Exploits in Wetware: Defcon SE CTF Experience

Show transcript [en]
what are some of the types of social engineering attacks that we've seen so you've seen all the traditional attacks right you've seen the impersonation tailgating tailgating is still a problem today right we haven't fixed that problem yet shoulders surf reading dumpster diving and then some of the stuff we see more today right the fishing machines machine anything that ends with ing basically and then you know I did my own little branding here I don't know why it's doing that it is yeah I'll push on my connections and see if that helps at all I got a lot of connections up here
well if you could see that that would say you know it's my special branding for what we're gonna expect in the future and you're seeing some of this already and one of the things is social media impersonation so we're seeing the bad guys are out there they're creating Twitter accounts and you know you go to a company maybe you experienced some poor customer service and you're in the lineup for an hour and you tweet to them you say hey this is no good I really don't like this you get a tweet back from who you think is them and they say hey no problem just send us your account name and we'll give you a credit and so
they start harvesting your credentials so they're really setting up fake accounts in the anticipation to to get that customer service interaction software-as-a-service for se everybody else is doing it you can get dial of service attacks now as a service so we're really going to start to see that ramped up I would expect on the private side we see that already on the nation-state side you've seen the 50 cent army in China and in every other country really gravitating in that direction and you know I think you'll see that more and more in the private space as well virtual kidnapping so where your accounts get taken over and there could be various ways to monetize that maybe
they're just going to held you for ransom one of the areas that I think you're really going to see huge developments is whaling and the reason I say that is because this is these attacks now have moved for you know it's cool to do this I can tell my friends I did it now it's monetized this big business now right so who holds the money while your executives right so they have the authority to transfer large sums of money so there are gonna be really bigger targets and I think there'll be a lot more effort put into that so what's the origin story for this social engineering stuff right it's it didn't just occur it's not a new thing
I'm pretty sure the people who built the pyramids you know I think they're pretty good at social engineering if you want a crash course in social engineering just walk oh no a used-car lot and and wait and see what happens and that experience is pretty interesting right you'll have someone come up to you and they'll go through this certain script and it won't be oh what kind of car would you like to buy it'll really be how much money do you have to spend right and so it's it's a very interesting approach they're not concerned about giving you the best car they want to extract as much funds as much money out of you as possible and
give you the least value in most cases I love doing that I love talking to those guys so why should we care about social engineering what's the big deal so read the this charts taken right out of it that's really distracting I'm glad I'm not looking at that come on I got to give you something
hello okay don't touch it all right so please say so yeah the Verizon report so this is a chart and I like to look at charts and I think of charts as stocks basically and I extrapolated this this is not what it's really gonna look like over several years but just for visibility you know if we take a look at this social engineering right that's the superhot stock right now if this was a stock you'd want to buy it we compare that to some other things right we see that the physical right that's doing pretty good probably an ETF maybe not a big dividend right but you know it's still not bad not as good as social you
know and then malware that's probably bonds it's leveled off a little bit and then what they refer to is hacking I don't remember the definition it's kind of generic that's the stock that your friend recommended which is never a good idea right so you just look at that and vendors are saying well it's going up by 20% whatever that percentage is you could just eyeball that and you can say that's pretty steep right and when whatever attacks you're looking at most of them have started off at least as a social engineering attack whether it be fishing or fishing or whatever it was right so it's usually and especially the oesn't is usually that first stage of an attack
if you see people looking at all your stuff doing Osen well that next step is probably going to be something a little more serious so that's why we should care the OSI model I always like to poke fun at the OSI model any of you have done an exam lately you're probably pretty familiar with this we don't typically look at it on a day-to-day level but the interesting thing is it only focuses on the technical right so the joke is let's add that user layer on top of that because I'm not gonna spend a ton of time trying to hack your firewall if all I have to do is phone your user base and say hey what's your password and they
will give it to me right so five minutes later all right so kevin Mitnick had the pleasure of meeting him in Vegas this year amazing person his books are fantastic you know he had this great quote the weakest link in the security chain is the human element I believe in that personally after my experience is there anybody in the room or do you all feel that maybe that's not the case do you think that maybe social engineering is really not that big of a deal not that big of a threat are we drinking the kool-aid yeah okay do you want to do a quick demo to see if you could be socially engineered yeah it's worth the time two minutes okay so
let's do a trick real quick this is a cheap trick you will not like me afterwards especially if I trick you so you know full disclosure okay so let's do something real quick let's pretend we're a company we're all working in some big company we're awesome we're making widgets and I'm the info SEC persons just one of me so I'm just full out and I got to do some policy on stuff you shouldn't be doing so my executives said they're sick and tired are you doing this thing like I'll say something easy like let's say hand flipping right you're not allowed to hand flip hand flip is a fireable offense okay everybody got that don't flip your hands okay don't do that
I'll gonna do something like dancing but I don't think anybody you're gonna want to dance so so no hand flipping that's the rule it's in policy okay you've all read the policy of course right because everybody reads all the policies okay so let's do this all right and I need full participation for this okay let's put your hands out in front of you like zombies yeah thank you very much I appreciate that okay so we're gonna start with our hands up okay busted see I told you I told you it was a cheap trick but that's basically how social engineering works right like you're told not to do something and then I kind of put you in this weird position you know
where you do it right maybe not the best example but it just kind of shows that everybody can be socially engineered everybody ends up clicking on that link and those emails are not even that good yet wait til they're good right they're getting better for sure so I'm sorry okay I'm sorry about everybody has that different look at this point in the presentation I'm sorry that idea I ripped off from somebody so if anybody remembers where I got that idea from I've tweaked it a little bit I think I've made it better but let me know because I have no idea where that's from so if you're still doubt the power of social engineer and just go google it
right most of most attacks start at that place either OSINT or pho NSC all right so a little bit about DEFCON who's been to DEFCON holy smokes okay who wants to go to DEFCON okay good I was really hoping there'd be as many hands on the second round they're good okay so I've been at DEFCON twice first year I went there you know you buy your ticket for blackhat if you're going through a company and you could get kind of DEFCON on the side and you avoid the lineup and it's kind of like you know when I first did that it's like okay well I'm a good blackhat and then oh yeah maybe I'll go to DEFCON so
I I went through the first year and you come out of blackhat and it's you know you wake up you go have breakfast you go to some talks you have a lunch you go to some talks you go and party and then you just rinse and repeat right DEFCON is not like that they don't have lunch right so no one's holding your hand no one's going over this way sir right it's really you just do whatever you want to do there's talk so you can go out in the desert and shoot guns there's the villages CTF there's whatever you want to do so it's really whatever you want to make of it people call it a conference I don't think it's
really a conference anymore I think it's a series of conferences and a whole bunch of other stuff and you know I got the feeling when I was there it's more like Burning Man and in a conference right if you read the ten principles of Burning Man you kind of understand what I'm talking about but definitely worth your time it's a couple hundred bucks great value but it's whatever you make of it I brought a guy from work this year he went there different experience because he didn't really know what to expect and it can be a little bit overwhelming so if you're gonna go kind of plan what you want to do so I saw the su village when
I was there I spent a few minutes at every every little stationed at every CTF or every village and I went in there and saw these people phoning these companies phoning actual companies and getting points so well that's pretty cool I'd love to do that so I thought okay well I'll apply for that right that's gonna be my plan of attack for this year I'm gonna apply but hundreds of people apply so how am I going to get in there well and they're the people that apply are really skilled there's a lot of talented people at Def Con how am I gonna get in there so I thought well okay I'll make an interesting video right and like
everybody life gets in the way I didn't have a lot of time so I made a video I don't know if I'd call it interesting it was really creepy you can go and watch it it's not great it's just really spooky crazy weird but I get I guess that's what they were looking for because they said yeah Rob come on in so that was good for about five minutes I was pretty excited and then I realized holy crap I'm gonna be in a room in front of hundreds of people for 20 minutes and I have to perform so goodbye weakens weekends and evenings I spent about a hundred hours prepping for this which sounds ridiculous and I
guess it was it was quite addictive I was a total novice so some of the areas for me that burned a lot of time was how do I collect data how do I store data how do I organize this data because if you have a thousand data points and you're trying to make sense that and you're not really used to doing that it takes a bit of time to do that so so that was interesting I learned a ton so if you want to learn if you wanna go take a course or something and and get a crash course in any of these areas things like this at these conferences the CTFs are a great way to do that I
can't emphasize that enough so the CTF is basically two stages you have your first stage which is three weeks at home in your pajamas doing OSINT there are sixteen people that could participate so 16 competitors and you start following them on Twitter looking at what they're doing everybody has their own target so what's a real company and it's part of a common industry so this year it was the gaming industry and which was cool because I have some of the games of the company that I targeted which made me feel a little bit weird but but it was alright I got to know them really well and you have 29 flags to capture and work different points
depending on the quality of the flag so what's your SSID is worth more than oh how long have you been working for the company no engagement so you're allowed to phone the company but I'm not allowed to talk to them so I just can confirm the phone number works and that's really prepping me for stage 2 which is your 20 minutes phishing live at DEFCON and there's echoes over two days they're gonna either go to Friday or Saturday and the winner really is the one that captures the most flags or the most points hence CTF so you can get the same points that you collected during the OSINT and you but for the vision you can
get up multiple times depending on how many people you phone so if iPhone person a and get all the flags that can then do the same thing on person B not person number letter but anyway so you can repeat it over and over again and some people just go for the big flags like please go to this website and they just keep doing that over and over again all right this is the flags I don't expect you to be able to read that but basically there's things like you know do you have a cafeteria what's your VPN janitorial service OS 10 year how long have you worked there for so those are some of the common ones
then starting my OSINT because it's a corporation LinkedIn was your my friend right it's just amazing how much you can just collect from that alone for individuals you want to go a little bit differently but since my target was corporate great starting point because not only is it very well laid out but they've given me some really key indicators right tenure what they specialize in what department they're in so you can start to kind of group those departments I had multiple offices and locations so I could find out what location these people were in then also there's links to their other social media which is great too I don't even have to go hunting for it right it's all there with
LinkedIn if you send me an invite on LinkedIn say hey Rob can you join my LinkedIn I will accept why because it just expands my search range right which is which is fantastic LinkedIn will try to make you buy a membership at some point and as you limit out your search capabilities on there and you could do that I was determined not to do that so there's a tool called Linkedin x-ray which is a great tool and it will allow you to kind of search the whole area get much wider results without having to pay so I'd highly recommend you take a look at that so once you're going through the company you're gonna get a lot of people that
you could go deep on kind of the 8020 rule of course though it 20% of those people are gonna be the social butterflies that are gonna put everything out on the internet right they're gonna be putting your VPN information out there so really I focused on those people and also their friends because they go out with their friends and their friends takes pictures of of their stuff right of their laptop and things like that so really focusing on that go into their personal websites which were just fantastic they'd have their resume you know home home address cell phone number what technologies they use so that was really really helpful as well so you don't want to look at
everybody because that'll just burn way too much time so I was a novice when I started this I'm you know I still classify myself as a novice compared to many of you but so when I was out there doing my OSINT hunting these people unlinked in you know when someone looks at your profile you you wonder who was that why are they looking at my profile so then you go and look at their profile well if you do that to a few hundred people and they all start looking at your profile so I noticed that after about a week into it in which which point it was too late so then I was like oh dear that could go really bad right
because all I have to do is say hey did rob say look at your profile yeah he looked at my - and then you know could be game over there so many of you probably already have some of these solutions in place if you're doing this professionally there's a lot of options to give you a little more privacy but yeah don't make the mistake that I made all right so pretext development and pretext is really kind of your story that you're going with so to develop those talking to a lot of people over beers hey would you believe me if I did this or said this so I got rid of a lot of pretext through that because at first
you're like okay I'm sneaky I'm gonna have a really sophisticated pretext right it's gonna have all these bells and whistles and no get rid of those right just super simple as simple as possible I started talking to receptionists receptionist's are golden for this right because they probably have kids so they're used to you know that sort of stuff they used to say no very politely they're usually super professional because they deal with cold calls all day long right and so they were fantastic I spent hours talking to receptionist's you know at the end I was so happy I was buying them chocolate just for all their help and really your receptionist's are are kind of your
firewall to your organization right as far as se attacks so I was really happy to develop those relationships even more but a lot of my pretexts were vetted through them and when i went to vegas they you know the they really helped me to make sure that I had ones that worked so so then you're going to Vegas and if you haven't been DEFCON before some some ideas you might want to think about I choose not to stay in the hotel that's hosting Def Con this year it was Caesars they just changed I can't imagine you know people that are showing up to Vegas you know that the sweet couple you know the in their 60s they come in and they
don't know that there's three security conventions going on at that time and they've got their laptop with them you know I just feel so bad I actually talked to one couple I said hey by the way you may will not want to get on the Wi-Fi why and then I started to tell them and they just kind of slowly moved away from me so you know I tried right so you know just you may want to figure out where you're gonna stay there's the three conferences right besides the black hat and DEF CON and you might want to go to all three or one and but you got to figure out where you're gonna stay so that's always a challenge
comfortable shoes so Vegas is brutal that way right I was doing 10,000 at least sometimes towards 20,000 steps per day everything is through the casino right so bathroom food whatever you want to do is through the casino so you're doing a lot a lot of walking famous Def Con real rights so three hours of sleep two meals a day and one shower you know it's a room like this but even more packed sometimes so there's a level of stinkiness involved sometimes so they ask you to do the hygiene part of it so how did I prioritize my marks right then this is an important part right you're gonna have a lot of people to choose from when you're there I only had
20 minutes and real attackers are gonna think pretty similar to this right they have a their they have a business that they're running so they don't a waste time right there they have a lot of things to do they want to get points that you want to score right so same with me so I took a look and I developed kind of an algorithm for my marks I wanted like low connection scores on LinkedIn because that was gonna tell me that this person's not really well-connected they probably don't know a lot of people in the organization and they probably don't know the industry that well either so they're not going to be able to go
tell somebody hey this weird guy's calling me um very easily right so that's what I'm looking for they're not gonna know what normal looks like probably rights so this seems kind of weird they may not detect that then the next thing is I'm looking for people that will actually talk to me because it's no good if I phone you and you're not gonna tell anybody but you're also not gonna talk to me so I need somebody who is expressive so those if you're taking a lot of selfies and stuff like that you know I'm going after you and in your ability to share so if you posted the VPN configuration on your Facebook then yeah I'm putting your name down on
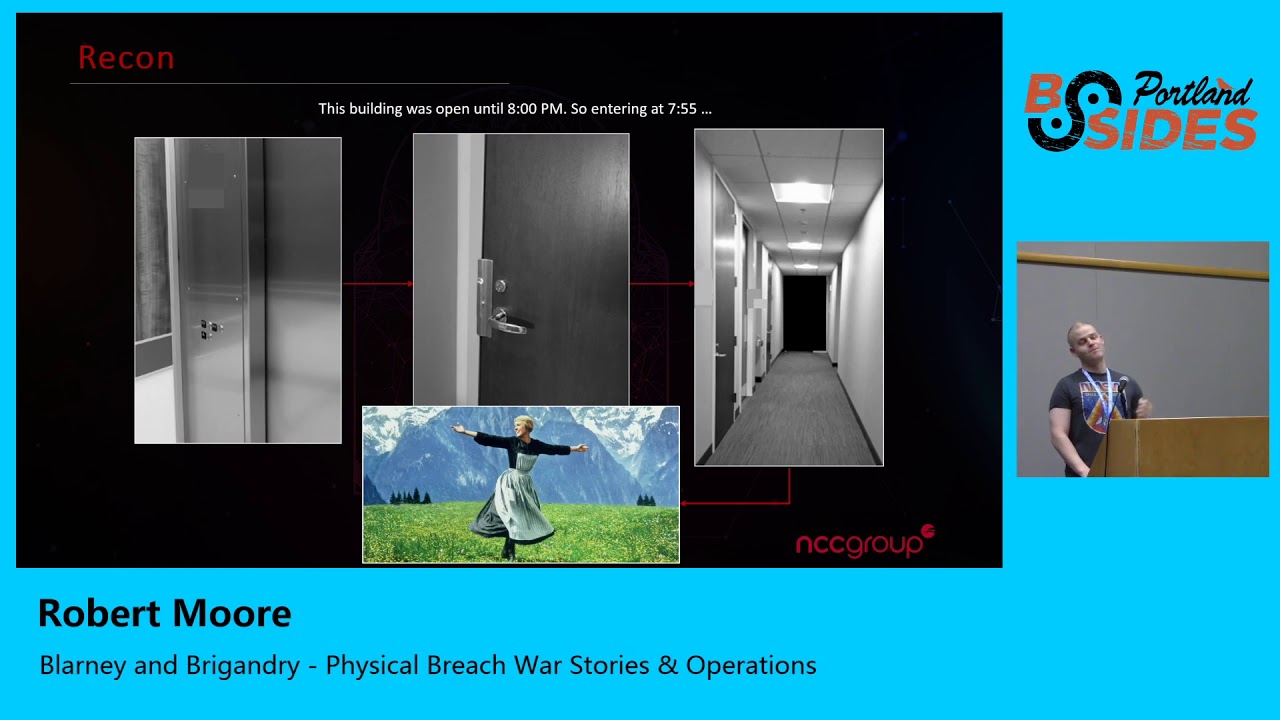
my list right so basically high charisma low wisdom scores which actually quite often translates into interns and contractors and you know I think that it's part of the transient transient nature of their business but but that's pretty much who I was targeting that's what the room looks like and I just thought I'd show you this in case you're planning to do this it's really exciting being in the booth and when you're in there like any high-pressure situation you realize that sophistication and complexity is your enemy and it you just kind of domed out things down it's like okay this this is simple and it's gonna work and I highly recommend that sort of strategy and
you'll see attackers do that too right there their attacks are pretty pretty straightforward and pretty simple in the booth the clocks the enemy right so as you're dialing that takes time voicemail takes time no answers take time so that killed 10 minutes of my time right off the bat and so I fell down to my sure bets which was reception so I there was a couple different offices reception at both of them so I spent my time talking to them some other people had more sophisticated pretexts where they would talk for a couple minutes to introduce themselves and to talk about why they needed your information and those were doomed to failure because it gives the
the mark more time to think about it right does this is a sounding normal is this weird should I ask questions right so I find good attacks are quick and concise and direct unbelievable right so you want to have something that that sounds legit but don't waste any time on any fluff right you want to really boil it down some some of the general rules right so pictures were okay but no video because they were worried about the audio you in the state of Nevada you have to actually tell the person on the other side of the phone that you're recording and that really would have kind of given it all away and even though the booth is
soundproof you know you can actually hear the audience so they try to make you stay quiet until it's over and then if you do really well everybody jumps up in screams and yells and shouts which is pretty cool so now we're gonna get into some of the more interesting stuff some of the tricks that I used and some of the tricks you'll see attackers use the spirit of the SCC TF is really to not victimize the person so a lot of my tricks were really focused on the good side right the you know making people feel good as I'm tricking them as opposed to the more aggressive intimidation approaches that you'll see real attackers using I think they could
do better if they use some of the softer approaches actually but they I think for them it's more of a time thing so the first one is the confirmation if I know you're using Dell laptops based on my own scent I'm not going to ask you if you're using them I want to build that we poor by saying well how do you like them right and then in your mind you're saying well okay he knows I have them so that kind of legitimizes our conversation so that'll help that whole conversation wheels start turning if I don't know and I use this technique and it worked it could go wrong so you have to be a bit careful but you could do the
the reverse conformation so I say oh so you're using Dells are you but you're using lenovo's so some people will take great pride in correcting you right which is great no no no no we're using lenovo's right okay good thank you Chuck you know name-dropping I've used this and this worked and real attackers don't really use this one too much yet for fish and fishing but I think they will so oh mr. or mrs. Smith your VP of HR or recommended I talk to you if I know who that person is I know their title it sounds legitimate if the rest of my story sounds good you're probably gonna go for it blowing smoke this one
as well works great I use that as well you know you were recommended to us right and you know you feel special as soon as someone says those words right up me yeah thanks yeah I do have some good information for you so you know and that they're you're making the person feel good some more tricks impending doom and so this sounds negative I use this trick it worked and it's really I used this HVAC example where I said you know we've won the RFP Larry's going to come on-site tomorrow to do an inspection of your HVAC hey I just want to call and see if there's anything we need to do to get him set up to do that
what what are you talking about yeah don't you know like we were working with the property management company he's gonna be there tomorrow and can you use your cafeteria how about your washroom does he need to get it use a card to get in hey can you use your Wi-Fi to upgrade the firmware as well right so you can start going in those directions and for things like physical pen testing this might be good intro aloud to vent everybody likes to vent right and so this can work pretty well you know my boss is yelling at me he wants me to get this done you know can you help me out and sometimes if you can get them to
vent a little bit you can start to build to develop that relationship smarty pants you know how did you ever figure oh thanks so much this works great too I try to work this in to every pretext right to really thank them to be very courteous people tend to respect that a lot I find zero-sum okay agreed this is used by the bad guys quite a bit right you've probably seen this quite a bit very usually it's that time sensitive thing so somebody's gonna get this thing of value it might as well be you so you know quick click the link right giving you that pressure we did a phishing program and we found the time sensitive
ones worked actually quite well it triggers people to take action so whatever you can do to get them to stop thinking about it right just do it you know sympathy this works great as well real attackers don't use this very much but I think they should you know I'm new at this you know can you help me out you know I've been trying to do this it's my first day on the job my boss is gonna be so mad if I screw this up right who's not going to help that person right and I find so that worked quite well as well so now we'll get into my pretext and so these pretext use a
lot of those tricks um and because a lot of times you'll get stuck at reception if you don't have the people's dids direct inward dial and so I anticipated getting caught up in reception and I did not because I didn't have their D IDs I did I took all of that other PBX but but it was good you're gonna you're probably going to hit reception and and and there are masters at detecting BS right so I want to really make sure I was ready for them so these were designed to kind of get through that front door you know so spoofing the university or college that some of their employees go to their interns specifically I'm calling in a
reception saying hey can I talk to so-and-so he's your intern I'm calling from the U of whatever and you know we really want to talk to that person to help develop our intern program sounds legit right so then once you're in the receptionist has probably said oh it's you of whatever they'd like to talk to you that builds some legitimacy right and then I introduce myself as that and then I go through my questions boom boom boom boom and then at the end I ask them hey can you transfer me to so-and-so because they're also a former student or an intern as well so now I'm inside and now I'm getting routed through without having to go back
out and come back in the blue-collar disco so I really like this if you have any knowledge of areas kind of outside of yours for me I work with data centers quite a bit historically so I know a little bit about HVAC so it'll be able to talk that language and say you know this is where Larry's going to come in and do the servicing I can talk about HVAC s'right and and the person on the other end you know it sounds legitimate to them right so if you can throw out those industry words that really helps as well I did this one in Vegas and it worked pretty well some targeted methods right so
these are the pretext where you're going after a very important piece of information which is probably going to set off some red flags if you're not extremely careful Mitnick does this really well you know if you read some of his books he talks about how he layers right he goes after the first one and it's relatively easy it's relatively benign it's something that you would look and go why would he need that information but then you use that for the next call and then you use the content you got from that call for the next call and you're just building this snowball of knowledge right and then when you get to the you know let's say
the fifth or a sixth college you've got tons of information to make you sound like an authority or an internal person so that's what this is all about so the first one was the enemy of my enemy you know so I'm calling as a potential tenant and I'm asking you hey how is it working in your building what's the property management like and they're gonna start to tell you about the different things within their building and there's a ton of information out there if you want to learn about a property to take that approach it's surprising how much is available special delivery I use this one it worked pretty well the script for safe FedEx or any of the
couriers is pretty well known and so you can get the receptionist to talk to you a little bit with that sort of call yeah can I tell you a secret everybody likes secrets right I've never ran into anybody who said no to this question so I'm calling as a recruiter my company's gonna lay off some people and I'm trying to find a new home for them and you don't to help them out and so I'm calling companies like yours because they'd like to you know work at a company like yours and I just need to answer you'd answer a couple questions they have like you know how's your cafeteria you know stuff like that and they usually get a bonus for
recruiting and so they're probably thinking about that so this question is usually pretty exciting for them because you're gonna give them qualified candidates um so this is another good one right it's that that greed emotion greed factor the full dumps these are great if you can get somebody lined up to do this right you're gonna go in the radio station contest I mean any sort of contests it's so overused now real attackers gravitate towards this you know how many times you get the call on your cell phone congratulations you've won a cruise right it's so I didn't use that one it was on my list but you know it's just so overused the upgrade opportunity so many of you probably work
with vendors right when you have a new account rep how does that work right somebody just calls you out of the blue and says hey I'm your new account rep how you doing right there's no real formal approach to that quite often so if I phone in and then I say hey I'm your dell account rep I know you have Dells I know what models you have right I can call in and sound pretty pretty legit go through hey I want to send you some free demos how's that sound it sounds pretty good right I just need to know how is it how's it working out with your VPN client right so I can start
digging get a little bit of content that way you're so special the engagement survey I use this one this one worked really well and it's really fast too once I get the person you know I do some name-dropping I do that trick hey I'm working with the VP of HR they gave me your name right and they said you could help me develop this engagement survey and as soon as you get them to say yes and I don't even the person said yes and then I moved into the questions so quickly I barely heard it just so you just get that little bit of commitment and just start rolling right boom boom boom boom and they're answering
questions as quickly as they can and so that's that's a really good one for a lot of content the final one there okay you caught me a lot of people say well if you get questioned you should never drop your pretext the joke is even when you're going into the police car with the handcuffs on you should always stay in pretext and I kind of didn't want to do that I wanted to put a twist on that a little bit so it never happened I was really wishing it would happen hopefully in the future it will or they say hey you know what like Rob I'm not really buying this I don't think you're my dell account rep
this actually happened in Vegas to somebody else and it was hilarious because they knew the person they were impersonating it's like I don't think that's you and they were arguing for about five minutes no it's me it's me it's like okay where do you live and it just went downhill but it was it was hilarious so so my pretext was okay you know what congratulations you caught me you're the only one in this whole company that caught me right I'm gonna give your name to the executive and because you're an example of the type of employee that they need to have so you know I'm making a note of that and hey if you've got a minute can I just roll
through the rest of these questions just to develop a baseline so so you know I've made them feel good right nobody's victimized he well they kind of are but they feel good about it right so I'm just kind of like flipping it over and keep on rolling so I thought that might be more effective so I was I really want to try that in the future now this is the reflective moment that I promised you okay some questions to ask yourself you don't have to say this out loud because some of these might be uncomfortable you know what you know when your staff especially your exec have been socially engineered right you know if some executives will come to you
and say hey yeah I've been emailing this bad guy back and forth and you know they think that's funny other executives may not say anything because of embarrassment or something like that so do you have a mechanism to trigger that feedback to you right because you probably want to know sooner than later how bad would it be if your CFO transferred you know millions of dollars there's companies out there that have wire transferred 50 million dollars right or more I remember the one 50 million which is seems like a lot of money right I would be in a lot of trouble if I transferred 50 million dollars from my bank account if there was that much in there so you know so
that's that could be embarrassing does your insurance cover that right that would be interesting to take a look at if you give away your money are you insured right do you have the internal resources to manage that risk right so if that was to happen what would you do would you start doing some sort of forensics on that to figure out what exactly happened would you have visibility would your InfoSec staff have the skills to do that and then finally you know can you navigate through Equifax paradox what I mean by that is who's getting fired right so and if you don't know the answer to that question it's probably you so it's good to know
that all right so some recommendations understand your exposure first of all right so always sent yourself that's always fun oh isn't your company find those social butterflies so who are who are the people that are publishing your VPN information out there now that's probably a good thing to take a look at what's at risk right is it proprietary information is it source code is it big buckets of money right so what are you protecting these attacks are monetized so the end of the day they want to make money so build up some defenses against phishing some things you can do you can do a phishing program everybody's doing this these days you want to measure the
clicks but I would also say you probably want to take a look at how people are reporting it as well I did a phishing program it was a lot of fun it looked really cool and I was a novice and I released all the emails at the same time so everybody got at the same time don't do that because people got it and they're like oh cool what's this right and they're clicking on it which they're not supposed to do just to see the splash screen then they're telling their friend to click on it right so just don't do that and I didn't measure reporting which would be a good metric to have right how many people are
actually telling you they got this this weird email you can create an ext tag on your incoming mail that's coming in from the outside so when the president gets the one of actually the CFO gets the email from the president that says hey can you wire transfer 50 million to that other company over there it's an emergency if they see the ext and they realize that oh maybe it's not the president right because that's coming from the outside in you won't do this but you know you could stop allowing active links in the email so they actually have to copy and paste and they would actually see that okay it's it's not going to amazon.com and then provide
some other channels other than email right and we're starting to do this quite a bit we're realizing that we're overloaded with emails right and the amount of time you can spend reading any particular email is probably seconds right so some other channels there's and there's so many of them defense against phishing right so your executives are the the highest target the the big value target right so if you could vish them ask their permission first be very sensitive use that as a learning opportunity but tread lightly right they may not find this as entertaining as you create choke points so I talked about the receptionist's a little bit and really they do such a wonderful job of
protecting our business and do they ever get any info SEC training or awareness training other than they say the the annual click-through stuff right so that might be an opportunity on your PBX you probably have dial by name do you still need it I love that feature because I can go in there at night and I can get everybody's number I can get everybody's title and then I go through their voicemail and listen to their voicemail I get so much information do you need it probably not maybe your sales department needs it maybe your marketing needs it but your IT department other people that probably not right I don't want it dids you've directed or dials most of your
staff does not need di DS give them extensions have it routed through reception they're probably calling out a lot or some but they're not getting a lot of inward calls right so why have that and don't match your D IDs with your extensions either oh that's that's not very good stop answering the phone I got in trouble for AB for putting this bullet point on there right so take that with a grain of salt that's one of my opinions you know if you recognize the name and it's your boss you probably wanted to pick up the phone I did this this talk internally and a lot of managers looked really badly at me so I had to put that in
brackets they're always answer if it's your boss get on the offensive right so I write a lot of policies that nobody reads and we do the annual training as well the awareness training and the joke is how fast can you get that done right nobody's reading policy in it you know what you have to have it so I'm not saying don't have it but a majority people are not reading them right when you fire somebody you point to it right but instead I'm saying we need to create a culture change right of continual challenges so take those people that are doing the right thing and make them into heroes communicate okay we're doing this this goal so InfoSec is doing this
advertise that right we don't have to be the bad guys we can say hey we're doing this this is exciting you can be part of this give stuff away give out Starbucks cards right be the good guy yeah right you'll get so much popularity just by giving out Starbucks cards put people's picture on on your sharepoint or your confluence site and say hey this person did this it was fantastic that's really what we should be doing and then ultimately we want to get to culture change right so one of the problems we often complain about is oh the bad guys only have to get lucky once or you know I don't have budget to really and make a
difference and to protect all the things I need to protect yeah that's that's that may be true right but and we can't scale if we don't scale we can't we can't really win that that war right so if all our employees care about security and we always say they should but they don't right they're not rewarded on that so they won't right we have to reward them and we're not at this point putting that on their yearly review right that's not one of their goals necessarily hopefully one day it will be but we can do other things right we can make them into heroes and and then you can based on that you can scale you can make them
into mentors right so then they're teaching on your behalf alright some of the tools that I looked at and you look at this is like well Rob I use those tools every day yeah it's really how you use them and then what your target is using right so you kind of roll down this list LinkedIn if it's a corporate target that's where I would start use x-ray it'll help you out a lot to bypass the page service twitter is great for images very fast you can do that you can do tools like all my all my tweets to get everything all at once Instagram if you want to do geolocation it's not bad there's better tools out
there where you can fence off an area set a time and then get multiple multiple channels of of that so there's what's one there's another tool out there for emergency management I can't think of it right now but if you're curious just let me know I send it to you Facebook's not bad SlideShare surprisingly good right I don't know why but people put their reference letters on SlideShare and that gives you tons of information personal websites are gold and job postings I can learn all about you know your Cisco firewall that you have and you know what you're hiring people to look after right just go through that Google Maps you can get your picture of the building entry
points stuff like that signage sometimes you can read that which is very nice if you're gonna do physical pen testing that's a good starting point and then once you're through that move into more specialized right so you know your wearable Strava is great I can see where you ran showed an IOT right pastebin I can set up an alert on your company Spokeo at an individual level I'm gonna get a ton information from that and then more specialized which is even more fun right so I can look up people's you know criminal record or their taxes property management is a really nice area that I'm focusing on a lot lately there's a ton of information out there for that
some resources so one of the best resources is Michael bezels in Intel techniques you can go there there's a ton of tools there it's like this big menu system of tools so if you want to do some OSINT on somebody or a company just go there and it's kind of simplifies everything for you he's got training he's got a podcast tons of information if you live up my way tottington does something similar he trains most of the government agencies he's a great resource as well again online training articles and stuff like that and then of course the social engineer right he really is the one that organizes this sec TF both at Def Con and Derby now so he's got tons of
information great podcasts as well if you've got some money you can buy plural site if with your company cyber e is a free resource online as well and they've got lots of great tools I'm a big fan of them alright so I rock through that pretty quickly if you've got questions we can do that now I just want to tell you this is my latest project here my it's kind of an OSINT project so if you have if you have any interest in ocean you can take a look at that let me know what you think always looking for feedback on that if you want to reach me those are the ways you can do so now
twitter is your best bet so we've got a few minutes questions yeah the very back
yeah so I didn't cover that but that's one of the places where I started you know just doing a who is there's a lot of good tools out there that provide information on that I like to look at who registered the domain and then I look at the IPS go on to error and look at who owns those IPS that's great as well that'll tell you a lot of good information I got emails I got phone numbers and the phone numbers nice because even if you get the pretext that helps you with the bank of numbers because then you know at least I've got that far right and then it's narrowing down the suffix of those phone numbers
so definitely want to look at that yes sir yeah it's yeah yeah yeah yeah I don't really need that right like if you gave me someone's name or a company's name all you need then is time there's so much out there right it's it's you know it's it's amazing how much is out there so just need time and you can start gathering everything
yeah so I'm sure there's a lot of good tools out there unfortunately I'm not using any of them if somebody has recommendations on that I'd love to hear that because that burned a lot of my time and I'm still struggling with that so right now I use Excel right people use Excel for everything they probably shouldn't including myself so I would have links within Excel to the to these different channels and then I could sort and stuff like that in Excel so that's why I use that and I knew how to use it so but I wouldn't recommend it yes sir
yeah
yeah yeah yeah I saw people use that and I think that's very effective you know the joke is you know people put their there they're going on holiday on Facebook and then their house gets robbed right same idea my out of office I'm very careful with that I simply say that I'm not available that could mean anything but as an attack or the minute you see that you could then you know you could leverage that for sure so the I don't like to put a lot of detail in that if I say I'm in Hawaii then they'll use that right oh hey yeah I'm calling cuz Rob's in Hawaii I said yeah he said I should give you a call to
get this so for sure that's a good technique yes
so it wasn't on Facebook it was on Twitter and yeah yeah there was there was myself and there was another person who talked about that where they found it on Twitter and I don't know what people are thinking I think that that's you know as we do our self-promotion with these social media channels and we build a brand as a night as an individual we have to be a bit careful about what we're putting out there right so we're proud of the companies we work for and we want to talk about the companies we work for but I don't think it's appropriate to - it's post or VPN configuration so yeah it's that's a really interesting area right is where
do you draw the line with the self-promotion and branding right so it's VPN was definitely across the line so yeah I recommend go out and take a look at that right see if any of your employees have done that that's one example of things they probably don't want to do and then you can build awareness around that yes sir yeah so all of the information is open-source and so you put references to all the information that you collected so you have links to it so one of the bits of one of the bits of evidence that I found was a YouTube video a tour of their office which was incredibly useful yeah so I did that frame by frame and
you could see the in the mirror there was a reflection of somebody bringing up their badge like that and so I screenshot of that I had the second in the video and sent the link in for that so yeah there's yeah that's how you do that yes sir yeah I think it was about 50 pages and yeah you know you could have gone more and more and more and it's funny because you start going down that rabbit hole and it's so fun right like oh yeah I got this one right and yeah it's just you feel like a private investigator or something right so it's a real rush so almost I was so frustrated because I there was one or
two that I didn't get and it was who does their garbage and who does their bug extermination and I was trying I was working so hard at that and you know trying to get different camera angles of their office and I could see there was a truck in their parking lot oh maybe that's it but I couldn't get it quite right using all sorts of different satellite imagery and yeah that was fun but missed those two you
you