Why does everyone want to kill my passwords? - Mark Burnett
Show transcript [en]
ok so again this is Mark Burnett our last speaker for today he is the author of the very acclaimed book perfect passwords I was actually considering to bring in here to Las Vegas to have it personally signed I still have it at home mark and I again mark came with this talk have you actually been tormenting your family over this I am ok yeah time so I think there's gonna be very interesting to listen what's he ever actually be done in doing so mark your free dude kassad all right ok um I'm Mark Burnett I guess hi MA I I did stuff and I talk about stuff so but on my first slide here i'm going to read my
intro ok so this talk is about passwords and killing passwords and really the mess we've made with the whole password thing because although we like to think that we have played a part in making the world more secure mostly what we've done is alienate users we've made them log into everything over and over and over and over and over we tell them to make sure the password is really strong but don't write it down and of course don't forget it be sure to add some special characters or sometimes when it's a bank don't include special characters banks we bombarded users with I gotta change my screen here the NIP bombarded use it with a never-ending supply of policies
CAPTCHAs remember me boxes on behind now and of course you don't check the Remember Me box even though it is everywhere and of course usually retaliated how they know best with memes and you know we can't blame them because we created them we recreated those monsters and they are monsters but I have got this little analogy here actually I just saw this video has got to find a way to work it in we are all losing okay now i don't know i don't know if you notice it it's kind of quick but um i watch around this year i'm going to zoom in and it slowed down but watch around this area because there was
something just kind of went by real quick there you probably missed on the first time so alright so we've been doing passwords for several decades now and you think we've pretty much got it figured out right but but let's let's look at what we've accomplished and let's just kind of do a report card here password policies seemed like a good idea but you know it turns out we really don't know what works I mean users have bad passwords so hey let's force that bit passwords but that kind of end up with not enough requirements too many requirements strange requirements no no two identical consecutive characters and I don't know if you know me on twitter i
complained by a lot of stuff short pass for explanations policies for policies I mean come on failed user education you know they're still confused with as much as we've we've tried there they still suck at passwords they still hate passwords they still want to kill passwords they're always trying to find some some way to work around their passwords so we're going to fail on that too
password manager hey now I know we've talked a lot about password managers and it's kind of important thing to a lot of people here a lot of person here but you know we've got to face it they're just a temporary fix they're really not a long-term solution they kind of tacking on to tacking on to this problem we have a password and we're trying to fix passwords by having password manager but yeah Hardware tokens hey no talk Hardware tokens we're doing for decades now I mean we've been trying to get right and we've tried a lot of different things but the thing is I've ever tried to get someone to use a hardware token who isn't in the security business or
Leslie you know the company forces them to you know it just doesn't happen and there's that now biometrics hey users like those fingerprints I scanner is voice matching you know movies have been doing it for years it looks cool seems really secure I mean you got it if I mean if it's something really secure they're going to voice match right but you know we still haven't figured out how to make it we really haven't made forget make it secure and we haven't figured out how to make it anonymous and we haven't figure out how to make it work everywhere yeah oh I don't have sound I just realized the house cool pop pop okay sounded like that kind of
alright so the way the stars is until this this particular topic stars until had me write an article a few months ago and and they've seen they seen a lot of my tweets and stuff and they thought hey it wouldn't be cool if we got we wrote an article about killing passwords and they thought you know it was gets a bunch of equipment it's let's let's try it out on my family you know and kill password see what really works and yeah that didn't go so well but I got I got um some wearables stuff some some you bikies I'd bunch of those laying around hi scanner a fingerprint scanner and password man tried to use intel spooky
and this one mimics parent was really fun for me but um you know I I did it for a few weeks I got all my I got all these things hooked up you know got everyone in my family I def I got you know I had this interesting it was pretty diverse thing in my fam I got my eye to my wife you know both I that's another story my three my boys I get for and my father-in-law oh hi especially my father-in-law I'll just let you guys just I don't know if you can see those big
you got to read some of them my father-in-law put tape over his webcam transparent scotch tape I'm amazed at despite my best efforts my father-in-law's ability to fill his computer with every Spy were known to man my father were locked today told me he needs to get a copy of Harvard graphics then I realized you serious I'm just going to say the world is not secured till my father-in-law can go 90 days without getting some kind of infection on his laptop no every hack today wasn't because of the passwords I released seriously people like my father in law okay my SSID used to be not found my home group blocked and we flexed over broken my father complains that nothing
works at my house well I have so many stars what's that hey so anyway I've got a pretty diverse group to pull from needless to say my father-in-law got the cat book which is you know password manager Kathy password manager disguises a book about cats anyway that's really interesting though because I got I got this stuff I mean I got this you know I got one of my son's to use you bikies I was kind of hacked but I got him to you know use him for all those different passwords someone were static ecstatically up hard coded passwords but you know the whole thing was to kill passwords at that point my wife got her
this does this fitness tracker and the thing is though you know once she found out that it's worth how much was worse she's going to sell on ebay so that in last the it was just like I last about three weeks and then you know I can see I it all end up back in on my keychain again they just kind of they just kind of gave up on it but why can't we get people to to use this stuff I mean why is it so hard I mean I couldn't get my own family to do a knife would think I like to have some kind of influence over them what do we need to do to get user participation
here wait oh hey listen to mall okay so
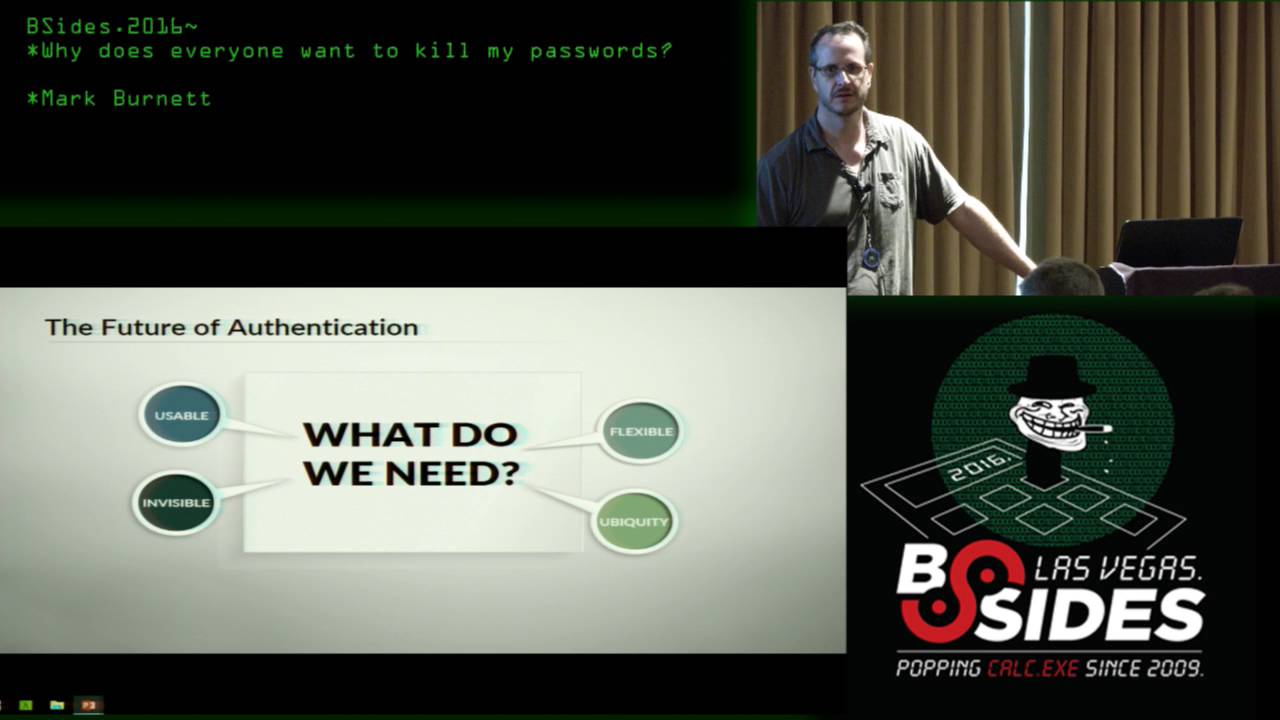
it's got to be usable I mean it's it's if it's not usable I mean obviously it's got usable but you know it's got a its got to have its going to be easy to install it's got to be I can't have a lot of terminology you know crypto terminology it can be frustrating tudela yeah it's guess that's thing with my wife she gets really frustrated with stuff so if it doesn't work like the first two times he's ready to give up on it so it can't be frustrating these be flexible needs to work across a lot of different platforms now we get it there's a lot of cool authentication stuff but only works on windows or it
only works on your mobile so it's got to work on different platforms it's got to be compatible with a lot of different authentication technologies I mean windows hellos nice but it lost stuff you can't use it you can't use a you be key to log into windows hello it's got a its got to be invisible it's a user and you know they just really got to feel like they're not even using it i mean that's that's the biggest problem with passwords aren't they're far from this invisible they they're struggling with them all the time i mean just just monitor the key word password on twitter and yes silloth it's kind of funny but you see all kinds of complaints about
passwords and it's got to be ubiquitous i mean if your bank sent a sends you one token the only works with their with their website what's the point of that it's got to be something that you can you can use on all the different websites or all the different systems or only works on websites but not their less or vice versa I mean it's gotta be something that that works across different systems so with this in mind you know I decided to take to the extreme okay didn't work with my family but I thought I tried myself I mean I'm pretty brave so I I got all this stuff to get I had a few
more things my keychain I got this you know there's that I track her and you know I installed it all my system I system really doesn't boot and very well anymore but but I did I installed it all you know and I um you know I tried it off like what you know what are we doing wrong here I mean what am I why isn't this so hard to figure out and just to be clear we're going to killing passwords anytime soon you guys know I'm just skip that one so let's talk about password managers I said there are temporary fix they're just kind of a crutch to get us through to make passwords usable for now I mean it may
be 10 years maybe 20 years but they're really not going to last it's not a long-term solution here I mean we don't know our own secrets i mean we create these least we don't even create the secrets that generates a password for us it manages the the secret for us it enters the demand for us but it's not just kind of breaks the whole security model breaks a little concept of having a secret because yeah we have this this master password but it's not really way this is going to work and we just got to look at that look at passwords there are transitions or should be there to get us to this place where we can we truly have
a seamless system where we're you know we're doing more than just typing in static passwords you know tulus type type in sac passwords for us sorry but to get that to get to that place we're going to have to get operating system support we're gonna have to get browser support I know that was my quest now yeah he thinks that browser shouldn't be involved but you know you got to have the operating says you gotta have the OS it's got to be have a trusted platform to run the browser and the brothers going to have that trust authentication platform to log in to your websites and if we don't have the browser involved if we don't
have the operating system volved we're just not going to get that I mean it's just we have to the only way we're going to do that is to get every component integrated and so who's going to do that not in search who's gonna do that I'm asking for volunteers no okay okay so what you have we've been doing this for a long time we've got we've tried magnetic stripe cards we've tried smart cards token generators all kinds of technologies and that's what users want they want something it's easy something is plug in or or you just be near a computer unlocks it if it if you lose it you you've got this thing Galaga if you
lose you grab another thing and that's your thing and you do that to log in and you lose that thing and you get another thing so you know that's that seems like a great solution but you know hard work the classic trade-off between hard work the classic trade-off between security and convenience and you know what seems great for users really doesn't work well for security soap and vice versa but you miss them let me do it again for you so around 2005 a lot of websites realize they need to do Lydia thing to make things more secure so we started like paypal and ebay and some banks they started distributing these these vasco go tokens you know you push the button
it gives a six digit code and actually i really like these every night I've had these for 10 years and the battery still works I still use them on my paypal account but I guess they really kind of thought for the for the companies because they just you know they kind of it got to where they pay pal just kind of hit that that feature for a while it must have been a major sport headache so we couldn't what's that exactly nobody use them but me and like you probably and like some other guy so Bluetooth now a Bluetooth interesting because people are always trying to I mean Luke to seems like the perfect way
to do this you know you don't have to touch it just go near your computer it unlocks its but it's not exactly secure I mean you it's always on you know it's easily spoof able it's visible I mean within 30 feet or more if you have a if you have a I mean sometimes I've seen people will do up 200 feet this right antenna vulnerable to man the middle attack i think there's going to talk at DEFCON about that but we keep you know keep put everyone keeps going back to this these blue to stuff and the protocol is insecure there's just really no fixing that unless unless we fix the protocol but one thing you do is you
treat it like it's an insecure network and we know how to deal with in secure networks I mean you you have proper key exchange you have certificates you can have pin certificates you you don't just detect the presence of a Bluetooth market or as you you exchange you do a proper challenge response you exchange a time base or digitally sign time Bates token but no one does that it's a problem is this tractor used for my wife what I just end up using some software effect I there we go and we used some software this rojos it's kind of cool you you have all these different things you've got USB flash drives well Luke with Bluetooth key p kc s number 11
security module you back east you can plug in all these things and they even laden with windows really nice i did that with my wife integrate it with a couple other things tasker and some stuff on her on her phone and you know i worked good until like I said ebay you know my wife sake now on that you know stories my life anyway huh that's right I study DEFCON badges feel like from five and six but you know let's go for a lot of money on ebay it turns out so try a these fitness trackers actually kind of cool because you think about they've got first of all it's something you have you know you've
got possession there we also got GPS on some of them you've got biometric markers I mean sent this one's got a heart rate sensor you know that if there's done authentication through heart rate it's got microphones on it you can do voice authentications got galvanic sensors you know it's basically got a lie detector test on here not a watch but I mean there's a lot of different possibilities I mean you could you could if you really want to make that work I mean wearables are really interesting and it was you know it's pretty transparent of Microsoft try to do do it with their bare thing called so variable called fan yeah they're real band and either which is basically if
you push a button gatekeeper now this one's kind of interesting I don't actually like I like this one so this little thing right here you get a USB dongle and then you just put on your keychain you walk up your commuter answer it's really accurate like you can see how far you want to be from a from your computer you can say like three feet or five feet or 15 feet it's really and you get within three feet it you know locks and when you lock way it unlock or other way around you can choose how you want to log in if you want logging with just the gatekeeper or with a pin or whatever it is just really
cool I really actually kind of had fun with that one but then I saw this thing just enter your winters paso and enter your windows password below this enables you to log in to your PA whenever someone asked your windows password you know that's bad sign when it went it went authentication so I saw this and I saw this and it was just bad I mean I don't you can see here vice Mike 10 you know and the encrypted and there's the call the code for encrypting it and yeah it was just bad i mean it's kind of sad because that was kind of cool I know I've worked with I'm we've been working with them and they're
they're improving that but it's you know it's that there's a lot of potential there are something some way we can go without you know some bluetooth device it's pretty seamless for the user you bikies right I mean we all like leave a cruise how many people here have you baqi all ride how many people out for you bikies one two three what's that on which one
the 40 well it depends on how I mean what kind of crypto you're talking about because there are i mean the yuki is writable and you can you can put in you you can write your own java modules in there so i guess it depends on what you're using for but you know it depends on how your how you're using it and i think i think you big he's probably the closest to to getting a real hardware token it's usable it's cheap you too you too f standard a few of those you to have tokens this one here it just kind of folds out and tape Phil ruin I got four five dollars on amazon widespread
adoption a lot of people well I should say widespread adoption among us really easy use you know put in push a button the it's got the the ue key itself got the OTP smartcard channel response other stuff but we still can't get people to use them I mean I gave my son three you bikies for all is different you know that's six different passwords because you know it's about Ali had I still couldn't give an use it for that I have my one of my son's I my tan year old like he actually still uses his you Vicki yeah you know logging into here's the only one of all my family who actually survived the whole thing uses
you've a key to log into gmail but but we can't get you be able to use them i mean that's about this easy as you can get right in SC rfid got a ring here got two little NFC tags on it and OA got on the back of my back when I got a Hennessy tag back in my wallet I got ya see tax I can yeah swipe my wallet and in the bathroom I can swipe and launch my apps I need on my phone
yeah son someday yeah the Nano I believe or yeah I think I don't know one of those RFID is cool that rfid thing you know I'm yet I mean I got these these little scanners i put on my computer i used to seeing my computer with such a mess you know all the stuff edit a stuff taped on there because i had a you know so i got NFC and rfid you know so it's kind of guy i actually got another one for my garage so i can open my garage door with that and i work but great for that but I don't you know the thing is you can't change it it's just a code I
mean it's spoof able it's easily copied you can't turn it off so it's not like like Bluetooth I may at least blue to it you can kind of secure it by only turn on when you need it you need a reader okay you know those readers but I don't know what that is oh so I used event ghosts in Windows i used the realest thing i use tasker and kind of got all the stuff integrated it worked out pretty well and it's really cool but it's just not secure at all I mean might work for home users than that I don't know just don't do this I mean unless you got some foil gloves or something
because you know once someone I mean it's spoof legislation sees someone scans it and you've lost it you gotta like what do you pull it out and put anyone in and you can't really change it and that's worse than your fingerprint mobile devices some some based on Google off maybe there's a lot of them some are proprietary simi's algorithm some these personal custom algorithms somebody's push notifications some use a combination of that those things they're really contour easy use everyone's got them some kind of mobile device people are more willing to protect it and they're going to notice when it's gone it's not going to be gone for long the problem is is they're vulnerable to
remote attacks you could you could have some bad apt someone installs there's they're slow to replace and you can't just go get a new one on the plus side there is a lot of support for Google ah i mean i've probably got 30 40 on my google authenticator and it's just constantly growing so i'm not going that's you guys get that so oh I forgot about it yeah that's that's what I call him what can be chopped off I kind of ran out of graphics so I started using some stock photos so i guess thing is with fingerprints finger I here's my fingerprint scanner it's a little tiny one the problem with fingerprints and this is the authentic they had oh they
had a problem where they were storing the password encryption what the way that some of these things work is another reason why I said that was bad news when they about a bad sign when they ask you for your password though they'll encrypt your password and it has some logic in the program that indicates you and if you pass that's dedication then they decrypt your password and use that to log into windows and so that just means your password stored somewhere and most likely it's got a hard-coded key somewhere or based on your PIN and it's really cool it's built into windows you know but the thing is you can't login to website your fingerprint you don't have you know
there's not really much you can do with it and just log into windows that's why there may be your M your mobile phone as well and oh I risk no irises are interesting I like this one the best that camera is just kind of weird I think
and this was my personal favorite because I just worked really well it was just really seamless it's almost as when worked almost as well as the UH the bluetooth yeah okay so me my kiss it says looking for you making sure it's you it logs me in so it's kind of it's kind of cool I pass pictures I kind of freaky but yeah it's just I mean if we could get this something like that to work I mean like I said we get the OS support we get the browser support and then we get the application support but the thing is we're not going to walk in not going to log into any websites with
this so it really not much look I should've got a big pitch i guess but there's really not much you can do with it other than just I mean oh you can play asteroids kind of cool you can you look at the asteroid in it blows it up and some games but it's not much you can do with other than that it's I mean it would be nice if we could get that more commonplace but they aren't really cheap has about one hundred eighty dollars for this guy's to the up so they're all catering people waiting outside yet take over the room so I have to ask mark to speak every five minutes five minutes k
acta de yeah oh you give it away Hayes voice fix don't ask for passwords if you ever do use a i could meet you cut biometric or alternative indication you ask for your password there's several of them that did that it's just that you know they're storing it somewhere oh and there's this thing I mean you've got a class pass you can use you icky but if you lost lost your Ubik you device click here to disable you with key and then over here it says use email verification instead so it's just kind of I why not just e-mail verification in the first place I mean it's you're not any stronger than that weakest think they're so expanding
modalities well we I go back to fix fixing it is you start strong work backwards we allow a lot of different allow support for a lot of different types authentication don't I mean these lot of these like LastPass for example it lists you know these these certain two-factor authentication things you can use you know if they're not I obviously not gonna be available on every device for for every person I mean not everyone has fingerprints I mean you know it's just you got to have flexibility based on where the user is what kind of ice are using where they're logging in from and other factors that you know that could make it potentially suspicious so
you kind of take away you know is this suspicious you try to take the score away then you add on with this the stronger authentication factor is determined to get you back to up to where you need to be you know to a certain score to to pass them and here's some kind of testing things that you could look at where you where where you are when are you there where you were which device you're using who you know who is with you but I hear something you probably don't want to use um something you forgot something you lost anyway something UAE's how'd you bleed so I thought you guys might want to use the hashtag and kind of carry
that on but rules based authentication of that's one thing I'd like to see I'd like to see some kind of I mean with uh with like within the windows hello for example you can log in with a fingerprint or with your face or you can log in with your pin code or password but would be nice to say you know I want to log in with three of these three out of four or I want to say you know these times I want to log in three or four if i want to say if there's been more you know certain conditions i would be nice to have a rules-based setup that you can decide either we could decide let us
have five different ways to authenticate you have to about three of them artificial intelligence there's there's a lot of potential there for understanding when to require multiple factors or you know three or four factors for authentication then if you can't find devices some of the password managers do that were already smarter wearables that would be really cool okay but are you okay and then there's this that's it I guess they don't have questions we have questions have time for questions while they're setting up I I was told they are really eager together get in here but again you know Mark would be around so pleased you ask him questions outside





