SyedZaidi
Show transcript [en]
[Music] okay so let's get started so as you can see on the screen that I will be speaking on the incident
response how many guys work in in response here okay just two okay three okay so basically uh my name is s zadii and uh I work as a senior responder at sofos and I am in industry for H 15 years where I have worked in dfir and it I have Masters in N Communication in security and hold several GX certifications gcfa GC uh what I do is what I love I love dfir and thre hunting because that gives me a satisfaction which I do I love to help people so in case you want to connect with me after this talk uh happy to do so on LinkedIn I can uh help you Mentor like how you can excel in in response
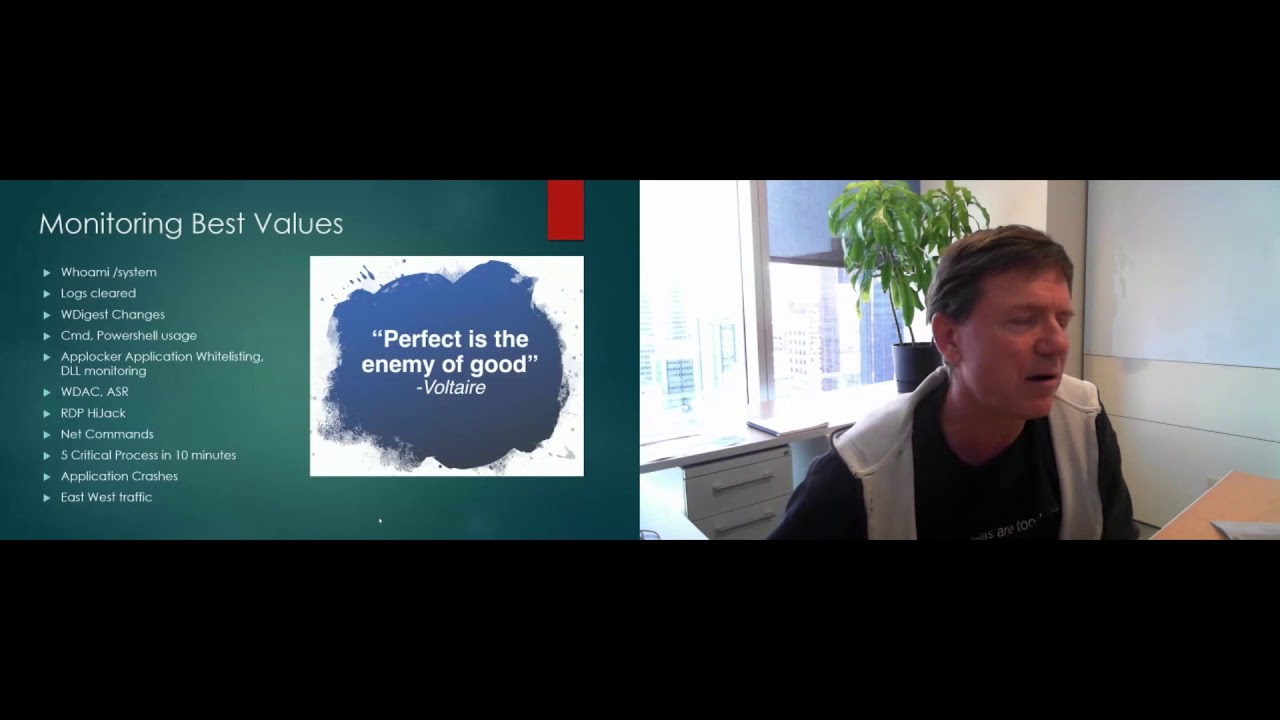
and hunting I I'm a strong believer in learning and research that uh you have to keep Lear learning and doing research don't stop always you know willing to get the answers like why what and how because that always you know helps you excel in life and this is my uh quote here that your team strength lies in the weakest person in your team how strong you are but if your team has a member who has no understanding of what to do and not helping that person then that is your strength so help your team train collaborate and make our team strong so as you can see on the screen that there are these few topics which
are pretty complicated and have less understanding from the in response protective like that is scoping the incident impact throughout time thre intelligence I development and visibility so so these are the few topics I will be covering to today to give you the better understanding that what I have learned what I have seen while working as an insent responder that I will be speaking about so let's take a real life example like uh in your house there is a robbery and incidents do happen so how would you handle that in incident would you just do nothing definitely not you will do you will take several steps so for example the first thing you you should be looking for is how they get access to
your house how they came in and that is the access control part like how they got the initial foothold in your house and then once you have have taken care of that you can cover that like okay they came through the door how they came like is there is there is a key which which they have that is there is a fingerprint loot which is being vulnerable and being hacked so that thing will lead you to some answers and once you move further what what was their motive here like like why they came they they came here for just to some documents to steal the crown jewels and Etc and then if you go further here and you
might see that okay I have some cameras installed I have some sensors here why they didn't deta when that actor or that robber came into your house so this means they might have hacked it and they might be watching you and that is the persistence mechanism which they can use to come back in later and then you need to also look at like how they have evaded those things like your door lock your fingerprint sensors your your cameras so definitely they have done the defense evasion to evade those things and to get their goal the reason why I speak about here is because in cyber world is it's the same thing like the same thing but what changed is
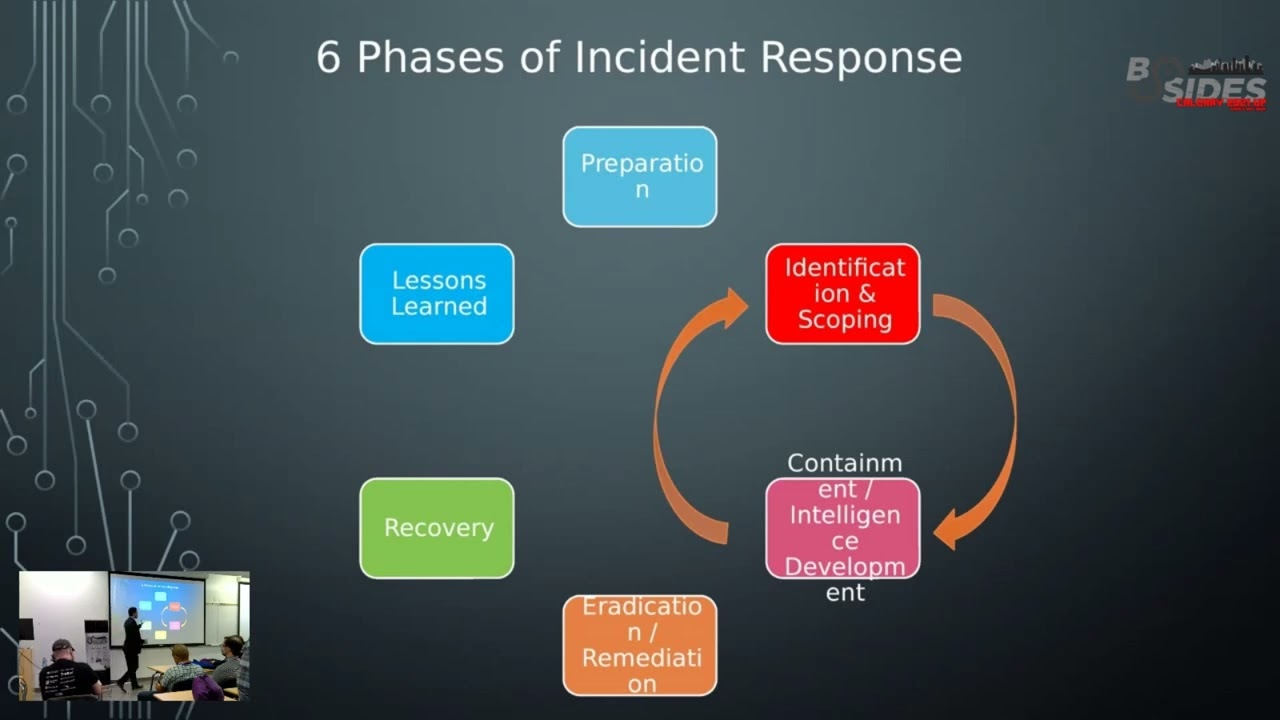
the demographics because to come to your house or to your bank they have to be physically there but in cyber world they they can be anywhere they can be anywhere and they are like do some reconnaissance from like sitting in Russia or Georgia and you are totally unaware of that so that's the reason basically I have taken a real life example mapping it with the cyber world okay so I'm sure you guys are familiar with this six phases of the insulin response the first step is preparation second step is identification containment radication recovery and Lessons Learned what I will talk about is specifically about what people Miss there like in the preparation phase if you don't prepare well for the
incidents all these five steps will be very difficult but even if you prepared well in your preparation phase you might have difficulty in these three phases if you don't cover these two steps well why because when incident happens all businesses approach to recovery like we have to recover we have to recover we want to go back to business and that's where the the problem starts so you have to first identify and scope the incident what it mean is so for example uh a company a has been hit by the ransomware attack right and the ID guy checks okay there are only three machines which are uh I can see have an impact like the file is being encrypted
and there's some other activity going on and they re and they go for remediation and recovery so what would happen is that you are going for only three machines where the actor have moved to 20 or 30 or 40 machines so you have to scope well because if you don't scope you will go there and then again you have to come back here again which is very costly right because that will take number of days human resources and many things once you do do with the scoping here you have to make sure that you understand what is containment and intelligence development most people think that containment is that you have to just you know block the IPS on the firewall or
just block the hash and we are good enough no the main purpose of the containment is to know that how the threat actor has put a foot in your en requirement how they have came in like it can be anything it can be uh the RDP which is remote desktop protocol one of the most famous attack Vector with threat actors used to come in your environment and if right now if anybody you of you guys use showan you can see right now there are almost 10,000 plus servers worldwide which are exposed to internet via RDP so you see it's very easy for them to come in so you have to make sure that you contain the incident
well this part is all about developing the intelligence means that as you are doing the containment you are investigating you are machines and while doing that you have to record those indicat terms of compromise means you are investigating a machine for example and you see that okay they they run mimic cats mimicat is a tool to gather credit credentials so you have to record that event with the time and some other parameters if if if you don't do that and if you are like okay I can just take a paper write down there then once you reach to this F phase of eradication you will be missing the ioc's you you will be missing what has
been done by the threat actor so you have to make sure that during this phase of containment and intelligence development you are doing the right things by containing by recording all indicator of compromises and space here you have two options like you have to to either just do the eradication or move on or you do something more here because people think that okay we have removed the thread actor and that's it but you have to make sure how the thread actor have moved on that machine or the en environment if you only you know focus on removing set actor you might have more things to do so so so for example if you have been
hit by a adversary which is scrip and you know about the ioc that's fine but if you have been hit by the AP or you are being hit by some other unknown apts then you have to make sure that you rebuild your machines because if you're not rebuilding your machines that's the issue and then in the recovery phase we recover the business but the most important part of recovery is that you should have goals to improve because if you are focusing on that okay my business has been restored and we are good to go we are getting money then I bet that you will be hit again you will be hit again because one thing is for sure that if you have been
hit by adversary you have to take ristic measures here you have to make sure that now you have enough defense capabilities to protect against because why because during all these phases you have to make sure that you know one thing that threat actor came in your environment and they know your weakness they know your weakness that you don't have a good EDR solution you don't have uh CN you don't have the good firewall or your firewall is vulnerable not patched so if you don't take that actions before you go to this phase this means you are planning for another incident to hit you and in this phase what you're going to do is that first thing you have to do make sure
that incident is over you have to do the validation that there are Nothing Left Behind number two what you need to do is that sit together and discuss like what went well what went bad because you have to improve your things so so for example you were hit by The Ransom re and it it took you around four weeks to recover your business is this what you want or or you want to have in just one week or two weeks and how you can achieve that that's the thing basically you should be doing here this slide basically is what I have discussed already before and you can see here that these are the faces watch what
what we have discussed and what you should do okay visibility based on my experience and trust me uh businesses who are hit by ransomware 90% of them don't have a visibility of the assets like they don't know where the assets are lying and what I mean is not the money but the machines the servers the endpoints the Wi-Fi routers the device where are the deciding and do you have the count of that because you might not be knowing your assets but but I can assure you the threat actor knows your asset because they know that that's the PIV point they want they will use to come to your network so that's a key that visibility is a key in response what you
cannot see you cannot protect so you have to make sure you have inal visibility of your environment because the thing is that this point might confuse you but this is a very honest Point here because if you don't know your asset you might not patch it and it might be the most vulnerable machine in your network and that's what thread actor loves because they try to exploit the vulnerability they want less noise so ra so so so so rather they go to a difficult task to get into a network they will find that weakness which you are unaware of so visibility this slide basically is all about the scoping and containment of an incident you can see here that no
scoping if you don't scope well that means you don't have have an idea about how bad is the intrusion how deep they are in your network and if you don't do this well this means you should be ready for another incident no containment that is a backa game because what you're doing is that okay I have a very good scope here I know that okay these machines were hit by the r of here I know it good go scoping but you're not closing the door here and people are coming inside right so you have to make sure that okay you have done the go to scoping but you have to contain the insent well and while doing these two
things you have to make sure that you're recording things as you investigate otherwise it can be a nightmare because if you don't record because what you doing actually you doing the in response and for six and in for 46 the key is you're your notes that how well you you record those things and if you don't do this well that can be a shoe and as you can see here the goal of the containment is you you need to make sure that your defense is enough good to make the threat actor frustrate because when they get frustrated they will do mistakes and we have seen that because I have been uh in the incidents where we
can see that we were fighting with a live thread actor and and when they do this when we have this things I can see that thread actor mistype commands they do mistakes and that mistakes are very noisy you can pick them on the CM or your EDR Etc so if you don't scope well you don't contain this is what happened and this is one of our incidents I worked on and you can see here that three threat actors lock bit Hive black cat three T actors destroyed that organization within just two weeks and how they came in they came in Via RDP and the most interesting part is that that you can see here that this
incident happened in May sorry a April to May and this thing is in December so that means that 6 months before the incident happened someone got to know about that their rdb is open and you can see here IAB initial access brokers they are the ones basically who knows about these things like okay their port is open or their machine is vulnerable and they go to dark WP and sell those things so that's what exactly happened here that in December someone got access to the RDP they this they sold that to these actors and then you can see here that on 20th April they came in in they did data extration they run mimicat to get
credentials because to execute a Mal with the privilege you need to have credentials and then just after three days they execute ransomware but things got interesting because just after few hours hi came in and they did encryption and then just when they were doing a self remediation because they were doation and and what they were doing is they were just rebuilding the machines backat ransomware hit them and that ransomware was a pretty like nasty attacks they they they they just destroy you completely and that's what happened like that attack completely destroyed them and we came there for help here you can see what happened with them and this is very rare to see actually that this is the file and you
can see that loog bit did the encryption and then hi the same file and then again Hive see that okay that's not their ex extension so log bit will encrypt again and then they see okay that's not our extension we will encrypt again and then that at there the third encryption and and you can see a single file was encrypted almost five times and what happened in this is that okay you are a big company and you have money and you want to pay Ransom okay what have happen you have to pay Ransom at at least three times and even yet if if with the ransom and get the decryptor you won't be able to encrypt sorry decrypt
because if the file is being encrypted multiple times the BD changes so you won't be able to even um decrypt but what you can do is you can you know request them okay please don't leak our data on the do weap and other topic uh that is Instant versus imp impact is something really really not understand well the businesses always comes into action when they are hit by the impact because if you see that the encryption is the last step it's not the first step so you have to make sure that you are doing a good deduction you are seeing things in your environment because before the encryption they have done several things they have to take
the foothold in your environment they have to escalate their privileges they have to move in the environment and that's really noisy if if if you have a good good CM you can really watch that moving and defense evasion very noisy because when you do that your windows machines your windows servers trigger sever alerts was pretty noisy so if you can stop the attack here you can defend against the ransom reare because this is just a small subset of the whole incident they have to go all these phases which are really noisy really deductible before they went to a final phase but the catch here and and the catch is this thing that dual time and if you can see that this is a
box and whisker plot and you can see here that this part and this is right now the maximum number of days thre actor was in the environment was 120 plus days and that's a median that average is 60 days and this year the maximum days is just 41 and 20 is the average days so you have to make sure that you are in a good detection know your environment know what's happening because if you don't act quick you won't be able to stop the attack the last DW time requires a speedy action from the all the Defenders if you don't do well that can be a Shue and lead to the overall attack I development many
Defenders don't do that they they okay okay I will record those ioc's indicator of compromise in my own notes and will you know contribute in the defense but the thing is that the these incidents require a collaboration and you need to make sure that you are having a single sheet to record all those events because that will help and help you in a very long way why theat compromise you need to make sure that you're checking throughout your environment and if you record well that will that will improve your thir intelligence one thing number two it will automate your inser response so for example if you find malicious activity on three machines what you're going to do is you
will not do in depth investigations of all the hund machines you have to be quick here and that that quickness will come from these ioc's that what it will do is that through your EDR so for example we have sofos in s force what we can do is we can run OS queries do you know about OS queries and anyone okay so basically OS CES is that you need to write a SQL C so for example select from this thing so you convert that SQL cury into a meaningful OS cury to search for these indicators throughout your environment and in just few minutes time where you will go to Every machine you can just cury thousand machines at a
time and find out okay what happened actually so it really speeds up the Enterprise incident response and one more important part about about the about this is that that you know you need to make sure that your notes in instant response are are so good that not you but your team member or your team lead can reproduce the same incident from this iot sheet because if they cannot then this means that you have not done the good job here so this is all about I development remediation and recovery so before we have spoken about what you should do in remediation and Recovery here we will speak about the failures because if you don't do things
accordingly they will fail and the first part is that you have to do the proper scoping because if you don't do the proper scope hoping and Remediation will fail was what you doing remediation you have to rebuild machines you have to do some other things so for example if you believe that only five machines were infected and you rem them you haven't scoped well and that will be the biggest failure and you have to understand the intrusion like what it means basically is know your threat actor what it do I don't okay don't focus on the ioc's for example if you are hit by a black cat trans trans go online read about them at
what they do because might be you are missing that that thing that okay these ransomware group lock bit comes they encrypt your machines and do these things black cat might be doing some other stuff so if you don't don't know your uh attacker that can be a big issue and the most important part is validate your steps of remediation you have to validate this means for example we have many cases where during remediation we ask our customer okay can you block this C2 IP address that command and control IP address by the thread actor can you block that this they say okay we have done that but few hours later we are seeing the same activity from that IP
address so this means you have to make sure that you validate each and every step if you are rebuilding a machine you have to make sure that you rebuild it properly knowing all the parameters you know about the thir actor here once you move towards the recovery phase this thing is is pretty clear but this part is what we have seen before that if you don't plan to detect the attacker earlier after moving through all the phases of ins response you will have a reinfection so you have to make sure that as you are moving in in response phases you are taking appropriate steps to be become more defensible because if you don't do then
we have seen just before that you will be get hit again by The Ransom groups or any other groups or might be a script KY because if if if you're too open you never know right these two topics basically are like very outside of ins response based on what I have experienced that they believe that threat intelligence is a totally different part and threat hunting as well no when you're doing an insent response you have to make sure that you are doing it in the right way because that that Intel comes during when you were investigating so you have to make sure that you are recording those things because that should the key product of this phase that's phase
number three of the in response and if you're not doing it well then you might be playing a v mole to you know regard those ioc's see what what what happened and running again and again this point is very important in threat intelligence and what it means basically that once you have the enough knowledge of the attacker while going to Google know about the attacker that part really helps you in thre intelligence let's take an example here so you have been hit by a very sophisticated adversary they came in they take your data they encrypt your machines and they clear all the tracks like you have no idea like you go to the machine and say okay nothing is there I
can see only files which are encrypted but when I go to logs there are no logs but if you have understanding of the threat actor intent okay black cat R for example when they when they come in they always clear the tracks so you will find some other artifacts in your ins response to counter that but if you don't know you will say okay this is good you move further and that will be a big failure in your inser response as well as threat intelligence how to be very effective in inter response threat hunting like threat hunting when when we speak about is it's like it's a proactive approach like you are doing a threat hunt to find threat actor in your
environment but instant response is responsive so how come these two things go in in one one way they have to basically because in instant response threat hunting is a critical critical uh function because what what I do is basically like if you are just going for the known ioc's of the thre actor you might fail because if you see the trend from 20 from 2015 till till now many threat actors have change their tactics like for example Reich rware is now nowhere but they are here in a different name black character somewhere you might not see them few years later but they will be there with some different tactics and if you Google them and say
okay I have the ioc's and they do this this this you will be feeling your answer response you be feeling that so you have to make sure that you T hunt because it helps you find those things which you are unaware about and the best part about threat hunting is it helps you to uncover persistance mechanism because that's how threat actor stays in your network because they want to maintain that that thing to come back in and then again that t hunting helps you to uncover the unknown ttps tactics and procedures taken by thre actor so for example if you see that okay I have hit by a lock bit rans somew and they have this ttps but when
you do threat hunt you find some more ttps okay they do tendential dumping they do defense evasion which they were not doing before so if you go for a known ioc's that will not help you out so you have to do thread hunting so these two two topics are really important if you want to do effective incident response this part okay um it's pretty clear your EDR solution it's pretty clear thing but what happens is that businesses thing that threat actors have been really sophisticated now like really sophisticated and they believe okay why you spend $1 million to have a EDR solution in any way they will come and they'll destroy us because when the thre actors have a
motive to destroy you you will be hit like like there's no question asked that you will you will be hit if they have a motive against you but if you have a EDR what it will do is it will stop the attacker it will make your ins response easy because when head actor will come into your en environment and there's no EDR they can do a lot of things but when you have a good EDR solution after coming to your environment they have to do one thing they have to disable and destroy your EDR and that's not easy they have to do a lot of things and at s for we have seen that a lot and we have seen chats
on dark web where we have seen that actors doing a conversation that can you help us out how to disable SOS we have seen that so your intent is to make the life of thre actor really hard because then you do that we have seen cases where thir actor comes in they see two or three machines it has sofos okay let's go to other organization which you don't have enough defenses and other part which EDR plays is that it ensures a quick and effective intern response so for example you guys are being called for the Enterprise intern response and there are around 4K machines and they okay what tool we have you Google and you have okay we have a
tool called Siler which is a for collect rtor or velocity Raptor or the most famous wicona you go you download that and you run to every machine just imagine that you have to run that tool on every machine it will take take time and you know that there is a threat actor doing the attack and you are trying to collect the locks at the same time you have to be effective that EDR solution will help you in the effective incident response and how you can do that because if you have a good visibility of your hosts you can just run qes in your environment on all those 4K machines and see where is the thir
actor right now where it's heading to so this thing really help this part basically is little controversial that you know it it help you to have the visibility of your environment to to have the unprotected machines but based on my experience this is really really handy here this is really really handy because what it do is that your EDR solution curies the machine and resolve the name to that DS if they don't have that EDR on that uned machine you will see the IP address of that machine or the machine name itself and you will know that okay this is the machine from where the attack is coming so that will really really help you out and doing a effective incident
response so right now you are in your office and you're not HIIT by the somewhere and you are having a very good business going on going on going on but if you're not doing this thing you are lagging behind a lot and what this mean is basically that this Dev exercise is is is all about that you do a dry run of your insant response process so you are sitting in a conference room and someone ask you like okay you have been hit by a ransom weere what what you will do most people will say oh no we are a small business we won't be hit by rent ofe we don't have enough revenue or they might
say you know we have a solid defense we will we we can defend but that's not the answer you you should have you you should have answer like this okay we are being hit by attack we will do this this and this if if you can't answer that question well then this means that you're not ready for the incident and when you're not ready for the incident this means you you will fail so here are the three most popular scenarios for the C of exercise and one which we will discuss right now is a ranse incident and why I have chose this topic because right now you can see that this year Ransom is leading the total attacks happening in
the world 66% and the mean cost recovery for each business is around $ 1.82 million that's a lot of money for a small business or for a medium business there a lot of money here so you have to make sure that you know you take proactive actions by doing the T top and these are the few questions you should ask sit and ask and this is a scenario here that your Company CFO called you and they are saying that you know um I can see that files are being encrypted by something I cannot open that there's a ransom note and I can see that it has some text some bit bit coin number etc etc what should I do like what you will
do and these are the questions uh you would be asking yourself your team that what you will do here that how what would would would be your first course of action can you do instant response do you have the enough resources to do that how you will identify the scope like how you do that do you have the right people do you have the right knowledge about the attack do you have the right technical uh tools to defend that and then is it worth paying the ransom and the most important question in every attack is where the sensitive data is stored because right now as we are moving through several companies in Canada are being hit by vens this week before there
was a company whose data was leaked on the on the dark WB so you have to make sure that where this data decides ask yourself and you know U work out so what I have done is that you know I want to make it really interactive and I want to have your responses I want you to help me out that I am a business owner and how would you help me out in figuring out what should I do if I hit by Ransom attack so if you have your phones please can you gosite m and once you are there I will give you the quotee to enter to log into that interactive
Fest okay the first question and this is a basically the code you will enter after you have go to the website m.com you will see a play option there just enter this code and you will have this question in front of your screen so what will be your first action from this point to contain or minimize the attack and this question is very important because there a First Step the first step and first step if it's wrong then it can be really really bad for you guys so so far we have number two
option decision okay so we have the results and it looks like that once you are being hit by The Ransom weere most of the pupil selected that you will isolate the infected machine that's a pretty good step because if you know that this machine is having some malicious activity going on that mean means that okay I will isolate that but this response is equally good here because you need to make sure that you validate the incident if that incident is happening on your end point then this option is pretty good right you just go get the C out and you and you call your manager that okay I have seen the B activity happening but the same thing is happening on your
servers that is your domain controller or you change server then you can't just do that you have to make sure that you have enough reason to prove your point because because because if you isolate your domain controller no one can log in and you will be getting call from your CEO okay it's time now time to go home which you don't want right so these two options are good so so so so if you have so so if you have a server like domain controller Exchange Server this option will be most viable that you validate okay I can see I'm just activity on those servers and it's confirm that this there is a serious attack going on and I will
chew this part so these two things are the right options Bravo on that moving to the next question how will you identify the scope of the attack and why you should be doing that that question is pretty important because you have to know the in depth of the intrusion
okay so far option two is winning right now we have three options here and I think we have all the answers and option number two is a winner right now so like most of the people answered that what the do is they were logging they will log to their CM might be Splunk or the EDR solution hopefully so force that uh you go there and see okay I can see this activity going on and try to scope the incident and that should be that that that should be every company doing it every company every firm should have this capability that they get can go to their EDR and CM and see and scope the attack but
unfortunately in real world this is not the case because what we have seen that prior to the activity it's bad to say but prior to the activity a firm whose revenues around Millions have not have never ever logged in to their a spun or ADR solution it's there sitting in air conditioner very happy that no one is coming there and then attack is there so in that case what you should do is if you don't have that enough capabilities take the help from the IR team if you don't have your IR internal IR take the help of the external IR because they can be the ones who can tell you that that we have the
enough capability to to go in your environment and see how deep is the intrusion and they can help you in scoping so these two options are the best ones this option is good if you're very small business like if you have six or five machines but the problem in doing so is that here if the person has no understanding of the attack he might say okay nothing has happened and there where you will lack so these two options uh are the best ones and again Bravo on doing that this means I can show that the you people have good understanding of how to do IR okay next question which we have disc discussed before a very very important
question how will you identify if your sensitive data during the incident has been accessed and taken outside your
environment Okay so we have a tie between one and two okay it's
moving I think we have a good results now so let's discuss so before we move to these three options uh someone has put anything else and that's pretty good you know that's pretty good because that person has a better understanding of things which we are unaware about so if that person can you know just raise the hand perfect so what you think is should be the best option here see so that is the right answer here
please yes so yes it will be situational and that's why this answer was put here because sometimes you have the edar with which can you know do this thing but sometimes you have a DLP solution DLP means data loss prevention and that means that every data accessed by someone and Tak taking out can be a problem so these three options is business dependent but this option can be very helpful because why because you might not have DLP on the machines which have a sensitive data so for example let's take an example here a good example and bad one first is a bad one right so you have a business VI the COO the CFO and the cxo they they
all want all the data of the organization on their systems right like that boss I want every Exel sheet on my machine and it may contain most of your stuff what happens there is that you install DLP on two of the systems not the whole environment and for example if that is not being uh installed on that machine that data can be accessed taken out and you will not be aware of but if you have a good EDR solution and you can cury that machine okay that is a file and then the last access time of this file then you can pretty make sure that you know things are covered so these three options are
pretty good and Kudo few foring that okay another question what methods can you use to contain the attack and we have discussed this so I'm hoping we have a very good answers for this
question okay so we have the results and this is basically what I was expecting as the answer here engage your IR team to contain the attack because if you are going for this option then you will be hitting again if you are doing this option blocking the IPS head actors might change those IPS and come back in if you are doing this option uh it might be bit effective but the example which which we have discussed before the triple Ransom attack that was happened because of all these three things and I think we will conclude the presentation now so before we conclude uh I will just share my last slide
so we will do a short recap of the things about what we have discussed that you need to make sure that when you're doing a cyber incident you need to make sure that you're doing it it it like you're a example you have to scope the attack acting up in the incident is a key you have to make sure you have a visibility and run T Tops and I think don't we don't have part for the questions so thank you very much guys like [Music] it