BG - The Dark Side of TheMoon
Show transcript [en]
thanks so much for everyone for coming to our talk for Dark Side of the Moon so just really briefly uh we're with Lumen Black Lotus Labs I've been with the company for about two years now as a threat researcher primarily focused on uh crime Weare type bot nuts so um basically your emot tests quack Bots trying to map out their architecture and trying to understand kind of who's behind them my name's cud I work for Black Lotus layups 2 I'm the reverse engineer and I help lead up the crime Weare side of the team I've been there about 5 years awesome so just kind of a little overview of kind of what we'll be talking about first um just for anybody
not familiar with talk about Lumen and kind of Black Lotus Labs as a whole then we'll get into proxy services and how they're used they're actually kind of rather abused but we'll kind of move then over into the actual Moon malware and kind of do a deep dive into how it works and kind of what we started noticing then we'll move into kind of the faceless infrastructure so the actual proxy service understand where users who are using the faceless service are coming from and then we'll go into we tried to um disrupt the moon and faceless and tried to take the whole thing down and we'll talk about what happened how did they respond and kind
of what did we learn from that so uh for anybody who's not familiar with uh Lumen kind of the easiest way to understand uh kind of what we do is when you think about um how data gets transited across the internet um at some point whether you're talking to to somebody in a different state or a different country at some point that data is going to go across some form of physical wire and as you can see from the chart those blue lines um we make up a large portion of kind of the internet backbone as a whole so from that we have a lot of asns and isps that peer with us and that we peer with so we
can see traffic from all over the world and this helps us especially for um threat hunting we can see you know IPS ports where people are talking to and metadata like that so where black lotus Labs comes in is where a threat research team for alumen so we primarily focus on our netf flow data and hunting anything from crime rot Nets to apt groups to novel uh activity that is unknown so just so we can all kind of get on the same page um when we talk about bot Nets um bot Nets are just a group of devices that all kind of serve a common purpose however botnets can be broken down into subbot Nets so for
example you could have a botn net where one part of it's doing scanning one part it's doing Espionage one part of it doing something completely unrelated but they're all somehow connected um obviously B Nets generally gathered through malware some form of exploitation and then they can be made up of multiple different device types they can be gathered through fishing they can be gathered through exploitation um you name it one of the interesting things to understand about bot nuts though is um size doesn't always matter it kind of matters um what sort of botner you're trying to make so let's say you only have 10 Bots and you're trying to make a spotnet that's not going to work very well for you're
going to need a lot more but if you're trying if you're an AP group doing some form of Espionage campaign 10 Bots may be perfect for you so it all kind of depends on what your end goal is so this kind of leads us to um talking about proxy bot Nets or uh if you're actually going to try to sell it maybe call it a service instead um so proxy botnets excel at a few different things one is having a large pool of devices um kind of scattered all around the world world so if you think about proxying um let's say specifically for these criminal Services um most of the time let's say you have uh credit card
credentials and you're trying to use that somewhere um and let's say your credit card is based in Las Vegas you'll need a proxy that's going to come out somewhere near Las Vegas so if you have if you make a proxy bot up but all the IPS are located let's say in Italy well that's great if your end users are trying to get to Italy but if they're not that's completely useless and won't be helpful so you need your IPS very spread out the next is you'll need a pool of infected devices to remain undetected so this is they can't be all blacklisted or nobody's going to want to use them they'll never get pass any
endpoint detections um another kind of crucial factor is who are you going to sell to so if you make a proxy botet you kind of have two choices one you can sell to kind of end users like you or me maybe you sell by the IP maybe you sell by bandwidth or you can create a bot net and sell the entire thing to let's say an AP group or some form of group and just basically let them take it from there uh the next important thing is no IP leaking and this is actually in both directions so obviously a proxy or a VPN um you obviously don't want your own IP leaked but from the operator side if
they're leaking how they access how you can access the proxies well any user can basically figure that out and then resell their entire botnet almost for free so they need to make sure the IPS are bar disconnected from each other between where the actual proxy is and the end user and the final is you'll need constant regular additions of new fresh IPS so you can't control what your users are going to do with these IPS so one of them might decide to just Mass scan the internet over and over that's going to get blacklisted really quickly and basically unusable so you need to have a way to constantly be getting new IPS so kind of to summarize it out proxy
Services they'll have really clear um kind of terms and conditions of how your bandwidth is going to be used how it's used and you can opt in or out of it versus proxy nut you have no idea you're even infected your bandwidth is being used and you're none the wiser um and as you can imagine there's a ton of gray area in this so actually really recently um there's a proxy botet known as Cloud router and Cloud router had got to about 200,000 to 250,000 and the government actually just took it down about 2 or 3 months ago and the way Cloud R gathered their Bots was through a free VPN app and basically buried far deep within the
terms of service they basically said hey we're going to add you to a peer-to-peer Network um but nobody would have actually read that um so nobody knew they were part of it the government ended up taking them down and arresting the operator behind it so in that case for the free VPN clearly the government thought that fell in the category of malicious so you can imagine there's tons of services that fall in this really weird gray area of are they truly malicious or are they actually a service so this kind of gets us into the ual faceless proxy service so there's a few uh proxy bot Nets that are powered by maware so you have things like sock
escort NX and faceless I'd say are the three biggest um faceless grew out of a service known as isox which started in 2014 and that year will become important when we move kind of over to the Moon um it's always been advertised only in criminal forms you'll never see it advertised um by kind of benine users and up until our publication it was long speculated that it was primarily powered by aware but nobody knew how or kind of where they were getting this from so as you can see from the figure on the left um that's kind of a brief overview of just kind of the structure of how uh faceless looks from um a bot perspective
and one of the really interesting parts to take from that is faceless is located in 188 different countries so at the beginning we talked about you need a diverse pool of proxies um they clearly have it so you can basically go anywhere you want with the faceless service on the right picture you can see basically what'll have and if you decide to buy an IP an IP will range from you know 50 cents to $2 depending on how brand new it is if it's blacklisted and things along those lines so you'll basically have a way to use it and then hopefully um the user won't be able to backtrack to actually figure out how to
resell that so when it comes to um our netflow data we have a ton of data and our goal is um finding these type of botn Nets in the wild so kind of how do we do that um given our massive amount of net flow data we can see a lot of communication so we can develop puristic and different methods to basically try to figure out what's suspicious or what's kind of anomalous activity so you can think of an easy example is let's say you know yesterday 10,000 routers based in the US all just started talking to a Russian IP well that might not be malicious or even um bad necessarily but maybe it's something we want to look into a little
more just to understand exactly kind of what's happening and basically this approach can be extrapolated to as far as your imagination can kind of go in terms of what you think is suspicious this will kind of bring us down to a small population where then we can do some manual research to look for True positives and this is actually how we kind of rediscovered the moon malware was reemergence so the moon's been a proxy botnet um that was first discovered back in 2014 and if you remember from the previous slide isox is a proxy service that also started in 2014 um turns out out that wasn't a coincidence um Lumen uh tried to disrupt this bot nut in 2019 um and after that
report there was no real talk about what happened to um the moon or anything so nobody has really um known kind of what it's been doing but it's been in action for about 5 years since that um so this time we actually hopefully figured out exactly what it was doing all along so then we found a sample that we believed was part of the facelets network but after analyzing the sample it turned out that it wasn't the C2 IPS that were embedded in it oh sorry let me go back the first stage the sample decrypted the the second stage which actually turned out to be the moon and once it was decrypted it would execute
the binary and set up some firewall rules to block Port 80 and 8080 probably to prevent other malware from infecting the device so it also contained a list of three hardcoded c2s and those c2s were not faceless infrastructure or known faceless infrastructure it it also from reverse engineering we saw that the malware attempted to contact the c2s on this port 15194 and then if nothing was returned it would send another hardcoded packet to port 16194 and then the binary also had the ability to download and execute additional files so we went ahead and ran it and we got a response on the port 15194 and it returns some data and then what looks like a file name and then
that file name would be requested again from the C2 along with another number we're considering a version number we're not exactly sure what it is and then so that would download and execute these socks files so what are socks files we don't know um we received six different files they were basically the same there were two offsets that were different in the files one was a hardcoded C2 and the other one was a replacement for those hardcoded c2s so those um those those c2s weren't active none of the c2s that were in the socks files were active so allowing the malware to continue running we get an additional file named Socks t and this sockt creates a binary file
named Sox dotw and this file contained a bunch of binary data that was read from the previous files and this data is the c2s and you can see here they're they're all the same it's in this case it's 19531 143 7.73 and this is a known faceless C2 so connecting to the faceless Network the Soxs files will reach out to the C2 it from theox dotw file on a random Port between 4210 and 4217 um and then it would send a hardcoded packet and this would just go on and on until eventually we received a another C2 that would be reached out to by the malware again and this then this C2 it would reach out on
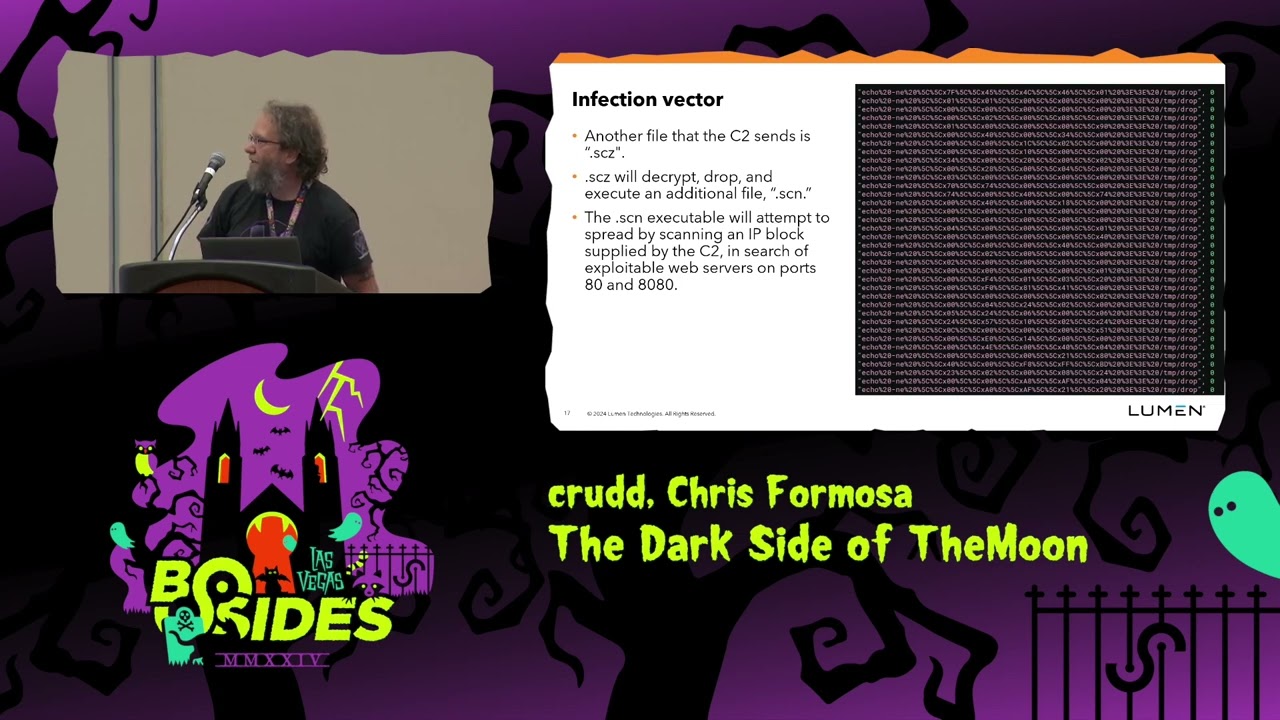
Port um 5010 to 5017 the same random Port chosen by the previous uh previously and then the same the new c2s it was the same IP in this case will respond with a domain and a port the proxy to and you can see that going on going on in the pcap next to it and another file that we received was a scz file and this was set up the same as the Main Moon malware and decrypted and it would decrypt and execute this scn file well the S CN file was would uh attempt to spread by scanning IP block supplied by the C2 in search of exploitable web servers on ports 80 and 80 80 and you can see that in the
screenshot next to it where it's actually that's the exploit that it would use to infect the um iot
devices Sher said so now from the malware aspect we knew um these two were related but now we had to figure out just how much the relation was so from the top left chart um that's stay from when we saw a moonbot and then how long it took to actually communicate with a faceless C2 it actually 80% of moonbots would communicate with a faceless C2 within two days and keep in mind that we only see sample data and not all the traffic in the world so that number is likely 100 and then the other part is the inverse relationship is true as well so not only are most Moon Bots becoming faceless Bots but also almost every
faceless C2 is around 80 to 90% made up of moon bots so basically the Moon is the Sole Provider of bots for faceless and faceless is solely taking Bots from the Moon um they're kind of a hand inhand relationship or at least they were up until our action so the next interesting thing is faceless has a really interesting architecture so from looking at a bot perspective all the Bots will communicate with the exact same Moon C2 there's only one Moon C2 in total and all the Bots will communicate with it but uh there's multiple different faceless c2s and a bot will only communicate with one in its lifetime and it has a very specific purpose so for example uh all Bots from
a singular ASN communicate with one faceless C2 and this is basically all the devices in the SSN are basically old end of life devices so clearly they found an exploit and took over basically the entire ASN we have um if you remember the worm file that Steve talked about that's basically anything that gets infected through that worm file is going to communicate with another faceless C2 they set up one solely dedicated to Asus spots and what's interesting about the Asis spots is that it doesn't appear that it's only end of life devices so it's unclear if they have multiple different exploits or how exactly they're taking over so many different Asis spots we saw them take over over
10,000 within I think it was 72 hours so so um clearly they have a range of exploits for it another one is that they basically set up their own scanning infrastructure in that they have servers that I set up to basically they have vulnerability scanners on them and they also set up FTP servers on them so basically they'll scan for different vulnerabilities that they have and then if they find it they'll basically send you to their FTP server and then anything that talks at FTP server is seen becoming a faceless C2 shortly thereafter so kind of moving into the actual faceless service um so now we know the Moon is the proxy botet behind it but
now we kind of want to understand um how exactly was faceless working and what can we do to kind of disrupt it so when we look at how faceless Works basically it'll start with uh somebody like you or me is kind of the end user and then you'll either reach out to one of two things you'll reach out to the actual faceless C2 which is a weird choice for them to have users directly contact it but not my decision um or you'll reach out to an intermediary node which will then that intermediary node will contact basically push the data over to the faceless C2 the C2 will then reach out to the faceless spot and then it'll go
to the end Target and that way um the pipeline's very appus skated so no IP leaking would happen um but what's really interesting about this pipeline is that only about 25% of the end users are coming from hosted IPS so things like T um a VPS so we actually think most people who are using these anonymity services are coming from their actual address they're not trying to hide themselves really they think these services are extremely secure for them we see an average of around 7 to 10,000 distinct IPS uh per week that are contacting this service so that's likely at least several thousand different users every single week are using these tools so um they're very popular um
services so uh it's well been speculated that faceless is always cated to cyber crime but there's never um really been tooo much proof about that so one of our goals was to try to figure out could we see if like does it actually c a cyber crime outside of posting on criminal services so when we look at um when we remove all the hosted IPS and the tore IPS we try to figure out um who's actually connecting to this service so the top six countries make up around 90% of users that are contacting um this service and we have a data bias towards the United States data so the fact that it's only 25% is actually quite small
that then when we look at the rest of the countries that round this out we have Nigeria South Africa Ghana Russia turkey all areas that um can sometimes skew higher in cyber crime or cyber fraud related activity so this does kind of line up with if this was a completely benign proxy service we would likely expect many more countries to kind of round this out but given kind of the countries we see this does line up that it's catering to a specific group of people and likely focus more on cyber crime and cyber fraud related activities all right to the fun part um so we tried to disrupt the Moon on August 26 um we
know routed the entire faceless pipeline we know routed all of the Moon infrastructure The Faceless infrastructure all the intermediary c2s everything we could and initially it looked like it was going really well we had about the service went down about 70% of the total Bots had completely disappeared from the service and then shortly thereafter as you can see on the right side the entire service went down um so we were pretty excited for a little um but that was quite shortlived uh later that day um the entire service would come back online at full strength um which was quite confusing to us um but when we looked at it a little more we noticed only 30% of the original Bots
were now part of the faceless Network so basically that 70% that we kicked out they somehow supplemented a new 70% of bots within I think it was 24 to 48 hours um so what happened um so before we know routed uh faceless they had an average of about 50 to 60 devices per IP that were being used um and this was quite common for multiple months before our no route then right when we no routed almost immediately they jumped up to about 100 so IPS or devices per IP and as you can see that number kept creeping up all the way through June to where they had about 170 devices per IP when you get into this range of
devices per IP likely what it means is you're starting to deal with a lot of mobile devices so a lot of mobile gateways a lot of devices are coming through so what most likely happens is we took out a large portion of their Network and they somehow found a large either mobile bot net they had or maybe they found a reseller and they were able to get tons of mobile IPS really quickly to basically supplement our entire effort and as we notice in July um they finally uh created a new moon C2 so from the one we know routed they finally made a new one and lo and behold their numberers started dropping immediately is they started likely getting a lot of
the devices that previously we know routed they started getting them back uh so kind of was our no Rod a success um partially yes partially no um so we did clearly um remove a lot of bots from The Faceless Network which was definitely a good sign um the thing we really underestimated though is just how much of the botnet they were going to be able to refill so quickly we um did not expect that they'd be able to find another botnet so fast or another population so kind of how do we improve this for next time um one of the big ways is um when we no routed them they kept all their same architecture even
though we took out like 70% of their Network they clearly were in kind of phase they're affected by that so we would likely need several more partners with us who have the ability to basically cut the kind of paths for um these Bots to go through and it would force them to change architecture get entire new Bots um so that's kind of what we're hoping in the future is we can partner with a lot more entities in order to do a lot more damage to these type of networks and yeah if there's any questions we'll be happy to answer
them yeah oh sorry I do have a mic here um so I'll be running around if you do have a question raise your hand up high and I will come with you with a mic who are you hoping to partner with you to take down the botnet um yeah so basically people who have the ability to um disrupt internet traffic kind of at scale would be extremely helpful so like Lumen um going back [Music] to going back to kind of this network map so when we know out we basically stop any successful communication from transiting across our wires so other um large isps or asns that have kind of similar networking if we can partner
with them especially ones we do very well in the US but especially in other countries and other areas um the more Partners we can get the more basically we can cut off traffic from all sorts of areas so if we all do it together um we could likely take down not only this botnet for example but a lot larger scale ones that are even more spread out
sze can you say that
again uh not directly um obviously we have some Transit lines that like their data like that's how we could see the users are coming from there but we don't have like specific Partners located there do you have a contact mechanism or an intake if somebody does want to reach out or an organization wants to get a hold of you what's the best way for them to be aware of your intent and try to get a hold of you if there is a front door over uh yeah definitely here um come talk to us and we can pass our info we would love to talk to anybody Twitter oh yeah Twitter too um black lotus lab
is that our handle Black Lotus lab yeah Black Lotus Labs on Twitter but definitely uh anybody come talk to us if you're interested in um yeah potential partnering or if you could help at all um we'd love to talk uh yeah
definitely when you saw the big spike in the uh traffic where it was obvious that they brought in not to say another Network potentially but they probably got it from someone else any chance that where you were saying it was mobile did you see any iot stuff or uh I guess other Internet connected devices being used in that or if it was discernible yeah so considering so one of the hard things was um considering we know routed them from our infrastructure and they didn't change architectures we couldn't see they basically got a ton of new Bots outside of our Network um so basically um if we had other partners obviously they could have cut that part off but
they basically were able to create a whole new botnet outside of US Mobile based
awesome well yeah oh did you uh see any evidence that this was uh like something automatic that was maybe horizontally scaled similar to to kubernetes like noticing more demand and just scaling up more like containers type thing like is there any evidence you could see that it was something that they just had in reserves from before and they just fli the switch when they noticed a demand yeah there's a chance it could have been um however we did see them going down and then when they went offline um clearly something happened and then getting a whole new population so either they already had a contact almost ready for this sort of situation like maybe they already had that
Pipeline map out and said hey we're going to keep this up but in the day we need it we'll turn that on that definitely could have been something along those lines um yeah it's hard to tell exactly um we couldn't Trace down um any other proxy Network that they definitely were coming from for this
one awesome awesome thank you guys so much I'm sure they will be here and available to answer any more of the questions you have but that is a wrap for breaking ground here folks on the first day of east side Las Vegas thank you so much for coming out for those of you tuning in at home thank you so much for tuning in we hope to see you right back here tomorrow either in this track or another one at bides thanks again





