BSIDES Cape Town 2018 - Lightning talks - Let's Talk Implants - Dale Nunns
Show transcript [en]
this is going to be it's a lightning talk so it's gonna be a rather quick Who am I those who didn't see me earlier yeah I'm a software developed by day I jokingly am a hardware hacker part night and it appears sometimes I speak at K at B sites this isn't my day job why did I write is but anyway okay so why are we actually talking about implants for those of you who've avoided the news and in particular Twitter you may not have seen that so what this was was a bloomberg write-up they claimed that super micro motherboards had been backdoored with a hardway implant and the idea being that the story goes that
it was the Chinese some subcontractor to a subcontractor to a subcontractor of Super Micro so what they were doing the story goes anyway is they were actually taking the boards when they were being manufactured they were making some changes and they were putting a component it's very vague as to who was doing what and why and how but supposedly there was a component on there and suddenly these boards found lis ways into servers which found their ways into the story goes Amazon and Apple and all this kind of stuff and gave the Chinese access to service now everything was very vague no one knew anything and everyone went maybe I don't know kinda sorta a few a little while
later I think it was a week later so Bloomberg came up with a new version of it which was that someone else said no no no hang on the story wasn't quite right they modified the network sockets themselves and put something in there and that was intercepting traffic and that then was a backdoor into the servers and etc etc and this sort of story kind of blew up with depending on which side you won if you made money in hardware security and that kind of thing then obviously that everything was true and if you had no real interest in ear that well hang on this is all fake so the they were Twitter wars erupted over this and
very room everyone was angrily tweeting at everyone else as they usually do so what is a hard way implant so hardware implant in these cases most of the time is essentially just something that you stick on to the hardware a piece of hardware that allows you to either export rate your data out of the system through and non normal means or to override some part of the system it allows you a backdoor that you that isn't in software often without the software even knowing that backdoor exists a silly example of this is just like a mud ship on a games console that is essentially a hardware implant although you're not stealing any secrets out of the machine or anything like that
a lot of people seem to think this was near but Hardware implants aren't in the 1970s the Soviets put a what the back then was called a bug into typewriters which allowed them to actually transmit everything was typed on the US diplomats typewriters to a low van outside the embassy where they proceeded to capture all the information if you go back through various sites that's bunch of them where they all list all these kinds of things those kind of stuffs been done for years the catch is is that you did it for a small number of devices it was one country you know 20 typewriters a hundred typewriters in this office or that kind of thing then of course a
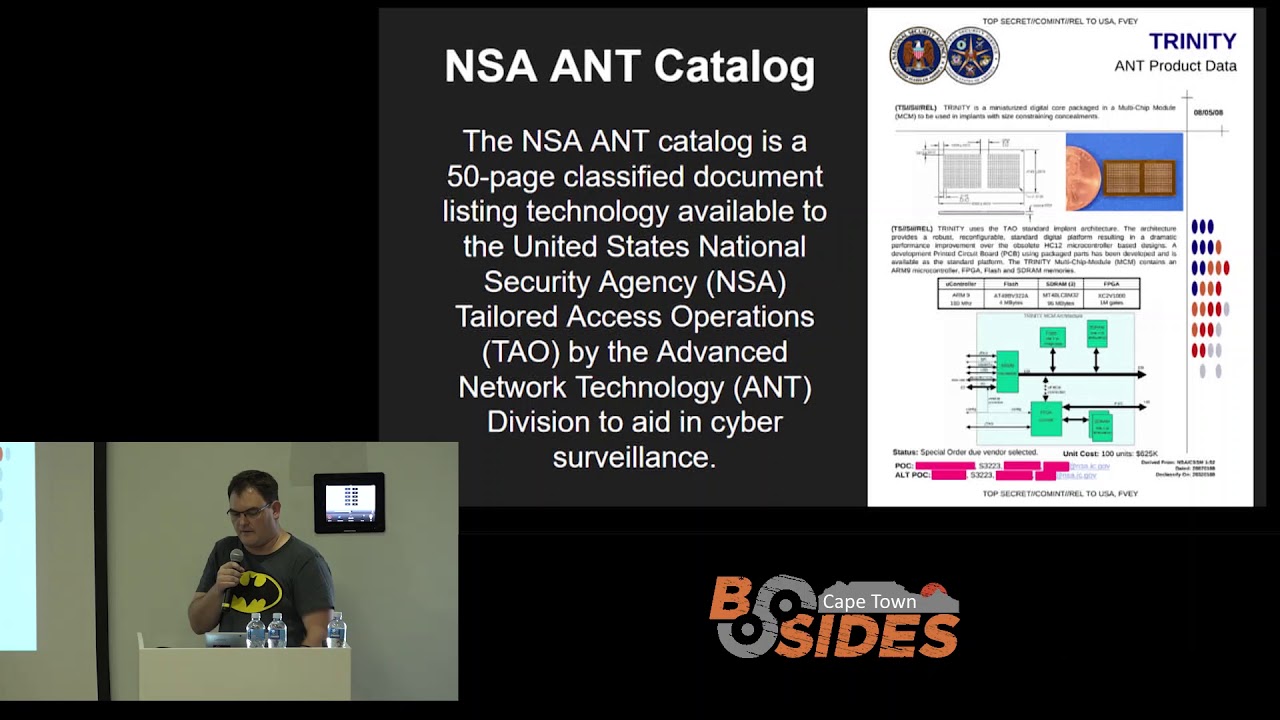
certain three-letter government agency went and accidentally left a few details on the internet or somewhere and this was late if you want an interesting read you can go in Google you'll find the PDF for this this is the NSA and catalog there's a few versions of it and a few other leaked ones this is an amazing read of absolutely crazy little hardware devices that all allow you remote access to things stream data out of weird high-speed Wi-Fi links and radio links bypass all kinds of protection and encryption and other things it's a very entertaining read the crazy thing is that this like Sonny showed people what you could do if money was no object you can make
things much smaller than people thought you could up until this kind of thing leaked everyone always said the argument was it costs too much we can't have something custom-built that's small to put into a device so back to the how does all this work so on the Bloomberg story this photo without the tags was actually in the the thing Hector Martin he's one of the guys he's famous for being a part of I think it's failed no fail over the guys who hacked the PlayStation but basically the you'll find is a couple of this Futter around what it is is if you looked at the photos and what Bloomberg we're talking about was there was a little chip
supposed implant their little six pin thing that was stuck on a board the theory that various security researchers came to was that if this was actually true what that little chip was doing was sitting in between a flash chip which had storage and this big chip here which is the BMC which is the board management controller which if you do anything with servers it's also referred to often as lights-out management basically it's the control of the server environment with win without the CPU knowing so through that you can turn things on and off and power things and monitor things temperatures and all those kind of stuff if you go and look this is otherwise known as sort of like the Swiss cheese
of the networking community I can't remember how many vulnerabilities they found in the various versions of this but I know I had to scroll quite a bit on the page it runs it depending on which board you've got it's got a 2.2 on some of them version Linux kernel with almost no patches applied and the story the idea being that oh it's it's closed no one goes and pokes around in that it's fine the interesting thing is is the BMC is plugged on to the various buses on your motherboard so it's got access to the network controllers it doesn't have direct access to your CPU or your RAM or stuff like that but it can do
interesting things to various bits of hardware so the Bloomberg story was okay some guy is in China and went and put a new chip on there modified the board layout had a space specifically made for this chip and we plunked this lordship on there now the problem with that is that's actually easy to spot if you modify the boards you will spot it during sort of like a visual inspection a lot of these companies actually have automated visual inspection their x-ray aboard they load the x-ray into a system and compares the image against the original and says there's a new Parcher who put that there so the correct way of doing this would be just to swap out
something like the flash chip with your own custom flash chip now if you've bought anything from China for cheap you will have seen this happen time and time again so what happens in China is you will get a chip it says ST micro on the outside and it's got a number on it and it should be that chip but it behaves slightly differently the reason for that is it's not an est microchip it's someone else's chip that they kind of this close stuck it in the same holder lasered the logo on the outside and it gets shipped now you could do the exact same thing for this you'd have a flash chip pertaining to be a flash chip and
it's not a flash chip so like you say if you're gonna read there's some very very interesting articles about this hector's written a bunch of stuff there's a few other people who've tweeted in that some of the backdoors are insane we were chatting about it earlier in the bedroom because people have suddenly discovered that the VGA connector is hooked up to the same bus that your network adapter runs on and your RAM runs on and your keyboard controller runs on and so what you can do is you can plug a VGA cable in talk to the i2c bus tell the bus to do something fancy to the network oh and inject these key presses on the keyboard
controller and and and and luckily it's only on certain motherboards or certain laptops and that kind of thing but like I say what happens is when these machines are bolt the guys they build them out so quickly and they forget to wire everything else so you don't really need a back door just change the flash put something in this story goes that people who have looked at this particular implant say what it's probably doing is just switching out the flash at certain times and boots a totally different flash the controller you don't know it's doing that so how do you fix this the big problem isn't its supply chain it's ways your machine Hardware being
built if your hardware is being built outside of your control you can't do anything about it the problem is is that when you move the manufacturing back to America which is the current orange president is planning to do it doesn't help because although the manufacturing is happening in America now all your chips come from China so okay we move the chip manufacturer back and then eventually you end up with all the manufacturing there and even then you still can't trust it the components arrive on a real it wouldn't be hard to pay one employee to switch out one reel and now you've got a broken other-- thing in your device you can encrypt everything you can do hardware
encryption stuff but again it's you can't talk to every chip on every device and authenticate every single transaction now this is becoming a bigger and bigger problem you'll see if you deal with US companies special governments and that's the government goes hang on these manufacturers we don't want any of these project products in our systems because they may or may not have backed or we're not quite sure but like you know our our three-letter agencies told us just avoid these guys we're not saying about changing it these are two parts they look identical on the right is a standard XO quad gate on the left is an eighty tiny eighty for those of you who know electronics will know
that's a microcontroller it runs code the cool thing is you won't be able to tell the difference if you just change the lettering on the outside between those two chips and you can make the left one do everything the right one so like I say you know how do you stop that kind of thing my favorite quote though was mine so everyone's going on about the fact that these backdoors are going to be you know serious problems security risk et cetera but like I say is often the hard way implants don't have access to the RAM and stuff like that so you can't get data necessarily out and that kind of thing so my argument is who cares about
getting data out let's just say that a third of some big cloud providers equipment has got my Hardware implant in and let's just say that all it can do is write to various flash chips on the board that's it and it happens to be able to see network traffic well then why Kahn ice puts on my special thing in there right zeros to everything when it sees a certain thing and shut down an entire cloud provider now if you think about it that's it's not particularly it wouldn't be particularly hard it's a once-off I nuke the US and that's about it I can only use this thing once but you only have to use it once so yeah
that's it [Applause]
yes yes yeah like I said there's a rabbit hole that so the only reason I'm doing this is because I got sucked into the rabbit hole of reading these things there's a group of people Hector and there's a few others Sutherland he did a talk and there's a few other guys security people who do some hardware stuff and basically if you get onto Twitter and you start looking and you'll just see them they'll tell mention talks and at one point I queued up I think it was 12 hours of just hardware security talks like this and that was just scratching the surface the the problem with the hardware security is you don't see it you can't test for it it's not
the normal kind of thing and people always ignore the hard way it's like oh no no we don't have to worry about that but like you say everything runs on top of these things they are all closed there is no code you can poke at sort of publicly available so yeah





