BG - The Badmin Project (Na-na-nanana Na-na-nanana BADMIN) - Gillis Jones
Show transcript [en]
all right so uh hi everyone um welcome to uh what I lovingly like to call the Badman project so Al there we go so um alternatively called badman yeah CU badman B Because badman space space Batman sound a lot ofik whatever I thought it was cute I'm Gillis uh for those of you who don't know me um I'm a ABC engineer over at white hat analyze uh around 4,000 sites weekly uh I've been in it for around 3 years or so and uh I was one of the first people to turn in a bug bounty on goog plus um and I've received uh quite a bit of money from the uh Facebook bug Bounty which is
Awesome by the way and if you don't play with it you should and I make developers sweat and not in the you know hey you're kind of sexy you know I'm getting turned on but you know in the holy you just broke my application I'm going to cry now this is who I work for um we do all kinds of softwares of service and
whatnot all right so first of all uh you you hear a silly name like badman what do you think you think you know holy crap someone came up with a horrible horrible catchphrase for a horrible horrible uh terminology well it means bad admin um and a bad admin is basically a web application developer who through either laziness or ignorance doesn't alter the uh default configuration of their CMS uh install now it can also be the actual cm M developer who you know how many of us actually think that including hard-coded pass like back door passwords into a uh into something that's used by millions and millions of people as a good idea it's an awesome idea huzzah all
right so if you include if you include hard code passwords into your CMS you automatically fail I'm sorry but you lose so much much respect um or you know hardcode fast phrases for administrative functionality is it really a problem now you you'd like to think that as an industry we've gotten the message across that at least at least you need to change the default file path for your logins for your admin logins no just just for slash admin an admin login.php there's over 10 million records on the internet that are indexable by Google this isn't C this isn't including customized strings such as you know SL peer SL renovatio or any any of these others uh unique names there are still
defaults now are these good targets now there's a lot of discussion of cyber war and all this other stuff but in State versus State uh Warfare this is the type of Recon you do you would do you know a search for a specific uh uh top level domain and with China uh there are somewhere around 2 Million results now a interesting fact anytime I search for this string Plus either CN orir China or Iran Google would automatically uh make me do a capture for any requests so it makes me wonder just as aside if there is a government agency out there doing massive amounts of searches for uh foreign targets so what can you get just through a
URL now a lot of us know this or at least I expect you do um but a lot of uh custo cms's they have uh unique admin logins so in this case um Pier has a specific default file path and parameter that's passed now if you can hit that you can pretty well identify the CMS even if they've changed uh the actual page that you that has returned when you visit there you can tell what it is same with renovatio and same with about 35% of the uh actual database you know they have uh either the CMS name or version number in the actual uh URL string now basically what this can do is allow
me as an attacker with absolutely no effort just going in and checking for a 200 response from your server for this specific uh URL string if I get 200 response I already know what you're running without having to do any work and that can allow me to find uh vulnerabilities that are absolutely specific to that framework now the project was born out of frustration with you know having to spend you know 45 minutes to an hour researching this you know on every single freaking pinest if you look back through uh some of the projects in the past 10 years there's been a lot of focus on Hardware passwords uh pheno Elite did an amazing amazing job
assembling a hardware password list um back in 20072 2008 it's still maintained and it's one of the most comprehensive out there that I've seen but there's no equivalent of that for web application security so I decided to um at least attempt to assemble something along the same lines um now where I work as the TRC the threat Research Center on average we spend 45 minutes to an hour and a half coming up with custom um uh attack vectors and I wanted to assemble all of that information in one easy to use place so that you could reduce the amount of time that you actually have to spend and invest in research by a factor of five
to six times so this is my project uh this is a little interface that I've come up with um you can see basically all of the uh individual cms's listed uh there's over 150 actual records in the database I had no freaking idea that there were this many cms's out there and each one of them has a unique configuration a unique uh attack method methodology associated with it and they're all uh alphabetical and whatnot because you know OCD and whatnot now there's the admin login URL uh and when I say that it this is where the attacker goes um by default to access the administrative login functionality so sometimes it's accessed by a specified Port but other times it
is uh it is just simply a resource uh parameter added onto the end of it now uh hippoc CMS for example uses uh you know if you just try to append SL CMS to the end of it typically it won't work however you have you if you append uh Port 880 to the end uh you get access to the admin uh login now occasionally um so with a uh with a CMS such as uh bricolage or Cascade you'll log in in the same spot as all the other users um now there's also the username password um what I've included is the uh username password combo of the highest privileged user um that is included by
default uh so that you can uh get the most access possible with the least amount of research required um and in rare cases uh if there are uh authentication bypasses available I include links to those so you don't have to worry about uh worry about actually authenticating you can just do whatever the hell you want now um I also include uh additional documentation so uh you have a easy one hit source of all of the uh all of the configuration options that are available to the administrators of the uh application and there's also the know exploits Link at the very bottom of the page um I've I've elected to use exploits download um because I also use
osvdb but um unfortunately it seems as if uh osvdb isn't as comprehensive with uh web application uh like cms's and whatnot which is unfortunate because they're the superior platform I'd like to see them go at least focus a little bit more on web applications and it's a good starting place to find uh weak spots in the actual coding of the application so even though uh certain vulnerabilities may have been patched you can see where the logical fallacies lie in the actual coding of the application is a developer lazy in their encoding methods you know do they not care about authentication are you able to supply your own cookies or whatever else now just a quick analysis of um some of
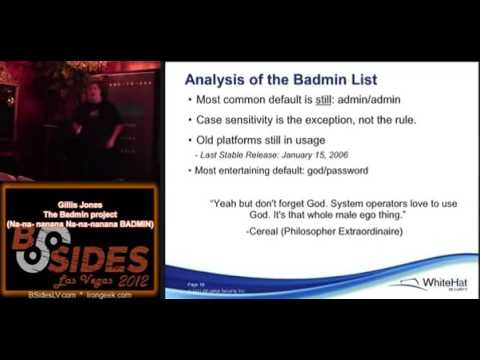
the records I was able to find um the most common default in 2012 is still admin admin case sensitivity that is the exception it is not the rule by any means um even applications that like to say that they are case sensitive uh often times you're able to uh completely reverse the uh case sensitivity set so say the first uh the first character is capitalized instead of doing that making it uh lower case and all the other characters uh capitalize so it's checking for the difference uh not the actual string um old platforms holy crap uh there there are uh platforms on the list which date back to 2001 they're not in wide usage but they are are still in
rather significant usage on the internet now of course the most entertaining default was God password this was from a uh CMS called PHP nuke or or PHP nuke from back in 2006 um that uh you know just like uh serial said you know there's something about ssops that just love to use God it's the whole you know default male ego thing all right so I've told you a little about a little bit about um the actual problem of you know default admin credentials on the internet but surely this can't be in like a wide attack Factor so the Utah uh Chief technical officer actually had to resign over this vulnerability there were 500,000 500,000 Social Security numbers
that were taking because of a single default password that allows you to reset admin passwords across the board on their Network um basically uh a crew out of Eastern Europe broke in and sold off all of the names and there was so much identity theft and basically their entire security team got canned uh and they H have they're having to build it from the ground up now that looks like something from the mid 90s doesn't it would you be surprised if I told you this was March of this year yeah um and the Verizon uh breach report uh states that about 44 to 50 uh 44% of their analyzed breaches uh could be attributed to uh
a lack of uh varied passwords and or easily guessable passwords now there's a distinct difference actually um in larger and smaller organizations um smaller ORS is 44 larger it drops down to nine I think this is rather easily attributable to uh smaller organizations not thinking they have the actual money to invest in security you know you're solely profit driven you're solely wanting to get bigger and you don't think about the security of the product and you know how much work does it take to change a password like all it takes is a decent mindset for [Music] security Now what can an attacker get with a default password this is from an actual test um a actual client site I can't say
any names and all of the data has been uh homogenized however let's walk through this real quick so these strings up here you'll notice uh removed a legal value now I was able to get to all of this through a basic authorization prompt with the default lowercase admin lowercase admin which brought me to a search server uh called Ultra seek and it's basically controlled uh 10 to 15 different SQL servers and any Associated Blacklist white List information uh regarding that now it tells you exactly what is on The Black List what characters what strings um what literal uh translations it's doing and it's useful uh if I'm an attacker and I don't just want to see what's on
your site I want to actually attack your user base this is what I'm going to use to actually refine my attack also gives me uh internal IP addresses so if I use this as a pivot point point I have all of your internal information that I need to launch an internal attack so in this case you have uh the address the DB name the uh the host name any Associated languages etc etc uh basically give me all your respects about your network setup also you go further down tells me exactly what server operating system you're running uh what patch version what uh let's see what patch version what distribution uh any distribution comments etc etc you can guess why that's
useful now also I get click history of all of your admins so guess what I can tell exactly when your admins log in I can tell when they want to patch I can tell when your admins were to obsessed with porn that they forgot that they had a uh uh server upgrade running and if they only log in twice a week guess when I'm not going to be attacking the site exactly uh also uh gave me uh internal file passs and uh the actual buffer size of the uh designated uh temporary storage as well as the actual directory listing of uh the internal file paths so I got to see exactly where they were storing
their temp files and you know usefully where I would need to break out of to get a directory traversal
attack this is where it gets fun so I of course I had to censor everything because they were client specific usernames however um needless to say I I was able to assign myself uh admin status over any of the designated SQL servers uh I was able to change passwords for any existing users I was able to remove access delete accounts all that fun stuff and here's the scary part this little uh web app had a power button see that down there that one little button allowed me to turn off all 15 SQL servers all 15 it actually executed a cut power command to their server cluster what the I'm sorry I'm sorry um it's not the
best idea in the world first of all if you're a web developer don't code in a power button no matter how useful it may seem unless you have a you know you require your admin to use actual gold flakes to execute the request if you find that technology please let me
know so also in addition to that I was able to disable um any and all controls that were uh actually protecting the site is a dis uh disable The Black List uh uh enable logging so in case you weren't aware um often times if a logging is enabled on a web application you can get remote file inclusion simply through URL tampering so if you're able to uh pollute the actual uh the actual log files that are being executed you're able to break out of the echo point and actually execute anything you want um so you're able to disable uh SQL injection protection uh enable directory traversal um allow attackers to access other default locations and uh
check this out down here that little string there called uh SSL keylist yeah that gave me the entire SSL key list SSL passwords um the SSL Port uh the email address of the CIS admin um and all kinds of other useful things oh is that a network user uh domain username why yes yes it is all right so the takeaway from this that I want you all to take is first of all change your freaking passwords it's not that hard second of all uh if you want uh to do a um actual uh a actual test with the uh stuff and the things and
whatnot it's uh wh hats.com Badman slbadhti6by
[Music]
XML form so you can actually import it into any tool that you want um and basically use it to do some very rudimentary fingerprinting of uh cms's nothing along the lines of Wordpress scan uh you know I haven't gotten into version information on the specific uh on the specific actual cms's but just to show you how it works real quick um scroll down and there's all of these different uh cms's uh and for example if you go to let's go to PHP slash you get the um you can get uh this is this is one where you can actually uh bypass the authentication but you'll see uh you click on it drops down uh you get the
admin login username password and in this this case the additional URL which is the actual authentication bypass for the application um get the comments uh sometimes um there will be uh proprietary encryption algorithms that uh use a static key in this case the site key uh that they use by default is uh PHP web blog and uh the exploits link which is uh the actual URL for any exploits and uh yeah if y'all have any questions or would like to talk to me or call me an I'll be around thank you





