Challenges of secure coding
Show transcript [en]
[Applause] so I hope you are not tired or I'm tired and thanks for still being here I'm Portuguese um but I work for a Dutch company the software improv group and the headphones off SI g I enhancer them so i'm gonna tell you about the company and what we do because they are sponsoring me to be here and my Italian Boston you want to go conference in Portugal and when you want to what you want to do there you have to justify the budget and the money you're spending so but this is a nice company and the things we do are very nice so basically what we do is we look at software and we measure a software
quality by helping people in growing their software quality so we have models based on the 20 50 10 ISO standard and among these models we look at the maintainability of the software in the long term but we also look at security reliability performance and other properties so we might with all these things and we give advice to to our clients basically we are um a consultancy company I'm not consultants to formally of the widest so let's see I'm researcher and I have a background on many things and nothing at the same time so i did a pc informal methods related with cryptography and then i'm working on security right now so this savita there's no no no direct a trail of my my
knowledge and I jump from you the different areas in same related areas at the same time so I want to know what you expect from this top you have any expectations so how many of you know what is a sequel injection how many of you did a sequel injection okay so this is very familiar to you I yes so this is what we do when we evaluate a software system I forgot to tell something we have a lot of software but we get from our clients is for school we have a huge database I cannot say that is the biggest in the base in the world will have a huge advance of proprietary software from our customers and what we do is to
look at the their software so as you know to develop secure software you have to be systematic and you have to follow some guidelines of secure software development and we start with trading so all the developers should be trained for secure coding and then when they start about developing a product they should start by finding the requirements what are the security requirements of my system then they started designed coding and then they need verify back to their software the the cooler they meant verifies the requirements that they initially part and something went wrong so when you deploy your software something is not right and you don't know why so that's where we help our clients
and they always come to earth like what did I do wrong where's my job but it is right so the question is oops where does it spell so this is my theory but maybe this is right so all the developers have a training are they are all trained and then they have to define disability requirements and what we usually find is the software needs to be secure what does that mean no one really knows then because of that so you say your software is to be secure okay they fail to identify the threats they're rid of their vulnerabilities and their risk so they cannot cannot mitigate their home abilities but they continue and they start
developing their software with a functionalities and then they need to do something because the software needs to be secure so what they do they build security has an overlay and they try to do tests or not so people usually fail in doing in testing security requirements they do proper unit testing of the functionalities not all the time but sometimes but for security we don't see any tested even fantastic some some of a cough of our clients don't know what fantastic so and this happens right so you are on the news you have data breach and you fail to be plan to deploy on time so she's just blah blah blah or it seems so but what do we do in the reality how do
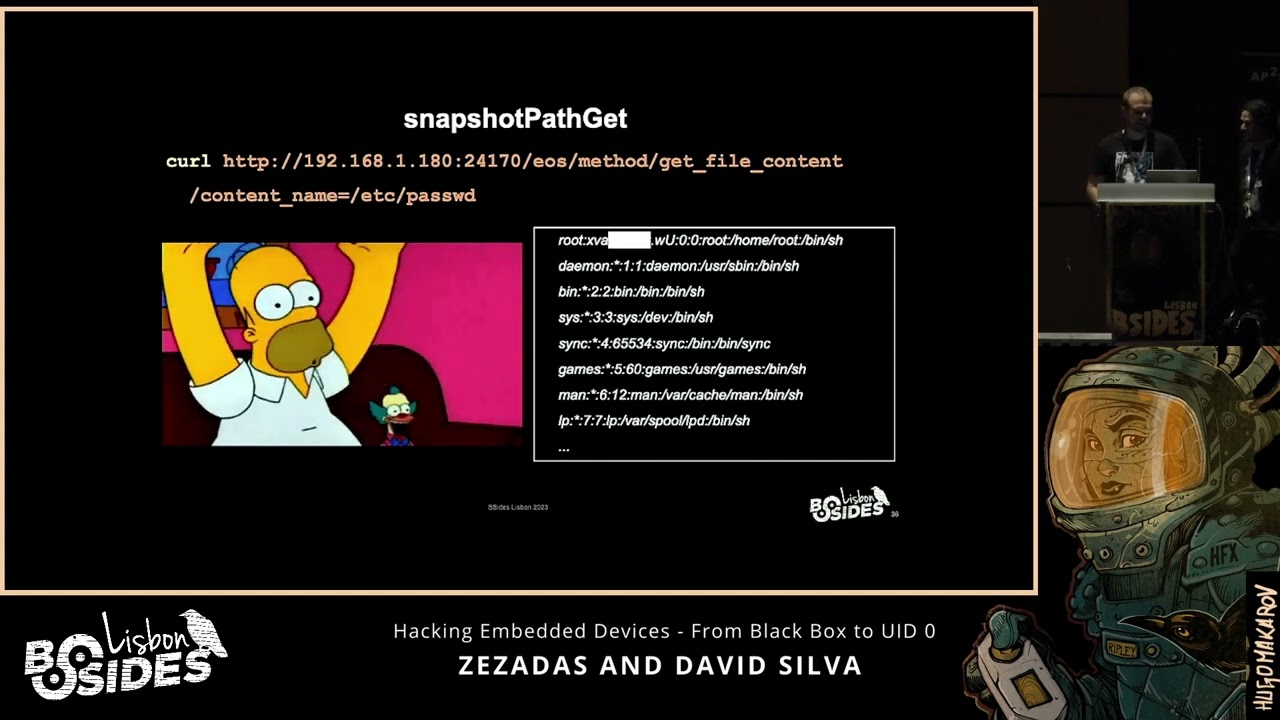
we help out so basically we get a lot of code we look at the code and we try to find the probabilities in the code it might seem easy but it's not because developers are really imaginative they come up with the most interesting things you can imagine and sometimes a very very hard task because frameworks are different so now there's a lot of height frameworks and you learn react everyone is different one and these things together together with the backend languages becomes complicated to analyze because they like to the treaty stuff and that's what I'm going to stop so what do we do when we do secure code reviews or software inspections hug so we asked for the requirements because
we look at the whole picture we don't look just a software to the software we need to look at the whole picture so we asked for the requirements the designer system we asked for source code we asked sometimes for demonstration of the system because we need to understand what is happening and we try to understand how is their secure development process but they don't get on the obvious information so we can always get a demo because the system works can we get the source code and get some information of the development process but that's all no requirements and no design for security so what we see in the code it's not just white it's not that it's
not that we don't see anything so we see good things so this is not a snuff that everyone does the same or there's like a hundred percent of people do exactly the same it's not true but we see some good things happening somos software developers know what I have to do some bad things and we see also some ugly so what do we often find has the best practice so everyone knows what is a sequel injection so everyone knows how to mitigate it so everyone is perimeter and squares but I believe that there's a reason behind it's not because they the developers you want to use to validate inputs to use brother / impress queries but because all the orem
frameworks that are provided nowadays to parameterize the queries the other thing we always see is that because they use these high frameworks nowadays and these front-end frameworks already have some embedded security we always see they take the front-end be validated so you can't do a cross-site scripting on the browser side you can't do certain attacks or on the browser side because these frameworks already provided some security they also implement authentication correctly and this is because this is a security requirement often so you want to improve login and password and there's mechanism to implement this in the in the correct way so they always using filters and this always works for that usually so now everyone knows that the
communication need to be secure so everyone uses https TLS 1.0 1.1 not always the right one but they try to protect their connections and they keep the Cyprus which that are the four point for the web server which sometimes we dangers so they use security framework so spring security Spring both security those used at least provide some additional security level or increased purity lo with lo efforts from the good side the developer site and they don't try to show exceptions directing to the user or they try to avoid it because they know that printing strike stack traces or in the accession directly on the on the browser it's a bad practice so they are going they are doing good stuff at
least the clients we have seen I'm not we have we haven't seen the whole world but there's things we don't find and these things are actually very easy to implement so it sounds weird but most of the times all the HTTP headers I think for some level security or make your application more robust are missing so cash control they don't they little to protect cash secure cookies there's no one there's the very few developers that actually use correct flats for for cookies so access control so everyone knows what application is so login and password and you block the user from entering and but about what about the permissions are you allowed to execute certain functionality
the system I not allowed so this a part is always very complicated implemented in a very other play and is sometimes done in the intern in the wrong part of the other of your system session tokens so they should use the default session manager of the framework we are using but sometimes they generate cookies that are based on on the on user data for instance it has the user name is extra cookie so log files they never contain the information that's necessary to form a proper audit operations and connections in the back end so everything is protected so your external network is secure connections but internal at work it's completely open and this is this this could be acceptable if your
users are not inside sitting at work so if you have everything in the same network and you don't protect the dimensions then it becomes a big problem so what we always see and this is a huge trend nowadays I don't know why it's hard coded passwords so everyone uses the same password all the time to encrypt the data and these passwords are sometimes in the clear in configuration files which is already a bad practice but sometimes you find them in the code so meaning when you patch this code the code goes with a password that was created by the developer and if you try to reverse-engineer this code you can easily see the password that it's easy
trick with the day what I think that we often see is that developers don't know how to use crypto levels and there are many reasons for these I believe the main reason is because crypto is hard and there's no guidelines on how to use a problem cultural to properly use a crypto library and I'm not going to continue but what we see is that most of the home abilities of software of the car of our customers it's because the live is a use have vulnerabilities so you cannot build a secure software without checking the New York dependencies if you're the practices are vulnerable or not so one of the things I think it's very very
critical it's the access control problem that exists in software in the software systems and the reason that I believe that so many are there there are so many problems with permissions and checking permissions in a system is because they don't centralized at the access control and they don't define it in the requirements face so this all starts in the beginning so that's why I showed the development rescue development life cycle because if you don't develop in the beginning in the ill don't start developing the beginning right way then you will never feel from implements your software in the right way and we are but we see sometimes so you see customers implementing access control policies on
the front end application so on the browser side and this is very nice but what happens is most of the applications nowadays expose arresting here in the background and if you don't protect your recipe I you can easily bypass all about precision magni besides that loading all the content to the browser leads a lot to a lot of little breaches so but nothing we are always see is mixing development code with production code so the production code that is fast that is released has a lot of developmental and this is a good way of introducing a vectorial system so you remember the goal to go to maybe this is an example of what happened there and
we see a lot of misconfigurations resulting from development code that is embedded in production code and but we always advise is a bit cleaner code is a fur coat so
how comfortable are you with crypto I knew like that guy that is gonna run away so the Credo the crypto kudos a problem in the development in a real enterprise software and back in two thousand six crease and I mean his vice president of very cold nowadays identified some mental mistakes and presented the talk explaining how he could use the script on States to exploit the software then one of the things that he mentioned is that on that time 2006 Oh ten years ago there were a lot of homegrown algorithms so people instead of using the standard algorithms for quick though they were implementing their phone and of course this security by obscurity is not
security at all so the other thing that he pointed out is you could be using a block cipher but with insecure walls of operations also there was some kiss porky selection and the key length was not big enough and it was we used a random number generation was never used or it was eased in an improper way and the the current use of the crypto API was not being before whoever see over this ten year so in 2006 i was even not finished I didn't finish even my bachelor so I didn't really know about free go at a time and what I see that happen in ten years in the enterprise world is that most of the developers
don't use homegrown ographers and they use recommend alanis but everything else remains the same so we still see a lot of incorrect usage of crypto and the question is where does problem line like what's the problem not developing your software then some I believe that sometimes when you train the developers the training is not effective so you go to a training off to one week you have little bit promised cured you have no background of pickles and you have to become an expert after one week on security and on some fella p series of secure software that doesn't work very well yes security is very difficult concept to grasp so developers are in the dark the con CNT
they try to do things but sometimes it's hard so they try their best but they fail because it's hard to understand and the other thing we see is that there's no requirement so defining that assist the system is secure is not a requirement you have specified one d150 to a force what is the security requirements of your system and because of these so they don't have any clue most developers go to very well-known forums and try to understand how to vote in script oh how to implement a security in their software and then these forums sometimes or most of times a lot of insecure examples but because you don't know how it's what's the correct way you cannot judge whether
it's insecure or not and the other thing is this crypto these the frameworks and lie means that you see that I used that nowadays have a lot of embedded security sometimes I have the defaults have defaulted are not secure at least that many reasons for that but I think this is a big problem because if you tell a developer use this library your software is going to be secure if you do these things and east but you don't change the default then you have a problem and developers don't read the documentation or sometimes the commutation of the libraries is not available or it's not clear enough so if we go back to the beginning I
think the problem fails in the beginning when you know when you will have training but when you try to start a value system and when you define requirements and design so you don't define the requirements then you can never identify threats and vulnerabilities so you can never be together and then when you try to deploy a system or to verify justice system before the deployment you have to test it and when we see is so skype analysis and dynamic analysis are rarely introduced in the pipeline of the development of a system only the the company have is a big company and have a very mature software a secure software development and sometimes clients don't know what
pentesting is which is be dangerous because we think come on how come you don't know what is all what you need to do to improve your system security so that's it um I promise to be short I don't have that many things to say I just wanted to present the ideas because I was sponsored to come here and
what we do is look at software so we wrote a book about building maintainable software so we have 10 guidelines on how to write software and i only have three copies on in c-sharp so if you want a coffee you can take it afterwards but you can also hear omni hub and you want to be to have your coat check for d steyn guidelines it's free and you can use the better code hub which is a platform that tells you how mundane of all it's just awkward it's not free for enterprise software but if you have a an open soft an open source software you can use this so i [Applause]
guess it so do you model as part of your program ready we so we also we'd also do a threat modeling is part of the analysis development but what we mostly do is the code review because by the time we get the client the client already has a system that is being developed they want the client one stupendous system but they want to know what are the inside of the system or the client has another external company so I developing the system and they don't know how the system is being developed so most of the time schedule secure or reviews but we also do some some threat modeling analysis for good you find it link on stuff on a
curve how do you communicate that your comments on terms what's the workflow anything knowledge we take a lot of screenshots and we talked to the developer directly and we tell them so you did this wrong did you say no like you know this is wrong you see it's not a bad price they say okay but I don't see the problem so the problem here is to explain the developers or after afterwards the management how what is the impact oslet for mobility in their system and the you can say oh you don't have the HTTP all their HP has it you should have me stay and Wyoming so you have to explain what are they in
fact the possible attacks if you see them the most difficult thing afterwards because not everyone understands easily how what the impact of the vulnerabilities in their system so you just don't make any kind of exploitation or something like that you just shut up this is where no we are not pastors so we checked security but in time and some easy Nile from developers easy like when you show page program you let students but for that we would have with me that infrastructure we could make attacks in fantastic so we usually we get to the source code we don't we don't say think that you don't develop an apartment so how do you how do you guys how do you
guys tackle things like race conditions and and all the ghost was about that usually hard to track and hard to explain because i worked in development for eight years and every time i had to explain some junior what a race condition was and how the hell someone could lift money from the website without doing in the second act of him he went nuts but i lost four years for all of my life so our our made and so we don't fray sister look for buffer overflows in the code that is a frenetic use diagnosis if the client asked for what we do is the we try to to check whether the development team performs a
secure development from the beginning of the system so we advise on how to build the the right thing and not not particularly but particular plans of the system we can detect it but that would make our analysis much more expensive sometimes we do that if you have unlimited time to look at the system and try to break all the doors but that's not what we do we were more practical and we try to identify threats on high level and Alan and tell them you have to take this into a conference or authorization they have to do the test not us so afterwards in two apprentices and what happens most of the times that the pen test text alerts that we detect but
they can't see the inside so the Fed s more um more black box next week thanks for thank you so one of the one of the problems that you identified in the process was the requirements specification what are the deliverables are how do you define the security requirements because that's really hard right that's really hard on the system so you started you should start your fat modeling so you should started you can use try ah so better than the holomap biology to identify price in the system and then and you identify how to mitigate this these threats so so approximate those there are classes of potential problems like in fertilization so what we smooth there exactly so our models will have a
model we are not doing this so we don't come up with the ideas of nowhere so they have a model where we have guidelines of secure development and we check these guidelines you Colbie and once again that's not the specification for the requirement that's what that's what that's what I'll be Wireless input validations environment of the system for instance it's a high level requirement that can we stayed up a different types of survival
[Applause]