Kenneth Peeples - Zero Trust Architecture in Service Mesh
Show transcript [en]
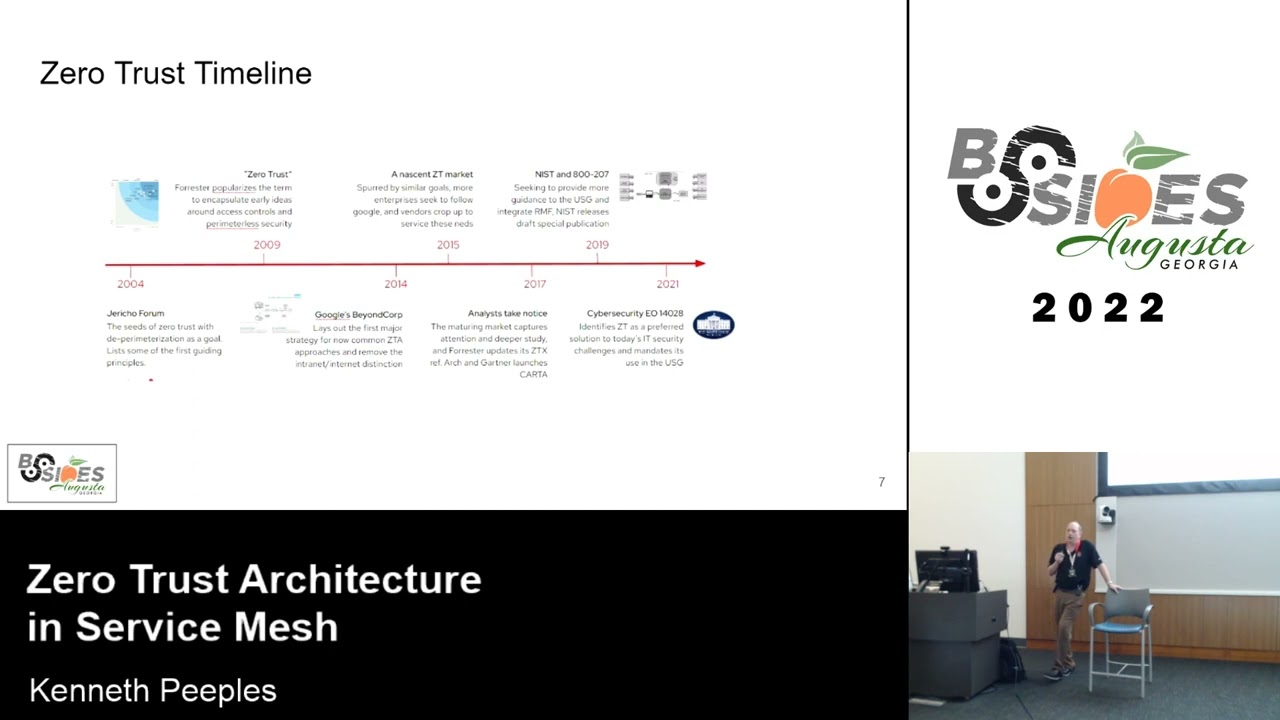
is a red hat principle architect thank you [Applause] all right we'll go ahead and make sure this works go ahead and get started if I can get this going right there we go uh so I'm going to give you a short link where you can download the PDF you can see everything on the slides and and one of the reasons I want to share that short link there will be some graphics that come up and I'm going to ask a question at the end of what is zero trust and you can rent when a hacking kubernetes threat analysis book so if you're familiar with container platforms familiar with kubernetes this is a hacking kubernetes book and so when I get to that link you can pull it up on your phone or laptop and when I ask the question you should have the answer and I the other prizes are the network switch right Wi-Fi adapter and lock pick so this was the abstract that was put up and so I wanted to make sure it was in the PDF because there's a couple of read ahead links and I'll be walking around some just for a minute and then I'll have to sit I had knee surgery so um I don't have meds now because it's been about four weeks so I may be walking around and sitting so excuse me if if I'm around too much but the agenda today I'll talk about the topics we'll go into zero trust service mesh I'm going to talk about red hat openshift and service mesh but keep in mind the service mesh and based on istio and kubernetes those are vendor agnostic so everything that I go over you should be able to install on your own and try service mesh and try some of the references that I'll give you for the workshop and I'll show you how to do that so hopefully you're able to use that Public Presentation link I have there and pull it up and uh when you see me get to the disa reference architecture diagram that's the one that you want to pay close attention to when I ask the question for the book giveaway so um I'll have to get used to to looking down there instead of looking up at the screen or my laptop so I am a principal architect for Red Hat I've been with them I actually left and went back total of 10 years and I focus on Department of Defense projects but security related initiatives I spend a couple of days a week doing internal Red Hat initiatives and billable to the Department of Defense and I went to University of South Carolina and University of Phoenix for bachelor's and Master's in computer science and working on my Doctorate of engineering now at Colorado State University so the online programs that a lot of the universities are getting a lot better and helpful for those that are still work and one of the things that I would like to say if anybody in here is still in the service or planning on going into the service I wanted to thank you for uh your service and any of the dod agencies I spend uh have spent a good bit of time on different DOD agencies but Army and at Fort Gordon I've spent a good bit of time lately so what we're going to cover today uh the first topic will be zero trust and we could spend a lot of time on each of these topics but we will hit some Concepts on zero trust then we'll hit some Concepts on service mesh and some examples of service mesh and then we will talk about specific implementation example around Red Hat open shift and red hat service mesh so what is zero trust uh there are a couple of things I want to uh note on what is zero trust and that is it is a security framework when you talk to folks who say they have a solution for zero trust or a product the solution you can get toward the zero trust framework but getting a specific product that covers everything in the framework that is more difficult and we'll go through some of that but the main Concepts around zero trust are getting away from Castle and moat and making the perimeter more important than assuming there's a breach or a possible issue internally so when we go through some of the other references we always want to make sure from end to end that there's encryption that you have multi-factor authentication that you're looking at least privilege and that's all the way through Network and up the stack now we can't look at Perimeter and say that um we have a firewall or we have disconnected Ops we have to assume that there is a breach inside the network at all times and we also need to be able to analyze within anything going on on the network so now we want to make sure that with no traditional Network Edge and we're going into more iot there are more Edge devices that we're looking at dads which is the data assets applications and services so a couple of things on the timeline for zero zero trust is not new uh people have been talking about uh the parameters perimeterization removing castle and moat concentrating on encryption and identity for a long time and you'll notice this timeline talks about in 2004 when there was a Jericho forum that talked about the parameterization and then went on to Forester which is an industry analyst talking more about their thoughts on um zero trust and then going into Gartner with their Carta and Google with a Beyond core and Foresters was ztx so you have all these different concepts previously from different industry analysts and organizations but why is it important today if we go over to 2019 into 2021 2022 there's the nist special publication that defines core components of zero trust deployment models and then the executive order from President Biden came out that there are certain things that you you have to do certain actions that the agencies have to adhere to and I think in that executive order it mentions zero trust like 14 times something of that nature but the key is the modernization and moving to the cloud and then the 2022 memorandum from OMB is not on this timeline that was uh earlier this year but it talks about specific actions that are required within the different pillars by the end of 2024 so what this talk focuses on a service mesh and some zero trust aspects but there are specific mandates for DOD agencies and across the government to complete certain tasks within certain time frames so I'm not going to read all these but I did want to include it in the PDF so you can reference them it's the executive order that I mentioned from President Biden I put the OMB memorandum in there because in the appendix it lists all the uh actions that are required with the different pillars and specific time frames and you can find different documentation from nist NSA sysa so forth and get more of an understanding of the different aspects from what you need to to build in your Enterprise for zero trust I went ahead and put some links to some of the global agencies because it's not just the US that has said oh now I need to make sure everything internally is just a secure coming into my network now I have to make sure I am assuming that there is a breach internally that I always uh verify and I never trust so now it's more about granularity and making sure that you're validating on every transaction especially in microservices which is what we're talking about with service mesh so some of the core components and principles that are in the niss special publication and this diagrams so you'll see this throughout the talk and the different diagrams where we have the control plane that manages configuration and for the proxies and then you'll notice the policy enforcement points which are the proxies for the the microservices that we're going to talk about but the important thing to to note on this diagram is I'm splitting Network traffic on the uh to the policy enforcement point that is what is going to enable access to the Enterprise resources so as this says the important thing is the all the data sources and all communication is secured on the network and everything is considered a um a resource and then when we look at the core components we also we have the enforcement Point you're going to see in service mesh you're going to see the decision point and those should be thought about in everything not just service mesh where am I enforcing policies and where am I building the policies and making them available to make a decision for the enforcement point so if you'll notice this this is what I was mentioning a minute ago that this is zero trust reference architecture so if if you can take a note of this diagram that's what we're going to talk about on the book giveaway in a minute but you'll notice that there are seven main pillars five of which are the user device Network application and data but you'll notice over on the right hand side there are different color for Automation and visibility some of these go across a couple of pillars and some go across all and the key here is looking at this diagram it is a security model right and it is holistic security it's not I take authentication for a user and I'm done it is a maturity model that you have to think about for customers to go from a basic to Advanced or basic to an optimal maturity a model on capabilities that are deployed so one of the things that I like with this graphic at home with the systems the multi-factor authentication while my son asked me something said well we need to do the multi-factor go ask your mom too and my wife just looks at me like I'm a nerd so I like that picture a lot so as I talked about there's a zero trust maturity model that sisa put out and this helps identify the traditional down to the optimal so not just service mesh that we're going to be talking about here in a minute but the different pillars and what you should look for in traditional Advanced optimal I I look at this like devsecops and your pipelines that you're building you're never going to be finished if somebody says I'm done I put a product in for zero trust it's not accurate because it's a complex solution with many capabilities that have to be installed and one of the things that you note here would transition to zero trust is identifying the actors the assets looking at policies and you'll notice identify candidate Solutions so what technology isn't products should I be using so that I can get to deployment and monitoring which is the very last thing and this is just another view another input on a maturity model that's in the just a reference architecture the other one was oops this one's sisa this one has traditional Advanced optimal this one in the disa reference architecture has Baseline intermediate Advanced but you'll notice they're similar and what they're looking for but what I like in this one is the discussion on Discovery and assessment so if I were to go into a project for DOD I would want to ask these questions and ask you know how can I apply all those Concepts on the project and look at a higher level program what is the program doing for zero trust and with this these are red hat products when you look at open shift you look at Advanced cluster security IDM staff and so forth I like to be vendor agnostic even though I work for Red Hat I like to talk about open source Technologies so the key is not a red hat product although I know everyone in here loves red hat and wants Red Hat products the key is looking at the capabilities and how am I fulfilling that need or requirement so I don't want to go too deep into this but there are the old layer three rules that a lot of folks use and some of the firewall companies are putting out next generation and this is an example of a Kipling method that Palo Alto uses and you'll notice it goes not just Source destination Port protocol but it goes from who what when so forth across and the middle one is around the Enterprise guide which is a book but it goes into the subject the target the action the condition and then on the right it goes into the zachmore standard which is fine grained authorization so the key here that I wanted to show is that um we want the fine-grained authorization we want to know more uh than just a couple of specifics about who's accessing a resource we want to get down into the granularity all right so we're going to go ahead and give away the book so please just trace your hand who can give me the capabilities how many and the exact ones that are in the data pillar up somebody has their end up back there okay so look at this closely this is not the pillars but the capabilities in the data pillar there's so who sees something else so does anyone see that some go across pillars go ahead correct I hate to ask you but I can't walk that out there so everybody had good answers but machine learning is part of the data as well and that's where I was trying to go that's why I put spans two or less pillars to give a hint there that there's actually the machine learning that's included as well so good but I'm glad everybody was able to pull that up so let's start going into service mesh so um this concept or service mesh and within openshift the off service mesh operator is based on istio and that's one of the more popular um service meshes and we'll see additional examples the VMware AWS so forth not just red hat but just as we talked about with the nist special publication there's a control plane there's a data plane East-West traffic right and we have a sidecar that protects each micro service so why do we want to do that we want to control Network traffic and control the health we want to separate that from within the any additional logic within the microservice we also want to be able to observe and Trace so that's a lot of the benefits of the service mesh so these two examples the one on the left is AWS and you'll notice that they have the concept of envoy as well there are multiple components that work within a service mesh for that Network control and the segmentation away from the microservice itself and then the right is tanzu so all these are around the kubernetes container platform okay so when we look at the service mesh data plane we're looking at as I mentioned the sidecar controlling the the networking and isolating those to the sidecar instead of being controlled by some other method and so what does that give us one of the things that the OMB memorandum indicated has to be done before physical year 2024 as end-to-end encryption so mtls multi-factor Authentication what the service mesh helps with is some of that security with mtls and service to service with certificates so I know what service say and service B are and that they are authorized and can authenticate between Services also the observability circuit breaking load balance Etc so the data plane focuses on the network portion then when we look at the control plane as I mentioned this doesn't look at the data packets but this does make sure that policies and configurations are updated in the proxies as needed on the data plane all right so as I mentioned istio is one of the popular service meshes and we have our service A and B with our sidecar or our proxy and we have the control plane with istio and it has some components that control Discovery certificate management and so forth so that has been accepted even though it started a while back I can't remember the exact year but it was a started a while back and the cloud native Foundation recently in the cloud native Foundation even though it's been around a little bit uh what I wanted to show on the right hand side and we won't dive deeply into this because a lot of folks are still focused on sidecar or proxy but when you look on the right hand side there's something called ambient mesh an ambient mesh just came out recently and istio there was at least one guy that used to work at red hat that went to solo.io and within that ambient mesh they are trying to give the ability instead of using a sidecar to have a z tunnel so it's a mixture of being able to use layer seven and and layer four within this model and so I have the links there that you can look at in the future so as we talked about with service mesh I have advantages and disadvantages I feel like there should be music or something because it's so quiet in here um so with some of the advantages and disadvantages we talked about the security observability that's a big one the um reliability is another and product productivity and efficiency and I don't know if everybody remembers the pizza as a service diagram that went all over LinkedIn and so forth but now with service mesh Cloud native or service serviceless on that far right hand diagram you'll see service mesh in there and I need to change that pizza as a service to show that um and I don't remember who originally did that but a disadvantage is some of the possible delayed communication now we have the proxies in front of the microservices that are intercepting and deciding what should go to the microservices so depending on Hardware depending on configuration that can be a delayed communication so again this is the this is a different link but it's ambient security and what they're trying to do they're not trying to completely get rid of sidecars but they're trying to build this ambient service mesh in istio so we have the pp with layer 7 and the security secure overlay and to me when I look at this the biggest thing or two big things in here one is the separation of the application from the data plane which we talked about the proxy and application being in a data plane but also avoiding the multi-tenancy that may happen with your proxies so it's a good read to see what's going on in the future and I don't know when that will get into the service mesh operator for openshift or the other vendors so just to I like this image too with our service person protecting us the zero trust model but the three things to note here as I was talking about a minute ago was the certificate management between services and the mtls so those three really apply to authentication authorization of services communication between them and the mutual TLS so that's the two-way encryption so I threw this out here just to uh everyone I assume knows IBM bought red hat and red hat is still continuing its open source and open shift is one of their big products that we work on different Cloud providers and different verticals but what I wanted to note here when we get into openshift and service mesh the service mesh we're talking about istio traffic control kiali which is some of the traffic visualization and Jaeger which is that tracing and I'm going to show that just briefly and give you links that you can try this in your own environment but some of the use cases are listed here that you can go back and look at but the Z zero trust aspects you can see that in the different use cases for service mesh and I know this is going to hopefully this won't confuse everybody give me just a second so when we go back to uh technology focus and how we can do segmentation and other things you can see that service mesh can fall into this capab different capabilities but it wouldn't solve everything that you need to solve for service mesh I mean zero trust all right so where was I so you'll notice looking at this diagram and looking at um how we've overlaid the ZTA core components that are in the reference architecture from disa I'm sorry from nist the nist special publication as core components this has our data plane with the proxy and we have our control plane that has istio and it has the different components of istio for Discovery configuration and certificate management and of course we consider the proxy as the enforcement point we consider the control plane and istio Demon as the decision point and you can refer back to uh some of what I was talking about with the right hand side there for some of the bullet points so I wanted to throw this in as well and talk about API gateways so I make the assumption that if you've worked in microservices you've started working in API gateways as well so North South traffic coming in through an API Gateway Red Hat has three scale which is one of their products and whe





