Building the Flight Deck Tools and Technologies for a Robust AppSec Program - Chris Koehnecke
Show transcript [en]
Chris is DP security engineering and ceso at jit with over 20 years of experience in cyber security Chris is focused on cloud security security program development security strategy assessment and management of cyber Risk please give it up for [Applause]
Chris e
all right besides Albuquerque good to be back for year two um awesome to see everybody um you know last year was a great start um had a lot of fun last year and this year seems to be even better some great talks uh just to kind of get rolling I think we're like four or five talks in today I haven't heard anyone uh bring up the crowd strike issue um maybe maybe for the best we kind of let all the dust settle um but my talk today today is about tools and um you know with with the issue uh it's you know still ongo I'm just curious just kind of a show of hands how many people in like their
their job function were impacted or are impacted by the crow strike issue just by show hands so okay got a few how about your like your daily interaction like yesterday you just noticed that um like an issue caus an issue like you're out traveling or doing something buying something purchasing something and we show hands anybody else kind not a whole lot that's kind of surprising um I I flew in from I live in Dallas Texas so I flew in uh yesterday and uh got a little bit delayed because the the flight issues uh and then maybe can um you know grabbed a b to eat at uh at the airport Chick-fil-A and they actually had a sign
up to said hey we we're opening late because of technical issues like wow this is really real uh these are uh this is a lot of things a lot of different ways also I check to the hotel they had to go the old school way they couldn't uce the credit card they had to they write it down so um so really impacting and you know I bring that up because um I'm going to talk about application Security today not about endpoint you know the crowd strike issue but one thing that um I wanted to kind of bring up is like you think about this this is going to play out right this obviously the issue just happened and there'll be
a lot of we don't know all the details about what happened lot it's already come out if you've been reading it track it uh but who's the you know kind of who's the what's the big impact from a cyber security perspective that we're going to see coming out of this who's the who's the big winner here and my concern is that you know Bad actors this is a this is a big deal because obviously the cros issue um you know impacted the availability of so many services out there uh so now when you go through we look at again time back to my talk here we'll get into tools here in just a minute um you know the scrutiny
around tools is going to be that much more uh you know that much more intense in our companies you know if you're consultant with your clients like you know used to be hey we pick a security tool here's all the reasons and justifications now the whole kind of cross you know is this going to potentially impact their availability we should always be part of a tool selection process but I think now it's going to be even more impacted by concern is that are some of these endpoint solutions that are really important because we look at a lot of the latest breaches that have come out um you know malware infected on end point I mean come on that's like 75% of
the latest breaches these days right it's a very common attack Vector so we'll see how this all plays out but I just wanted to you know bring that up and I'm sure you guys are have a lot of conversations to talk with you about kind of where we see this all going in the impact so um just a little bit of an side before we get started here uh so uh uh my talk today is about application security and actually another impact from the crri issue you see two people up on the on the screen here so I'm Chris kenck I me I live in Dallas live from Texas yesterday uh we got a you
know uh close friend Matt Roland he lives up in Boise Idaho he works for United Airlines he was going to come down and his fight was cancelled delayed so he couldn't make it today so we we don't really give this talk together as a u you know as a Duo but today it'll just be me so um so again another impact in the issue um pro issue all right so um maybe just you know quick uh introduction just a little bit more about about myself so um you know I um I've been uh Consulting for quite some time so I started my career system administration kind of way a lot of us to right hands on keyboard um you know I
love that at for for a handful of years and in Consulting um I I really wanted to you know help people help companies you know problem solving work on different types of projects so I joined KPMG uh big four um you know almost 20 years ago so I got in you know actually quite fortunate I got it early so I got to work on all kinds of different types of projects uh business Comm Disaster Recovery um security operations penetration testing vulnerability assessments um you know all the above so that was really cool experience for me um one of my clients uh actually built a startup uh all around application security and there one thing I noticed
as a consultant is that you know we had a lot of great projects a lot of great outcomes but I wasn't seeing a lot a lot of the processes and tools that we had we had picked for clients kind of stick and then different regimes change um how can we really uh you know build products that are you know meant for developers can can kind of stick with a uh with with a product so I joined a startup uh called jit uh jio uh which is focused on empowering developers with security um and I actually just recently moved on actually going back back into Consulting so this goes to show in cyber security uh your career can take you a lot of
different ways uh the key is to keep your keep your ears open and your eyes open right it's a lot of opportunities out there um outside of work um love the hike love the outdoors so that's why I love coming out here you know beautiful up in the Sano mountains um I didn't get a chance to go for hike yesterday CU I was delayed but uh always look doing that liary golf courses out here too so love spending time in the outdoors uh and traveling um and actually that's where the Genesis for this talk came from in traveling because you know in my Consulting days you know I used to love that too young getting back into it you
know travel uh to see different parts of the country get all these different experiences working with different companies um you know that's a lot of fun and then you know Matt working for United uh and being a u director of application security like hey let's build a talk around application security well let's you know since our passion one of our key passions is around travel let's do a bit of an analysis an analogy around uh flying a plane because quite frankly cyber security and application security is pretty dang complex and so is flying a plane so we thought it would be a good analogy to kind of break it down so apologies for the rendering a
little messed up here on the slide but um so I'll jump into the kind of introduction and overview about application security um spend a little bit of time on that uh and then I mentioned this is about two roles right which is why I was able to bring with the crow strike thing but uh uh the to application security tools so we're going to spend most of our time talking about tools for prevention uh um in terms of your your tool set and your Suite of tools from an AB perspective and then also we're going to get into tools for protection as well and then at the end I'll just kind of tie it all together of like
operationalizing what this kind of a best practice looks like in terms of an application security program what we need your tool set and how it's deployed um maybe quick hands before I jump any further um I'm curious my abc people how many people who work with appc on a regular basis you know securing applications you know managing an application portfolio just show of hands um okay we got a few um maybe maybe more a few more penetration testers or more kind of deeper technical uh people in the room today but um this this should be good though this would be good kind of helping you better understand what are some of the key tools think about in terms of the
application security program all right so when we get into of course you got to start with the why right um you know why is application security why is application security program important and there's a lot of reasons why uh it's important um you know if you go to the OAS you know top 10 and there's a lot of a lot of great material that OAS has uh you know when Matt and I were putting this this deck in this talk together we had a few things things that kind of jump to the top of the list for us you know one is that you know if you look at from an appc perspective um in particular if you
talking about software companies where you know they're delivering you their core product is their software application so you think about you know like all the right share applications you think about Amazon and shopping across the board right there's so many zast applications everything's out there uh it'll be more and more if you look at from an AB perspective it's that first line of the fence right how you protecting your application keeping Bad actors out protecting your data across all your development stages uh so it really becomes in particular for those companies and I love the the last talk talking about think about your threat actors and if you think about your risk assessment for for a company if you're a
SAS company your application is super important I have to say you know it's not important for other companies U that aren't sass companies maybe it's a little bit less uh important but for those companies where hey your web application is your core business you know your your program is your first land events uh so super important the second one up here might be a little bit surprising you think about cyber security you know but I personally put this up here particular with my journey is about development philosophy because you know if you think about the application security tools out there we'll talk talk about those today you know from a cyber security perspective again we're really focused on protecting
data keeping Bad actors out making sure the application kept up to dat um making sure availability again the application is U is up and running and not impacting our business operations uh that's all super important but if you look at modern SAS companies today you know and I'm sure many of you out there you know there's releases happening changes happening all the time of these applications there could be multiple releases per day right um in some cases more modern ones you know dozens up to 100 releases a day you don't want to slow that because the C professional this is you know part of my learning to a consultant perspective of course security is super important
you've got you got to think about the business and that development philosophy piece uh is super important that you pick the right tools and it's part of your app program ultimately your is your driving through the process um that your developers are enabled they use the tools they like the tools and it's not slowing down that release process for your application uh and then the third one up here is regulations and compliance and this is where I I spent a lot of time in Consulting uh but you know appc is a big part are you running the appropriate scans are you protecting your data um can you show that uh you think about some of the standards out
there like S 2 and ISO and get things like fed ramp um you know application security is a Hu a very big part of that um that compliance piece so by having a strong application security program you're also going to need a lot of those regulations and a lot of compliance things you have to do anyway right so hopefully it helps just the reason reasons why you have program now again I'm talking about tools today um but it's very important to note that that's not the only thing that's part of the story from the application security perspective um you know what else is new you know people process technology right but looking at this it is super
important and and again Matt and I have separate talks for each one of these different um categories or program pillars right but your team your abct team the roles responsibilities um skill sets you know you know who's doing what that's a super important piece uh it's part of ABC um also looking at your processes or how you're carrying out you know different um your standards your policies making sure your data is you know properly protected what are those processes behind it and your standardized uh you set of processes you know that's a really important piece too but kind of that fun stuff to talk about is tools right so we're we're going to get into tools today but uh one thing I
will will urge you is never start with tools um it's always good to have your processes set up for your apect program what your team looks like um you know prior to selecting those tools also understanding what your risk posture your risk assessment it can help drive that U you know your tool selection um but just to give it there is there is more of the tools as I think we all know all right so I talked a bit about you know Matt and I having this passion for uh you know traveling and and you know think about you know how airline travel has changed our lives uh and again it's very complicated uh I'm not a pilot um nor do
I pretend to be been on Plenty of plenty of flights but if you think of think through uh you what a pilot goes through U and what really what a team goes through right a flight team uh that goes through where they're taking that flight there's a lot of things that are part of that right and we thought this is a really good analogy um to go through so just kind of run through this we call it the flight deck right and how do we compare an ABS program um to you know operations for an airline so first piece gets into the the pre-flight checklist like what does the pilot do gets in the you know gets in
the cockpit before it gets in the cockpit um you know uh before they get in the U on the plane they go through their pre-flight checklist all things they have to do so this is where we compare this in static code analysis right I talk about this in um SAS which gets into checking your code for vulnerabilities and issues kind of making sure that's all set up appropriately um next we just gotten a lot of uh publicity with this of course solar breach we talked about a lot about last year uh bid AQ uh but making sure that you got your supply chain appr Place set up we kind of thought about this as like a fuel gauges right that do
we have the right amount of fuel for the flight um is it um you are we're going to get where we need to go uh is that all you know the appropriate fuel is that all um U you know what we need so that's we get the software composition analysis or SCA day um this is another piece for app um next gets into you know when you're getting ready the flight is going to take off and think about the flight plan you got to understand what's the weather out there right do we need to avoid any storms any issues so that's we thought about what kind of the external pieces there and that's we got
to D of dynamic application security testing what what does the external environment look like right from our for our web application how do we manage that um next gets into again about the pilot um you know inside the cockpit and all kind of interactions are happening with the pilot the co-pilot the team inside the cockpit this is where we get into uh the uh iast or U Know interactive application security testing this is more like the details of what's Happening actually within the application uh which can be really important I'll talk a little bit about that as well um then we get to actually kind of flying the plane and you know where the pilots spend most of their
time of course is on you know taking off and Landing uh but there's this very important they turn on the automatic pilot they get them from point A to point B uh so this is where we get into runtime application security protection um and again this is more of a tool for protection that I'll talk about here in a little bit uh and then last is it kind of of course you know super important since 911 is it kind of have that that line right that no one can pass on a plane you know is they're going in um you know only one person to be up near the cockpit door so that web application
firewall or w right kind of like that was a good way to analogy for um you know what what a web application firewall is so this is something again you I kind of like this is think in terms of how you explain a a web application um you know program what that looks like and if you're if you're you know a flight geek like I am just a good way to be able to kind of uh you know characterize or explain what it should look like uh and what you going to think through of course I urge you to perform a risk assessment right get into the details but a good way to kind of
explain what we need uh we think this slide you know does a good job of telling that story all right so let's get to the actual tools now and um I'm going to start with the tools for prevention so I talked about that uh you know that pre-flight checklist right stat code analysis uh testing so what is statico analysis testing and I think a lot of you are probably familiar with it um and it's it's actually super important you think about that pre-flight checklist that the Pilot's going through and looking through all those different things you know your code and the quality of your code is super important as part of your web application it's the
core of your web application so you want to run the appropriate scans and check for of course vulnerabilities as well as what's you called code smells um issues with the code poorly written code again I think some of the stuff's going to come out with crowd strike maybe they had some issues with their code we'll see how that all comes out but static code analysis testing can help in all these different ways is you're developing your your uh your application so vulnerability and again it's not just vulnerabilities right it's also code issues now what a common problem that we see with static code analysis testing and I'm most familiar I using SRE you guys have heard that static code
analysis testing tool um you know but there's a lot of tools out there that that that do static code analysis open source and Commercial tools um but it's you know uh one of the key things about static analysis testing is that uh it comes back with a lot of vulnerabilities and issues typically right and quite frankly a lot of teams tend to ignore uh this thing it might be a check the box thing like hey we've got we're on you know GitHub or gitlab we use out of the box St analysis checking it checks for code issues we think most of them are false positives it kind of goes into a backlog or might going to a security
team uh discussion um that's one of the biggest challenges with static C analysis is making sure you got the appropriate call security efficacy right real issues and risks are being detected by this so one of the things that we've uh we've learned it jit and Matt and I have talked a lot about is that the process for handling the results from static code analysis testing so a couple things to think about right is one is these the automated code reviews so how are you embeding st of code analysis testing into your development processes so there's a lot of tools and platforms out there to help you do this but I think the thing you know times have
changed from maybe you know 10 years ago as a as a security professional I would pick the SAS tool right I would run the the the the SAS scans against my my company's codebase my client's codebase come back with all these results you know oh my God all these highs really hard to kind of read through and understand is is this SEC professional so I have to go back and talk to the development teams and Engineers a lot of friction right a lot of meeting you know a lot of challenges around handling those results from the static code analysis testing so one of the things that we're doing now which I think is working much better is we're
bringing a couple things one is we're bringing those results those statical analysis testing results directly into uh the development processes so like if you're using a modern source code management system like a GitHub or gitlab or bit bucket right for every single poll request every single change is happening you know well your static code analysis scans against that change and then bring those results directly to the developers and give them suggestions of how to fix that's way better than the old way that I talked about of running the scans myself and the security team and then like this is a high it's not you know it's bringing those results directly to the developers and then
giving them suggestions on how to fix way better way to secure your code and also have better quality code um as well the other thing that you I talked about um SAS is notorious for like a lot of false positives um you know maybe is is something that's right high it's not really high like the risk ranking can be an issue so the piece there that we look at is what's the context right so if you can have some additional context engine that can help you better understand hey these static Cod analysis scan results on our codebase were detected these are the real issues uh you know these are on we need to go fix could make a really
big difference and have a really big impact to help you with that development velocity as well um the only thing I'll say about sast is that then I also include that is Secrets detection right so there's a lot of tools out there if you're familiar with like truffle hog or git leaks um a lot of the like the SAS tools they have like embedded Secrets detection that's a really big one right because if you look at your code base it's very common and again you know U I'm not a developer I'm not going to point fingers at developers but it's pretty easy to inadvertently have secrets within your code right whether it's something that happened
between testing and like a a testing phase uh it gets into your uh your production um it can happen so that's one where typically hey we don't have a lot of uh arguments around hey we found a secret real secrets we have to go fix that but that's a super important piece there in terms of having clean code and having um you know Cod the you know fewer vulnerabilities and issues and and exploits that attackers Can U Can exploit getting those those Secrets out of your code early in the process is super important so um so that's static code analysis testing um next gets into the software composition analysis and again talked about this be kind of like a fuel right
uh uh fuel gauge making sure you the appropriate fuel for the plane the plane's going to run as expected so these are all software components um that are part of your web application the web application needs to be able to run uh these are open source components um you know this is again I've gotten a lot of press because of the the solar winds breach and if you there the Microsoft breach uh there's been quite a few high-profile ones so there's a lot of tools out there that can help you with this in terms of making sure that you've got your software libraries you know is very clear about everything that we're running in our environment right so what
are all the different software libraries that are actually in our environment and are we keeping them up to dat as well so um this gets into what's called sbom right or software bill of materials um and and that's really a leading practice now it's and it's yes it's for compliance and those of you that have have had to um you know create suffer build materials or S bombs like yeah we have to do this it's a compliance thing but it can really help you because um you know it's a way for you to manage and maintain to make sure hey these are we know all this with inventory right we know all the software libraries that are out there um within
our environment we have the current versions um it can help us track to make sure that uh everything is up to date know what is out of date um so that's a super important piece there um you from a software composition analysis perspective making sure it's all today um up next is again talk about weather radar when the plane takes off and making sure we're avoing any storms or issues this gets into Dynamic application security testing so this is detecting vulnerabilities actually in your web application apis while they're running so you think about this like um you Dynamic application security testing and these scans typically it's hey your application is out the while because I
talked about how um I talked about how the uh you know ultimately the security for uh your code and making sure all software libraries are up to date uh you want to make sure that you're uh when you're actually running you may have missed things or new issues may have come up so running those Das scans and you know looking at U you know tools like um uh there's tools out there like um actually there's there's a ton of tools burp Suite is probably the most uh uh famous and popular one that people have utilized uh we use zap open source jit for example so there's a lot of tools out there but running on a regular
basis those Dash scans and it could be you know I know I'd say daily you know you can you can run a daily scan authenticated is preferred on your web application see if there's those issues out there that we may have missed dur development processes um that's super important um all right so time has flown by um so I've got five Stu I'm going to kind of cruise through here a little bit um just I'll touch on this just really quickly I ask interactive application security testing actually Matt brought this up to me it's a bit newer it it combines SAS and Das um it can help you to get more higher Fidelity finding I
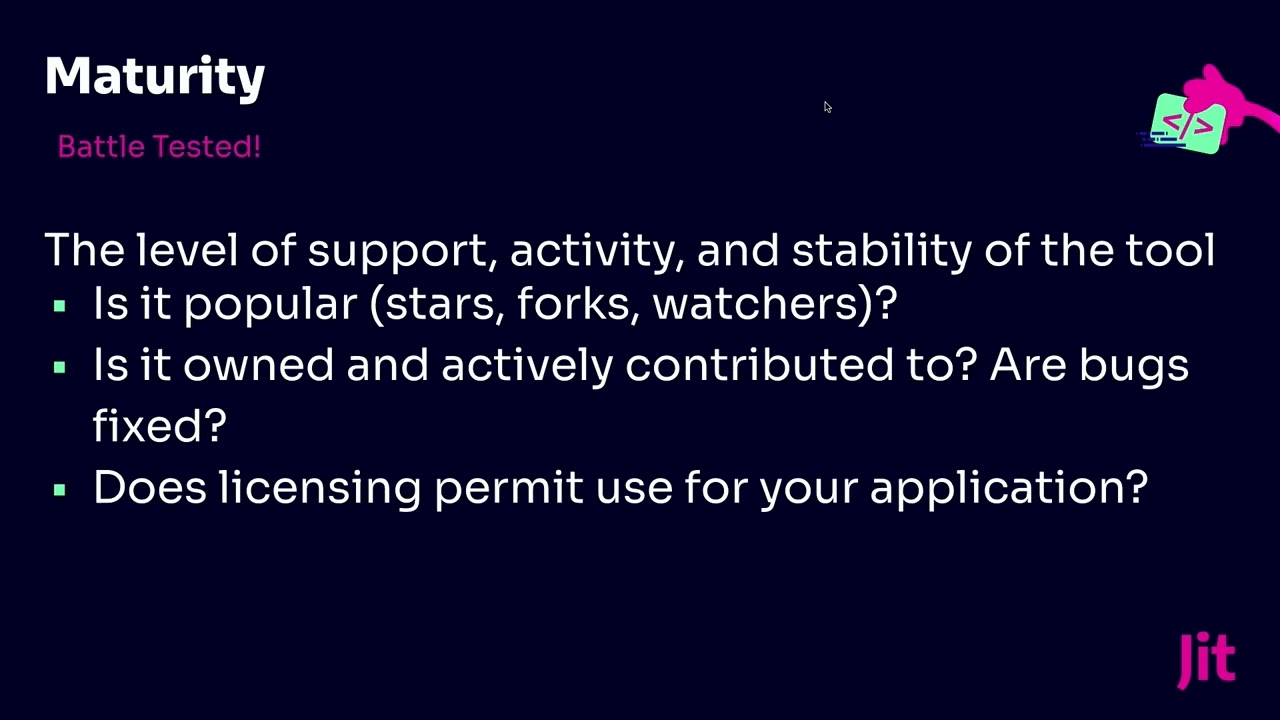
personally haven't used this but I don't if anybody else has I talk to you about any experiences you have of of you know positive things about is or negative things you uh through is um so again U the tools you know and talk about this of uh you know making sure you pick the right tools what are some of the the selection criteria uh for those tools so um you think about open source versus commercial there's a lot of great open source tools out there right so I highly recommend take a look at that right so what open source tools they free you know I mentioned like SRE for sass they of course they have a paid
version now because they've got still popular but there's a free version it's pretty it's pretty great so U and there's a lot of other ones out there too too you want to make sure all your languages are covered when you pick the tools that's a super important thing um you know if you have a certain framework that you need to follow uh from a compliance perspective um yeah that's really important too um the last thing I'll say about tool selection is that make this a team involvement what by that is like we're cyber Security Professionals you know we take this super seriously it's our job lot of times maybe we take that too far because
we pick the tool we implement the tool that we bring our development team in there for a tool like a SAS tool it's going to be brought into development processes so bring in your developers where they get you skin in the game we'll highly recommend that um it's part of your tool selection process um tools for Perfection is going to jump through this uh Ras is runtime application security protection and wav Up application to firewalls um again these tools could potentially break your application and again was the cross track issue from yesterday you know you make sure they're they're configured appropriately but if you have a higher risk tolerance if your company does if your consultant your client has a a
higher risk tolerance uh these could be really good tools to look at as well as part of your application security program um if you want to make sure you know everything that's happening particular with rasp that's happening within your application and here's just a quick uh quick view of w is on the outside and Gras one actually inside your application or inside your environment all right so I'm just going to I'm going to wrap it up here um one thing I'll say is like the operational view of like you know when to run these different tools I like this slide a lot because you think about you know pre-commit so developers they're know they're creating the application uh
they're in their local ID on their local laptop um that's where you could run things like sass in SCA then you get into the the commit phase and then you run additional SAS in SCA U and then once you get into testing you can start running your gas stands and then actually deployment that's wor some of those tools of protection in come in place as well but who want to only give this view um all right well with that said I'll I'll wrap it up um open any questions and again thanks besides Al for for cominging back from year two awesome turnout it's been a lot of [Applause] fun well there's no further questions we'll go ahead and roll to the next
presentation