CTF Walkthrough
Show transcript [en]
my name is Jackson how was the evil mastermind behind the other CD f's how many cuts xx you okay I don't know how many people that finish knishes set seven okay not that I miss and reduce the resolution of the CPF I'm going to to stop this because I don't have much time so basically this is I made a storyline behind this basically these sites is a organization that fights sorry
so we are Liberation's Googlebot that we're trying to sit down I'm not going sorry why not forever but this step was made up of four exercises for challenges and okay I'm going to start with really simple but I think a lot of people that start on here but I'm going to show you that it's not that hard because I'm going to start okay so everyone knows this part right so this is basic 64 this is really simple you could do this with any jeweler that you you want it cure you anything okay so everybody got to this part right I know that this is a very common encoding and I'm talking on the super revolution
well it's hot encryption or anything which is an encoding so if we see here we have just capital letters and equals so if we didn't know what what it was because just search on Google I'm coding betting people's if you see the first results you will see that that meant many up so the first result is actually advice 32 article where we see an example that uses three equals s P so from this point we just need to decode meed color online for base 32 I think want to make okay so this is a little we see that this is a decimal and we see our positions on the numbers so when could assume that this was just a ski or
that I tried if you can see it but I'm crossing meet you yes so this was the first flight okay and I'm going to prove to you that this is so this is our a precision EMP cannon that we are now we are requesting our supply to strike to manager and we take you out and that's it this is a this was the first challenge second under the player I sleep with some that even means on the titles and you will notice that specifically on the third the third challenge but this this is what I get it's just an image and we have to figure out what's in here in this image so the first thing that I normally do in this
kind of exercises is these staggered X because it's a very nice tool to analyze images and SEC the decks will tell us that there is actually some some like that appended to the end of file so one could also use a tool called people and what will also help that there is as if perfect encrypted zip file at the end of the of this image so from this point to NZ the path so I'm hoping the file to a specific section and then zip it it's asking us for a password and so we need password I'm showing you that there's actually better so right now we and the password must be hidden somewhere as having being
12 because it's the only thing that that they give you so which spits out lots of information about the new about the image and mr. interesting comments you see that it's kind of strange so I'm going to show you you can also see this information on Windows when we do this is really simple you should set to go to properties on the details and it's right there the comments again you could you could not enter fight that this is just a ski and an X so what I'm going to do is to rebuild it again you're honest I miss apart here and the password is first strike elite speed mode so we have not the contents of the seizure of the
deep inside image and there we have it we have the node ID incited now we just need to get and we get flight
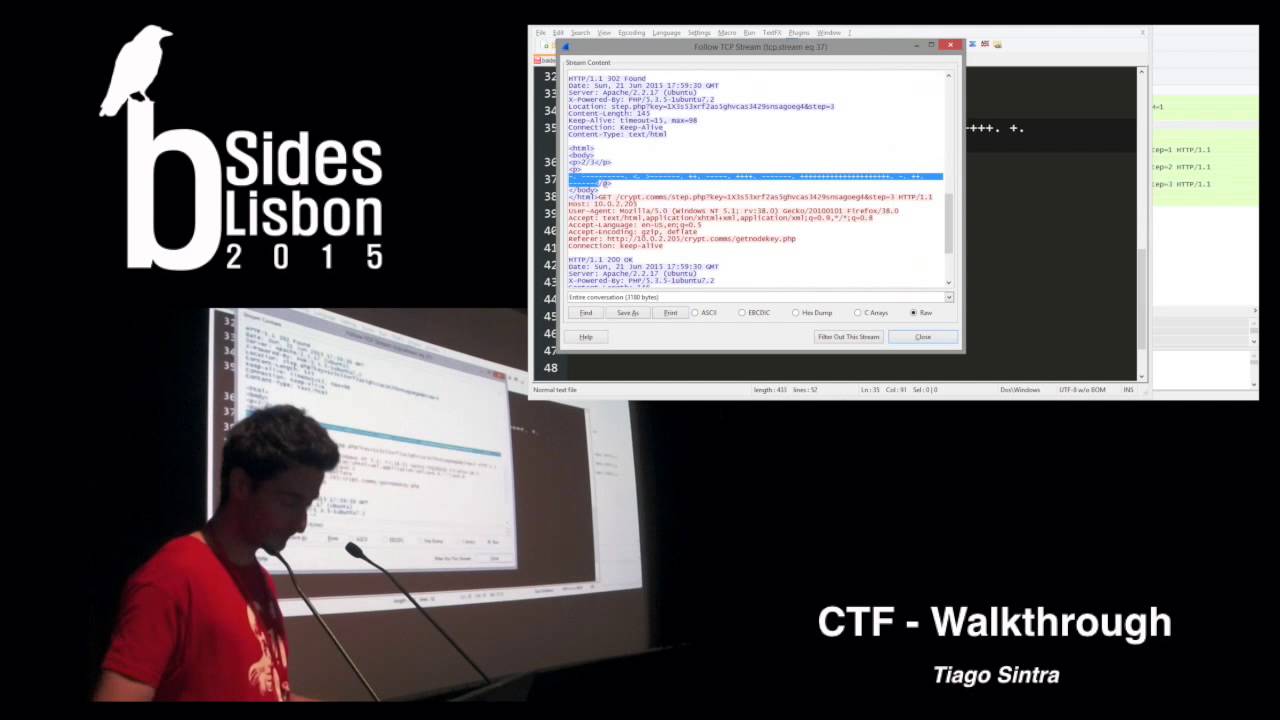
pretty simple again I'm gonna just get our subway and it's firing Indian people eyes so we've got two dollars now and we're going to the third challenge this this challenge was interesting the people were really great so basically what I'm saying here is that we intercepted some packages some packets so I give you a link to a PDF file I'm going to download it and open it on fire sir you could also use network miner or any other tool that over speaker I'm using my chart this is where things get complicated I try to do this as simple as possible so in my opinion it would be very creative creative in this one so let me
just pause for a second because this pcap well as I actually expected this from a malware malware analysis on the Internet what I did was to strip out foliage detecting and I injected my my my my knee HTTP traffic that I did on my pants but some other data which was not HTTP and a lot of people were losing time on that because it's actually real traffic that was so we that was an Gmail account with the best word
but the thing is is it was supposed to be simple right so I think with me I'm just so what we have here and we see here that basically it's like a page that will directs two times and give us some hints that to follow the points treatments it's the encrypted key so here we see that the body is each way to redirect the parts of bevel as you see here is the first part of three two part three I think this was kind of logical so I think the first step here is to concatenate everything this is what I'm doing here and everything so for some of you would look at this and right away
you will see immediately what it was for for those of you who don't know it but for those of you we didn't know what this is the title actually add even and you'll see whether why the title is wired language so terrible or where language and with such are Google for wire language and notice that google corrects you in suggest that it's clear language human memories we want like digital stuff so so good
you're evil yeah why computer languages I guess that's what we are talking about right here so any one of these links will show you right away what it was so I'm going to open the second one from we bet which is very trustworthy source
so we're going to scroll down a bit and there are examples for each each weird language and so let's scroll down any pointers and they are all too fat and okay so right away we will see this 25 so what we need now is just to decode this using a bring our encrypted text and there we have it to be as in alladhi step once again I'm going to put this on our inspector
I think this just a lot of fun great okay challenge was a very simple reverse challenge not anything near remotely like Marco do maybe for next year is a new 32
we found the ports on a machine that allows us to download the botnet client so I don't love these clients and I'm going to open it for you of course it study run this without any problems because it's a malware client asking us for encryption efforts I don't know what the password is I'm going to put something and it says about for a checkup so one thing that you could do was to okay maybe it's asking us for a password but then aa B will be outputted by the way so one could think that's okay let's search for Strings and this is executable minus n 19 which is the size of the anomaly if you if you think its
8:03 16 plus 3 but if you there is no nobody here that's because I have encrypted it it's using a short version so you will never you will never just by strings using strings on this tiny bit ago so we will do a little bit of reverse engineering and I'm going to show you a few I'm just want to open my immunity I mean crystal at once I can see so I'm going to get to the entry point and then I'm going to scroll down
okay so we'll just hold on of it's on the to get the interesting stuff we already know that the program is asking as far as people encryption pepper so here we'll we'll find the string and I really here we see that the program is asking us for a password and now we see the good stuff here so if this if you notice here is a lot between getting an account or password accepted so a simple way to would you check this would be to find reference for this password accepted line so we see that immunity gave us that the reference is this channel so it's just it's not 0 so if you reach here I'm going to put a
breakpoint here and eventually the the code will reach this parts and make the validations of the best work some will put something which is not a pestle obviously so we have seen here that immunity is telling us it's it's a breakpoint and is having its that the job is will not be taking so we want to take this jump because we are we want to go to back password not spell buster so this is really simple because oh yeah by the way DX is zero miss comparing to zero so that's why it's it's not jumping because it will jump only if it's not zero so what we can do here is very busy it's just we see
switched jumping from zero we jump it and this was one of the many solutions because I thought that there are some people that changed the beats of the fly but bears on the beets or of ax Cupid go go lots of ways here I switch to 74 which is to jump with people and now we see that the immunity is telling is that the champ will be taken so right now I'm going to do a step over and actually see the cub jumping to the password accepted and I rehab it's now I'm going to run and the program will decrypt the password and if it's done on ID I'm going to move to put this on a notepad
so you can see it and there you have it we find the less flag and the main command Apple ID
it was simple and this was the final exercise any of you could reach here you will see this we have the fried servants and you will be rewarded by the agreement okay this is it guys I hope you enjoyed this





