things is if you don't have anything on the network to communicate it's not actually going to see anything so what i ended up having to do to actually get away from to get away with generating enough traffic so that i could go through the packet through the initialization vector generation process was i created a cron job that just sends out a ping every 15 seconds to a null address something that's not even
within the range that's offered by the dhcp so it's never going to find it it's just going to sit there and generate so it's got an art broadcast makes it really really easy to do an arc replay so once you actually start once you've actually got that traffic you can capture that and then move on now i also mentioned hey you can actually read this one so one of the other things that i mentioned was i set up the the timer on that so you can see i've got a five minute timer on there so every five minutes it shuts down brings it back up so i've seen i see a couple people that have got their laptops out i don't know
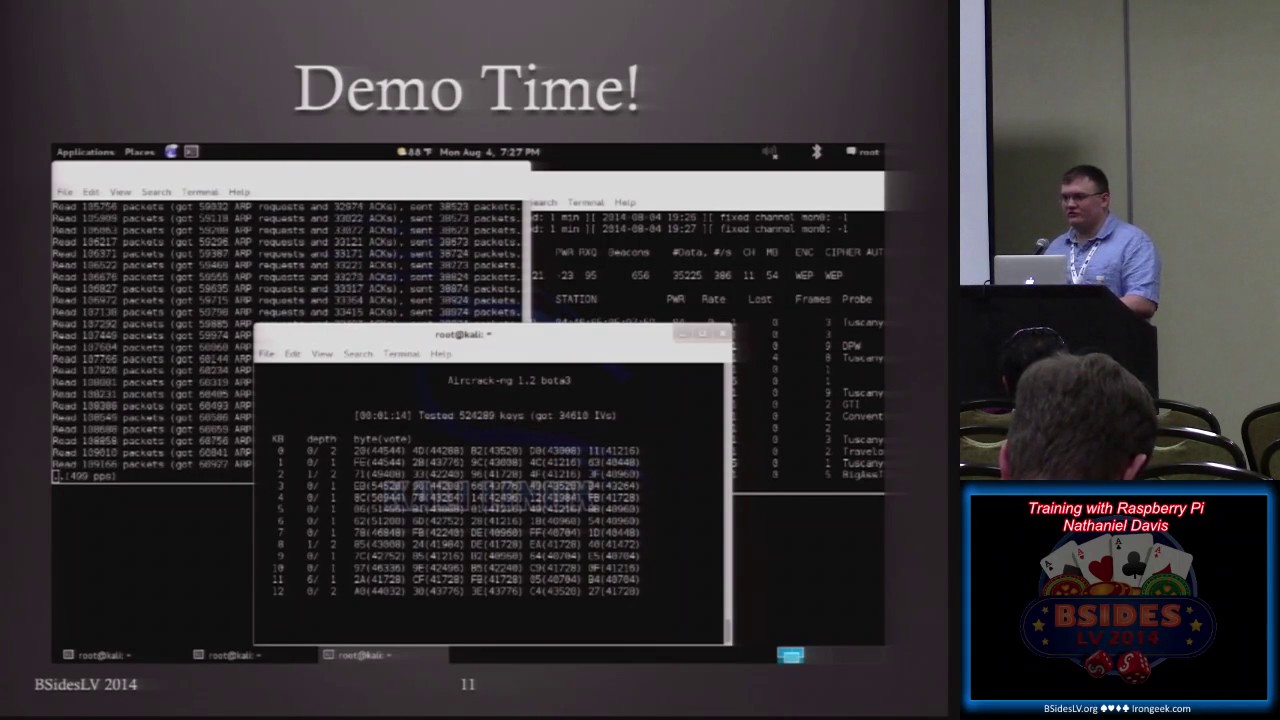
if you're actively working against what i've got or if you're just doing something additional but one thing to point out if you were actually trying to capture initialization vectors and you weren't paying attention when it shut down the key that you're trying to find will never actually be recovered because now you've got two sets of initialization vectors for two different pass keys that are causing problems so i've had enough problems with the demos in the past that i actually decided that i'm going to run a video because trying to do it live has gone sideways on me more times than i can count so i'm actually going to run this and i'm going to talk over it so
you can get an idea just to show you that it does in fact function it does work and i jumped ahead
so yeah i know everybody knows kali linux so i've got three different windows running here and so one of the things that i've done with it and so you've got i'm gonna work on my sizing on this stuff so you can see that i did it live i just recorded it didn't do a whole lot of editing so i'm just initializing my device to actually capture it that might work appreciate it so i've gone ahead and i've initialized it i've got it in monitor mode i'm using the so this is me actually going against the pi so i already started doing my art replay i've already started looking at the rest of it so this section here you
can see that it was actually monitoring at the time and the arp replay has started so i'm now going to go ahead and capture the information so it's going to take a little bit so now that i've actually got the initial effect initialization vectors coming in it's going to go ahead and run against it so i'm gonna keep talking about the pie itself because otherwise you're just gonna be staring at numbers moving on the screen and we spend most of our days staring at numbers moving on screens waiting on computers so i'm not gonna force you to actually just sit there in silence and watch this does not work so one of the big problems that i've one of
the big problems that i've encountered with this or one of the things i should point out about it is so most people expect wep to be fairly easily cracked i did say that this is wep 104 it's a longer key so it actually forces you to watch the process be aware of the process that's going on and some of the other things i wanted to talk about while it's going and you should see it in a minute or two where it's actually going to find the key not yet still early but some of the things that i'm looking at and some of the suggestions that have been made to me about this were hey this
is a great way to actually train people set it up in a classroom environment and one of the options to improve it that's been suggested is how about you actually start logging device association if you do that if you set this up in a classroom environment and you already log you have a log of your students and their mac addresses once a device is associated with it and you scrape that off and you keep that in a log file as an instructor you can monitor the fact that your student associated with that mac address or that machine that that student is working off of has successfully associated with a device which means that they've already
cracked the key so you can tell what aspect they're on what phase they're on and you can identify okay well this student's gotten it i've got this group of five over here that hasn't gotten it yet maybe something's going wrong and you get an idea of hey i need to target this particular group so that i can actually work with them a little bit more so it makes it really really easy to see what's going on a way to gauge it and that's the other reason for having a secondary method of getting in in this case i actually ssh into the box on a regular basis and just to mess with it through the back end rj45
i'm still not there still waiting so one of the other aspects with it as far as the whole training platform and i've got people messaging all kinds of fun stuff everything happens when you're live aha here we go so one of the things you'll notice i do have a key on that one and it is the that's the bravo 299 and so now i did tell you about ssh into the box earlier so this is me actually going back into the into the box one of the things i created just as a way to monitor and check it is the fact that as i have it right to a log file so every every pass key that i use
is in a log file and the most recent one is at the bottom of it this was originally written so that i could do a verification that the randomization was working and i could actually see what was happening on it so you can see here where it actually maps where it actually matches the the uh the key that was found when i was actually running the craft so if you actually get to once you get inside and you associate to it then you can actually get into omas matilla day and see some of the other stuff now one of the things i want to point out for those of you who actually if anybody was actually trying to do the challenge
i did flash up on the screen what i was looking for there is this fantastic image that is my where's waldo image and i was looking for somebody who was going to tell me that it was an epic waldo fail so we'll actually get to that further on it's actually hasn't there's a very funny story with it that i'm going to end on that that's associated with it so a couple of improvements something that i'm working on right now is wpa2 wpa so i'm actually trying to get away from wep but trying to set up a way to actually do it with either wpa2 or wpa so that what i'm looking at doing is grabbing from a
basically from a rainbow table doing a random grab line so that i've got something a known key that i can then drop in place writing that in place and then setting it up so that using two dongles in this case one as an access point one as a client have one broadcast out go through every couple minutes have it drop have it de-associate and then reassociate so that process that you can actually capture that initial handshake as is required to be able to break that one of the other things it's not platform specific it doesn't have to be and that's what i'm looking at doing is i'm actually looking at making it so that no reboot
is required like i said it was it was fast it was something i could do to make it work i'm now actually looking at cleaning it up turning it into a package that i can distribute as opposed to sending out the entire image because let's face it a lot of people don't want to pull down a i think the compressed size is a gig and a half that expands out into a 4 gig image file a lot of questions get asked why do you want to give me a full image because one i'm lazy and two i don't know enough about actually creating an application package at this time to be able to give you a simple package that
you can just run and it works i talked about device association logging as far as from an educational standpoint but even just being able to scrape that for other purposes allows you to turn it into a honeypot of sorts especially if i improve the code so that all it needs is a service restart as opposed to a platform restart so you get to the point where you can start using that as a honey pot monitoring what's going on see what people are throwing against it and if they break it okay you lost 75 as opposed to whatever production system that somebody may have been going against not a problem it's it's a marginal cost when you're talking at that level
but one of the things i wanted actually a couple things uh now about the epic waldo fail so there are two people in the back of the room so uh jackie and fun time and i and they're in the back corner chuckling their heads off right now who are part of the reason that i'm even up here because i was talking about this telling them what i've been working on and what was happening and their part they're the two people that for the most part helped push me forward to actually get up here and submit this information because they thought it was a good idea now we were out one evening and they were telling me about this race that
they had done and they're like there's no way you'd ever put me in a talk um right there guys so i just wanted to put that out there but there is the epic waldo fail mud splash fall on your butt and some happy cheers so now as far as as far as me you can find me on twitter at gither there's an email associated with this project the wi-fi range box at uh gmail and i've got the image location up on sourceforge i've gotten some feedback that says that image may be corrupted i need to verify that uh if you want to if you want to risk it and pull it down let me know but it's just the only problem
with it is it just didn't extract properly so if you're willing to do that let me know otherwise i'm open for questions really nobody all right so again so yeah i think it's i think it's a great thing and it's i hope i can actually get it out there for as a place for people who can be able to to work with it and learn from it because i know i had problems with it and i know i can't be the only one that has problems with this now did anybody actually try to go against the box did anybody mess with it you did any problems did you were you able to get in you couldn't get in
like i said it's a five minute thing so if you actually missed if you missed your time uh then you then yeah but if you want to stick around we've got i've got the room for like another 20 minutes so i can actually keep it up and i can talk to you a little bit about it but i'm actually done with as far as the presentation portion of this if you have any questions or you have anything else let me know if you're if you don't want to actually get up in front of the room or bring anything out oh i will definitely talk to you after the fact i'm gonna stick around for a
little bit appreciate it thank you very much
you