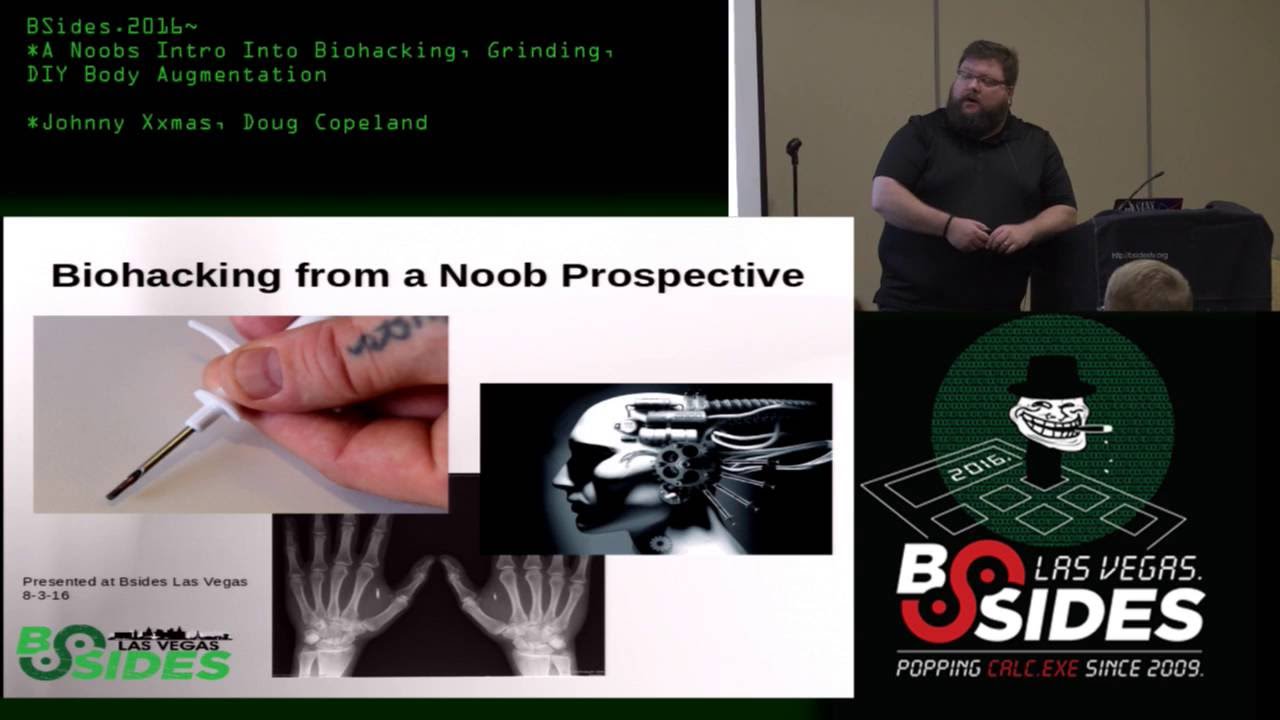
Threat Actors in Cyberspace: Insiders, Criminals, Activists, and Nation-States
Show original YouTube description
Show transcript [en]
everyone thank you for coming to my talk today especially given the time slot so when I was teaching at Iowa State University we used to call this the death hour because students used to have allergic reactions to their lunches that would cause their eyes to swell shut so I hope I don't see anyone have allergic reactions today to my talk because these slides are 100% hypoallergenic so as you heard of my introduction I'm Ted corbeil so I'm a retired Marine intelligence officer so I've been out of I've been retired for about three years now so what you're gonna hear from me during this talk is you know a unique spin on cyber threat actors okay so real quickly
on Baron Baron is a cyber security effectiveness company so we have the first business at an analytics platform that measures the effect effectiveness of your security through security instrumentation so we provides you that evidence that you need to measure manage and prove and communicate your cyber security effectiveness all right but I'm not here to pitch when I'm here today is to explore cyber threat actors and I'll give you some some similarities and some experiences that I had in Afghanistan supporting counterinsurgency operations right so a lot of you when it comes to threat actors you might have more technical knowledge so you might not hear much new from me but you will hear it in a new way
I guarantee you that so like you heard in the keynote speaker today I'm an aspiring new security people right I come from a non-traditional background to get to where I am today so hopefully you'll appreciate you know kind of a unique perspective on what it takes to go after threat actors so one every marine starts off with our missions the first thing we do is mission analysis problem framing mission analysis but we determine what the desired outcome is we define what success looks like and then once we have that then we backwards plan from there given the time resources and materials we have available to us so for cyber security our goal is to protect
our digital assets we see regardless of industry companies have digital assets from which they derived their their IP their intellectual property or competitive advantage right and a significant breach or loss of that IP has economic consequences and damage to their brand reputation so as a result we see companies spending tremendous amounts of money to protect those digital assets Gartner forecast next year that companies will spend 124 billion dollars on cybersecurity tools and services so we're going to talk to you about for now is you know the various threat actors are out there so we're going to talk about grandmothers drink stirs guerrillas and governments or as you might refer to them as insider threat cyber criminals activists or
nation-states before I get into that quick war story so typically this talk is given by our sizzle Brian cantos he was unable to be here so at the last minute he asked me to step in for him so as the keynote speaker said I get the opportunity now to speak for the first time and at end of my first 'besides episode so I'm new to this space and so far I really like it but based on that I've decided to put a unique military twist on this talk so you're gonna see me juxtapose between my afghan experience counterinsurgency operations and how that's directly related to the same kind of threat actors in the cyber space so a little bit different than
what you're used to hearing so in 2001 we declared war on terrorism right and we launched campaigns in both Iraq and Afghanistan to deny terrorist sanctuaries from which they could plan can future attacks on US soil right so it should have been a pretty straightforward fight right it should have been an easy win you have the one side you have the mightiest armed forces in the world right with a trillion dollars and on the other side you got a bunch of dudes in sandals and running shoes with some 70s and 80s era Soviet weaponry but yet here we are 17 years later still continuing this fight so I went to Afghanistan primarily to defeat the Taliban we were there to provide
stability to the region and create the conditions for the successful transition of security responsibility to the Afghan army so that we could safely withdrawal the US forces but when I got there I come to find out that there was multiple threat actors impeding our ability to do our mission there that aligned pretty well to the 4th categories of third actors were gonna spawn the cyberspace we had insider threat from the Afghan army we had criminals around the drug trade there in our Southwest Afghanistan where I was we had Taliban insurgents to deal with and of course we had nation-states Iran and Pakistan that were getting involved in that picture so very nice correlation to what we're gonna talk
about so some commonalities that I see between the threat I face then and the threat I feast I face now right first it's relatively inexpensive to do some of these things whether you're insurgent that finds an old 500-pound bomb and manufactures and improvised explosive device from it or you're just you just grab a laptop and it writes some code some script right it's relatively inexpensive to conduct these type of attacks low attribution right whether you're insurgent that can blend into the populace or you're a hacker hiding behind a keyboard it's very hard to attribute who's doing these types of attacks it's relatively easy right you can have very successful damaging attacks with low technology and basic
techniques right and last but not least there high payoff right you can have devastating consequences in relevance to the amount of effort you put into the attack and frustratingly you can stop ninety nine out of a hundred attacks and it's just that one attack under overwhelms all the rest of your success so lots of commonalities then between them the first threat actor group we're going to look at today are your inside threat whether it be your grandmother who continually falls for the phishing emails or your Uncle Jack that's tired of being a dull boy right they're extremely frustrating to deal with because they can have devastating demoralizing effects on your company when they're successful or your
organization and it's hard to deal with because traditionally your defenses are face outward not inward so it's a challenge to counter these there are many different categories of insider threats but we primarily see three types of categories that we deal with here you have your careless insider that no matter how many hours of cyber awareness training you sit make them sit through right they still use weak where's password 1 2 3 right they still write it down on a sticky no and then post a selfie of them with that note in the background right on Instagram right you see them they upload a bunch of data to the thumb drive and then they lose it
or they email unencrypted sensitive documents out right so careless insiders tend to do a lot of damage blonde boo snake then you have malicious insiders who are doing it intentionally whether they're employees that got passed over a promotion or found out layoffs are coming or just tired of being there right or didn't agree with whatever that organization was doing you know they do it on purpose and it can take the data out or do some sabotage and do some internal disruption and the last quarter your category is master rating insiders and those are external people that get inside your organization under false pretenses or it could be malware or something it doesn't have to be an individual so difficult so in
Afghanistan like I said before I deployed there in 2011 December of 2011 the week before Christmas for a nine-month deployment and I went over there with the intention focused primarily to defeat the Taliban and set the conditions for the successful transition of security responsibility to the Afghan army well when I got there I surprised to find that the number one threat actor we had was in fact insider threat the Afghan army were conducting attacks and killing more soldiers and Marines then the Taliban were and it only got worse in 2012 the year 99 month tour so we spent significant amount of resources trying to investigate profile at risk individuals and figure out you know what why were they motivated to do
this and it turns out most of them were coerced into doing so they didn't have anything against us directly but they were coerced by the Taliban to conduct these attacks under threats to themselves or to their family but the motivation aside you can just imagine the frustration it is when you're over there for the sole purposes of training these people working side by side with them so they can take over that mission and they're attacking and killing you and although we put significant security measures in place to try to mitigate some of this even the most minor incident had huge publicity wins for the Taliban and it supported the narrative that the Taliban were driving us out of the
country because if you recall that fall before in 2011 Obama officially announced the withdrawal official withdrawal of US forces from Afghanistan and even put a date on the calendar for us so they knew exactly them when they were leaving so they were making it a point to step up their efforts to try to kick us in the tail and as we were walking out of the country so extremely extremely frustrating and you know detrimental impact to our brand image right the Marines and the u.s. horses supposed to be almighty and yet Taliban are winning from these from these kind of attacks and last week in the news I know if you saw it the insider threat
continues right security personnel for a high-profile conference with senior Afghan officials and at you at the top US commander General of it had a conference and they were ambushed by their own security detachment Afghan official was killed a u.s. commander general survived so that that threat persists but even US companies and organizations have detrimental impacts from Barren damage from insider threats we saw a few months ago the hit that the stock price took for Tesla when reports came out that a disgruntled employee had sabotaged right he had been passed over from promotion and allegedly hacked into and corrupted the manufacturing operation system for the Tesla 3 plant and you can see as a result the stock
yet that the drop does anyone know I had peaked on August 7th yes you're right yeah all right boom right Elon Musk Twitter tweeted out that they were he's gonna take his company private and boom right so who says Twitter's not good for anything right well you know ironically that Twitter that tweet right or at least a whole nother can of worms right and you can see their stock price plumbing because you know people SEC had some problems with releasing you know private information that manipulating the market so you know to me that's a careless insider right well not traditional cyber cents but you know a tweet right now you got a double the Tesla took the double
insider whammy here and gotten got hosed so just shows extremely frustrating and devastating consequences to brand reputation alone not to mention loss of IP from careless insiders the next category look at are the gangsters right near cyber criminals these guys are motivated by money right so it's extremely challenging and frustrating to deal with criminals when you're have must abide by the laws and regulations and they don't right it's an unfair fight right that's it's stacked against you when you're trying to play by the rules and they can do what they want as with the insiders we generally think of it as three types of categories of criminals now granted sometimes insiders or nation-states yeah or might be also motivated by money
but we're talking about them separately so I've removed them from this list but you can see the general three categories the professional the mule or the getaway right and they each have different skill levels and sophistication and motivations for while they're doing it for the professionals are doing it by the money the mules there could be complicit or naive in the fact that they're laundering proceeds from cybercrime and then you have to use the youth who are you know not not subjective too strong consequences so very challenging in Afghanistan we also had to fight with criminals so quick geography lesson for those who have never been to lovely Afghanistan you can see that it's primarily mountainous with
the Hindu Kush mountains to the northeast sloping down into the desert here in Helmand province so this is our area of operations for the Marine Forces so why would anyone care about this arid densely populated piece of earth does anyone know yeah opium right water border yeah yeah so it turns out that this area of the márcia or the Helmand River that flows down from the mountains you know this is some of the most fertile farmland arable farmland and all of that all of Asia or all of the country and in the surrounding area and coincidentally the United States from 1949 until the Sylvia invasion of 1979 were supporting the Helmand Valley Association mirrored after the Tennessee River Valley
Association so we built a series of dams and irrigation systems and canals to make this the most fertile firmly farmland because in this area those tribes are essentially subsistence farmers so these these initiatives were meant to increase crop yields so that they could support the larger population yes there are some lithium rare minerals in and around the desert here but primarily the reason why people care is like the gentleman said their poppy right so the number one crop grown in Helmand province today is poppy right and it's not to supply you all with poppy seeds for your bagels right it's because the sap from heroine plant are the sap from the poppy plant can be
turned into opium right so a criminal Patriot Network the illicit funds from that drugs it was the center of the cause of the root of most of the discontent and chaos and violence in the district because you had all multiple actors vying for control of that money in those fields so you had the Taliban insurgents were funding their their insurgency through this money cuz insurgent terrorists don't fight for free right they still want to get paid you know the criminal patriot networks and in Assam sadly in some cases even had Afghan officials all wanted a piece of the drug trade so extremely extremely frustrated a complex situation when you have multiple actors criminal element undermining the ability to do your
operations we see the same thing on the cyber on a private sector right business US businesses are constantly struggling to have their having their operation is interrupted by cyber criminals last summer we saw HBO get a series of hacks and held ransom right in this particular case Iranian gentlemen stole some unreleased videos and the script to an unaired episode of Game of Thrones and demanded six million dollars in Bitcoin in exchange for not leaking it but she continued to trickle out right but you know as we know it takes more than just a hacker to take down Khaleesi because that season had the strongest ratings 12.1 million people watched the season finale of Game of Thrones last year so
probably many in this room watched it the next group we're gonna look at are your gorillas or you're hacktivists so unlike cyber criminals they're not motivated by money these guys are motivated for you know fighting against social injustice so in Afghanistan you know we had to deal with terrorism so to me they're the same one in the same only their tactics different right they're both motivated by political or social agenda only their tactics change so terrorism terrorists use violence or intimidation and hacktivist uses computers right but to me they're they're difficult because they're irrational right their actions are aligned to get publicity so once back to what I said before you can stop 99 out of 100 but that one is enough to
give them enough credence to have cinder term success in Afghanistan we were fighting terrorists right so we had the Taliban they're an Islamic Muslim jihadist group right so they were vying for control over Afghanistan from 1996 to 2001 they ruled under Sharia law till we removed them from power in 2001 and since then we've been trying to remove their influence from the country and instill government the government of the Islamic Republic of Afghanistan as legitimate control of the company but as you can see frustratingly last year last month in the New York Times right after 17 years billions of dollars thousands of lives they still control or influence more than half of the country so very very difficult shows you that it
doesn't take much to be effective and achieve your political agenda through terrorists on the cyber side we have hacktivists so one of the most well known groups is anonymous alright so a group of hackers that are fighting injustice we can see you know several examples of them hacking into government organizations in protests of the death of unlawful shooting of unarmed black youths so in San Francisco with the BART and then in Ferguson last year so very very difficult to counter this threat last but not least nation states right your governments does anyone know this is an image of from yeah now what happened well this is a good example of a nation-state what happened to Sony yeah
they got they had crippling crippling cyber attacks against them right to prevent the release of this film so you can see this the threat is real you know so every major country now is starting to introduce cyber warfare as a legitimate arm of their military forces but international laws and treaties don't address cyber warfare yet so as a result you see a lot of foreign nations conducting cyber warfare Tiffani's Serra typically right so it's very hard to attribute what they're doing to it and we're guilty of it ourselves right stuck next Stuxnet so we see this is a this is a challenge in Afghanistan we say allegedly yeah allegedly so in Afghanistan you know is no secret
that Pakistan and Iran were aiding the Taliban in fact Pakistan openly offered them sanctuary in the south so the senior Taliban officials had lived in the south and from there they could plan and carry out operations into our area of operations there's no better example of that then the village of Barham sha depict in here on the southern border this village in bazaar actually was split in the middle with north of it in Afghanistan and the south part of it in Pakistan and from Pakistan they would they would stage and launch their attacks into our district so we were continually conduct offensive operations to interrupt the flow of manpower and materials into our into our
country but we could never go south of south of the border right we had to stop there so we were constrained it was frustrating to try to counter this nation state because we were strained by rules of engagement or international laws does anyone else think of someone that's gets frustrated by not being able to retaliate because of some arbitrary line right dog poor dog here so I'm not saying that the Taliban are Looney tune fans and I'm not saying that Warner Brothers supports the Taliban I just noting the similarities here right that they were hiding on the other side of an imaginary line with the ball that we can take away from them there's another
example of business are also hindered by their ability to prevent nations from stealing their intellectual property so this is the example of Chinese Chinese company right they were had a contract with American Superconductor for their windmills when they were unable to successfully reverse-engineer their operating system they paid a Austrian contractor to that company to steal it right so he steal it turned it over to China they started selling these in the US but the wind turbines and it resulted in them having lay off half their company half their employees and saw a loss of 1 billion dollars in shareholder value right but we decided to take action against China so we successfully convicted them in
court and we find them 59 million dollars in July so 59 million dollar fine for a 1 billion dollar loss of IP and income not much of a deterrent my hands are tied when it comes to this so very challenging to deal with nations to threats from nations dates so I think I've done a good example of kind of showing you you know the similarities between the threat I face then as opposed to the threat I face now one of the keys to being successful to a military to civilian transition is to be able to clearly explain and adapt what you did in the military to what you're doing now so when I look at both these situations
that I just described to you I see some common challenges we both face with first was anyone in here I have unlimited budget and resources for their security program yeah I didn't think so right wouldn't it be nice if you had unlimited resources so because you don't you can't defend everywhere you have to decide where your most critical assets are and you have to strategically focus your resources on trying to protect those but even if you did have only unlimited resources when it comes to cyber security don't lend more money at the problem doesn't fix it right and even if he could buy the latest and greatest technology out there technology doesn't always work the way it's
supposed to and it can be very difficult to employee property set up in to configure and even if you could do all that and buy all the technology and set up the perfect defense it's not a static situation right it's a dynamic evolving threat you see this threat counter threat counter counter threat in the military we use the term doodle-loop observe orient decide and act where you observe the enemies doing the orient on what they're trying to do you make a plan the counter that you decide and then you act on that and what you're always trying to do is continually get inside the loop of the enemy and make them react to you but the biggest
challenge I see in both these scenarios is how do you measure and communicate ROI and success how do you show how effective you are against insurgents all right count how effective are you doing against the insurgents or how well do you communicate how you're communicating measuring cyber security effectiveness cyber security as I said in the introduction you know hundred twenty four billion dollars estimated to be spent next year on cyber security tools and services cyber security is becoming a board level conversation where boards want to know our data safe people in executives and board members are losing their positions now over data breaches so as a result they're demanding evidence of effectiveness so often what you see is
some type of executive dashboards that has you normally includes everyone's favorite beloved heat map right so on the left you can see the flagship product we put out semi-annually twice a year in Afghanistan what we were trying to show the measure of effectiveness of our of our counterinsurgency operations by showing Taliban versus Girona influence so this was a very laborious six-month process where he had to take a bunch of subjective and qualitative data and work with multiple stakeholders who own that piece of Grant ground to fight over what color you're gonna make it as a green we're good is it red we're bad or is it somewhere in between very difficult here's a here's a deck you
tved ash board I found that was presented during RSA in 2016 looks very similar right generally you take whatever arbitrary data that you can collect and you figure out a way to jam it into some kind of heat map and tell a fuzzy picture that you're good right that what you're doing is working whether that be oh so very challenging but in both scenarios this doesn't necessarily effectively measure effectiveness it measures something but it doesn't give you a good accurate picture of what you're doing is working so who here has some examples of how you measure security effectiveness in your organization what's a metric out there that someone uses speed up ticket closure yeah right reactive right what
else time since last breach anyone what else time to patch correctness of configuration okay so is that generally result in a hit list of all things that are waiting to be fixed okay policy place all right any dwell time okay what else items that have breached SLA no okay blame it on your third-party provider your MSSP that works awesome okay all right once again I mean it's data that you could collect that not necessarily effectively measures the effectiveness of your cybersecurity tools right so what if I you know so it's what we found is it's not necessarily your fault right because we don't have a good way to gather quantifiable evidence of effectiveness we're forced to manage by
hope and assumptions we assume that the tools work the way that vendors say they do we assume that you've deployed them and optimize them and configure them correctly and that they stayed that way we assume that your people know what they're doing and they know how to execute their properly follow the processes and procedures in case if there's an incident or to prevent an incident and most importantly we we assume that we know what's going on in our environment right the frustrating thing about cybersecurity is you have the responsibility for protecting it but you don't have all the authority over the environment IT can make network changes that counter you know the counter mind and rule you're you're
exerting controls you know in a you know ineffective and you might not necessarily know that that happened sometimes they might tell you sometimes they may not there was really no definitive way to know for sure right and we know what happens when you assume so what if I told you that there is a way that you could quantifiably instrument security so you could get the data you know to make sure that your security tools processes and people are working the way you think they are so we've instrumented security instrumentation and more than a hundred companies across all industry verticals and what we found and should be no surprise of those in the room that the
amount of money spent and the amount of effort put out does not result in effectiveness we see companies in the news getting breached all the time in fact when we our business analytics platform what we find when we put this environment is that less than 25% on average of attacks are blocked and of those ones that are blocked less than 40% are actually have a correlated rule in the sim that triggers an alert so an analyst saw it right so on average what we're seeing is 20% effectiveness of a cyber security stack in companies once we put in our business analytics a cyber security platform or effectiveness platform so that means to two dollars out of every ten dollars being spent are
you're getting your money's worth out of so we're not saying that you companies have bad people we're not saying that there's bad tools we're not saying that there's bad processes all we're saying is there's never been a way before to effectively quantifiably measure the effectiveness of your security controls until now right so we'd like you to think never at the beginning when I said I hope that this talk my military perspective would inspire you to think differently about security well this system brings me to what I wanted to think about in terms of instrumenting security what if they could implement a business analytic platform right that could provide you the quantifiable evidence you needed to effectively
measure manage and prove and communicate your effectiveness to mitigate business risk from cyber so this is a security instrumentation isn't just new it's a completely different way of thinking about evaluating security so as a military intelligence officer my job was to provide timely relevant and accurate information to the senior leadership so they can make decisions around operations and planning right in corporate America I see the same need for demand for evidence and data executives are lying evidence all the time to make business decisions right to determine where to spend time and devote time and resources and what we see all other traditional business functions have a standard set of quantitative metrics and kpi's by which they can
measure and show the ROI for those programs or their effectiveness why shouldn't cyber security be the same right why shouldn't we be able to have elevate cyber security to a data-driven quantifiable business function like everything else so during this talk I hope I've shared with you a unique military perspective on the con the similarities between threat actors in a counterinsurgency environment versus cyber threat environment and got you to think a little bit differently about cyber security so I can said in the beginning you might not have heard a lot of new when it comes to cyber actors but hopefully you heard it in a new way this time are there any questions it was they're terrorists so generally what we
what we found is we did a study of 21 attacks had taken place over the preceding 20 month period and what we found was a majority of the individuals that had done the attacks came from one particular village in Northeast Afghanistan that was on the border of a very strong done Taliban controlled area and those individuals would go home to visit their family and then they would either be physically threatened or told that they would kill their families if they didn't conduct these attacks so that's how we're able to determine and and start evaluating a risk profile right if they were come from a certain village or area of the country if they recently went on vacation and they came
back there was indicators at which we could then deny them access to weapons or remove them from vicinity of us or something to try to kind of mitigate that effect data I'm an Intel guy so data is my life right I've been in the information business for 25 years versus Intel tracking what enemy's gonna do now I do it in returns of cyber threat actors or in my case of sales enablement what the customer wants great question I appreciate it yes
yes well that's the that goes back to attribution right when you have a bunch of people flowing back and forth there are official legitimate the border crossings and then there's everywhere else that's kind of like the US border right there's lots of places that people and materials can move back and forth it's sometimes it's hard to separate you know refugees from bad guys as we're facing right now right I thought a hand over here now a person all right I thank everyone for your time thanks for coming [Applause]