5 Open Source Security Tools
Show transcript [en]
all right good afternoon everybody I hope everyone's enjoying the conference uh awesome turnout right just amazing to see all the different talks you'll let uh very technical talks um you know some really good uh you know career-minded discussions going on the the diversity here is fantastic and um I think the biggest thing is that it's great to be here in person um you know I we still don't get on the zoom calls all the time I'm sure it's just it's part of our life it's part of our world um but it's nice to be in person actually shake hands with somebody say hello you'll have a face-to-face conversation but going back to the zoom calls because
we're still on all the time I like to start with uh things overheard on a zoom call um just to get us rolling we're gonna go with product teams and Engineering teams and Leadership teams uh the first one is we need to empower developers with security it's always a good one to hear another one we hear is it's not clear about how we need to enable security within our products and what the requirements are for us to be successful and then probably my favorite one is leadership team we need to shift left right so I'm sure we um and again the shift left movement is uh it's it's a great thing um you know the fact that we're um you
know we're uh we're we're really seeing developers being empowered with security um you know being enabled you know trained in in our software development processes you know getting stronger and stronger from a security perspective it's fantastic but what are the ways to really do this effectively um and that's what this talk is is partially about is looking at some of the different open source security tools that are out there um and evaluating those open source security tools and understanding what what are some of the uh leading practices and and tools out there that are going to help us to reduce vulnerabilities within our software applications and our software development processes to help us get stronger and and help us you know help
our applications be more resilient to attack um and just overall um you know reduce threats and vulnerabilities so um that's what this talk is about is the top five open source security tools that we think every developer should know all right so just to kind of get rolling here uh you know quick introduction so I'm my name is Chris Kennedy my last name is very difficult to spell you can just call me Chris uh but I'm the VP of security engineering and ciso at jit we are a startup uh based out of Tel Aviv Israel like many other cyber security companies uh we're about 40 people strong focused on application security uh and this talk is really
um you know it's it's it stems from a lot of the work that we did on analyzing open source tools and sharing some of the findings uh and some of the recommendations uh from the talk um prior to joining jit I joined about nine months ago um and I was the first U.S employee uh my other um you know co-workers and team members are all based in Tel Aviv um I was with KPMG for 15 years so I did you know cyber security Consulting I let our Cloud security compliance practice at KPMG which basically meant that we we took you know different you know service providers tech companies could be startups could be big companies we took
them through these arduous um you know Cloud security compliance processes many of you are familiar with I'm sure some are more Baseline like sock 2 and ISO some were super challenging like fedramp uh it was an awesome experience I love the Consulting side of the house but I solved it too many times we'd come in as a consultants and we'd bring in processes that were you know they're too heavy-handed too laborious developers didn't own them they didn't stick they would they would you know really stifle developer velocity and ultimately would make it challenging um you know for for products to grow and improve over time and the developers didn't want to utilize some of these
processes so I got the opportunity one of my clients started jet which stands for Just In Time the company they work for in uh really give you know gave me the opportunity to say hey let's get let's you know the shift left movement again but let's let's give developers you know real tools and functions they can utilize uh to improve application security so that's a bit about me um I'm a you know I love to travel um you know I I love um I love live music as well um definitely love the outdoors so it's great to be here in Salt Lake City you know obviously amazing winter with the uh the ski conditions if anybody got out
there I'm sure many of you did the local is incredible and summertime is amazing here too by the way the hiking and the biking everything else so nice to be here I live in Texas so like many other Texans and Californians we like to come and and enjoy your your land so thank you for that um all right so um one other thing too I want to share is that since I am so I'm the first US employee for jet if anybody wants to snap a quick you know photo here or there I would appreciate it and send it to me because I like to send stuff back to the team in Tel Aviv they you know
they wish they could be here quite frankly I mean the developers of my team they love these conferences so uh I'm very proud to be an ambassador for a company um all right so kind of getting in the talk here um again the five open source security tools every developer should know what are we gonna cover first off you know categories for the tools right we're gonna go through a structured process of looking at you know how we kind of group the different tools and where they fit into the software development process um then we're gonna do an evaluation of those open source security tools kind of how we how we do the evaluation then
I'll share some specific recommendations and you know just to be clear is that these are our recommendations um again we're startup um you know we're we're fo you know AWS serverless GitHub uh it's actually quite nice to be a company that started the past couple of years because we were very Progressive from a CI CD perspective I realize not everybody has that luxury uh in the room maybe some more on-prem and Legacy Tech that's part of your you know part of your environment your Tech stack but still I think the recommendations will be super helpful for you guys um and then you know how to leverage the tools of overall and then how you can
learn more about the tools and of course follow-up from there uh all right so here's the here's the categories for the tools that we're going to go through uh of course we got our code scanners you know our static code analysis scanning you know looking at you know Secrets detection that's a very important piece uh you know dependency checking with all the focus on software supply chain and making sure our software libraries are up to date you know is a very uh you know key attack Vector uh especially the news in the past couple of years infrastructure is code scanners so we'll look at those as well uh container scanning for your software packages and
then runtime scanning as well so those are the five categories that we're going to cover um all right so first off how do how do you evaluate an open source tool security tool and how did what was the process that we followed uh you know to be able to kind of pick the tools like Pikachus because there's a lot out there uh one thing I will say before getting into this too is like why open source you may Wonder right open source a couple reasons why we really evaluate as a startup we love the fact that it's free obviously having a free tool out there is fantastic um you know if if it if it beats the
need uh we also like the fact that we feel like a lot of these open source tools and the way that they've got a community supporting these tools if it's you know obviously if it's maintained appropriately we really like that fact right getting away from the whole security by obscurity and having a community kind of building some of these tools and the kind of different inputs that's a really valuable thing um so that's that's why we like open source not that we don't like commercial tools as well there's great commercial tools out there too uh but this talk will focus on open source um now the evaluation criteria um you know if you look at the result
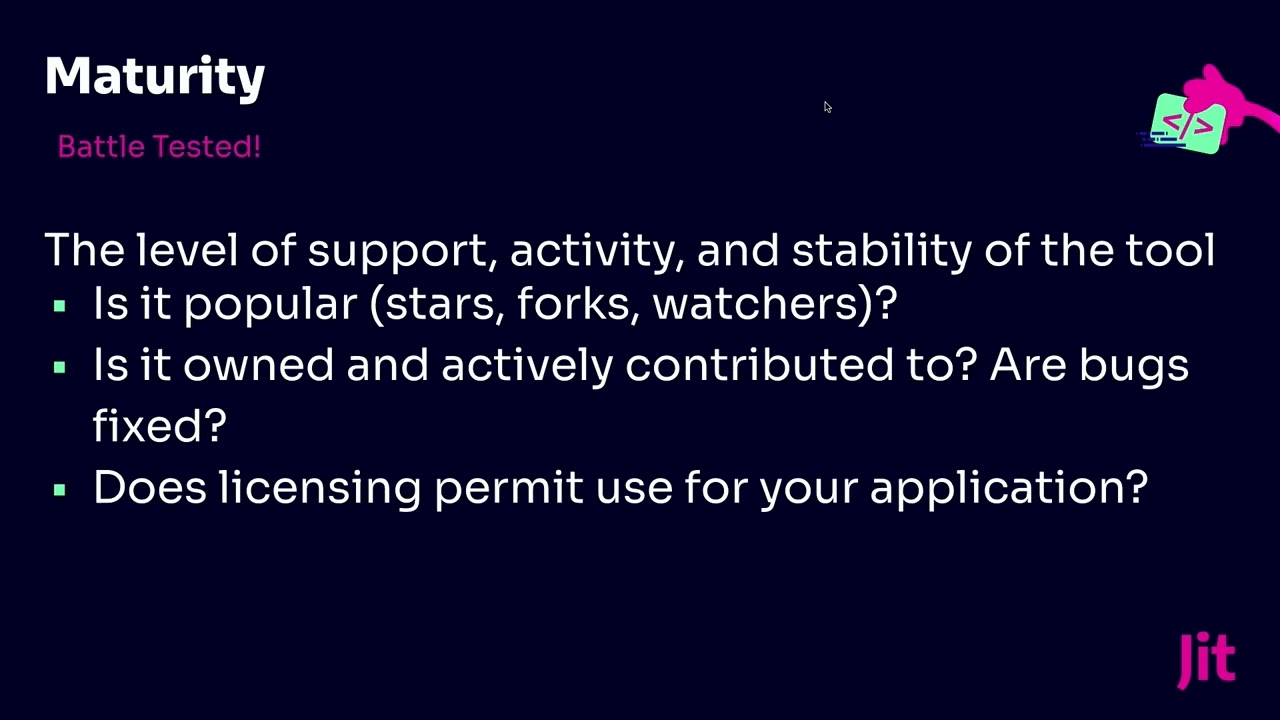
quality obviously it's so important out there that you know the findings from the tool right are they accurate right can you trust them right that's the most important thing for any Tool uh but certainly for for an open source security Tool uh the next one is developer experience uh you know again if we want developers to really own these to own security it utilize tools and have automated ways to build detect vulnerabilities and fix issues quickly adjusted time within your you know within your code as you're developing uh we want that developer experience to be as you know as easy as possible quite frankly uh maturity I talked about you know we like open source because we've
got these different inputs right we might have there might be a team lead or a development lead but there's different inputs but how often is that tool being updated you know is is it you know is the tool been stranded is it um you know is there a potential that um the tool isn't you know is no longer being updated to with the latest threats and and issues that's an important piece and then of course you know the customizability um and I get you know for every environment's a little bit different so you want to make sure that tool is going to meet your needs and your environments this is kind of the high level criteria
that we utilize just to kind of start our process right for our evaluation of the tools um and you just you know cover the the topics right so for your result quality look at accuracy you know the the developer perception of that result correctedness right so we want to make sure you're looking at how many false positives and false negatives are out there right running the actual tools on your code all right and um and you know getting those results right that gives you comfort that you're getting results that you can trust as a developer um so that's a really important piece and then comparing those results you know with other tools as well for the Developers experience right you
look at hey can we run this everywhere right locally on our terminal in an iede within the CI it's got a You Know It's gotta be it's got to be more quickly right the tools got to uh you know quick scans quick results uh you know results can be are easily readable uh and we can you know run the tool ourselves to kind of feel you know get that experience as a developer um from a maturity perspective uh you know the level of support activity and stability of the tool again is it popular you know I think about like the restaurant reviews here right before you go out like there's a million good restaurants in Salt Lake City by the way
and like there's they're growing all the time I've learned that coming here for work quite a bit uh what do the Google reviews look like right for or if you still use Yelp for the Yelp reviews for uh for restaurants um you know the Stars the forks the Watchers it's not everything but it's an important thing to look at right what's the community think about this tool um is the tool owned and actively contributed to it I talked about like is it tool stranded you know is it or has it been updated on a regular basis you want to check to see that and then of course the licensing right because sometimes you can say hey the tool is
open source but you just get this little piece of it right you know you have to pay for all the additional uh you know features and functionality um so that's an important piece too from a licensing perspective um and the customizability uh you know the extent which the the tool can be tailored for you again based off your your environment uh right so if it's if it's too generalizable that you know does it the potential for Less you uh utility for your environment uh you know and can the tool be configured specifically for how kind of how you operate the languages you use uh you know how you know your cicd processes right so that's an important step too so
it's not it's not one size fits all um all right so now that you kind of understand hopefully the process that we went through and how we kind of analyze the tools let's go through each category show the tools and show what we picked um so we're going to start with code scanners um so first off again what do we mean by code scanners um identify vulnerabilities I like this I'm not again I'm not a developer I'm the ciso but uh code spells issues with your code um you know could cover the OAS top 10 the cwe top 25 you know secrets that are out there you know any custom rules that you that you don't want within your code
you know things like that so these code scanners can help you detect those issues while you're developing so here's here's a list of Open Source uh code scanners and you can see that we group together the SAS scanners and also the secrets detectors uh Secrets detection in here you see there's quite a few tools out here uh I'm not sure if you know I'm curious maybe we could talk after the you know almost a lot of time here but you know are you familiar with these tools because we spent a lot of time kind of searching and enumerating these tools and then evaluating uh the tools so can we we looked overall you know some of these tools like spot bugs
Bandit AWS get Secrets semrep uh you know listed here on the screen get leaks and we chose semgrep along with Git leaks right so a couple reasons why one okay going back to our criteria result quality we felt like some grep uh you know really helped with the uh from the security perspective you know many different security tools were integrated within some grep like get leaks for the for the um the uh the secrets detection and then it supported so many different languages as well so we like some grep open source for that reason um and here's just a quick example showing how uh git leaks is actually running within some grab for the secrets
detection just a simple way where we uh we were able to run and detect uh you know some potential Secrets within our code which happens all the time right so we want to you know continually check for that um you're kind of looking at the developer experience for some grep you know again it runs everywhere so that it met you know to kind of check the boxes there and then it's super fast right there was no compilation we're able to run some grep and get quick results back on issues and vulnerabilities within our code and then that customizability perspective it was super extensible many outputs you know anyone could write the rules again it was simple to write so we
felt like some met the you know uh fit the bill for us across all the all the criteria and again the power of having git leaks within some grep we also like Shuffle hog as well from a secret detection perspective so that's kind of how we looked at um how we looked at the the code scanners um here's the sub view of the the maturity perspective and I think it's cool to look at like okay like how many users um the GitHub Stars the docker polls right it's kind of like the restaurant reviews this gave us a lot of confidence that hey we like the way Sim rep works and the community likes it as well right
so that that helped us to uh helped us in choosing some grub uh all right so up next is dependency checking um you know second on the list here for good reason with all the software supply chain um you know issues out there and breaches and attack vectors you know Bad actors are certainly looking for that now it's front and center uh I think there was a really good talk earlier talking about how like ransomware has come down a little bit um but certainly if you look at like software supply chain you know that's that's that's front and center with a lot of the breaches out there which I'm sure you guys are tracking you know what
is this again it's we're detecting open source components with publicly disposed disclosed vulnerabilities so looking at this term SCA or software composition analysis to find those vulnerable libraries and software packages in our in our environments um so what were the contestants um you can see here on the screen uh you know quite a few that we looked at um and there's actually I love giving this talk because I've given it like once or twice before and we've actually updated here uh because we you know um in terms of the tools we're utilizing but you can see things like if you're familiar with npm audit o wasp has their own tool called dependency check but the
one in the middle there open source vulnerabilities by Google we just we made a change and we're using that this now uh osv by Google um so always which is actually called so it's osv scanner is kind of the scanner that runs at the top and then uh Google manages the the database that of the the vulnerable software libraries that runs underneath osv scanner so we really liked it for that reason um you know if you look at the result quality right there right hey if Google's managing the database again it's open source you know it's Google's kind of managing this open source project uh we like the fact that it's at the osv scanners leveraging that osv
database of all those vulnerable software packages underneath uh you know Aggregates the curated sources so things like GitHub security advisories as well and supports a lot of different languages um now looking at the developer experience you know uses that osv schema it can run anywhere so we felt like from a developer perspective super easy to use right um you'll see the the scanner is very lightweight in terms of running and again the power of that that osv database that Google manages um you can also see on the screen here it shows some of the things like the open ssf if you guys don't open this us up that's another good source to say hey what's the quality of this open source
uh you know project uh got a passing grade and then you can see some of the stars and the forks and the Watchers here on the right hand side uh the customizability um again ability to scan specific uh software building materials that was great multiple options including a recursive uh scans we like that as well and then from a maturity perspective you know really seeing this take off and this is this like star gazers uh chart that we looked at we can see that a osv scanner you know a ton of people are using it I think I think it went officially live at the beginning of this calendar year if that's right yeah actually back in December of last year
um but you know it's taken off right so we we like it for that reason you know a lot a lot of key contributors there and people that are using it and liking it all right so up next is uh infrastructure is code scanners um and you know this gets into detecting those you know those misconfigurations I don't know why you know AWS out of the box and gcp and Azure why they have some of these default settings which are are not great that need to be corrected but they're out there of course you can have you know inadvertent misconfiguration in your infrastructure as code things like missing encryption you know permissions are too broad not you know appropriate
logging some of the basic you know kind of minimum viable security pieces that could be um a problem with it within your infrastructure as code um the contestants here for infrastructures code we looked at TF SEC by Aqua kicks by check marks I check out by Bridge crew and then Terra scam by tenable we chose kicks um a couple reasons why the result quality I think what's really amazing about kicks and running all these infrastructure scan as code scans you know 2 000 queries so there's a lot of things a lot like a lot of potential misconfigurations that Kix is looking for then there's this nightly build right it's being constantly updated uh so it was a ciso I got a lot of comfort
around the you know how often kicks is being updated um and then if you look at the developer experience again you know all these built-in remediation recipes so it's not only hey we found this misconfiguration well what's the what's the fix right so Kix has a lot of those built-in remediation recipes and they can run everywhere um and then that customizability you know you know the the queries can be written in a lot of different ways and supporting these uh kind of supporting new Frameworks as well so we were like how we could kind of cater kicks to our environment and then we and they and with from a maturity perspective we saw that kicks had a you know a lot of you
know queries uh your users uh was constantly being updated so we got a lot of comfort around the maturity of kicks as well here's just a quick view of like what it looks like to run kicks is it uh like with an Amazon EBS or elastic Block store they were running kicks against that specific resource uh and they came back and said hey there's a couple of findings here uh where the text here in pink that shows and there were some unencrypted volumes it ranked them as a medium it gave us the the result the the risk ranking you know the data that we needed uh kind of usable data from that perspective uh let's move on here and I'm going to
talk kind of quick because uh there's a lot to cover here not to go kind of Gym manico style on you guys but uh I'll wrap up here because I got a few minutes left but uh for container scanning um again what you know container scanning detect vulnerabilities and and configuration issues in our container images uh we looked at trivia clear and gripe with a three kind of container scanners we looked at from an open source perspective uh we like trivi uh we like the fact that it supports uh scanning container images you know all these to get a different um you know different types um so we really like that it could generate an s-bomb that was that was
helpful as well from a developer experience perspective super simple to set up right so our developers that got trippy going it could run anywhere it didn't take long at all to run the scans uh from a customizability perspective uh again very extensible you can write your own logic you know plugins right into the CLI and it's highly popular with a large community you can see some of stats here on the screen a lot of people using trivia out there and then here's just a quick quick example of the results from Trevi it shows hey it's got you've got the cves tied to a specific risk ranking and it talks about you know specific uh specifically what the vulnerability was
that was detected uh and then last is the runtime scanning definitely not least um you know from a runtime perspective of course at you know you do everything you can to shift left you detect those vulnerabilities as much as you can as part of your development process but you know there's going to be new vulnerabilities or you know you may you may have to you may have to release some vulnerabilities into your environment you may not know you did it so that Dynamic application security testing that's a big uh you know a really important part of any good security program we looked at zap uh a wasp zap we look at nicto uh Wapiti and then arachni is
contestants for our Das scanning um and we chose OAS zap um if you guys have used zaps is probably the most popular open source uh you know uh web application scanning tool out there we actually hired Simon Bennett's who who runs the zap project we actually hired him at jit so he's part of our team now uh which we're super excited about uh but we like the fact zap's got you know a ton of features out there it's aligned with the owas top 10 which is really important all these different rules you know fantastic and then from a developer experience you can run it pretty much anywhere you know pen testers use it developers can use it you know really
good um you know really good developer experience uh could be integrated into your CI CD pipeline um and then you know super customizable a lot of extensions out there uh it can extend to the CLI and then you a maturity perspective it's again probably the most well-known open source web application API scanner out there so that's why we like zap uh here's a quick view of the output from zap you know detected some of the you know vulnerabilities um and actually shows in here um you know specifically what was detected you know cross-site scripting attack uh gives a gives some of the information like the the severity and other other important data um that's uh that's part of a zap a zap
scan this is just the kind of the the the the code here the the results back all right um I know I ran through that really quickly uh typically I'd maybe spend more like an hour on that but I wanted to kind of do a brain dump with you guys just show you all the work that we did on analyzing these open source tools and kind of getting them all into the uh you know making the selection the right fit for us and the reasons why we use them um so here's just a quick view of like all the different types of tools that we're utilizing at jet uh and I you know I think the one thing
um it took a bit about our product for just a minute is it one of the challenges like okay great I've picked all these open source tools I've integrated them my CI CD processes I'm going to run the scans you know um on a regular basis you know for every code commit that's still a lot of work as a developer to build a manager even though you pick the right tools for your environment so how do you manage all that I mean the answer is an orchestration platform and that's exactly what jit is is a security orchestration platform so it jit you can actually utilize all the tools talked about you can you know you can integrate
and again if you're using GitHub and AWS super simple to integrate with our platform and then once you do you can turn on all those tools and then we'll orchestrate those we'll run all the scans for you you know so you know as a developer you can stay in GitHub all the results so it's actually the next screen here you know the jit will run automatically for each each code commit each pull request let you know about any findings that were detected you can fix it right there so you have to go to some security meeting you don't have to go you know uh be sent some report you have to go look at something else you can
stay within GitHub and fix the vulnerability right there or determine it's a false positive and move on um because that's really the future of security in our minds um and then there's things like we can see exactly like per pull requests and like for the past couple weeks you can see specifically about uh you know how you're performing you know are you fixing things are you ignoring a lot of findings you're getting a lot of false positives maybe go back and reevaluate some tools and configuration from that perspective so a lot a lot of capabilities there um great all right well I'm gonna go ahead I'm going to uh stop here um because I realize I'm a couple minutes
over I'd love to talk to anybody I'll be hanging out for the rest of the day before I head back to Texas but again thanks everybody for your time if anybody took any pictures uh please send them over you'll eat feel free to email them over to me Chris jit.io would appreciate that um and again any questions about about the product about the you know how we picked open source tools and kind of a deeper dive um let me know and also I have some uh we have some amazing swag our branding is awesome I'm wearing the T-shirt but um if you'd like a water bottle or bag please come say hi to me I've got some
stuff to give away and thanks everybody for your time foreign