GT - A System Dynamics Approach to CNO Modelling - Sara Mitchell
Show transcript [en]
all right so I'm Sarah Mitchell and I'm here today to present what was my master's thesis research and it was applying system dynamics to CNO modeling but before I want to be before me I want to give a quick thank you to to a few people who I could have done it without the first is Jared any girl who was my piece of the thesis advisor Andy Moore at cert CC in Pittsburgh he does a lot of stuff with SD and insider threat research and was really happy to help me apply it to larger CNO modeling and Deana Chuck who's here today couldn't done it without her feedback and without her input and everybody here today it's
actually great that people showed up so just to give you guys kind of a rundown on how I approached my research the idea was really Jared's he kind of threw it out in class one day of what if we could do this and so I went up to his hey can I do this after my thesis and he was like yeah sure that's awesome and so we kind of broke it down into fourths over the course of the semester I did a lot of SD specific research I did a lot of research specifically on the adversary I chose which happened to be a PT one and then I did a lot of model development and then I wrote my paper which I am
willing to share with anybody who would like a PDF copy so basically what the research looked like was a ton of text books SD is a very formalized modeling system there are a ton of text books they're very awful and very dry but necessary to read to spend yourself up on a topic and then I split that with China and operation Aurora research researching everything from white papers published by the likes of north of remin to online articles from threat intelligence organizations like Mandy admirer I I ate it through over ten model drafts I think I'm on like 20 now I think there's a version number and really one of the big things I learned
is feedback as a gift if you're not getting different perspectives on your research you're really not learning and growing and even if it's you know hey I don't like this or hey don't agree with what you did it's a good thing to have that perspective and get the involvement of others so why did I pick modeling why CNO modeling conceptualization and information security is something that is often overlooked or poorly done in my opinion there's a lot of complex models out there just about the only one that I can think of it's not complex is the cyber kill chain but even then it only really takes into consideration the bite the more technical side of things and only one
perspective it doesn't offer the entire CNO from start to finish model and I really wanted to make something that was simple and easily consumable by somebody like my mom like I wanted my mom to be able understand I want you guys as moms to be able to understand what's going on it shouldn't be so complex and technical that it's unapproachable and additionally I really wanted to focus on why why do actors act in certain ways how do they act in certain ways what is how is the reflection of their overall strategy intelligence policy management and decision making process and this really comes out and st and what is known as feedback loops it's the idea of
everybody's iterating through some process and trying to iterate through as fast as possible so that leads us into why system dynamics really everything is a system everything can be modeled as a system at some level whether it's an ecosystem whether it's a computer network operation it really doesn't matter and SD really focuses in on that rates and optimization through the idea of feedback loops and these rates an optimization or how you can start to begin to extrapolate out the why if you see what people are allocating and how much of it they're allocating and what the time frame is you can kind of use that to infer and extrapolate out their larger strategy which is there why
because at the end of the day we're not fighting computers on a bits and bytes levels we're fighting humans there are human motivating factors and that's really why I wanted to focus on the policies and management and the decision making processes available to different adversaries and targets and organizations and this insight comes from events so an event in terms of SD you can be a CNO it can be a larger CNO campaign it can be one part of a CNO campaign you can model it at different levels and at different scales and rapidly expand and contract so case study operation Aurora I know this is an old topic but I wanted to pick something that was very well documented I didn't
want to have to struggle with all right well how do I get information I wanted to pick something that was everyone pretty much agreed upon everyone understood what was going on so just to give you guys a recap it's been a while uh Google Adobe and 30 other companies were compromised by what is attributed with high confidence as a PT one and as a result we will left China for a time especially their R&D side because as a result of this you know Chinese dissidents are targeted via via Gmail and Google services and also source code management was targeted there's a common software management source code management software utilized by all of the companies that were
compromised and the theory is or at least my theory is that they were trying to get access to current copies of source code that's kind of a cheat sheet for vulnerability analysis or be able to insert their own backdoors into future versions of source code that even having to get the get access to it they could just put their own and it said I'm waiting for developers to make mistakes so this basically happened over six steps so the first one is phishing email it's always a phishing email they then it was a malicious JavaScript payload which had downloaded from ie and contained a zero-day and then from there the binary executed a backdoors established and basically sprayed
throughout the network and exfiltrated data and this picture is from McAfee so now I want to get into how all of this applies at the with the model that I developed but before I begin I want to state some assumptions this is a very young model even though there are 20 different versions it doesn't account for the balancing of profit and cost centers it's really designed to be consumed at this stage with security at its forefront and I don't know how many of you are familiar with the software vensim it's a modeling tool for system dynamics it's not very pretty so I didn't use it for my slides but it did allow for some great things like unit
validation and things like that to make sure that I had everything was made sense from a baseline units perspective in terms of mathematics and like I said feedback is a gift I think besides has it's usually peerless to get feedback definitely reach out to be there and my twitter handle I'll have at the end I would love to hear your comments and get your feedback so this is the key so we have this idea of a sinker source and that's basically where it and where the information enters the purview of the model so this is where it starts or where it leaves the purview of the model that I'm trying information I'm trying to model then you
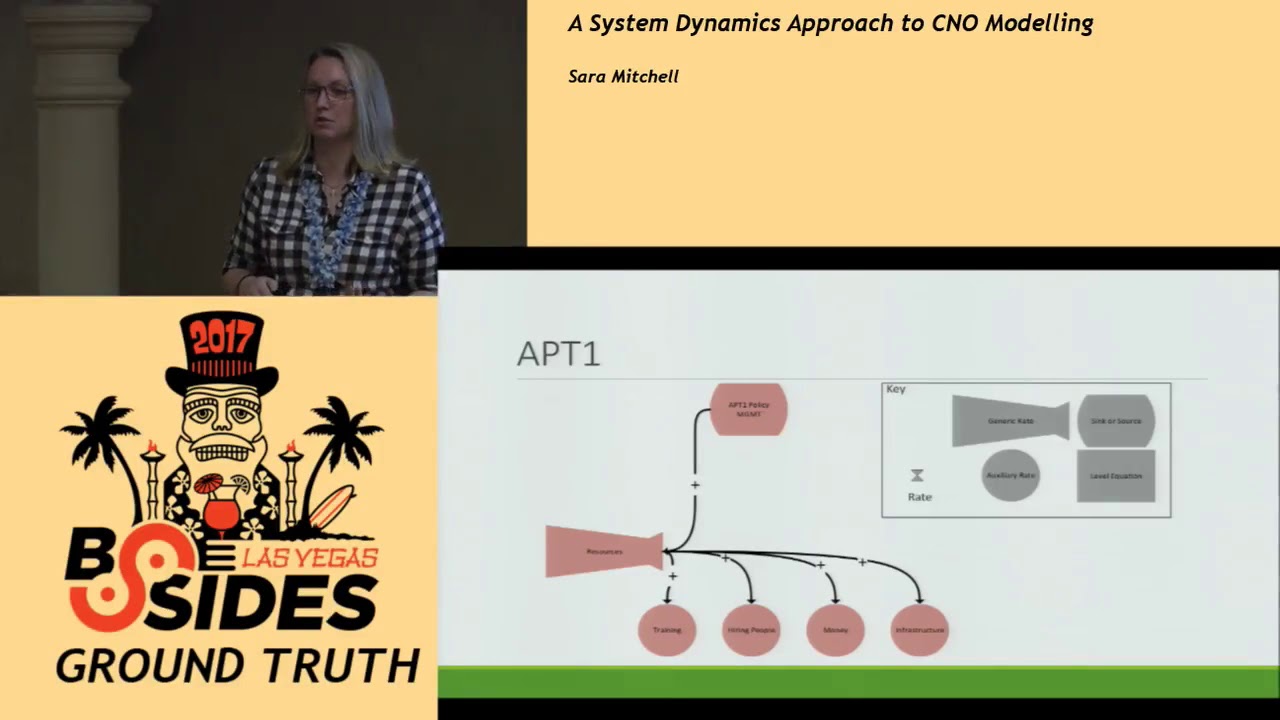
have these level equations so in terms of this model that's kind of like your TTP there your bag of tricks or things that you can do and use generic rates are conversions of auxilary rates in different things so an axillary rate you can think of as a subcategory of a generic rate so if you're you'll see the larger generic rate it's resources in the subcategories of that for example would be people time and money and then this rate down here this symbol is when you are converting one things state to another it's the same thing but you're just converting it States so you'll see that's what happens between clean and compromised machines so we want to look
at a PT one or really any adversary they have some sort of policy and management structure they allocate resources here indicated by the positive these resources that are allocated into training hiring people money and infrastructure hiring people can also be less formal recruiting people to your cause if you're you know not quite of a formal organization these resources are then converted into capabilities and we have these are kind of similar to this you can see a little different you have information gathering or recon you have social engineering attacks zero day attacks non zero day attacks so what and what I mean by non zero day attacks really is these are attacks that are known they've been seen before they're
defensible if you configure your posture correctly and then we have what is Middle infrastructure which is coined by Dina Schick and it's really this idea of a Hotpoint I compromise host a use host a to pivot to point B so then we can see the apt one action so they use all of these staves to go to convert clean machines to compromise machines and information it's hard to tell with all of the lines flows before back and forth between information gathering and the middle infrastructure is also a positive everything else is a negative and the reason it's a negative because you're giving away your TTP by acting and doing these things you're establishing a pattern or procedure for
what you're doing and you see down here that we have this other sink a kinetic or geopolitical action so think in apt one's case of Operation Ora this is them spying on people trying to discipline vehicle this is outside the purview of cyber you're doing you're using computers as a means to an end for something geopolitical we're very much kinetic so the large feedback loop here is a PC one it's allocating resources they're developing capabilities they're using their capabilities they're getting Middle infrastructure and information back they're reallocating their resources they're redeveloping and reallocating capabilities and doing it all again so it's this larger circle here that we see which would be considered their feedback loop that's
what they're trying to optimize they're trying to do that as fast as possible so switching gears a little bit we're gonna look at the other half of the model which is their target and you'll see it looks very similar target has the same things they have a policy and management body they have resources they have the same resources that they can use to allocate however in the case of the target they're going to develop hardening capabilities rather than offensive capabilities and these offensive capabilities are going to have an impact on clean machines and compromised machines and from the compromised machines the attacks hopefully you're getting detection information which can then inform hardening so we have a little smaller
sub feedback loop of this is your short short term information impacting your hardening so think we're seeing data exfil over whatever port that we should be seeing so we're going to write a firewall rule to block that right now this is a short term it's not strategy it's more at the tactical level and then you see this other feedback loop in here which involves threat intelligence so this is only for mature organizations I understand that not every organization in every state is going to be able to consume some sort of threat intelligence but if they are mature enough to do that they can use this to inform their detection capabilities and their hardening capabilities and then the
detection and threat intelligence in the long run as a strategy will re impact the policy and management so that's kind of the idea that if somebody comes to you like I sac and says hey you're a bank and actor X is a attacking thanks how do you reach us your strategy policy at the highest levels to help combat that and reallocate your resources accordingly so that's really this detection loops here that we really can focus on we see that all of these things are going in here and so if you get you know if you're seeing scans you know you can use that to readjust your hardening or inform your threat intelligence you can use
that and reallocate that information and sort of iterate through that process at as high of a level or local level or as you want and so the final model looks like this I know it's hard to fit all in one slide but basically that red box is the feedback loop of the adversary and the blue box is the feedback loop of the target or the defenders and you can see that they interact right here this middle point of the thing that they're all trying to impact is clean machines and compromised machines obviously the target wants to keep their Queen machines clean and the adversary wants to compromise the Queen machines so just to summarize the purpose of this model
is really the focus on resources an allocation to inform what strategy and policy are and by focusing on the optimization and using that we can infer extrapolate out the why why are humans acting different ways why are they using this capability versus another capability you know different things like that and that all comes from understanding the policy the procedures in the strategy not necessarily the bites and bits technical those are really just a means to an end you're not it doesn't matter what tool you use to scan why are you scanning well because I'm going to attack that why are you going to attack that you kind of get that idea of the larger system that's being used and I really
think that that allows us to see this nexus of intelligence strategy and policy really coming together at the highest levels to then inform the lowest levels of technology and just some notes on my future work right now this is a retrospective look I'm not a mathematician I'm very bad at math I would love to find a data scientist to work with to apply a mathematic simulation and be able to model and predict attacks so for example you can put in all of the information regarding the resources and allocation and information about policy and management structures and then the model operation Aurora and watch it go through using something like Benson and then I would like to also
test against other information sources given that I only had a semester for the research I would love to take another CNO and see if the information still holds and analyze it at the level at which I analyzed operation Aurora and part of that is all to make this consumable right now this model I understand it's very academic and it's more of a thought exercise but I would love for an organization to be able to take this and say okay I now understand that you know I'm here in the model and this is where I am in my feedback loop and this is where I need to get and this is the amount of time it's taking me to
hit all of these steps so how do I move through that faster and one of my thoughts with this at the bigger picture almost like nation state level is you can determine minimum operating levels so if you know that you know you need this many hired and trained people to attack your adversary needs this many people at this skill set to attack you for lack of a better example you can do something like what the United States government did with the Iranians and blocking them from being able to go into nuclear physicist programs you can do something similar pick an adversary at the nation state level and deny them access to what they need starving them
such that they can't perform their actions at least you know the highest level so instead of having qualified people who can actually develop and find zero-days and exploits for them maybe they can leaves Metasploit now because that's all they that's all the capability they have in terms of training and resources so they're still going to attack you and they still want to attack you but maybe you can defend yourself better because you now know what to expect or you can expect something that's hopefully a lot more defensible for your organization so that's all I have that's my Twitter handle please reach out to me there I'll be checking peer lists as well and I welcome any feedback
right out [Applause]
yeah to underscore somebody took 100 snot published anywhere I do have it out on the people drive and if you reach out to me via Twitter I'd be happy to share that link with you so sir I think it was really interesting don't ask you to speculate for a little bit okay on based on the components of your model and how you might adapt it what are some of the insights that we might be able to glean that come from going through a simulation that you think aren't immediately evident from the assumptions you made going into the simulation I think that one of the most obvious things is by seeing what capabilities are thrown at you you can make and
speculate and sort of derive intelligence as to the level of your adversary or we talked in script kitties are we talking you know cyber criminals or are we talking nation-states acting for cyber espionage reasons trying to impact critical infrastructure for very geopolitical reasons and from that I think that by seeing what's being thrown at you you can sort of determine the maturity and the sophistication of your adversary and make your decisions based on that as well that's fascinating there's some researchers that I should connect you that are trying to look at the code itself to make such implications I think that Matt will be else micro be really helpful thank you
what opportunities do you think there are two for the model to work with subject matter experts and subject matter experts to compliment the model to produce a improved combined say view of the situation that's a great question I think there's a lot of room for that I'm not a subject matter expert and anything I'm just starting my career so the idea of being able to actually work with and connect with other people and make this much bigger much more well-informed research project that would be awesome I think that would be a great place I think it would definitely add the credibility required to make this more consumable okay Thank You Sara and please remember to follow on on peer
list thank you very much [Applause]





