BG - SiliVaccine: North Korea's Weapon of Mass Detection - Mark Lechtik & Michael Kajiloti
Show transcript [en]
start with short video
[Music]
yah yah yah yah yah yah yah yah yah no questions and hypotheses from Connecticut come on
let's give a round of applause for the lady in pink hello everyone thank you for attending our talk as you can see our talks title is silly vaccine North Korea's weapon of mass detection so you have something here called silly vaccine we have North Korea will soon come to understand how it all comes together but before we do so let me shortly introduce ourselves and that's us that's actually not Seth Rogen that's me my name is Mark and I'm here today with my friend and colleague Michael hi and we are both researchers at checkpoints malware research team and without further ado let me introduce you to the subject matter so I'll start by introducing you to the story over
research and how did it really begin so the whole thing began at one evening I was going through Twitter and looking for something to read when I stumbled upon the following Bloomberg article called inside North Korea's hacker army and it turns out to be quite an interesting piece about a North Korean defector who worked for a government agency and you know ended up doing some hacking and throughout this publication I found some sort of notion portrayed by the author of North Korea's so to speak offensive cyber operations and in particular in one paragraph the author mentions North Korea's official response to allegations made against it by the West regarding hacking and I quote formerly North Korea denies engaging in
hacking and describes accusations to that effect as enemy propaganda it says its overseas computer effort are directed at promoting its antivirus software in the global market the country has for more than a decade been working on such programs including one called silly vaccine well what is silly vaccine well as you may understand from the previous paragraph silly vaccine is an anti virus which is developed in North Korea for the North Korean citizens so basically that's a North Korean antivirus or how we like to call it the kim jeong-hoon t virus and obviously this is not a product you can find on the Internet it not something you can you know download it's only existent within North Korea and the
version that we are going to talk about as version oh sorry it was developed as far as we can tell since around 2003 and the version we are going to focus on is version 4.0 which was released around 2013 I should mention that we are also in possession of another version from 2005 which is actually one of the first versions of Scilly vaccine and just have that in mind so I don't know if you guys know but North Korean citizens for the most part don't have access to the Internet instead they have access to what's called an intranet which is sort of this glorified local area network controlled by the government and if that's the case why would North Korea
need an anti-virus well there are a few interesting explanations for that one is actually to protect against smuggled media and in particular there is it seems to be a phenomenon of USBs that get smuggled inside the country and then get salt and North Korea's black market and if you don't believe me that's fine because still it's North Korea we're talking about but to corroborate this you can check the following website called flash drive for freedom which is actually and I should you not crowdsource funding thing for us bees that get smuggled inside North Korea so you can today donate your USB which will get magically inserted into a North Korean computer and if you are afraid of the IRS then you should
not worry because there is a tax receipt for every smuggled USB and if you're wondering what goes on to those drives then it's stuff ranging from Wikipedia articles to South Korean soap operas which is evidently a threat on North Korea anyways there's another explanation which is actually to sell this antivirus as a product and the global market and that's actually stated by North Korea itself which says that it devoted some of its efforts to develop this product as a worldwide product so we can actually corroborate this by looking at that 2005 version of sealy vaccine and we can see that this version was written both in Korean and English which may hint at the fact that the
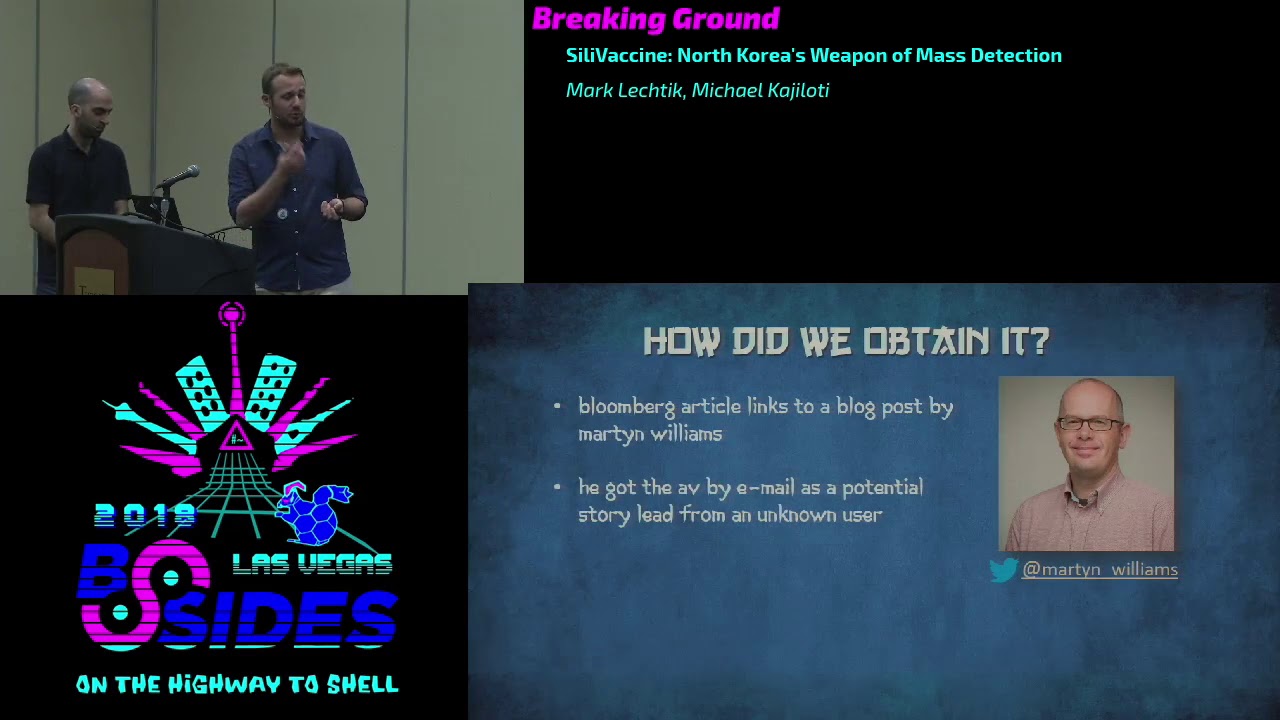
developers of this version wanted it to appeal to english-speaking users as well as Koreans so at this point you must be wondering how did we get our hand on this software well the answer to this lies in the bloomberg article I mentioned earlier which linked to a blog post written by this guy Martyn Williams Martyn Williams is an independent journalist who covers various news items related to North Korea and he himself got the software back at 2014 through an email a very weird email from a guy named himself conn-young Hawk which supposedly lives in Japan who sent him this antivirus as sort of a journalistic lead and keep this email in mind because we will refer to it a little bit later of
course martin agreed to share the software with us and that's the place to thank him because he really made this research possible so what were our goals when we started this research so first of all we wanted to understand how this program is built what is its architecture through which we really wanted to have some sort of an anthropological view on on North Korean engineering practices meaning how would engineers with restricted resources like those in North Korea would tackle a complicated problem like building an anti-virus from scratch of course we wanted to find any kind of mechanisms that could have been put deliberately in place in particular any kind of backdoor that could have been
set up by the government so as to spy on its citizens and with that in mind let's start the first part of this talk which is actually the architecture of this antivirus and I'll just go through the various components the essential components of the software so that you have a common understanding of how it's built and let's begin doing that by looking at the software libraries that comprise this antivirus the first of which is called SV shell DLL which is basically a shell extension for Windows which in particular at this context menu entry you see right here which allows the user to scan for files manually with this antivirus so you know what let's just see this feature in motion so here
we have some malware we're trying to scan it with the antivirus and nothing happens which is you know basically it seems like they had some problem with the QA on this feature but you know what the hell moving on to the second library here it's called SV Colonel DLL and that's actually the file scanning engine of this software which is in charge of actually it has the logic that implements the the virus the the virus scan of files this DLL contains 20 exports as you see right here which have the names as we found 0 0 1 through as we found zero to any if you're looking at a naming convention you you should never use and that's a
good example and of course the verdict or whether a file is malicious or benign is based both on the logic constituted by this DLL and a bunch of signature files that also reside within the package of this software third dll here is just meant to deploy other components we'll just skip through it next part of the next group of components we have here is pretty self-explanatory those are the GUI components of the antivirus the first of which is one called SV trader XE which is this small train menu you see right here and it allows the user to access any other GUI windows inside this program so for instance you can access the following utility called
as remainder XE which is a screen you see right here which allows the user to scan for malicious files you can play around with some of the antivirus configurations you can whitelist some of the files or blacklist other files and essentially this is once a GUI one-stop shop for all the software's features this component actually loads a driver called SV hook that sis which conveys some metadata on processes from the kernel space we'll discuss this component a little bit later in the presentation so keep it in mind another component we have here is also pretty self-explanatory that's the update utility it's basically meant to download some update components whether it is signatures or binaries and deploy them
on the clients machine whenever those components are downloaded they are checked by an integrity checker called SVD few PD and basically this client is talking to a server that resides within the dprk because remember in the dprk or north korea we have a closed Network and intranet there's no access to the Internet and this is why the update servers will reside within North Korea and the update protocol through which this whole thing is going to work works on top of HTTP and you can see some of the messages that are exchanged between the update client and server right here but what I'd really like you to notice is the best amount of information conveyed through those messages and you
can see stuff like a serial number and an interface number and an IP and other kinds of information that are passed on this on these update messages which for the most part is pretty suspicious but you know since we don't have any access to the real servers we can't tell why this information is collected so you know we just can assume that the North Korean government wants to collect some information for some reasons but anyways by looking at this protocol we've stumbled upon some peculiar implementation details so for instance if you look at the content length field of the HTTP header you can see that there's a typo here they used underscore whereas it should be a - and
also the user-agent that it's supposed to be that's supposed to convey the identity of this client - the update server is also somewhat peculiar so instead of actually changing the user agent field in the HTTP header what the developers did was actually to append another field called user dealer which I have no idea what kind of dealer they have in mind but it has nothing to do with HTTP and speaking of dealers we have another component here called SV dealer which is actually the real-time protection component of the software and this is essentially a service that monitors files upon interaction with them and scans them on the fly so for instance if you want to click on an
executable then it will be first scanned and only then executed and in order to achieve this this component loads another driver called as we filter dot sis which is a file system filter driver which again intercepts all requests all the user requests or interactions with the file system and issues the particular files for scanning - SV dealer before actually committing the reaction itself and again we'll discuss this a little bit later so at this point I should mention that the two components that actually issue scanning tasks here are sv dealer and as remain which would obviously have to load as the colonel the file scanning engine for this purpose but to conduct a successful scan
they would also need a bunch of signatures which is why this software has about 31 dot SPF files which we refer to as the pattern files which constitute the malware signature database of the software so the final component we are going to discuss here is called sts TDI two dots which is essentially TDI Network filter driver and if you have no idea what I just said that's perfectly fine because essentially what this component does is nothing and it turns out that while this component is supposed to be some kind of connection pool that intercepts TCP connections it never gets queried by any other of the components here and eventually just sits there doing pretty much nothing and
we suspect that this is just a residue from an older version of the Santee virus but really who knows so another note were he saying here is that most of the components you see here were attacked with the immediate protector which is usually pretty vicious for a reverse engineering fortunately for us the developers of silly vaccine did not set any particularly nasty features of this packer and we were able to handle it with you know relatively moderate effort and what you see right here is like the full architecture it's a little bit complex but what I really like you to focus on out of everything here is a component that we've already discussed that's sv kernel which again I remind
you this is the file scanning engine this is the heart and soul of this antivirus which is exactly why we are going to discuss it next and we'll begin the discussion on SD kernel by looking at what every good reverse engineer looks at strings and by looking at the strings of SV kernel which you can see right here we decided to do another very advanced thing that every reverse engineer does look them up in Google and much to our surprise we stumbled upon another file called vs API 32 DLL now here's ladies and gentlemen where it gets interesting so what is vyas API 3 Jilla well it turns out that this is actually a file scanning engine but it's
not just a file scanning engine as the file scanning engine of Trend Micro which was as you may understand quite shocking for us but it begs the question that the developers of silly vaccine actually used this component as is or did they do something a little bit smarter well let's find out so here on the screen you can see a binary diff between the Trend Micro engine and the silly vaccine engine and you can basically see that there's a 100% match on more than a thousand functions between those two engines which is like a quarter of the silly vaccines engine code also you can see that some of the export functions here have an identical match if we look a
little bit deeper then it turns out that actually all of the first 18 functions in silly vaccines engine mapped to some functions in Trend Micro's engine and just to portray it a little better let's take a look on three sets of such functions and compared to call for graphs and as you can see for the most part those functions are pretty similar but I would say that it would be a little bit more interesting to see what are the small nuances or the small differences between those pairs of functions so as an example let's take this pair vs init and s defunct 0 0 5 and you can see here this function vs in it which is basically meant to you know
just initialize some struct a prior to conducting your scan and what I'd like you to notice here is this usage of the memset function which in the Trend Micro case is just a call to ellipse e function whereas in silly vaccine is the inline version of this function you can see the same phenomenon here with the mem copy and qmm copy which is the in-line equivalent of mem copy which to me at least may suggest that whoever wrote the Silla vaccine engine had some kind of access to a proprietary resource of Trend Micro which enabled him to you know turn on some compiler optimization which was not turned on and the Trend Micro case let's look at another pair
here which is vs get VSC info and as defunct zero zero four and in this case this function is meant to just initialize some struct in memory with some metadata about the engine itself and here we can again see some function inlining but what's interesting here is that we can see the actual version that was used in Silla vaccine the actual Trend Micro version that was incorporated incorporated into the silly vaccine product so we can see that they used version eight point 910 which we know was released around 2008 and remember this software that we're looking at right now was released in 2013 so they were basically using a five year old engine inside their software the final example
here is this pair of functions of vs quit and as we fung hero 6 which is just a basically clean up function for various objects in memory and we can see that in the sealy vaccine version there is a call to a function i named as vio driver cleanup which is just function that unloads a legacy celia vaccine driver and what you can witness here is basically a call to a proprietary Celia vaccine function from within what used to be a Trend Micro function so this again shows that whoever wrote this software helped to me at least it seems had some access to right Erie Trend Micro resources at this point I should mention that we addressed
Trend Micro with this to get the response they were very cooperative and they gave us oh sorry so before talking about Trend Micro do you remember the 2005 version so we checked this version as well and as it turns out that this version also used Trend Micro components only they used kernel mode the kernel mode equivalent of the engine that we just saw which really suggests that this sort of copyright infringement was not a one-time thing and of course we addressed Trend Micro as I already said and they gave us their official response and essentially what Trend Micro cells is that they confirm that the engine in question was used by civic scene they stayed that they were they never
cooperated with North Korea to develop this product and that they basically have no idea how their engine ended up in Silla vaccine they do hint though that there could have been a possible a leak from one of the companies they cooperated with as om and in this sense I can say that other than being a North Korean product which is you know developed away from the public it's pretty hard to detect silly Trend Micro's engine inside silly vaccine and there are quite a few mechanisms for this and I'll let Michael tell you a little bit more about them thank you Mark so we just realized that silly vaccine is essentially using Trend Micro's engine and we're wondering if
it's using the same engine does it mean does it mean it's using the same signatures so if we compare them on the surface they look quite different silly vaccine uses multiple small files well turn micro uses a single large file and if you do a basic comparison you can find no similarity in structure or strings so we look deep and we found the place in the code inside Silla vaccine where the pattern fires actually being loaded and it happens in SV Colonel in one of the export functions the proprietary export function and here we can see that patent file name is being constructed a handle is being created to that file the contents of the file are being read and
then the contents are sent to some sort of a decryption function afterwards the decrypted buffer is appended to a memory to the global global area in the memory and then the idea of the patent file is being incremented and the process repeats so essentially what this function does it loads of the pattern files one by one decrypt them and append them all together now before we talk about the encryption itself let's talk a moment about the encryption key because there's something interesting here so this is the encryption key you can see here it's a seemingly random English string so we wondered that does this mean anything in Korean maybe and turns out no doesn't mean anything in Korean
but an interesting thing happens if we take this string to English Korean keyboard and try to type it while we accidentally forgot to switch to English so we would get this Korean string and if we translate this Korean string to English turns out it literally means pattern encryption so yeah now regarding the encryption itself here we can see sha-1 and a lot of encryption in going on basically we didn't really bother understanding everything because we were simply interested in the decrypted pattern files so we dumped them from memory and now when we compare them suddenly they look quite similar you can see an almost identical header and if we scroll a bit down we can find the exact
same strings in fact a simp comparison of the strings show match more than 90 percent and the difference is probably due to version differences and here we can find the trend micro's entertaining names trivial all surrender a and DJ virus which we think it's kind of fun so now we decided to test this thing so we took a bunch of files and scan them with silly vaccine and they were all detected and we scanned them with Trend Micro there were also a detected and but there is something interesting although they're using the same signatures in the same strings we're not seeing the same strings as an output which is suspicious so turns out silly vaccine actually renames the
signatures before displaying them to the user and here is an example to show you how it works so we take a Trend Micro signature George and George steal one and what's interesting does it copies that signature it breaks it down by removing any underscores and dashes and then replaces the prefix with a custom dictionary so at Raj is replaced with tlj the suffix is replaced so a number one is replaced with the letter P the casing is modified and it's all been to put together with dots now you get a silly vaccine signature so here is the dictionary silverstein uses to translate prefixes and here's the dictionary for the suffixes nothing very interesting but what is interesting with all of that
is that it turns out if you think about it the authors are probably trying to hide something so the files are protected with the media so you can't see any strings in the binary files the pattern files are encrypted you can see any strings there either and the malware signatures are renamed before being displayed to the user so essentially you have no easy way of knowing that this product is using Trend Micro moving on let's talk about some of the fishy things going on inside the this product so during our analysis we couldn't help but notice that many of the binary files contain a certain string which is pretty unique looking and this is mal dot no that F is
the string so we realize this is probably a renamed silly boxing signature because of the format but what was renamed here so let's run our renaming algorithm in Reverse and we will get mal no 5 sorry ma underscore new 5 but what is going on with this what is going on with this signature well here are two instances where this signature is referenced we can see both of the instances are in file scanning functions and we here we can see a file is being scanned and then there is an explicit check to see if the file was detected to be malicious and if the detection name is mal New Krypton F and if that's the case then this is
simply ignored and this is specious so we tried we wanted to test this thing so we took 6 files that are being detected by Trend Micro as mal a new 5 and we scan the vasila vaccine and they were not detected so actually this is quite surprising because when we did some QA on the white listing you can see that it's mostly okay but in one instance they actually made a typo and wisely see the completely different thing so the white listing still works though because this this instance specifically is redundant which begs the question now what the hell is new crib so what is white listed here well according to Trend Micro's encyclopedia which is the
thing we can see that they describe mal new 5 as some kind of signature related to old malware which has no relation to North Korea but a deeper is actually if we look at the signature format itself we can see that the MAL prefects is used for generic detection names so it means that this signature is actually a generic detection name that can be a genetic detection that can detect more than it was only originally intended to so we can't really know what was the malware or if it was a malware that was white listed here but we can speculate on why the white listing was being done so the most obvious speculation is because there is some
kind of an existing North Korean tool installed on on the citizens computers and they don't want to alert the citizens to to that tool or maybe to take it as malicious it's also possible that they want the option to create such a tool so that it will be detected by this signature so essentially not detected at all it's also possible that since they're using a third-party engine that engine detects one of syllabic sins own components as a malware and so they wanted to avoid it and it's also possible it's false positive management we don't think so so moving on we'll talk a bit about the kernel size of Silla vaccine as you mentioned Silla vaccine uses three
drivers but essentially only two are actually utilized this ESPE filter and as we hook so let's focus on them and snooping around we can see quickly understanding something going on here the address of entry point is in the relaxed section in both of the drivers and it seems to be packed by something called Bob crypt which is again suspicious now what the hell is Bob Griese we never heard about Bob crypt and turns out if you look it up in the internet it actually exists and it's a very old Russian Packer it supposedly contains advanced protection features such as anti debug in polymorphic code this is not very good news when you're dealing with a kernel driver so we
thought wait a second before we dive in maybe we can find some kind of an answer by just looking again from the outside and turns out we found our answer and the answer is 42 seriously the answer is 42 seems like the whole protection feature here is that the text section which contains the code is solved by 42 hex single bytes or so now that we have managed to open the drivers we can look inside and we can see we don't start with as we filter so as the filter is the file system drivers we mentioned it's loaded and utilized by a sweedler which is the real-time component and has two main functionalities it's responsible for
real-time scanning on file access so it in two intercepts file acess to issue a scan and it also protects the any virus binaries but really it takes you quite some time to detect took us quite some time to realize that this is the only two things this driver does because the code of this driver is a mess and I'm going to save you some time and really explain you the flow by simplifying it so the process the the driver starts by wasting some time doing redundant checks then don't amount to anything it then goes on to check after a while it to check if the file that is being accessed it decides if the file is
being accessed is one of the AV components and if that's the case and the process that is accessing the file is not and the AV itself then the access is denied otherwise it goes on to waste a lot more time again doing some things that we don't really understand why it's being done doesn't look like office keishon just looks like garbage code and finally it moves on to scan the file with a sweedler so it intercepts the file access and issues scan command to a sweedler and if the file is find found to be malicious then access denied otherwise the access is allowed now the second driver is a speck oak it's loaded and utilized by SV Maine which is
the main wheel component and contrary to its name it doesn't actually hook anything instead it's used to query object metadata from the kernel really it is pretty odd and confusing again it has a lot of code 13 I of those but only a field only only a little of that code is actually used and it's very buggy so for instance I said that as we hook worked with s remain but it really seems like these two components were developed by two different developers so here we can see the developer face remain programming has remained to use one of SV hooks IO control functions and buffer size the input buffer size of the IO control operation is - albeit now you
would assume that the developers have agreed that that that should be the input buffer size right but unfortunately the second developer didn't get the memo and actually returns an error explicitly when the buffer size is 12 so this thing is broken it doesn't work now looking a bit deeper I think we we can explain why as we hook is so buggy and out of place because when you look inside you see a lot of this now what is this these are strings debug print referring to the function that is being debug is SAP underscore eight zero zero something so essentially an Ida auto-generated name now it seems like we were reverse engineering reverse engineered driver here
so essentially what happened somebody the developer of SV hook took some driver to compile it copied the code and edit debug prints in order to try to understand what he was copying and it seems he didn't really succeed in understanding and he also forgot to remove the debug print now we talked to be quite a bit about we talked quite a bit about silly boxing but to get the full story I think it's a good idea to talk about the development story behind it we don't have time we don't have time how much time do we have two minutes okay I let mark tell you more about it okay so I'll try to make it short to
understand who is behind silly vaccine we looked at the version info of the files and we've come across two companies one is called PGI which is this weird Korean name that's North Korean establishment which we really it's not particularly interesting it's a known establishment another company here is one called SDS tech service which is basically a ghost company there's no kind of information about this company on the internet or any active record of it but still we can say a few things about this company it's based in North Korea as far as we can tell we can tell it by this brochure you see right here on the screen which is basically an invitation to a technology international
technology exhibition that took place in Pyongyang in 2006 we contacted the organizers and they actually corroborated the fact that this company came on from the North Korean side but still the question remains is this government entity is this a private company or maybe that's the same thing also according to one of our sources this company is supposedly a subdivision of the KPA where KP is Korea People's Army and but that's only a speculation we can't prove it or disprove it and basically how much time do we have sorry for ten minutes five minutes good okay so and as we mentioned previously dren Mike things that this could be a result of a cold leak could this cold leak
be somehow related to this company STS tech service well we don't know that but what we did see throughout this whole research is a connection with connection between North Korea and Japan and we can we already saw some of the things connecting here so we saw as the kernel from Sealy vaccine and Trend Micro's engine which are similar but also we've seen a few applications here by those companies Silver Star in Magnolia which were both developed in cooperation with SDS tech service and as a matter of fact those two companies which reside in Japan they reside in the same address which is quite peculiar and so on and another thing we notice is that all of
these three companies developed an application with the KCC where KCC stands for Korea computers and are very well known a research establishment from North Korea and you may take this one step further and speculate what could be the reason for this connection but honestly all we are looking here is just a crazy web of connections we can't really say what's the nature of this connections or what do they represent so we'll just need to take it as it is but still there is there are some traces of malicious intent here I'll let Michael briefly tell you about this thank you so at this point we thought we were done with the research and we were very happy
but we thought wait a second we didn't find any malware any backdoor doesn't mean there is nothing here and then we realized we haven't actually looked at the package itself or actually at the installation file we simply installed silly vaccine and started analyzing it so let's keep this part so let's look at the package now and we can see that if we extract it it contains an installation file which we used but actually this is not a real installation file it's it's a self-extracting winner archive with no metadata which contains what seems to be the actual installation file according to the metadata and something masquerading as a patch file which okay but when you look at the
Demeter data it's supposedly related to Microsoft automatic updates which I think you would say is pretty suspicious right actually turns out this file is signed but when you look up the signature designer you quickly come to the report of by kaspersky of the dark hotel apt which used almost exact same certificate to sign the malware's there the malware miner is there and this is a pretty pretty red flag and when we analyze this thing we we understand what it does what it does it collects information and send it sends it to a remote server and turns out this is actually the stage one malware of the Jackal botnet campaign and further analysis confirms this is indeed the
chaco malware and what is Jaakko well it's an ongoing it was an ongoing but what would campaign uncovered in 2016 by fourth point it targeted mainly Korea and Japan and while it infected a lot of victims the later stages of the malware were used only against select group of individuals with North Korea in Pyongyang being the common theme between those individuals another interesting thing is the connection outlined by first point between Jaco and dark hotel which in our case the certificate that was used in both of the campaign's is another such connection so who was the target here well it seems to us that this whole thing was simply a spear phishing attempt at Martyn Williams who
gave us this sample it could be that Jaco is an integral part of every syllabic scene installation we don't think so and finally remember that we talked about the whitelist is malware so now you must be thinking wait a second we just found the malware and we found malware whitelisting so this is the same is this what was white listed so when you scan this malware with Scylla Watson it's actually not detected but and fortunately turns out it's not detected by any antivirus at all and the reason it's not detected is not because of whitelisting simply because there is no detection for it not in a silly vaccine not in Trend Micro and not in either
antivirus problems so yeah now really final word just minutes to talk about the conclusions and open questions we still have so I think the main conclusion of this whole thing is that silly vaccine has been illegally incorporating Trend Micro's components propriety components for years over multiple different versions they also tries very hard to hide this fact obviously we saw that there is a white listing for a very specific signature and we saw that the installation comes bundled with the JA Kumar where there are some things however that we are not sure about let Marc tell you about them right so what are those open questions we still have so first of all how did this silly vaccine authors gain any
access to Trend Micro's proprietary components that's something we cannot answer also the whitelist thing we saw we don't know what was whitelist what was this malware at all what was the purpose of it we can only speculate and we did show you our speculations also did this malware did the jacuz malware does it come bundled with all the silly vaccine packages or just this particular package it's also something we cannot answer because you know you would have to be North Korea to answer it so we prefer to leave these questions to the research community and although we cannot provide real concise and clear answers to this what we can see here throughout this whole research is a
particular scene a theme of theft or illegal and shady practices employed by North Korea so as to develop their own homebrew software a software that otherwise may be in a perfect world would be a totally legitimate product and with that in mind I would like to thank you for your time and hope you enjoy one note here though if you want to see our research log into research checkpoint comm you can read the full report right there thank you we have time for about one question if anyone has anything they really want to ask just raise your hand and I'll bring the mic over yes one second hi I was wondering um you said that this
particular software was used to monitor like external media files I was just kind of wondering as far as the detection files the signatures that you guys saw you saw that they were I think that you said there were ninety percent similarity some similarities do you see that there were like additional signatures made for those media files that were smuggled into North Korea no I mean yeah actually they didn't it's funny we we are pretty sure they didn't modify they don't even understand how the signature files are built it's a very propriety format and that's the reason that the white listing was done at the code level and they didn't actually remove the signature it was it
would be easier simply removing the signature but they did it at the code level because they don't really know how to add or remove signatures no they don't try to delete smuggle files they it's a it's just that the smuggle file thing was just to get you to give you an idea of why such a product would exist thank you to mark and Michael thank you [Applause]





