BSidesIA 2017 Track1: Protecting Against Advanced Attacks – Andy Thompson
Show transcript [en]
alright thank you all for sticking around for our one of our latter sessions today I'll do my introduction in just a second but before I begin I want to start off with some story times so close your eyes or if you may just imagine this all right roughly about a year ago februari of 2016 in the steamy hot town as a manila philippines gentleman walks into a very busy casino walks up to the counter makes a withdrawal request they take a look at his documentation it all checks out a little big of a transaction but again it all checks out they load up the suitcase with a very large sum of money and the gentleman just disappears into the night
never to be seen or heard from again over 6,000 miles away in the Phillips Bangladesh the central bank of Bangladesh had just literally been robbed 481 million dollars that's right this was the largest bank heist in the history of the world and this gentleman right here unfortunately had to suffer the bird consequences of his lakhs internet or his lakhs network controls ended up this man's name is at or a mom he was a central governor of the Central Bank of Bangladesh he was just one of many victims of bank heist perpetrated against the Swift network now the Swift network was originally conceived in the 70s to facilitate banking transactions between other banking institutions they do roughly about 25 million transactions
a day and we've seen a new rash of attacks against this Swift network what we're finding is is the Swift network in and of itself is a relatively secure system it's the controls around and access to the Swift network which are often over slacks and oversight and that's where these attacks are happening what happened in this particular situation was that it was not a technical control that discovered this but an actual oversight they discovered a typo in the bank transaction five transactions were successfully went through there was over three dozen transactions that ended up being stalked if the transactions had all gone through successfully the bank heist would have amounted to over 950 1 million dollars what happened was is the
word foundation in the transaction was actually misspelled it was misspelled as a fun dantian and so that's how we were able to discover and stop to some degree the largest bank heist in the history of the world again my name is Andy Thompson I'm the strategic advisor for cyber Ark software I really have a really cool job in that I'm just get to help people and so I really absolutely love that I've got information systems degree from the university of texas at arlington have a comfy aaa+ security plus SSCP isss cissp and two three weeks ago I got my G 10 from GX oh I'm pretty happy about that happily married and I a member of a
shadow system tax of collective and Dallas hacker systems out of Dallas Texas so if you guys saw my talk earlier that these are the same slides but the real hacker in my family is my wife she's a travel hacker and is able to get incredibly amazingly cheap trips so that's a piece of real dapper very similar is my little tiny doppelganger that's Kinley she like to travel and run very similar to her mom and then there's my little doppelganger the little hacker this is Charlotte that's her keyboard that she sleeps with yes his name's tight knee so we're going to give this talk it's really a two half talk okay it's going to be red team starting off
where we're actually going to demonstrate a golden ticket attack and we're going to do it from the initial inception of the macro if you came to the previous talk where they were discussing macros this is a very simple not obligated macro all the way to where we actually execute our endgame the next phase of the talk is really a blue side of the talk where we talk about identity access management best practices and how any one of those individual controls could have been applied in a way that would have stopped the attack that I previously demonstrated then we'll open it up to some Q&A and whatever you choose to do afterward is up to you so
this is a golden ticket attack this is a whole proof of concept that I've done in six minutes but it would have been for if I was any better at typing I'm absolutely terrible at typing there's a couple of disclaimers before I really in the first thing is is that this is a simulation of the bank heist on Bangladesh but it didn't actually really go down like this in reality law enforcement found out that there were two other apt players in bedded in the bank of Bangladesh at the time this attack went down so it was this Asian crime syndicate the North Koreans in the Iranians were all in this same network at the same time it was just the crime
syndicate that was the one to pull the trigger and execute the in game first they've done some further analysis on this particular attack and they discovered they haven't quite identified it directly but they assumed that this money that was taken from the bank ended up being channeled to abuse i F and ultimately through Isis so this money could have actually gone to fund terrorism the other thing is there's absolutely one more than one way to skin a cat here I chose to use the exploitation framework powershell empire but you could have just as easily young used metasploit or native tools and even within that there are many different functions that we could have done even
inside PowerShell export our shelf Empire to do the reconnaissance and lateral movement user hunters a really good function within PowerShell Empire it just didn't work in my demo so I didn't do it and then lastly we're not dropping any zero days this isn't any elite hacks or anything this is very simple stuff all downloaded off the internet and I often joke it so easy you don't have to be a 400-pound hacker in your mother's basement to do this all right so golden ticket attack who's here familiar with the golden ticket attack or Kerberos okay let's get a couple volunteers I saw you raise your hand can you come up here real quick scheme come on up here and I need one more volunteer
you yes come on up here pretty green and my domain controller here's some tickets for you in fact okay so you guys go ahead and read your script hi I'm Bob I want to access a file on cloud server hey Bob what's your password my password is Seaside underscore Iowa underscore it is underscore awesome the password is very good very good hi file server I'm Bob I want to act in the fire I'm going to Thika so doesn't mean that the domain controllers days you're good okay fine there you go that is in SS in essence what a Kerberos exchanges the domain controller validates the credentials gives the ticket and the ticket is what generates access okay so this is what a
golden ticket attack essentially is doing here oh that is a golden ticket attack thank you I'll clean this up later I promise thank you guys for coming I appreciate you give them around a round of applause thank you alright so that was the golden ticket attack and that's just part of the advanced target attack what is an advanced re attack or apt it's really just the fact that they have an act bad actor or what is it a bomb threat actor from the previous talk embedded in your organization for a significantly long period of time and to the point which they know the ins and outs of your network in your infrastructure better than almost you do
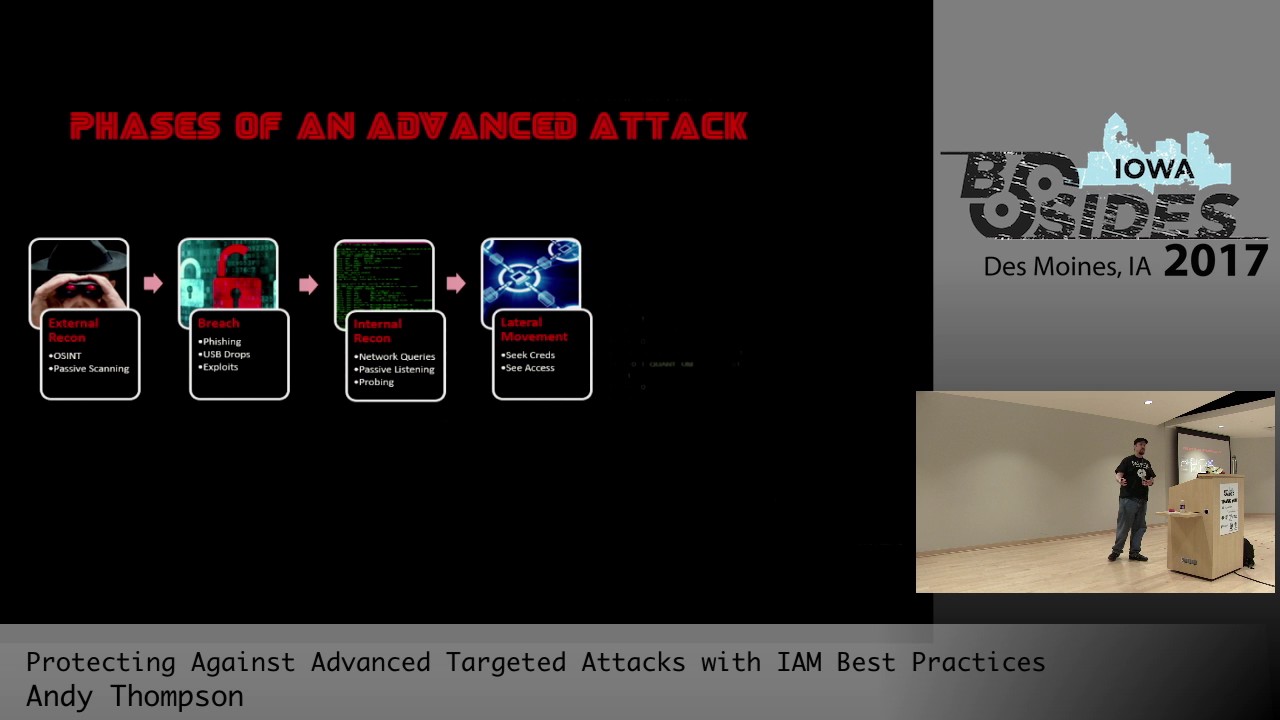
this is in direct contrast to what we've seen with other types of attacks we have the distributed denial-of-service attack not an AP not advance attack opportunistic attacks such as ransomware where they don't care who you are but they're still being attacked not an advanced targeted attack we the closest thing we see to that is the what we call a quick targeted attack which is those gentlemen calling from Microsoft wanting to help you fix your computer again you're a target but it's a not a long-term attack we're talking now about the phases of an advanced attack and what you're going to notice here this exactly correlates to your red team a apt attack and most importantly your
penetration testers the only difference is is that penetration testers have a much shorter runway where their operation is going to be what two three weeks tops these advanced actors can do to three years in your network so but here's the key is the spaces are still the same first one is starting off with the intern or external reconnaissance learning about the organization second is followed by the breach which is what we'll do with the macro followed by internal reconnaissance learning about the network learning about the systems on the network lateral movement is basically pivoting to those other endpoints and expanding your scope of influence and your access once you've established the amount of access that
you need to execute an in game it's a matter of establishing your permanency in your network this is the domain compromised and where the golden ticket attack comes into play and then the last is execution of the in game so let's start with the first phase of breach rather than external reconnaissance let's assume you've already done that what we're going to do here with PowerShell Empire is craft an email attachment with the macro and demonstrate the execution of it and then getting into your network so will first start off here again the only tools we are using here are PowerShell Empire and the vegetables with it this is a demonstration of a spaniard user it's a
Windows 7 machine the standard user count happens to be local admin on the machine but doesn't necessarily have to the end user opens up the Excel macro are they excel documents and macros executed and you'll see that its shell is established on my command and control back end so there it is now what we're going to do is interact with that shell and now we know it's got a local admin rights we need to try to bypass the UAC using the function called bypass UAC cleverly named we're able to execute a second shell with bypass USD permissions meaning that we can execute commands that require elevation without prompting that screen to pop up on the end user's
machine so we've gone ahead and we've done that we're interacting with our newly established bill and we can commence the rest of this attack so again now we've got our breach head into the organization now it's a matter of moving to the next step the lateral movement are eternal reconnaissance phase this is now where we need to learn about the network learn about the people on the network and the people that we want to attack you want to go after the people with the most privileged systems administrators and domain admin access is really ultimately what you want to get when you're dealing with a golden ticket type of an attack so what we're going to do is we're going
to run several commands to learn a little bit more about the organization and then how to pivot to it so we're going to go back to the recorded demo I didn't bring any chickens with me to sacrifice for a live demo so we'll just have to do what the recorded session so we're going to interact back with our elevated UAC agent I did find out that tab autocomplete work so that would have gone a little bit faster for me what we're going to do is we're going to run the module get group members okay we're going to define the domain administrators group with an active directory is the group you want to look at we could look at any group look for
this service we want to find out who the domain admin press execute were provided a list of the domain administrators in this particular psv there's only two domain admins but in an enterprise organization of significantly more the next thing that we would want to do is find out what sort of computer objects are in play what machines can we possibly pivot using the function community get underscore computers within power shells a powered youth platform we're provided with a list of all the computer objects that are on the network very simply done in the press excuse that you're provided with the long list in this circumstance there are really two machines that were of a value
the file server and the Swift server the switch server is completely locked down nobody has access to it file server on the other hand file servers are an interesting situation for a penetration tester because the NTSF permissions tend to be a little bit different than what you'd see what the normal application service so file server is an interesting target now we're going to run to get low Group command we're going to find out who the administrators are on that particular file server so we define the file server name is the server name as well as local admins we're provided with a list now what you'll see is that the same user that I we originally
compromised also happens to be an administrator on that file server that may have been that may not be the case that you can still use that information for your reconnaissance the last thing what we're going to do is run they function get logged on what this does is it does just what it says it finds the particular target server and it provides you a list of who's currently logged on to that machine we find out that there's a domain administrator that happens to be logged on to that same file server that conceptually we should be able to pivot to meaning that if we're able to dump the elsass or get the hashes we can then become the domain main
administrator so that's the reconnaissance phase of this particular attack so we now know what server we want to pivot to we know what credential we want to acquire it's just a matter of doing it now that's where the lateral movement base comes into play here what we want to do is we're going to identify that the file server rule on get sued and so we can use many different ways to laterally move within PowerShell Empire there's PS exec PS remoting through w my calls there's many different ways I chose to use of PS remoting for my demo but any of those would work just as well so again what we're going to do is we're
going to hop over that file server dump the creds and get the domain administrator hash back to the show we're going to re-establish a connection with our elevated you a seashell we find there's our agents right there here's the two shells we're going to interact with the second one and we're going to copy and paste as you win the invoke command or the PS remoting you run that command execute it and then you'll see a new shell will instantly connect this new shell is going to be your file server so there it is we've just been able to establish a new spell we've laterally moved to our file sir we're going to run a couple shell commands
just to demonstrate are successfully on that file so we're going to run the host name and you'll see that we are indeed moved did it to that file server we're going to run who is it still show that we are still that same user that standard music we haven't escalated our privileges just yet so the next thing we want to do is demonstrate credential dumping so let's see here let it catch up with me for a second running the creds command you see there's no presidential stored in the database we run mini cat it dumps it into memory so it now enough time as it ever stored on desk we're provided with the credentials we run presence again there we go there
are our credentials and hash and in clear text values now it's time to pass the hash so now that we have the password in the hash of the domain administrator we're going to pass this field of token and path ahead and have a process running as the domain administrator meaning that we can do anything the domain administrator can do we can do it now too so now we have established the persistence are the access that we need on this attack okay we've got pivoted access to the file server and have acquired access to do any domain administrator functionality it's now time to move to the compromise days this is where we establish our persistence that's such a hard thing to
say try establish persistence or permanent persistence is even better so what we're going to do now is the actual golden ticket attack and it all resides around the Kerberos hash it's a one-time hash in your Active Directory domain meaning that if that Kerberos hash is exposed there's really only one way to recover from it it's to tear all your domain controllers down disjoint every single in point from your domain re-establish a new domain and reef affiliate all your machines to the domain it's a pain and in most enterprise organizations that's irrecoverable from it's almost impossible so we're going to seal the Kerberos hash and it's done through a premium competency sync DC sink is a
process when a new domain controller comes online it reaches out to another domain controller and says hey I need all your hacks all we really care about is Kerber attached so that's how we're going to acquire it and once we have the kerberos hash it's a matter of executing the golden ticket let's jump back into the demo we now have access as the domain administrator so what we'll do is we're going to define that we want the Kerberos ticket hash by running the DCC command once you do that the domain controller will then send you the Kerberos hash what you'll see here is when we run credit union there you go there's a Kerberos fashion if all we
need to execute the golden ticket using the mini test module from powershell in our Empire were able to run the men get goal or golden ticket command we now have the it references the Kerberos ticket which we've acquired and we get to name the golden ticket and the duration how long you can have it up to 99 very soon I happen to choose the golden ticket and hack explainers so all we've once we've defined all the required parameters we press execute and we have generated a golden ticket we have established permanent persistence on the network so now we previously couldn't get into the Swift server I mentioned earlier now we have access to listed file content where we previously
could so now we've established our permanent persistence on the network we have acquired the access that we need we've done our reconnaissance there's really only one last phase in this advanced attack and that's execution of your in-game depending on what your motives maybe it made to be to disrupt the functionality of the application in a full denial of service attack you may want to do what we're going to do and we're going to compromise the integrity of the data in the transactions there's many different in games but again this is what we chose to do we're going to access the Swift server locate the pending transactions and inject are fraudulent transaction into the batch queue so back to the demo well you'll
is previously we did have access to this file server this is just directory holding batch transactions that are queued up ready to go at a certain time we happen to manipulate one of the Swift transactions and this is what a legitimate Swift transaction would look like with the exception that $50,000 isn't going to the shadow systems hacker collect wants you to upload the file into the batch queue it's bypassing any manual like human eyes as far as controlling that it's automatic and it's just a matter of executing the batch job that would have normally automatically run it processes it and there you go $50,000 furniture to the shadow systems yay there's only one last thing to do
here that's profit so well that commit that's like the total red side of the talk right so that's how we actually demonstrate at the time yes oh heck yeah this is the lousy 'used like noisiest attack you could ever imagine but it still happens and so many organizations don't have controls in place that can even detect loud noisy amateur attacks like I just demonstrated but yes very good point there are a lot of tell tell tell tell indicators of what's been happens here and that really good very well segues into the next part of this talk our identity access management best practices really how we could have gone to prevent this and notified us of it
happening as it's in play first is the fact of in point in least privilege the first thing that we made a mistake was having a local end-user with local administrative rights on the influence so that would have probably been the first thing that I would have done so remove the local admin right from the end-user but there are certain cases in which a user needs their local admin rights to run critical applications right well there's I there's a least privileged solutions out there that can elevate those particular at binaries but still leave the underlying user in a non administrative state so again removing local admin allow the application that nuni do need elevated rights to run but still let the
underlying user retain their local standards user permissions the next thing is application control even though they may have access to run it we may want not to allow that so blacklisting whitelisting gray listing are very important to allow an offer to block unnecessary applications from running but allowing the approved applications to run through now this really isn't an identity access management best practice but I still think it works being mentioned and that I think network segmentation is a huge control to protect against lateral movement in particular so again not really about practice but a good recommendation what this does is if you can segment your network to the point where they cannot pivot to those critical assets using
standard protocols and having controls to monitor the protocols that you do allow that will provide some level of protection the next thing is is if you do have network segmentation you still need to access those resources so i recommend you need using jump servers or proxy dashing hosts to allow for access of your sis edmonds to administer an assistant or critical assets because if you do that then those hashes won't reside on the endpoint they'll live reside on the jump servers because you can't pass the hash if you can't get the hatch right and then lastly with jump server you are provided a level of accountability and auditing so you can actually see what's being done with
those accounts on those those endpoints that kind of leads me to the next point of credential management securing in the ng you're privileged provisions I love this so you so much passwords to decrypt so whenever I ever get says your passwords incorrect but seriously there's three main components to a secure password the first is unique if you don't have if your passwords are the same across your enterprise that means you can leverage that same password across your entire enterprise making pass the hash super super easy to do unique values mitigate that the next thing is complex passwords maximizing the ability of complexity of your password really thoughts brute forcing and password cracking so that's great
but you can still use a hash and it's been crept so that's why we followed up with the next day's ever changing frequently rotating passwords so for example if you have a password that takes a month to crack but that passwords changing once a week automatically that renders by the time that passwords been cracked it's changed twice over so that's why we want those three tenets of a complex password the next thing we've talked about this several times over throughout our conference today the multi-factor it's a truly imperative to tie the identity to the account that's being used as you can really do that with multi-factor authentication and now this is a concept called a credential boundary this is
really cool it's really just we're going to do we're going to combine what we call functional accounts and credit or boundaries to show you what a mature credential network would look like it looks something like this when we talk about credential boundaries we're talking horizontal I'm sorry vertical balance this is your tier 0 construction these are your domain controllers the xxi has domain name servers Union these are your correlate to your tier 0 control out of that you're q0 assets use a stir recovery program okay so those domain credentials only operate at that level if your sim detects that they're being used anywhere outside of those tr.0 assets that will be an incident that needs to be read so we'll put it
down here please they're rolling it's there to the next is you have your application server layer boundary again you have application server credentials that only operate within those boundaries if you see it up above then that's a red flag if you see it below yeah I was here too which is your endpoint layer then you have potential indicators of compromise so make sure that you segment your network vertically with credential boundaries now here's a really key concept here and I touch something that's just a second ago when I mentioned multi-factor okay identity identities are you meet everybody in this room they're human beings blood and flesh right okay an account not an identity these are just X values that
define permissions that's all they are these are not one end of the same you don't need to have a one-to-one relationship of your passwords to your people okay think of it like this this is a construction set does everybody in a construction site have a hammer maybe a SkillSoft probably not a bulldozer heck no absolutely doesn't make cost-effective sentence so what you do is you have a tool chest okay you go to the tool chest you pick out the tool that you've been assigned to use for the job that you've been assigned to do you use that tool and you put it right back for the next person to use and hold it accountable that's what
we want to start considering our passwords are and our credentials so think of it like this okay here are five systems administrators okay there's using the standard low-level ad permissions to log on but we needed them to do administrative functionality so we provide them in secondary or not Cena's ATM or bank account star accounts you name it but it delineate the fact that you double the number of Provence in your organization we've gone from five to ten now we have five privileged accounts and we need to be concerned with what I would recommend you do is still have the same time same low on non elevated account but each one of them check out one privileged account so we
know that for the fact that we're granularly controlling it from a password complexity rotation and uniqueness so they just check it in and check it out whenever they need so what we've done is we've gone from five privileged accounts down to one preferred account so i highly recommend that functional account model for administrative users in particular so i've demonstrated the horizontal to your boundaries and a functional accountant model this is what it kind of boils down to when you look at it from a high level perspective that so we go from unbounded completely flat to horizontal boundaries and functional boundaries throw on a little least privilege and application control that is a secure secure network
so that is really the credential functionality there let's talk about monitoring okay monitoring of their privileged users this is applicable to your administrators as well as your third parties we mentioned earlier that target was victim to a third party HVAC vendor we can't speak to the security of our third parties so we have to protect ourselves because our vendors aren't going to do it for us so I recommend having your privileged accounts being managed by either internal or external being channeled through a process in which you can monitor them something like this if we're talking about simin aggressions as well could have detected a lot of the indicators in our previous attack specifically if we were able to
set the DC sink that would be without a corresponding change control for standing up a domain controller that would be a pretty clear indicator last behavior on alerting on behavior nominees so for example if we have a user that logs on every day Monday through Friday their domain I'm sorry DBA but they'll happen to log in at six in the morning from a Chinese IP without that sort of analytical monitoring that would we wouldn't be able to develop a baseline so you want to develop a baseline as user behavior from oh it could be anything from their VLANs or IP address their time in which there were accessing systems what systems they're accessing all these can contribute to
their heuristic foot and then again monitoring of access of your critical assets that don't correlate to your controls that you put into place like for example if you're using some sort of privileged account security solution and you see somebody i'm logging on to a database server that didn't correlate to an event where they check that same credential out in your privileged account security solution that means there's somebody trying to circumvent your control so those are some of the alerts that you can fire off on so in conclusion there's really four main tiers of controls that we can apply to preventing advanced target attacks I want you to understand these are just some of the ones that we've gone over
today there's not one single solution that will fix anything if you ever have a vendor that says this is the Silver Bullet kick them out because they obviously don't know what they're talking defensive depth is really the key to a sound secure organization having multiple solutions overlapping each other providing redundant controls will provide you with the security you need and again in point privileged privileged for local least privilege and application control followed by network segmentation and routing through jump servers enforcement credential boundaries multi-factor authentication securing the management privileged credentials through uniqueness through frequently changing in maximum complexity of your passwords and then lastly monitoring on events and heuristic behavior so that concludes my talk I know you probably have some
questions definitely identity access management it is a new I wouldn't say new but it's a new kind of direction that a lot of organizations are taking to dynamically provision accounts and stay in them up for use and then D provision them it's it's really a way to hold your accounts accountable I know that sounds redundant but you need to be aware of what accounts you have in your organization because quite often what we see is like for example when a employee is terminated in the circumstance that they have those two accounts that I demonstrated HR really only knows about the one so we won't need to be accountable for all the accounts in our organization and identity access
management program such as like sale point would be a good that would do something like that thank you yes yes I guess my understanding that how you basically provide access to lazy ass fired you have to control to prevent users from having a look like so solutions all right let me see if I get this correct because you're talking about how you AC is applied in this demo and what sort of controls can be applied to allow legacy applications to run but still provide the accountability of having user access control exactly I don't want to do that right I try not to make a clock super been very but there are applications out there such as in
point privilege management that do just that they that all their job is is to facilitate least privilege for users elevating the legacy applications that are needing local administrative rights but still not allowing the underlying standard user to be a local administrator so again that would be probably a conversation I'd love to head with the offline here you go I was doing this at a conference in Oklahoma and I have talked to a guy weighed the back and i chunked it just like dak Prescott which was awesome to go Cowboys but I totally pegged the project so it was that good that yes I saw their inhibitor yeah
location may use stage and then is on you might consider come back early if the programs like loading in here my trouble wouldn't really do probably searching my source of it are you running sizzling hot to build your chambers all in the column yet a user packages beauty here direct responses
right on thank you great recommendation the projector flavor this is right any other questions all right well I will be here through the rest of the day thank you all for listening to me I'm Iran I appreciate it have a good afternoon





