Pentesting Hardware And IoT by Mark Carney

Show transcript [en]
so good morning it's lovely to see you my name is mark I am the organizer of this particular shindig of b-sides and hopefully I am going to show you something interesting so this talk was originally something else for those of you who've been keeping track I forget what it was but a week and a half ago I got some one drop out last night it was Harmon he has an Assessor I'm afraid who refuses to change a dates unfortunately you know he's had to back out which was fine I suppose we find these things happen don't worry about a thing so as well as trying to organize a b-sides I've been trying to also think about things to
talk about instead of Harmon and what I do for a living is I do with I'm doing a full time PhD in maths please don't cry I know I know you say you do maths and people say you must be really clever now sorry I put teabag in the sink and the spoon and the bin and the milk on me head you know it's like I'll get it wrong on a fairly regular basis but aside from that I also work for a security research labs in Berlin well I do a lot of exploration of hardware devices for bread and butter and one of the things that I often find people don't quite get is what is pen testing
hardware so we who's read books articles on hardware hacking hacking hard work oh yeah exactly yeah so what do you do to go beyond that though how do you take it from being I am going to find some hack on a bit of hardware we're just going to do something and how do I make that into an actual attack on a device okay translating like when you learn how to use like medispa you get a shell how do you translate Metasploit into domain admin as a skill that you learn in your pen tester I was trying to bring out the skill level of what's going on in hardware hacking so that you start getting more meaningful vulnerabilities
out of the work that we're all doing and they don't hear actually do hardware hacking as part of their portfolio there are dumb bits of it all the hardware how could I know that I hands up that's fine so about me I said a lot of that already probably professional pencils too I am still a professional Penza I just tend to do more research and I put music degree because I have a music degree so when people were raiding against that poor woman who had a music degree I have one and I think that that's absolutely fine so I do some internet of a pen test social engineering phishing red teaming code of view I do lots of math I like numbers
numbers are great numbers like help me you know security can be quite hard sometimes and apparently you know like this is a screenshot from pollicis or cell labs where you can see that male that live comm only gets a B and people forget that actually accepting risk is a thing okay you can actually go on there I mean either wise Microsoft massive company more than very first you want to attack companies why they get B or because they've accepted the risk okay that's why these things happen but security being hard isn't necessarily that hard okay you spotted it who's seen it yeah there you go yeah that's you know people were like yes you want to
put this on Twitter a couple years ago people were like yeah so you can you can cycle through the oh you idea I'm just like the MAC address is in the Wi-Fi frame so if you can see the Wi-Fi you can just get the password okay it's a one-line exploit so a lot of people kind of bury their heads in the sand you know just sit there going oh we hope no one actually hacks us you know like you know it won't happen to us you know we're we're too small to hack or and no one would bother hacking us we're too big to hack no one would mess with us well yeah they actually you know but likewise you
see some solutions of problems on their way over engineered it's not doing you know sort of web development or assembly these are from the Internet these are great I love these fake Bob Johnson with this therapist so the idea that the idea is I want to sort of get away from you know sort of a very binary view of security you're secure you're not secure it's all relative it's all contextual it's all got other and I'm not saying which we don't think about it is time for example or trust being about terms or not an absolute and that kind of thing so I've come up with what I think is a decent allegory for what happens in
information security Adam interest um who has seen this before no okay cuz I don't you see ya puffin say okay so please don't spoil the joke so if you translate this you might get something like a child of a child is surprised at the market a child of a child o degrees you have needed lazy is he who doesn't go out lazy is he who is not led who cares about the little one all happy with rule again okay that's a fair translation I think it's always okay maybe if I has no one worked it out you know I'll read it out a very stereotypical harsh accent the amputee thumpety sit on a while amputee thumpety
are the greater foul other lacking of success and the nikita some men comport amputee to guide again it's humpty dumpty okay that's all I'm gonna say on that well the number of times that we say things and it gets misinterpreted it gets missed said because of lack of clarity lack of understanding okay so I want to try and get away from some of this stuff and try and break some of these boundaries that we have in security to make it more accessible notice to those coming into the industry but also those who want to learn new skills how do you relativize that to what you're doing in your work okay by the way this talk was
written about half about an hour ago if you finish is quite early there was a devil stuff to hack I'm gonna show you stuff there's no camera I'm really sorry but like I will be showing you hopefully stuff on the screen which will translate to meaningful action later on so the toolkit that you need for hacking hardware is actually very similar to the toolkit that you need for hacking more or less anything you're used to I missed em map off this but in terms of specialist stuff and most IOT devices yeah it's burp suite who's here has used burp suite exactly you already have a hardware hacking tool use don't know okay it's screen mini-com
okay yeah you've used that yeah cool flash phone with a bus pirate yeah yeah but in gdb you open OCD yeah okay people who do debugging logic software from Sally people have used that yeah exactly so you have the tools already a lot of people else you can just go and download them they're free nothing here you pay for okay yes there are tools you can argue are better and that's fine I want to lower the barrier for entry by going you know what you can do decent work in hardware hacking basically with very little actual kind of investment and like hundreds and hundreds of pounds so I'm hopefully going to show you that later
the demo goes completely wrong it's because I am completely unprepared but that's not really the case you also need some hardware ok toolkits well USB to UART converter CP to 102 board for example something like a multi lefty - 3 2h board is like a multi-tool board so it takes lots of things and puts into USB so it just SPI - you must be JTAG - USB that kind of thing and it does UART as well so realistically you could do away with the top line and just get one of the second ones they're about 7 pounds who has dots or used a [ __ ] crow from Zipit er systems yeah a couple so
yeah so that is now that Masterson ft - 3 - chip it used to be about $50 to get into that now it's about 8 pounds of money expressed a bus pilots who's using one of those anyone brilliant yeah they're great fun they don't support I don't recommend them at the top anymore because they don't support the firmware the firmware is now like pretty much unsupportive they haven't said that explicitly they just haven't updated since like 2009 or something no I think it's 2011 or something I think anyway it's out of that it could do with some extra work on it and if you want to get into that it's well worth it a logic
analyzer of any kind of salieri or one of the ones you can get off eBay for three or four pounds and I'll do we know they sell actually really really useful ok you can do a lot with an Arduino who's seen or heard of a jtagulator great who owns one a couple of people yeah you don't actually unless you need that many I owe you anything about Audrina ok there's a phone cord JTAG enum which is a firm ways and put onto it which will just do exactly the same thing ok so you know that yes the jtagulator is a professional tool you needed to get in to find a JTAG the fiery French is actually very very low
cables connect as wires and then some stuff to actually hack so you realistically actually have to go okay so so far we've racked up about 50 quid I think that's fair 50 26 to yours another but of course we have to first of all understand what we're actually talking about what we're doing okay what are we trying to do so this is what I call this isn't the IOT attack surface it will be in a second this is the basic attack surface for most things so you see that you have a user PC that talks to the internet you have a mobile app that talks to the Internet and the Internet is then where the cloud
services sit so you get things from user PC land to cloud services and from mobile app land to cloud services like that okay that's by and large most things fit on to this kind of diagram most things pretty much not everything I understand but all of your API is go over the web Germany now and you know there may be some Wi-Fi stuff going on well we don't really care by that immersive thing so if you do web app testing or in particular testing then you know you you only can really concern with a model that looks like this or very similar to the other my empty device this is what happens it's suddenly much more complicated okay
minimally you are you increase it by at least one of these extra hours minimum because your IOT device has to talk to the internet to get to the cloud services likewise the mobile app may directly interact with the IOT device as part of the attack service so if you add Wi-Fi you have bluetooth you're adding and adding to the attack surface here likewise the IOT device might have a web portal if it says CBE which you could put under the banner of IOT technically then as a CPE sight box and see my premises equipment so anything on Triple Play they need it that way so Reuters TV boxes now TV all those things so IOT device is talking to user
PCs directly maybe on going via here so the Internet to cloud services or they go directly over the inside themselves so you're putting stuff on the internet and then that's talking to a cloud service okay it's a very very different picture going from here which is where we are currently have well where we were maybe five or six years ago I think mostly you know to here wherever there's got a sense of any evidence connected everything's talking to everything else how does it do it well by and large they go I'll put it on the Internet you know and but sounds like a bad thing because it is so I get a pen test on time ago on
a device which is this device here and it was a device and as I started the pen test these devices went into the news this is the TR sixty nine attack which people have told about before but I want to sort of talk a little bit about how it worked these are V the mechanics of the attack but also how we how we were able to work on that attack in sit you with the devices okay I'm hopefully I'm going to show you some things as to how I actually worked out what was going on okay so CPE fundamentals alright they're usually MIPS alarm based whooshes tend to have one of these two okay arm you
see a mobile phones x86 you see on pcs mips you only really see in devices okay II tend not I haven't seen a mix for anything will seeing a mix phone and doesn't never seen a mix Pam I don't to be a Kyle of an RTOS flavor so they'll have a Linux kernel but I actually it's really operating with an RTOS as in it doesn't have an actual storage space per se generally it will have a page which you can manipulate which will be of like a configuration file in this case and then it will load that every time so it loads an image and then it manipulates the image according to the config file
which is more of an RTOS II kind of thing to do than an actual energy system kind of thing to do so it means that you have this weird kind of hybridization of all these different architectures meeting which is why it can be confusing for people when they wanted into Hardware hack okay especially making sense of it or how do you make sense of this when you want to get into a pen testing hardware so often development headers will remain and they have traces and you're wondering to some people say oh this never happens this this thought actually has where's the camera it's there so there won't be a zoom on this bunker just indicate
where is just these little pins just here I'll pre sold it they come on every board that is manufactured and that is the uart port in case you're wondering okay so that they haven't even tried to hide it okay no no attempt to remove the most of them but you'll often see these things and there's minimal restrictions on these things generally speaking why the planning restrictions is hard but you get other commonalities between devices they call how all these different devices how we have anything to go on well some things are the same there you know a lot of devices tend to using I you boot for their actual boot manager okay you boo there'll be different
flavors there were these different structures of the firmware someone use a Jefferson type thing somebody so squash FS that's ultimately bit of googling especially for Wi-Fi routes is there great to learn because there's open wrt hacker forums where you can get loads of information so a good place to kind of learn hence I've chosen to have a look at one here fundamental floors tend to be this kind of thing so you have a very tiny device running a very weak processor which is gonna have a longer time so it must never heat okay I mean and you've got all these things to juggle do you think do you honestly think you can fit an Apache server okay
Connor um and device no okay you will see Linux devices that have dot ASP pages that happens okay and you're like what but generally speaking what's actually going on is that you have bash script running in the backend if you have a kernel with a shell so what do you do we just use the shell to do things so you'll actually find that you have the ability to get RCE quite a lot on especially phone reuters simply because you have this happening underneath miss meterpreter is kind of a thing as i understand what old kernel versions like 2.6 is like a cutting-edge how far see peas you know and vendor maintain software is bad it's very bad everything's terrible
really it's and this is this is even if they use the latest SDK the SDK itself may well be out of I was just part of the problem of this front ability so the common web app phones you will see notice I'm talking about web app vulnerabilities on a hardware device okay because that is actually the kind of thing you can spot on the kind of thing you can utilize and use okay so RC is very common very little filtering off them and if they add it on one parameter they won't add it on its sister parameters elsewhere okay see surf costs that request forgery as you say who doesn't know RCEs sorry remote command
execution CSRF who doesn't know that call so you actually get if there are tokens there very weakly generated and actually rarely check for this therefore like window dressing it's like yeah yeah we would put CSRF token there yeah you don't check it though it's kind of defeats the point I mean you have caustic scripting of kinds you wouldn't normally think is possible okay I have an example of one which is just like what-what and then xxe who doesn't know what xxe is okay xxe is XML external entity injection which is an old old although those vulnerability from the dawn of XML where they realize that you can actually inject entities in and then you could use that to think of it like
cross-site scripting for XML but that's a gross oversimplification that is not to be used in training courses okay but like xxe is injecting XML pages that can then use protocols like file colon slash slash because if you have an XML parser running in a PHP server then you will have things that can cause protocols such as file HTTP SSH and gopher even okay yes good for still supported on the internet for those of you okay because why not have a full house so you see SNMP you see telnet and software versions that I have been quoted as being beyond old and this is actually can you read that on there so this lion telnet D was actually in one
of the scripts running on a device and it was we enable telnet by default for testing spi flash issue that fix was talent D - L been shell bash P so this is running us route by the way because there's no other users why don't you have extra users they take up space this is actually there and then now disable telnet for security concern okay because they realize that maybe having a root shell on port 3 double zero 6 was bad and this is this is legitimate ESP you short out with it if you want another device I'll come up it come with an ask but I won't say it on what was going to
be released clean Internet so what that attack itself began in November December 2016 it utilizes a bug in these last TR 69 so who has never heard of TR 69 T over 6 miles so it's who are those people who doesn't know you PMP ok couple so you PMP is like a dynamic management protocol where you can manipulate the settings of a device so a device can ask for a port to be opened and forwarded on a device through you PMP that's the idea ok you can do that kind of thing on TR 69 is the same thing but instead of it going through a LAN port it comes in from the Wow ok so the actual connection
from the telco it will call out to a telco server it will register itself and then the telco can push data to it updates firm well you know how various route tokyo's like update your firmware automatically on the Reuters that's how they do it ok so obviously this is something that has a lot of power it has a lot of expressivity it has a lot of potential issues and there's been a lot of talks with written and given unspoken on on the YouTube about that ok tiny I'm Tanya you know I'm speaking very slowly as well which is like unusual for me so there's now see in the surf XML input process there was no source IP filtering so it would
just accept traffic you see the device people would just accept the traffic it didn't go I'll accept traffic from this thing either a we just accept the traffic because why would you have filter it because it's a device right you know not like it's doing anything important you know no string filtering into an own RC en point okay if you look at previous fixes on the firmware if you go through the change logs you'll see that actually this was known to be an issue on this particular endpoint and it was filtered in the web front end and then it wasn't filtered over TR 69 and then you actually use so there is a thing called
TR 64 which is the LAN based on authenticated yes version okay because TR 69 has an authentication last year 64 doesn't and if you look in the strings in this binary you'll actually see that it sits in the TL 64 space so it's kind of a UPnP thing that you're actually doing this is terrible this hasn't come up one at all I'm so sorry so the idea is is that the the jerseys around point on the hose seven five four seven is the port and it goes to /ud slash act question mark 1 and then it goes accepts the TR 64 request it's so based okay so there's a little tool you need are some
PHP script remember only which you can just ask for all the UPnP parameters and this one dumps out the UPnP and also the TR 69 parameters as well so it just gives you everything why the same binary file running them all right same binary file for doing local UPnP manipulate request processing it's also the one doing all of the TR 69 does that sound bad that's because it is so enter puter sh is run so uh MTP setting is where the vulnerability is at the NTP and network time protocol it just refreshes every now and again against the time if fresh is a lot actually but never mind so as soon as you update it it'll run it'll it'll
remake the config file and then run it as a script so again what I said there's a wrong so the file is called wrong filed or CFG and what it does is it actually takes the config file and then posit it because I can't follow just X on a lattice point all right yes yes yes what what you just thought yes and then it populates this the shell script with the contents of the XML file for you and then it runs it it just goes you know what I've updated it should probably run this eye and then you get RCE and you can estate you steps and stage allows overkill okay and that's what actually happened in the end so I have
the the persistence lasts because the persistence is actually in the configuration side of the config file so even if you update the Rooter it doesn't fix it you have to update it and then factory reset it but otherwise you're still using the malicious content file because it actually has a bad script in it of course a denial of service in Germany and it compromised some cps in the UK and this is what it looks like so here we have a fairly who's not seen so before okay mostly you see insert that's fine so this is the kind of son the soap envelope you've got the usual soap blooms I mean you got some XML and this
is where the actual exploit went in so this would actually be an IP address or URL or a domain of some sort and then it would say alright this here's the time server and you can give it up to five of them but if you put a bag tick in and then you can just say go to temporary get from this and this was though this is what I'm being used in the actual payload change it to be executable and then run okay simple so simple okay this was and you could just send this over the Internet's to any device you would find who's not heard of Showdown who thinks that showdown will be useful
at this particular moment every house should be a big zalien so like you could just find all sorts of absolute hilarity by just trying to find devices that have a signature which of them I won't tell you whether it is but obviously you could work it out if you sat down for five minutes and just go and find horrible reuters you know and you could do this fairly fairly easily so demo time I see if it's cremated to work if this fails her Bendis Lee I am so sorry hopefully it will okay I'm also missing harvest so I don't see anything below here so I might have to just like resize a few things so I can see it so if you
wondering I think the sizing it really weirdly is he a bit strange I mean we're not that we need to ask so plug this in I'll show you what I do for a living so what we do is we first of all enumerate what is actually on the device and again I've had a close-up camera I'd show you but you've got a long chip you've got a a cage on top ok the cage is just an RF shield okay it's up to interferes and can also act as a heat sink sometimes as well so it's just it's just there to sort of help out on the circuitry you've got power management because you can tell there's lots of capacitance
right capacitors are used I like to smooth out flow a current flow and that kind of thing then also you've got some inductor sort of coupling bits and bobs the Ethernet couplers and you've got a DSL line processing this man okay so it's very straightforward just look at it and go I know what's on that there's questionnaire forward okay now what I'm going to do is I've got to blow some wires onto here and I'm going to show you the kind of thing that you can do with kit that won't cost more than ten pounds so if this goes we will finish fairly swiftly but hopefully this will actually work this has obviously been tested by
so many people for me but ahead of today I spent all of the so let's just show you some of this so I have one of these this is a CP to 102 board you have a usb on this side and you have a little chip and then you have wires on this side okay and this is where the you are is going to go in now I could use other balls I've got loads of stuff here it's great fun having a whale at the time because I love this stuff is great so let's show you how to do was it gone you stole my logic analyzer has anyone eaten analyze what I do very
quickly is just wire this up no problem we should be away with away with what we need to do so I'm gonna try to show you what I'm gonna do to give you an overview while I'm doing this I'm going to talk at the same time so what I'm going to do is I'm actually going to show you how to work out what's going on and the way that you would actually process this so run by mention RCE yeah who's ever written a web scammer in Python and a few people yeah who's gonna what a web crawler even that'll be an easy thing to do yeah exactly put those two two things together they have a web crawler to find stuff and
then you have a scanner which I'll just put a payload in parameters along the URL yeah whatever parameters were to try and find rce what if he went echo string to and then you would do something like slash dev slash t TT y is 0 y TD y is 0 that's the you are Paul and then you can have another script running in the background on a thread this is something I wanted to have written for you but unfortunately besides so you know like organizing it apparently takes a lot of time who knew I didn't like I've no one was more surprised than I was so yes I should be fine so I'm doing is just checking the traces
and where they go very quickly so you can see traces here they're very very straightforward to follow when you have a PCB most PCBs are for voters anyway are two-sided one side two sides the way they get from one side to the other is thing called a via okay so a hole is drilled metal stuff is poured in it's just solder don't worry about it and then you can electric current flow from a trace on top through the via and then underneath okay so keep so what you learn to get really good is going but is the same as that okay like your 3d perception awareness goes up to 11 it's brilliant so I'm gonna try and plug some of this
in see if I can show you getting to a boot log and then we'll talk about more stuff okay because the actual hacking of it isn't very hard from there this is probably one of the less interactive things you've ever seen in your life but then so all I've done is I've just got three wires keep our logic analyzed of an eBay and a few wires onto the headers there yeah what I'm looking for is Rx and TX who's never used you art before okay cool so I'll give you a talk on that one online in these things up so you art is so common as a serial protocol we just call it serial by and
large okay your hippie always a serial port well actually there were lots of serial protocols there are many and multitudinous stereo protocols but this one is so common that actually we call it Samuel by default okay other variations on rs-232 us IAR tu yeah you startled us art which is just steam it's a variation I won't go into details you know doesn't really matter so what I do is I show you how to get the UART out with a little bit of software called logic now I my PhD is in mathematics and I do a lot of logic and what I want to do is just go to software because I have a nice organized structure like that and
what logic tada okay there we go you'll be seeing this again by the way I think David Lodge is going to use this in his demonstration as well this is a very common bit of software okay you guys you buy the software for free so buy the software for free someone get me a coffee I need the help okay you can get this off we can download it for free and then you buy the hardware from them but actually it's compatible with other devices as well so buying a cell a logic analyzer they are brilliant they are worth the money they truly are however 160 pounds might be a little bit intimidating you can get going with all
other cheaper ones and buy a popup on later when you realize that you need the features okay okay so let's get this running so the way that this works is you set a sample of it I'm gonna go for eight million samples a second and for about 20 seconds and what I'm gonna do is set this running first start and I'm going to plug it in with it already powered on okay and when I do that you just wait for any sentence if someone can play the countdown theme I love it but we're having haven't given off notice for that so do that I'm always doing now is it's just Ching we can collect samples okay and then it's going
to give us an analysis off that so who's never seen anything like this before who thinks this is wizardry okay cool it's not wizardry it's really easy it press Start and then you wait 20 seconds so there we go we're done oh yeah and we need to publish them out doesn't look very exciting in the moment but if we zoom out oh oh what's this okay all right so who thinks this looks interesting yeah so what is this what's going on here so what we have is little snippets of data you see that there that's a digital trace that we will be through so so what you'll do when you go and read up about stuff and others are
gonna talk about this today I'm Jude Tammy and David Lodge and pentose partners are both going to talk give talks the CFP was done completely blind and then suddenly I had like a couple people from bet from the same company talking and it was like oh you guys are coming but yeah so in terms of how you are works it's really easy it whole time then there's a start bit which is low because that's how you tell the difference because it's digital okay it easy digital ones and zeroes then you have a defined number of bits and then it goes back up again so as everything is usually ten bits if you don't have parity bits okay start bit
stop bit um data in the middle in the sandwich all right I also we can see here we can see is health hi we use here dips and it goes along a bit honey goes up a bit I think goes down I think goes up it goes down and what you can do is you can actually work out its what the board rate is which is what you need to do for you well because you aren't notice doesn't have a clock signal okay other say the protocols like SPI or debug signal debug protocols like swd or JTAG they have a clock so what happens is there that when the clock signal is going along you have
a rising edge and a falling edge and so the the internal circuitry would read the rising edge or the falling edge depending on how its wired usually a rising edge and that says oh I now do something and then a falling edge and then a rising edge again so it doesn't really see the falling edge it just sees a difference okay differential and when it's doing that hey that that will then regulate how the internal machinery takes over so it's like changing the length of the pendulum or changing yeah changing where the weight is on App Engine I'm on a clock would make it tick faster or slower because the clock relies on the pendulum you can't change the pendulum
you have to already assume time unless we had to do with you with you arms what that means is I have to work out how fast it's running thankfully there's about twelve ways of doing it okay and that's it so what your so let me show you how you actually do that right let's make this meaningful so I can do analyzers so what I'm gonna do is I'm going to take an analyze I'm going to add an analyzer oh oh it's already got one here okay let's use this edit settings so we're gonna put it on to channel what is it channel to I'm gonna guess so the most common baud rate for things is
115 200 the next most common probably nine 600 and after that 57600 maybe and then you can argue like the the hit table after that okay but generally you actually know what you're doing how do I know this what magic how was I born knowing there's no I just googled it you know like sorry to be anticlimactic you know it's just all on Google so I put in a 10-1 which is the 8 bits for transfer you guys you have lots of options here one stop bit maybe it's one and a half or two stomp it's okay I mean you have no parity bits or even nor odd parity okay because different systems do it slightly
differently so actually this has a full analyzer and what you do is you go save and you'll see here can you see this down here you can see but it's working out letters and things so if I scroll oops trackpad master so if I go along a little bit come on give me something yes you'll see other traces don't worry about those I'm not interested so you're being a little bit blunt about it I scroll down here you'll see anything can you read this it's readable w there you go wed APR 2016 ott many people they're just there can you read that yeah there you go that is the data from the system what that
tells me is that so I actually can tell from here which channel is doing what okay I can tell you how well it's doing it what health but we won't go into that immediate so what I'm going to do is I now know that channel 2 is sending data you might say it's transmitting which means it's TX one of the others will be receiving that's our X pro tip UART is the only one that does this and it winds me up knowing TX goes to RX RX goes to TX as opposed to all of the others in the world we have master out slave in master in slave out because they've all undone the things like things connect
okay little things that you pick up as you go along you because you miss wire it and you set fire to us people not that I've ever done that because that would have been unprofessional I'm sure so I'm just a wire this up and just show you kind of what what I'm doing kind of with I can't physically do too much when I fight but we'll certainly give it a go so hopefully that from now are you there let's just undo that undo these so I'm gonna take off so the channel zero here isn't doing an AA kill they didn't it channel to it's the fun that is 0 1 2 so that was tier the transmit wasn't it so
I'm doing some wiring that on to the RN so I wanna kinda have a look at this later please do that's absolutely fine I'm also gonna wire up the ground because I've worked out where that is as well who doesn't know why you would want to worry about ground okay cool so ground is important because it gives you the solid reference I think to watch out for ground loops you have a heard of a ground loop going Google that and then you go on the YouTube video if you think they're not that great but yeah so you have have the same ground because you'd have slight differences in voltages remember is a digital signal but after a
threshold the thrush so their base voltage is different then either it just sees one alright or it just sees one kind of I think not sure okay so just getting the same common ground is a very good idea alright if you're not having much luck with it look for the ground okay as long as I normally show like how to use a voltmeter to find stuff and all that kind of tasks but I'm short on time and also it was this was all done in about 10 minutes so and I would never take this very carefully using the space that I have speaking out loud any questions on this so far no it's fairly straightforward okay so this
is where that analyzer comes in handy so those are the analyzer gives you so there you saw a trace and you saw me put the analyzer on and then you saw that it gave me data and the way that I got it was because it's an async serial asynchronous serial connection which is if you are not sure that's when you start looking doing basically integrated circuits to firing okay and you just start googling all of the chips and trying to work out what they and ideally getting data sheets because data sheets have pin outs and pin outs me advisors okay so this is not the jokes I'm a hacker okay calm user bonus right so let me
just close that and whoo this is really easy so far yeah I called it not too many people are completely bamboozled what I do now is just reset busy so now it's all wired up the USB is plugged in don't get the message it's all the CP to 102 chip is now close to us b0 okay and this is now the easy bit so it's sudo who can't see this by the way how many problems okay cool sudo screen I don't need that one five two hundred as the baud rate slash dev slash TTY USB zero bastard right now nothing's coming out until I do oh don't terminate come on come on oh look I've got the one way
around aren't I ah no directory yeah that's why sorry this is what I do I like sort of swapped sites in there badly and then so they can work okay that should now there you go I'm compressing it you see it so this is called the boot lock by the way I'll walk you through what it's doing so you saw it uncompressed the image and it's loaded the image and now it's going through all the processing to replicate the configuration to set up devices and all that bits all bash scripts which can be manipulated potentially alright a lot of it is comes down to this kind of stuff ok there we are look at that no
such device yeah it's having a bit of a bit of a car isn't it so let me just restart the device and just show you of a couple of things while we're here I'm not gon knock txy I didn't have I really hope this is to you so I'll just gonna find my USB is it okay let's leave that for them fundamentally this is what this is what when you say when you see a brutal loading really slowly this is why it's doing all this okay this is I think this is you boot it said they're sitting there and it's just going to scroll through we'll get to the end eventually can you see the well it's
not got to Wi-Fi yet okay so see here they said press ENTER to activate the console if I when you work at which which of the other two pins is T X right you can then get a root console like that applause but like so this is what a lot of talks finish they could have phoned how who this this is a viable attack you're wrong I'll tell you why you're wrong in my view if I can get into someone's front room with a soldering iron object analyzer a laptop and do all this that you've just seen me do all right then something else is wrong this is another tool this is actually the barrier to
getting into Hardware pan testing I think because this is like units alone the protocols it's another layer now we're [ __ ] just like we do normally you know you can now hack this just like you do any other server you can do callback shells you can do everything you need to you can write to a console you can do stuff right just like you would but that's how to think about it I think all right because let's be realistic you're not gonna get into people's living rooms into Politis but you are gonna be able to find use this to find other vulnerabilities okay it's through that kind of thinking that you actually start to admire bits
and bobs of design of certain devices and one of my favorites I was gonna do a slide but I forgot because besides one of my absolute favorites is the Amazon - button I love the Amazon - but why it's pretty secure yeah I think so I'll tell you why I think that that button Hugh brass is wired into the power management the device isn't on a device cannot be turned on without someone actually pressing it okay it is an arm for seven and a half seconds in which it connects to Wi-Fi and then sends over a web request and then shuts up that's it right there is no way of getting the device to turn on
remotely because it's wired into the power matrix alright so if you are gonna make use of an Amazon dash attack you have to be there exactly when they run out of product and press the button and then record that seven and a half seconds of Wi-Fi because otherwise you're not going to get anything out of it so is the Amazon - a viable target like if I could camp outside someone's house on wait for seven and a half seconds worth of traffic from Amazon - button there's lots more I could take advantage of okay I can just there's so much more I can do alright so in terms of this one let me buy where that divides into your threat
models relativizing to what you're doing this is how that this is how we think about security when we're doing pen tests why not for hardware as well and try and bring in this relativize this idea that everything has a context and has a threat model that we can actually work with so let's see if I can get this to connect - is it there there it is I think I just choose any one of the I'll choose number I'll do that one and so we should connect to this let's see if I can get the exploit to work while I'm here interneurons so I'm just using Firefox here and you can see in the background I have it's gone ah
something's done something okay that's just me connecting and it's putting a little bit of debug output that's not very interesting so things soever not found if I give it I don't say that oh my god what's the password hey you care if that was hard hacked clearly so this is the kind of thing you see day in day out so this is just showing me that the device is actually online okay now I'm going to do something which you never really see of course now you see all the time there's a little Pernod jar what like a spell jar I will eventually load a jar file but free everything is the free versions you don't need anything else why would I
use the expensive one you know when the free one will do okay and in a Blue Peter moment yeah here's one I made earlier okay who can see where this is going thank you skip out to this so now you're familiar with burp yeah good that's just what I am my own worst enemy Hydra of extinction making customized disabled why is it single at the table ah there we go don't wait yes I know stressing me out everyone's watching stop it I thought we were safe anyway so this is the fairly standard stuff that we see in cept his arm I don't really care what I'm gonna use this for is just to get a question
to a Peter okay so this is now going to go here and then just going to tweak this to go over the right port which is seven five four seven seven five four seven okay so here what I've got is a command here but I'll just try and see if I can get this to actually go echo test now this might not work he says qualifying everything very carefully TTY is zero if I remember rightly okay so now I send this what do we get to engine okay okay that went through and if we're lucky we got that PC that test now that's a hack I can very much kiss are there any questions comments
queries yes exactly and we're seeing that the cost is reducing yourself as well which is really really good so now like I mentioned about the liquor from zippers assistants I remember tweeted it out and Steven really who I think is lovely I've only kind of semi been in the same room as him once but like a he sort of sort of to to pack to be going why why don't you why are you lying to your users because he thought I was making these things like I was having them made and selling them like obviously it can't be eight pounds because the cost of learn like we had to do this and I'm just like really sorry
but actually this is someone else making it engine gen all right and he kind of then went oh cool hey guys look at this guy found like we are really pleased that I'd show the cost is coming down you know you can get here this is out I just shown you an RC e there has been practice as an old firmware version as well by the way so like it's it's it's kind of been deliberately set against but like this is exactly what you do now here's a thing which I wants to have ready but unfortunately half done you can actually have two threads one monitoring PI serial over you aren't and one just sending our CES and just
fussing that way and you can find if it fires if you get a hit it's an RC done dusted no two ways about it it's an RC e I I mentioned CSRF yeah I'm means I can have a payload in a browser that will fire to a known IP on mercy peas that will then do malicious things with an RC e through that pivoting that is cross-site request forgery okay like that's the way to think about this your web attack knowledge actually is really useful in your hardware hacking why everyone's using a web api okay gentlemen is there Balthazar Martin there's a some brilliant work and Fabian as well you presented it was a deep sack
on reversing a binary protocol you know which is brilliant work actually fantastic but sometimes you don't need to actually a web as a website API will be enough you know it's actually much more straightforward than people give it kind of credit for you know like I missed up it's very accessible and the thing is do you think that they have a SLR you think depths of thing and MIPS no it's like hacking in the 90s again okay so this stuff is actually really good for learning you start learning new techniques learning the stuff that we we fixed over the last ten years on PCs but also gives you an idea what we need to do next
any other questions comments queries yes
yeah absolutely I mean most of all meters now yeah yeah exactly is a superb way of pleasing your neighbors and really get along with it you know but like that's the thing so like I'm people saying so how do you identify chips it's actually really easy I put scotch tape over it and it'll show you the chip ID if you can't see it immediately oh yeah it's a bit hard to get to or you know that isn't working very well chalk dust Club some chalk right brush it off and it'll sit in the grooves and you just read it out like if you look on my Twitter at large garden I'll share myself emotion it's like I have pictures of me doing
some of this stuff and what I do is I put choking because it comes out so beautifully well really clear you know there's no mistaking that that is a best team that you do have one three cat6 for example how do I know coulda says it any other questions about this stuff this is all kind of stuff we're building on there were lots of courses and things to show you how to get on with it this is a simple example this CP 202 board is literally two pounds on ebay right now okay the logic analyzer is about maybe between three and five pounds depending whether you're gonna willing to wait for it to be shipped
okay little bit of commitment get it get a reasonably decent voltmeter maybe you know mama don't let go and a good set of settings you know and then you can find RCE really easily see what I did there kind of whines so there's no other questions I gotta thank you very much for your time any other questions no oh yes that is a really good question so I have I so I actually have lots more slides which I got a couple from other things but I wants to get that demo done to show you the the blue team side of it is really hard because you can have so I've done work recently on the Arduino
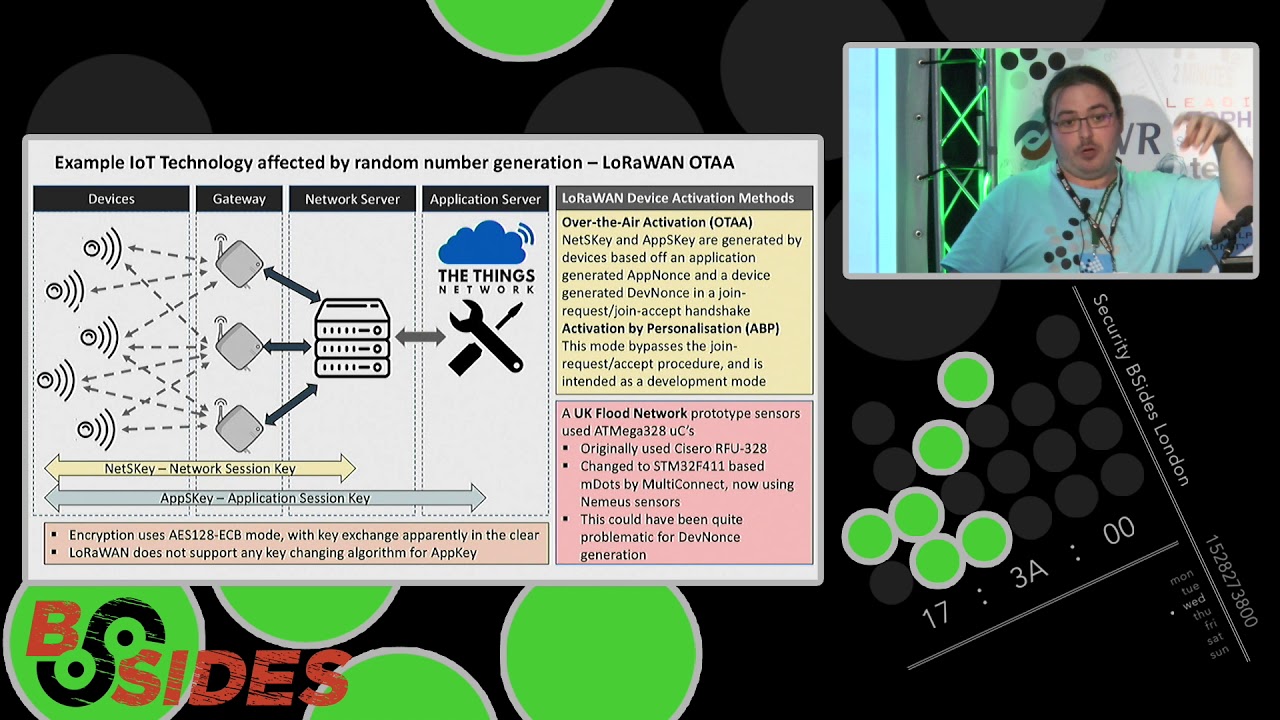
random number generator for example which is a bit crap and the issue you have there is that okay use the latest SDK that a fault on a number generator is an LCG from the Liberty which basically means you can go through the entire space of random numbers in about 20 seconds on the nights 86 just in case you're wondering what that means and that is the default on a number generator because the SDK says so so you go right Thapa crypto you gonna lose lip so don't live hydrogen alright and you implement that on an Arduino and you generate numbers you're still or the generate crypto keys you're still not having proper randomness at all because
you can predict exactly the sequence of random numbers so the problem that lies at so many levels because you have chip manufacturers that don't have a SDKs that means that the developers then can't use the latest software the developers then also might get a bit lazy possibly in something right and then the problem you have from that is that things generally just don't get fixed so this vulnerability is very similar to one that was actually patch and this should have been patched by Allegro soft who make the one-pager firmware but it wasn't because someone didn't renew a license they fix this in 2009 or 2011 or something and it was still in the wild in 2016 like you know
and it's because you have these supply chain issues that like it's very hard to defend against and now we're seeing IOT devices being connected to more and more things so for example the caller Dale Valley flood defense network is on things map right now that could be absolutely fine but if one person writes bad crypto then you're effecting a flood defense network there's a story of a guy who wrote and was injecting Mal data into a zip beam network for controlling his neighbor's farm in California so his name had a farm with all these intelligent sensors and we do exactly the right a more amount of water in the exactly the right place and the story
goes that I come from this in a newspaper but I've had two people telling me to be some apocryphally true but like they'd Mal data was injected the crops were over watered and he not only lost his crop but he was also fine for overusing water because that bit of America's a desert you know and they said that if you want you know very real costs and very real effects that's a farmer who can't make food that's not good this is why we need to start opening up like how to do this stuff for people to access it and start doing it themselves and then we can start doing what we've done in other areas attack you just find
the bombs and fire and find ways of fixing them or mitigating them or compensating controls or whatever we need to do right they are your nicknames boyfriend pentesting security go factory design the PCB tech test pins out
but he also have other things like am I here released Wi-Fi light bulb was it and that also like a her name one port running and it was actually pretty well put together you know it was wasn't too bad why they're gonna be here in ten years you know there's a lot of rushing to market we've got to be the first because to do all this which doesn't help yes it's not yes you could say that all there should be training we should be all these resources and I absolutely agree one of the things I do as much as I can who's at the presides party last night that was organized thank you and that was all helped organize my future
labs which is a startup incubator the way that I know them is I just go along and give security talks I'd like everyone here who is a security person to go into the same thing for your local startup incubator they can't afford a pen test if I start up and drop fifteen thousand pounds on a pen test they probably got too much money okay all their in Bitcoin alright you know like you can just go along and just give a talk they'll happily take you a lot I'll let that die I'll happily take you along and they will value it so much you know is trying to change the culture of a start-up as much changing cultures of
companies like this the supply chain issues but there's so many so much going on so that's not gonna answer your question I'm aware I'm very sorry that's like it should helpfully illustrate just how far these things can no okay let's leave that there thank you so much for your attention you've been great thank you [Applause]