Practical Out-of-Band Data Exfiltration in 802.11
Show transcript [en]
okay so hi everyone I'm well that's Luis Gomes we're here to talk about practical out-of-band data exfiltration in 802 11 that's Wi-Fi for ever for anyone who may not have heard of it before I pretty much have some bio things here mine's a little bit more serious Louise she's a little bit better so I work at check marks I work at cobalt as well I'd co-developed airborne ng which is a man on the side attack tool on wireless as well I built a couple of tools well actually it was more like a module or two for Metasploit too so I was a DEFCON 25 workshop instructor I did a workshop about scape II which is also the
framework we built this tool on so things should get interesting and Louise would you like to introduce yourself or just show you the money I don't know so for me I'm currently head of security for OLX and the gospel group I also work at cobalt I started in the banking industry or payments industry with SIDS and then move forward to I do a couple of things in my life but ultimately currently I'm just doing bug bounties shout out to support and also taking care of the security no Alexis oh okay so let's get down to business first of all let's do just a little bit of an intro 802 or 11 has several frame frame types there's this is the pretty
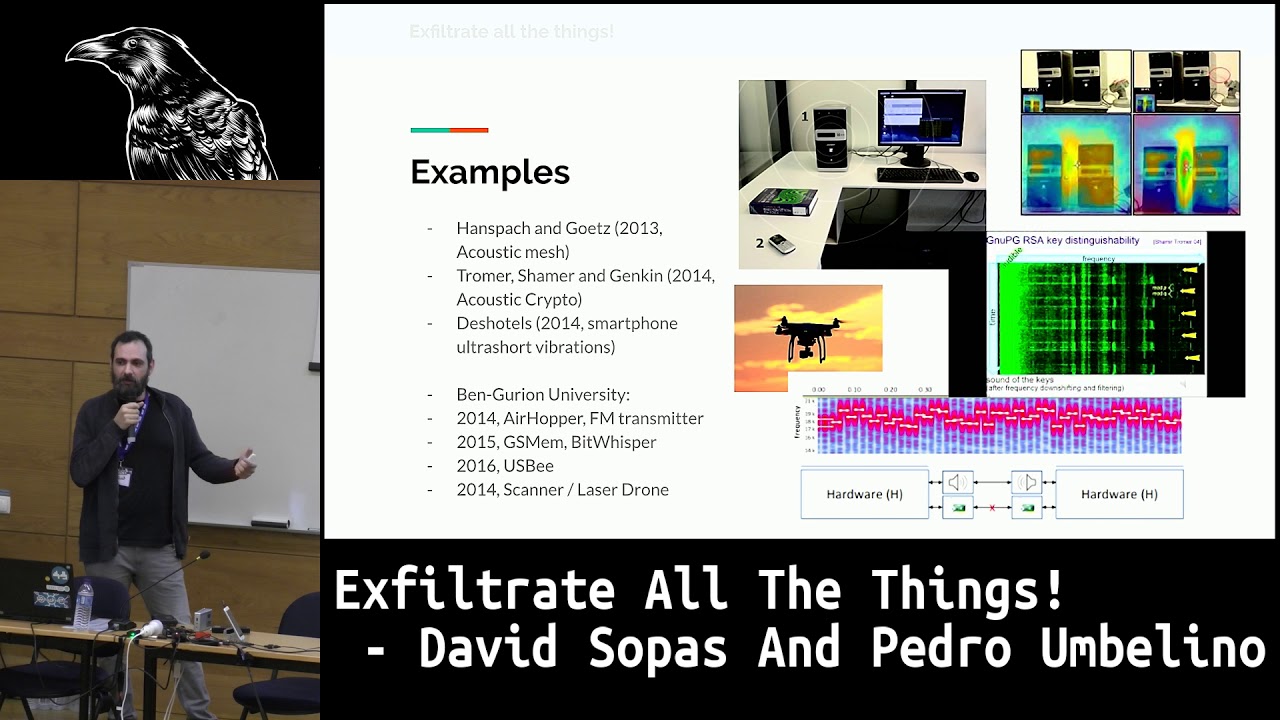
much what the format is when you have the the type and subtype actually dictate what the type of frame it is if you have control frames data frames and there's management frames as well what what prior art in data exfiltration was through out-of-band channels in 802 11 has done is actually good grab one of these many fields and try to manipulate them and insert data there where they will not be used or would not be checked or something like that so this is pretty much what we want to do this is your typical 802 11 Network you have a Wi-Fi router you have the internet on the other end and then you have the devices you have internally what we want
to do is something like this so you drop an implant there's a physical cable usually it's a cable connection on from the implant to the router and then there's an attacker device that gets some kind of signal or response or whatever communications through an channel that's parallel to the the actual server you're trying to use what are the benefits of this there's many you don't go through their IDs or IPs or whatever you don't send packets through their network you can even get to a point where the wireless implant does not have an IP on the network and and yet you can still port scan or do whatever you want and still get communications outside without anyone on
the inside having any idea what's happening so this is pretty much what we want to do and now what's the the problems we might face or the point the real point of this is to get communication and data across without being detected so even though the prior art has done this semi successfully the very first idea or the very first thought of how to implement something like this would probably be the level 0 attack which is the easy way just drop a rogue ap right so you just drop something there and connect it with a wired or Wireless to the on scope ap let's call it that or the target ap and then it just spins up another AP and you
can just connect to that through your attacker device and why what else would you need right well there's a problem with this approach well while it's out-of-band because it's not really on the attack network the beacons beacon frames sent by this ap which is in this case the Wi-Fi pineapple will pretty much give you away because the if somebody's doing defense on the wireless side they will immediately detect that a new ap has popped up and is sending beacon probes and sending you all these packets to your so that it shows up in your device list when you try to connect so pretty much this is something that was the state of the art or trying to be the
state of the first way to do it but then you start to get into the more technical things on how to hide data inside the actual frames and now I'm going to pass it on to the wish to keep going on the other parts yep so what we have right now is uh well we have some stuff right now that is similar to what we are about to show still it's not that easy for a blue team to detect but if the pans if the team is one skilled enough to if they have enough tools to detected but above all just the the critical point is is anybody looking at what you are trying to send out number the I think
the famous one will be spider Labs got one called smuggler and there is a patents already sore something similar about sonography we have exfiltration patents on devices similar to what we are about to show and there is also the one on the on the left on on your left alright that is pretty much a library that assumes that creates EDP channels and it's similar to ours and we're gonna show on the next slides that everything is these are nice implementations still flawed by design because if you will create an agnostic layer but in what we are looking for and you don't look for signatures or attacks that are specific using encoding or whatever your going to
think of at the end we're going to understand that right now the the critical part is most of them use either a something that you can detect just by looking at the Wireshark or cm or any other monitoring tool that you have or B if you have some kind of AI just looking for patterns is gonna spike right through it like you're gonna see all the communications and don't work because at some point the blue team is going to understand that something is off because either a there is a like he said in a rogue ap or one ap that it has the same name as any other is sending too much data encode the data on strange
fields or it's doing everything right but that always the same destination always the same fields never random feels always static so that is one of the ways that you see that don't work well you have one of the levels that is surely yeah you wanna show okay so this is one of the the means that has been have been used before to send data out events so as I was saying before the problem with the rogue ap is that it's constantly sending beacon frames with the SSID name so here I am I am Microsoft guests Wireless so that it will keep sending those like 10 every second or something like that so to make sure that it shows up in your device
list Wi-Fi access point list what some people find out namely the guys from spy their lives is that you can actually send just one of them and instead of sending in an SSID you just send data there like basically for encoded which is what they did so they actually implemented it I think we can probably show a demo of this okay so I'm just right
okay everyone's read the screen cause we're gonna yeah let's hope that's how it's possible to read yeah okay so this will be the the server so you would have to set up the receiver then you said the interface name and then so on one at one end you have the server and on the end there and you have the attacker so what you have is this is the implant and that's the other device the attacker is going to use to exfiltrate data to in this case we'll see very first why this is a problem so it will try to pretty much what it'll give me as a shell let me just try to pull this up for you okay
so pretty much what they give us is a shell if you do LS in theory it would be getting the let me just check for one second yeah right because for this to work every both cards have to be at the same channel so since that one was channel helping the problem will gonna work okay so as you can see it got actually a bad command but it's fine because this is kind of okay so now it works you see LS they cannot access something so this is actually just the proof-of-concept code I just literally get cloned it and try to use it so this is the experience you have you LS what it does is it runs your command grabs
the output wait first waits for five seconds then sends the response back as you can see it was just there right so this is the what they had right so it doesn't really have a problem here so let's try another command let me just exit so I can pull the screen up so let's try a command that has actually a little bit more of an output instead of just three lines or four yeah that's not gonna work it's just gonna say yeah no exception so yeah you bite format requires zero or something just to fifty fifty-five okay so this is what happens when you try to just use a tool that's already been worked on this is supposed to be the
state of the art of open source event data exfiltration in wireless yeah so wide well this is what if you grab the peak app if you are looking at at the traffic right now I don't know if some of you do blue team or not but even if you don't do blue team like if you look at at the SSID on this part of your window tell me that if this is normal like if you're just looking at normal patterns and that is what we are talking about this over here or on in here depends on where you want to look at if you don't get spiked by this then something is wrong like you need to
understand that if this is your state of the art of exfiltration then you need to step your game up this is not going to work in any organization with proper we're talking about back in the end of the slides we're gonna have military-grade acceleration like we're talking about when you want to do something right not get caught with it so normally what we are thinking is and this is for people that know me this makes sense so this is you want to get like the maximum amount of data that you can like if you want just show that ISM it can't like bring bring a big information outside because it's limited to to do the sides that you can exit
rate but the thing is we want to get all the things that we have there doesn't matter if you want to just have a foothold on the organization it just use as a shell or wear whatever you want but the number one reason why these tools don't work is that they don't know how to disguise sounds like you need to understand that if you want to get by any AI in the future or if you want to get by by any detection measure it needs to be expected to be detected but at least act act like a octopus just understand what is the texture the feel the looks and be like that all the time and do not spike
any type of thresholds on patterns because at the end of the day and we're going to show a little bit of an improvement from the state of the art that they have in until we show you the big boy is you can really just disguise like you can take from the from that specific spike that you see in the in the SSID the exfiltration and use other fields like he showed you the fields before just to give an idea where you can try to put your payloads to exfiltrate that or just to interact with the shell but at some point if if somebody like we are presenting now in the future if we present in more places
then the tool becomes famous people are going to start looking at the solution and they're going to create rules right so what we going to present in the end and this is just an improvement from from the example before is a way that either if they improve doesn't matter how how they improve it ten or call Watson or whatever they can call it to try to attract our tool we're gonna be step ahead and just blend in more and blend in more to the part where you can be exfoliating that and not get caught or if you want to get caught just in the end of the talk we I don't have nothing programmed to dinner and you for some
numbers we can already see some kind of detection but until then it's undetectable or if somebody got an ID in the end please feel free to break our two here okay so let's get a little bit into the specifics so as I told you before the other ones use the additional alt layers on the gyro 211 frames or replacing the SSID field with acne the data you wanna exfiltrate or whatever so let's try something different just a different approach let's use 802 11 data frames they were actually designed to hold the data so if you're doing like a get request that's where the get requests will actually be and they're usually encrypted because we usually Wi-Fi networks have encryption
so that's you're just gonna be looking at random data so that doesn't matter because for us what we really want to do is not stand out so how do we use a data frame and not stand out that somebody's sending something outside of our network well let's just take a look a little bit of a look into what the structure is of this packet so it's just this is just a QoS data so it has like the data over here this specific packet has a just 155 and 45 bytes of length it has some CCMP parameters because that's the encryption that was used on the Wi-Fi network some addresses just to know who is sending
who is receiving and then there's not a lot of little else so it's kind of simple let's see what this will look like for the attackers so they would just drop the implant connect it to the target and then send the data frames up to the other device how is this different from what we just showed you before well this is what the defender sees the the actual implant what it does is it scans the neighborhood neighboring a piece picks one that set the appropriate signal strength and then tries to emulate that that that ap is sending a message to another station that's even further away that you can see so you can just for the the defender
it they can just assume that they can only see half of the conversation because they're closer to the AP the station is even further away so they can only see half of it and that's like the server talking and when the client talks it's the other AP so the client will do the exact same procedure they will look at the airspace they will try to find a ap to spoof and then just start sending packets but there's a little bit of magic here like for example how does Wi-Fi station to know how to talk to Wi-Fi station one are you using hard-coded MAC addresses no because then you can track me so how are you figuring this out well
there's some magic called totp which is the technology behind your Google Authenticator codes that roll every 30 seconds so basically what's happening is this wireless implant is just sitting there quietly iterating its TOTP algorithm every 30 seconds and in the correct time slot when the attackers device tries to connect it will see if the MAC address which is deterministically generated via the totp secret matches with what it's expecting it will send the it will accept a packet and send the response with another just it will hop channels so this is set for a default channel of 6 if it's in channel 6 it will be ready to receive a new connection at the point that it
receives a new connection it will just send a handshake packet that will say ok this is the the MAC address I'm going to use because I already saw this station this station 2 which is an actual station talking to a p2 neighbor a p2 so let's just try to spoof that and now I'm the question is and this is why we was asking how do you detect this the question is how do you know when you're trying to protect your company which is target IP that a p1 from the neighbor is talking to Wi-Fi station 1 how do you know if that's a legit station or not is that in scope even yeah should you
should you try to even track the neighbors av I think the the asymmetry of the attack and the defense on this kind of wireless exfiltration with via out-of-band channels is it's kind of makes it really hard for the blue team to actually track this because this is just one of the ways that you can do it you can do it a million different ways and if you try to make the algorithm secret and that's the key the secret sauce years to your solution then once somebody buys it or picks it up then you're done if you actually have something that if you people know how it works and you still can't detect it then you got something and I think that
this is a very nice solution it will not work in every scenario because if you have a Faraday cage and a very secret underground vault then you will not have a neighboring AP so this will not work right but there are many ease offices in high-rise buildings or just a regular office building that has a lot of neighbors and a lot of a piece and then in the neighboring airspace so this will probably work in 99% of the situations which we want to talk a little bit more about the detection yeah so most of the times my the exercise that means you were having for almost a year now is either I think I develop a way to detect
it and it tries to break it like evade it but we do that exercise probably once per week so my question is for everybody that is this is a lot of information for a slide first I know for a toe the thing is this is all the variables that I got to think about when I'm trying to detect these type of attacks these are from to our expected the time is the like is this to AP's talking at a time there is no one in the office or or is supposed to have they are supposed to be talking at that time this is so many information but this is all the vectors that I got a
look and then from all this type of questions that I can ask myself to create a detection for the type of attacks that you see right now then we have different sources of data sources like can be from the type of a situation is trying to do is coming from the implant but when you're trying to construct the rules what you see is the thing over here so logical conditions to over something that I don't know if I'm looking I'm not even looking at or trying to create a logical condition that will tell me that the network events that are happening will result in an alert is very hard because everything is doing is expected so I there is no
type of a difference that I can look at a healthy communication between two APs and say well this is some yet we can detect because this has never happened before or I never seen this before or this can happens from time to time I don't know when but I should review the event every single time that it happens it doesn't happen like that the last version that we have from the 2a only adds when there is people acting only sends package that are expected if you look at RFC from from the protocol in look at our package and then on the end feel free D is gonna have my cell phone there and you're gonna see our
last version you can you go to the to the table and this is our military-grade this is an example of of a cell phone that it has right now on your hand you can go imagine drop the implant you don't you can go there and check it you drop the implant and you go pass by the office on the on the street you just you can interact with the shell and and either if exfiltrated or Rick on the network from the outside like in Starbucks just on the front of the building and interact with it the problem is nobody is going to detect you anyway because everything that is going out is expected so because they don't
even know that is the package that are going out are being used to accelerate that at all so my main slide about is the point of having these slide is blue teams right now the increase of complexity is pretty hard to deal with because we have more and more data to look at it even when you use ai ai is looking for patterns and the guy that is supposed to be the the brain of the operation is looking for stuff that that AI can't really recognize and even the guy that is looking at events that is supposed to to to be detected you can't see anything if you see the eye we can show you the peak up there this is too
much in terms of of information on a peak app for you for for me to show you but if you show the peak apps and you can feel free to download the code and try to use it and detect it you can't really see on the peak apps anything that I showed you before that is spiking when you go for every field every single field and you you can see a difference from my from your package and Jonas package it's equal the difference is econ the data that is available for your company and I don't I'm just telling hey connect to me hey do you want it do you want to connect to me so now he's going
to show you our ultimate military-grade and scratches or anything if you're here you know I'm here so after the talk please feel free I beg you just go there and test for yourself the execution and try a large command stuff that you see that father on the others and if you feel that is a weak implementation use the we're going to share the code use it and try to break it that's that's our money and this will be public on a github link that we will share with you guys so a pull request is always welcome if you feel like there's something wrong with it just one thing I forgot and this is a this is a this is gonna be the the
name of the tool so stupidly I forgot to because we are not that good in market marketing if you noticed I mean is not I'm trying too hard as you can see but but anything else just talk to us on the on the end because most of the talk is pretty like it's like you actually seen it terminal-based and we invite you to test it because it's we feel that everybody is like the best for your talent talking a lot and just having too much slides and information and you never actually work with it so you don't you don't know that's analysis so you need to you need to at least one time show people that actually works so
yeah that is why we have is there okay so on that note I'd like to jump into the actual detection code of this this exfiltration that we were using before so not actually the data ones but the beacon ones so I actually have in one of these machines I have a peak app that's sure this is still sniffing yeah okay so yeah as you can probably see there's a peak app here called level zero pickup and then I'm just gonna show you detect level 0.5 which is pretty much 13 lines of code in scape II codes to detect this kind of acceleration so this is the output of the script of the script okay so it actually found the
server responding to another LS la or LH or whatever and then the client sent you name a and then you found the Linux version of what what the implant was so this was just as simple as that it's 13 lines of code to detect we built something that was similar to this but with the assumptions that we had for our model so our model was if you find one way one directional communications between an AP and a station and you don't find the the other way then you will add this to our candidates problematic ap MAC address list if you do find it then you will remove the the MAC address from the list we I ran that
on a 1.5 million packets capture file and pretty much got 50 false positives because I did not exit rate anything I just ran the tool it should catch nothing and then I got 50 cases of exactly that scenario I was talking you to you about so there was an AP there was a station that was too far away and your detector didn't actually get to the point that it saw the connection back from that station to the neighboring ap so again you're welcome to start trying to use the tool I'll just demo it very simply over here yes [Music]
[Music]
okay so at this point this is running the server it will tell you what driver you're running because if you've ever done anything with wireless you will know that drivers suck so you have to actually code around whatever they decided was right for their implementation so what it's doing right now it's actually channel hopping and scanning a little bit of the airwaves and trying to see what is around it so it will find something that it will want to spoof later after it goes over the all of the the channels the client will do the same the problem is this is supposed to be dropped a long time before the client actually goes in exfiltrated data so we have to wait a
little bit for it to actually set up everything it needs and after it does this I can just connect to it
okay seems like it's ready so now we try it on the on the client and it does pretty much the same thing and tries to find something and then it crashes okay cool so first first mission accomplished demo fail I actually know this bug I just didn't commit figs which is awesome don't look at my code my code sucks please don't look at it don't even look at it yeah it's that bad so please PR you will get a link to PR you can't complain if you won't be out okay yeah okay okay so here we go again temp number two [Music]
so if you have any questions about this this is your time yep because I suck at coding I mean I'm not a coder I'm not a developer I just break stuff so yeah yeah that's it it's like we expect ya to be expected you should I don't know why you expect me to be like a high quality coder but okay in the future go Ling yeah perhaps if you write it I mean the point is I just thought this up and thought yeah maybe you can track it no matter how crappy the code is and trust me this is the good version of the code I will send you a link to make your eyes bleed if you
want yeah it's just words so yeah yeah if you work with any words no see over here for act oh yeah well you're welcome to write a see implementation because it would could use some speed a speed upgrade so yeah yeah okay so that's the connection established so now we have a bit of a more flexible connection to our Excel tration server we have no more problems with length we have an AK that can actually tell the server that the client sets the server got the request until the the client shall let's the server know that it got the response this is all within the 802 11 framework so yeah you will see the the AP again if
you go back to the slide where you see the two neighboring AP is talking to the stations that will be the the station you will assume that you will see acts to the APS right so you will see the AP is talking to the stations and then you will see acts coming to the APS but you don't know which ones no I'm sorry talk to going to the stations you'll see acts going to the stations because that's the MAC address the unique MAC address that will that's derived from the totp so that's how they know that they're talking to each other let's try the D message command again so now as you can see this won't fit in a packet so it
will just be boom boom boom boom boom sending in everything you didn't get the XO album resending like trying whatever you can still try to track it and you still won't be able to so if you got any ideas on how to fix this or how to track this we're welcome to hear your thoughts yes it's slow but it works yeah it's Python so but we do have over one kilobyte of stupid so not that limited
excuse me are we on questions right now yeah yeah sure after that you can go to over there and play with it hello yeah is this encrypted yes of course you are you're masquerading as WPA traffic you just have to encrypt how do you detect whether it's W you have you are you sitting the WPA oh yeah sure definitely I mean that's the we are looking for a PS which are using encryption so that we can actually send random noise and not be suspicious right and do you simulate the WPA handshake for a connecting stations no because you don't know that you you may not know or may not have seen the WPA handshake but
we can totally do that if you want to but we won't be able to properly do it because if you're on the out of scope AP then you will have to spoof it somehow because you don't know the key let's assume that you don't know the key of the AP you're going to spoof so the handshake will never work right you know maybe there you spoof it somehow well if I see two two stations talking to each other and they're not talking to each other that's the point you just see to a piece that our neighboring ApS that are talking to two stations but you don't see the traffic back from those stations right and this model has been confirmed
because as I told you I ran just to capture for like six or seven hours in my house and it's like just ground level and there's a lot of stuff on the street and offices and all that and I did see 48 or 50 devices that were in this exact scenario so you could see the AP talking to them but you couldn't see the conversation back so that's the model I was trying to replicate in the packets are all the same size how can they be if you do LS then it's just LS if you do bolero whatever a big command then it will be a big packet right so at least at best it will have like the size of
the block cipher right so that's the the only thing that you can probably use to track it yeah it matches the multiple of whatever the block size is so perhaps that's a way but I would like to see your false positive rates on the other kinds of right so yeah anyone else okay isn't it possible to detect by the sunna signature I was hoping for that question yes it is however after talking about this to the creator and firmware writer for the Wi-Fi pineapple he told me that there's actually a trick that you can do which is to modulate the power level at which you send the packets so that the receiving end will see a fluctuating our
SSI so now what right that's my favorite me told me likes for the other side if you have like if you have IPS in the corner of the area you can see if something is inside that's assuming that it will spoof always the same AP which it won't because every time you disconnect it will scan again and say oh now I want to spook the other one so how can you actually be sure that by detecting neighbor a SS IDs that are not the ones that should be inside that perimeter for example have Microsoft Network and you have ApS in the corners and if something from without being Microsoft is transmitting inside the area but how do you know that how you
distinguish the not being microsoft's transmitting inside the area because if you are fluctuating the power level then you're getting the RSSI for something that's inside no it's not because if I'm sending you at a lower power level then the power that won't get partners get yeah right yeah the corners yeah a good point yeah actually I didn't think of that so good one yeah that's a nice well I did think of that the problem is most of the times the we we have some scenarios where these don't work like one of them was being you don't need any of this if you wanna you can have the implant and imagine in a crazy scenario silo somewhere in the
desert and you only have one specific IP speak speaking to one one station then is no noise it's impossible for us to yeah that's the part of the cage yeah we can limitation speaking on your example if we are tracking the area on the specific area I just don't have a way to to emulate anything because they are they have a concrete whitelist that's why I had the illogical conditions of what I am expecting to see the same there are some scenarios where we can create like applicable solutions for but like in the future that is one of the improvements we want to have is like having this type of scenario so we can even immolate it
or or provide some kind of something they have to work on and yeah emulate and test the problem is actually creating tests scenarios and actually test equipment around all that so yeah especially the orner scenario I mean I don't even know how I would try to set up the detectors and try to go but that sounds like fun so yeah yeah well next year we'll have something like that yeah more questions there
thanks for the presentation I would like to know if if it is possible to detect through the TOTP MAC addresses so if they are valid Oh uy prefix from the nmap prefix list so I will select randomly or just deterministically through the TOTP secret I will use that to pick one of the vendors and then use that to pick one the rest of the termination of the man and if you if you guys have the attacked installed on that network through through the time a lot of MAC addresses will be detected no because yeah I've forgot to mention that part if you look here you will see a message saying stopping TOTP why because the
connection has been initiated and now it will stay at the MAC addresses it was big because I did notice that and that's one of the things I fixed because it couldn't be keeping changing VIPs their MAC address is every 30 seconds that would be a red flag yeah so when it gets a connection it stops there and then when I leave or timeout which just happened then it will start again the process of scanning what is what's around it and yeah blah blah blah so you are witnessing it right now yeah that's why we keep the program running your questions okay okay go to the to the station and just try it out on the
mobile device because that is the practical implementation err [Applause]