GT - Navigating the Changing Cyber Landscape: Trends, Costs, and Risk Mitigation Strategies
Show transcript [en]
thank you very much for coming to my session I know there's a lot of very interesting one going on so um just a quick intro i w company called M it's on it was on you try it again test test is that better is that better yeah okay
oh it's super good now try again can you hear it okay good yay okay all right so yeah I work for a company called Marsh mcclinon they're one of the biggest insurance broker and we do a lot of cyber broking business thousands of companies probably about 70% of Global 2000 we broke for them um I'm wanted to talk today about navigating the changing cyber uh environments and um quick intro um talk to you a little bit about the data and talk about the different trends that we're seeing uh you probably see a lot more um graph and statistics and stuff I build risk model for living so uh you're going to see a lot more different cost
components how long does it take and what the price look like so on and so forth so um I'm going to go through some of those including privacy specifically to business interruptions and as well as some of the ransomware trends and how many people are paying not paying just give some of those type of Statistics in addition also um there's area that's rising to become a pretty big risk and that's something that we should consider and then um the last but not the least how to improve the odds using what we do for research so go from there um data source so the data source that I have based on this presentation is sideway loss data flash
point uh any of the public reporting such as 10ks and so forth some of those large losses coming from 10ks um also all the marsh mlin claims so Marsh is a US brokerage business and then also the some of the UK European claims that we have as well as the insurance portfolio Mars mcclinon has a company for called guide Carpenter guide Carpenter does broking for all the reinsurance Brokers so all the insurance portfolio those type of uh when their the portfolio have claims we also import those data so um I want to keep the majority of the data from 2017 to 2024 depends on the Peril because like for ransomware it didn't really start till
2019 so I start 20 counting on 2019 on so that's how um uh the first part is Trends and statistics so this is a uh set of cyber events around 116,000 events from incidents from 2017 to 20 April 2024 I should not 2023 I I see a mistake now I didn't catch this one but um that's how many of those um um in the current environment uh one of the things that uh everybody's worried about is aggregating risk third party risk is top of a mind uh some of the common vulnerability Hardware software like the CR strike thing those are things that this is actually a slide that was generated toward the end of last year so we had
like common software hardware and that was already there and sure enough we were worrying about that and that came came out uh the common depend dependencies uh digital suppliers they all depends on one another um we had about 60 60% of the company has over 1,000 suppliers that they work with so partners and suppliers and of course the joke political stuff and in the Privacy regulation this is a new area that um didn't used to see as many claims as we do now uh gdpr findes definitely gotten a lot more popular uh and then the alphabet soup of the uh lawsuits CCPA bppa uh the first jury trial with bppa was the settlement was 44 million the second one
that we saw was 1.4 billion for the megapixel settlement between Facebook in state of Texas so that we also see a number of claims on that one as well too that start come up as well uh Pixie tracking that's also popping up a lot and in terms of uh data environment data encryption and bi are the two biggest uh concern and those are the generally the larger claims that we have seen uh so compromise if you look at our um claim rate about 80 some per of those Marsh claims did not have ransomware but still there's almost 88 90% And from quarter to quarter that number goes down one point or another but there's still a whole bunch of them
uh we definitely see more of the fraudulent fund transfer stuff as well as other kind of things that we're seeing uh supply chain that's definitely become a hot Button as well good news the rat going down you can see are the all the rates uh in terms of per you know uh starting with 2022 used to be really high it's going down a lot but that means a lot of our clients actually are increasing their limits and um uh re-evaluate their how do they want to uh invest in Risk Management stuff uh opportunity to look at see what are the cost of risk to them and if they can use the extra money to just increasing the list and then you
you can see the primary layer and the the total price both went down a lot uh I don't know how the cloud strike event going to affect so far we have as of Friday we had about 143 claims from that one so it's getting pretty high again this is a slide that I created a while back and sure enough that's the you know I added the cloud strike thing I have everything else on there except the cloud strike thing so uh widespread events zero day vulnerabilities zero day vulnerability on 2023 has becoming uh pretty um that's what Drive everything down because privacy event have gone down but except uh 2023 jumping up again due to zero Day stuff the clouds
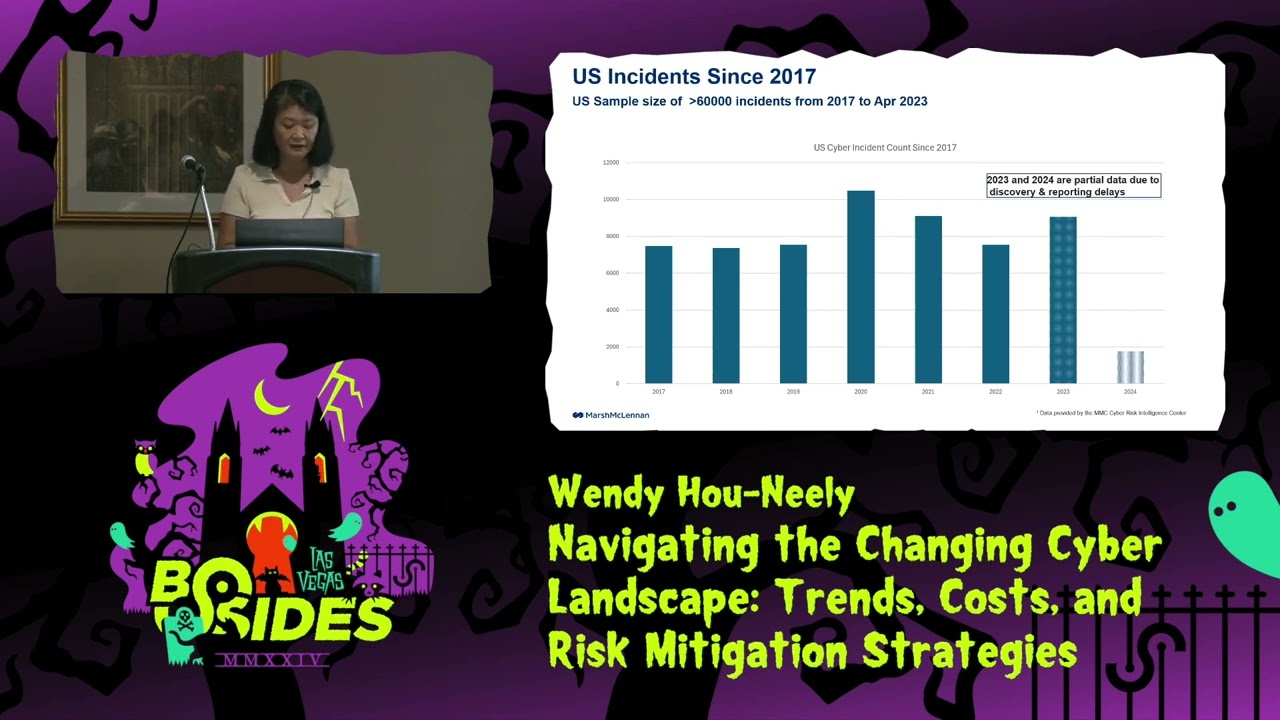
Microsoft Exchange move it uh move it had about over 2,000 organization that's affected the Cisco event as well as Cloud strikes about 8 .5 million Windows device and there's going to be many more of those things so and if you look at the incidents worldwide you can see us still number one Canada is number two now and Great Britain it's number three and then India this is just event count not frequency this is just an event count so but us tend to have the highest frequency and this is if you look at the US itself um 2017 it's General still increasing uh 2023 is probably partial data we had about us incident itself has about 60
more than 60,000 events from 2017 to April 2023 uh 24 why can't I 2024 I'm I think that one was one of the things so that should be 2024 so that's uh that we can see that in 2024 data it's uh totally partial so you probably get less than a quarter of data on 2020 for for that little thing on the botom the side in terms of cyber incident by industry you can see that um Health Care being the highest count and then after that is finance and insurance and public administrations and those are all increased you can see things are increasing in the green which is the information system stuff as well as the
manufacturing starting to increase in terms of uh we see a lot more uh Ransom more event in the manufacturer sector now also so this is the next chart this is a ransomware the other one the previous one is just um all cyber event privacy everything uh business Interruption and as well as ransomware so but if you look at uh ransomware uh manufacturer being the number one in terms of counts and then uh Professional Services like account accounting firms law firms those are getting hit pretty uh more frequent now and used to be they're very small if you look at the 2019 they're a little ban right there but it it comes over it's almost twice as much as what it was
before so we can see how they evolve in terms of Industries um here's one of the things that we were playing with um we want to see how what are the things causing the from the Cyber event that caused business event so if you look at it you can see that uh network bridge uh almost majority of it coming from either extortion or privacy bridge and this we just ran this for the retail industry and it's you can also see impersonations it get a lot of theft of funds most of those type of event and then system decreation goes to business Interruption event and that's how we saw of all the events percentage how they
came in and then where did they end up that's so it's good indicator all the existing data going for bridge response um the data average is right around a million and so um the 99% tile is about 57 million so uh you can see where things land in the 50 percentile one out of two it's almost a million dollar so the average and the 50% how come very close so um legal this is one that everybody keep asking me how much is legal how do you model legal what what are the things legal so legal on an average data average is about $4 million on what we're seeing and the 99% tile is about 266 million dollar so legal is a
big chunk of um um cost in terms of cyber event because even if they don't Bridge your data even they just touch the data you still need to talk to legal counil to say what are the things that I have to do to be compliant so there are things that you're going to have to do so that's what the legal cost look like data recovery so data recovery on average is about 2 million uh based on the data that we have uh up to 26 million 99% tile um this could get to be quite High depending on what kind of data so if you are engineering firm um your all the blueprints got hacked and taken away so
then you have to build a project you have to start all over again those kind of data would become very expensive uh if it's you know a set of customer type of data um it could be expensive but you don't have to build everything from scratch if depends so this wide range quite a lot um so in case you had an incident how long does it take for me to get over it so uh the median in terms of detections two days uh containments pretty quick but analysis take over a month notifications and discoveries and stuff like that take about two months and then the average on the detections it's a little over a month to detect it
and uh if it's a network intrusion it's also 36 Days uh containment containment is about four to five days but yes you can see there's very varies on here this is from uh Baker and Hustler one of the dsir report that they have so it's kind of interesting to see how um what a difference between median and average which means that there are a lot of company recover detected very quickly recover very quickly but in general it will take a while over a month to do the analysis and notify your customers and so on so so I'll dive into privacy a little bit more and privacy I go back a little further because the data in general
takes a long takes a long time for those case to close some of them from 2019 2018 those are still open those cases still in litigation so I kept data that's longer uh privacy in terms of privacy risk um data is still a pretty big components of it this of all the most impactful cyber events uh we saw 2022 got little less but 2023 due to the zero days it jumped right back up again uh data assets uh all the pi PCI all you PRI informations those kind of stuff and it's important for you to categorize your sensitive data and St store them accordingly and also to understand who has ass access to those data because we
had a claim that uh for example it's a partner it's a bill collector and they had a data breach it's a old guy Bill Collector and um they can't pay it whatever it is the cost was too big so they went out of business well guess what the company end up with the bill so they end up having to do all the bridge response notification everything else so watch look at the partner as well who your business partner is make sure that that is something that you would want to think about um additional risk area this is starting things that's coming up now uh biometric data all those biometric that bppa uh Hippa alphabet soup of all the
litigations all coming up a lot now uh so the next wave of things that we're seeing is Digital Risk class that involving allegations of illegal data Collections and sharing and um all those collection of data because of the llm model that that that's hungry for data and you're collecting those data and sharing those data building models for AI those kind of stuff we start seeing some of those kind of things coming to play uh and make a pixel pixel tracking also too that's also uh popping up quite a lot uh tracking the customers habit especially the healthcare industry they're complaining that they collecting their pixel data uh to to to uh look at what kind of how how what kind of health
issues that they have so that's in lawsuits and stuff like like that so if you look at this uh the this bigger household they are defending about 300 privacy lawsuit type of case about one out of every you know uh there's a big amount of those claimed I can't remember the exact number I think it's one out of every hundred claim uh event has a privacy lawsuits don't I have to think about that one so here's what we have so in terms of if you can see the last few year uh bppa you can see it's increasing from year over year but the meta pixel it gone from two to one to nothing to 12 of them
last year and I mean 2022 and then uh 44 and 2023 so tracking of customer use how they it's becoming lawsuit as well so and then the bppa claim uh right now a lot of those uh lawsuits are pretty hefty lawsuits so here are some of the large data losses I kind I updated this slide using more recent data um my marketing took out the names so no a lot of those are our clients so we don't want to show it like that so give her the country so you can probably look it up the dollar number and look it up and this is number coming from either from the company financial report or from their press release from
their 10K that they files and um this is just what they disclose this a lot of this I would have to say many of this is only partial data this is not the full loss amount so you can see some of those could be become very Hefty uh the settlement fines and penalty um this one's all public it's everywhere so I was okay to show names so this is some of the big numbers uh if you see the line two that was the settlement from Facebook to state of Texas that's the $ 1.4 billion dollar settlement for taking the uh uh the bppa informations biometric informations for for Texans so I don't know if we ever
see any of that so here's some of the his hisorical uh per record cost that's another one that everybody's asking about uh how much does it really cost me if I had a data breach and again this is what's disclosed uh some of those numbers I can guarantee you some of those number is more than double what it is they only disclose a certain amount uh others uh got away with like Marriott for example that it was 36 Cents that was right around 2019 that when it came up and they said hey nobody is staying in our hotel we're not making any money we can't pay this so it went down a lot so I wouldn't expect
that to repeat again but um if you go with the IBM's estimates $149 somewhere around there per record so I think that number is a little bit High depends on the volume of it but the range of ranging from 3610 to $547 so that's a pretty big Hefty tag if you want want to look at it business Interruption this one you don't hear about it until you really hear about it so um in general this is kind of what put cyber Insurance sort of on the map in the sense that for a long time before 2017 nobody care about cyber insurance and then they not the W to cry hit and then the not pet hit hit and that's when
they oh we need cyber insurance but then we don't hear a lot about it because um most of the company when they have interruptions they don't really have to disclose that they had an interruption or if they do have to disclose it's because it's really big so it's either all or nothing and then of course the latest one is the cloud strike one um due to Sol for bugs and that is also uh the estimates right now is saying uh 1 and a half to about 5.4 I think 5 for is a little high but still um we'll see um this is excluding event from Ransom War this is in general business Interruption so I'll talk about what's
different kind of business interruptions so there's the security failures and software failures and so forth and the first one in general the business interupt you cyber policy will cover your network business Interruption security failure malicious hacking DOL those kind of stuff it would cover the second one is business Interruption due to system failures and system could be software as well and by default the marsh policy language does include this one but um if you look at other policies you want to make sure that is in there as well so the software bug that cloud strike was talking about it's a software bug in a third party software used by you and a lot of our client that is
covered in our cyber policy but not necessarily always the case so this is things that you know um you do have to pay attention to some of this and then there's the contingent business Interruption so anything by a third party provider and of course again look at your policy language there are it providers there's non it providers for those as well too so be be careful of the last two what is just cover cover the it provider or doesn't cover the non-it providers so the things that I want to point out to everybody to talk about what is to look out for when you have business interruptions so additional risk area to consider for business disruption it's
here's the number uh 60% of the organization have 1,000 more than 1,000 third-party Partners that's a huge number and then more than half 73% of them have experienced significant disruptions cost by a third party whether's data breach whether's uh whatever things they have so don't think third party is not a big one of course you all know Supply chains all the common interdependency of softwares and Hardwares and and you store things in the clouds and what are those include if you talk about sales you know loss of critical suppliers uh like we have you know one supplier for the chip for Nidia for example Taiwan semiconductor those kind of thing so um supplier dependence uh I
don't want to get into the geographic political risk but I think that is one and that's starting to come up more about the war ex declare and non declare war exclusions in the policies and of course use the AIS um uh and the infrastructures that powers AIS so what if the infrastructure have issues what how what's going to happen to it uh there's access risk there's various type of plug-in designs uh those kind of things uh and also a lot of the data risk uh this is actually data risk is one of the big thing that we're very concerned about it's that what if they hacked in your data that trains your model and if if you were healthc care
provider if that data has been tampered with what would you come up with um and what if that's something that went wrong what would happen after that so that's part of it and also the hackers the bad guys also using Genai and cyber CRI crimes and stuff like that they also offer chat Bots with guaranteed privacy and and an anonymity and those Bots are specifically trained on malicious data including Source codes method techniques and other criminal strategies so it's Race of Time on AI on how to manage this one and then of course there's a different kind of thing called the operational technology so I'll talk a little bit more about that we hear a lot Mo mostly about it and it
and OT is a little bit different OTS is stuff like the SK skater system the things that manage your um water supply to say uh you know pipelines and utilities and powers and most of those systems is 20 30 years old systems lots of vulnerabilities um patching you can't really just say oh weend patching and shut down everybody's electricity it doesn't work that way so it's a very opportunistic and where before if you look at it there's only set amount of protocols but on OT side there are hundreds and hundreds of different type of protocol even the dolphin tank at the one of the hotel here it's you know at one point it was still S&P
protocol I don't know what they have changed it now but that's how they control the temperature of the tank so um in in OT risk also too when it goes down it takes a while to come back up and that's not something that um so often time we see it is connected with OT and there's different ports that in the OT side gets open and then once that get open we always see things that goes wrong so so here's some of the larger business Interruption event um we can see uh this is updated based on the dollar amount as well as time I try to keep everything from 2017 but I think I cut one that's 2014 here
so last thing but not last parel I'm going to talk about is ransomware um so ransomware I have data set about 40,000 events and only the event that intended to extract Ransom we call it ransomware so like a not Peta I count that as a bi because they're not really there to extract bransom they're there to cost disruption so some of the large ransomware losses that we see uh manufacturing if you look at the numbers this is a lot smaller in comparison so one of the things interesting about this Peril is that in the terms of tail this is a lot shorter tail recovery a lot faster compared to privacy Bridge compared to uh business Interruption
event so not to say this is not a bad thing but um this is a this is still apparel that's increasing in frequency and there's increasing also starting to trying to get you data so that they they can more be more effective in extracting The Ransom so if you look at the frequency year by year uh you can see on the top chart 2019 is a little bitty and I didn't put bother to put 2018 on I actually ran a Time series at one point and there's definitely a break point between 2018 and 2019 so 2019 was the starting of the really bad ransomware stuff ransomware is a service now if you look at 2023 it goes up much higher in
2024 there's still more but if you do it by quarter that's what it looked like on the bottom chart um total known loss by year so 2021 looked like a very bad year but again this is also just what's known there's a lot more to it than this so we can see there's um this is just by year you can see that it's up and down depending on the year but uh if you look at the frequency wise uh 2021 was high but 2023 is still quite high but one thing we do see the trend is this is validated by multiple um data source uh of those who decide to pay not pay from the data we have it's dropped
down to about 22% on 2023 and if you look at c-ware data they dropped down to about 28% um so it started when 2019 was about 60 some per it gone down to about 22% from our data that we have so lot more company are got having better control now they better backup better you know way of recovering preparing for it practicing if that happens uh so they can refuse to pay Ransom we do see that as a trend uh in terms of bridge response cost from 2019 to 2023 of the data the average also kind of go the same thing still 1 million this didn't change a whole lot the medium Bridge cost about constant
pretty much um the tail uh it gone up turn the tail because there's few large very large event on 2020 2023 so Q3 2023 was a bad time by and here's the Demand versus payments if you look at the medians of this um of the little horizontal bar the little horizontal bar this is the actual pay Ransom pay and you go year by year it's increas ining in 2019 to 2020 2020 to 211 pretty much just stay the same didn't change maybe lower a little 20122 it went down a lot but 2023 went back up again and the largest Ransom Demand on this list was $175 million demand so yeah that's in 2023 so that
that's this data point Thank it it show no it doesn't show it the power Point shows it but on the presentation mode it doesn't show it so um so just to get get an idea The Ransom demands kind of go the same route as well 2021 is flat 2022 is almost the same 2023 went back up um here's Ransom pay so the median of our data from 2019 through 2023 it's uh for 20 23 is a lot lower compared to 2021 look at the median in 2021 uh it's it's about 5 million that's the median that's really high and then was moving on to uh average the average here is the data average all the other
is a percentile so we don't want to actually tell you what they actually pay so I did a log normal distribution and give it the percentiles to get what the range are so so how do you improve your odds um using our research well for Vore be mindful of your electronic communication if they're in your environment they know exactly what you have in there they if you send the policy back and forth we've seen it they actually know exactly what your policy limit is and they say Okay negotiate all you want we know what your policy is so um this is kind of uh things that we have seing uh also don't contact the threat actor
directly uh talk to Legal about uh what are the laws notifications that you have to have uh there's a thing called the ofac um requirements make sure you don't do business with North Korea or other sanctioned countries and you have to make a decision whether you pay or not pay and then understand and involve your insurer and also keep all your records and stuff like that and track data recoveries and restoration calls all of those need to be tracked the next one this is just a to-do list uh I'm not going to go through every one of them this is a good to-do list before you have to uh you this is something before any incident happened including your
ransomware event you wanted to know uh you know what if they demand for something what if you double this extortion you should have answer to all of this questions ahead of time so this is a good checklist that you could have to say Okay do we have all this stuff and what kind of public disclosure do we have to have who do we need to talk to uh in case there's an instrument who do we call and who are the sanctioned entities can we make a list and do all of that stuff just to understand who to get all those informations from so preparation preparation this is what need to happen and in case you have to
pay a ransom um I would work very closely with your carriers and then you want to engage the outside Council and extortion Services guys to negotiate we do see negotiation have gone came back to very positive results so they are worth it um they also would provide intelligence to you know about the bad guys and what did they do what do they done in the past and then extend your payment deadlines type stuff um testing the encryption keys that they give back to you and then ofac checking those are all the um extortion Services could provide and then uh if you decide to pay don't pay the B actor directly pay the services guide let them deal with it so I think
that's it uh and then if you cyber carriers speaking of cyber carriers next one's also a list this is a list I know there's a lot of words in here sorry uh but this is meant to be list of what the insurance company expect you to have when you file claims so this is ahead of time just to give an ideas of what kind of a is it contained is it encrypt how does it impact it have you how many record is breached uh did you get them all out did you clean it all up did you is all the stuff yours that's you know those kind of stuff that the things that they would
expect you to have an inventory of it um um I talked about last year about a top control and uh this is one of the control by signal string so this is a uh we did us when companies come to us for to get insurance we make them fill out a questionnaire about several hundred I don't know it's quite a few hundred of questions and talk about their environment talk about the practice talk about the training talk about everything that so here are some of the system uh question that you see for the example of those kind of stuff so we took that and we get a few thousand of those a year so we took those thing collected those data
and collected the claim information we correlated so we can see the hardening technique has a very strong correlation if your configuration tools such as your active directories not set up correctly that's going to be you're going to very likely you'll have a claim so those are kind of things that we've gone through the study and the correlations of those strength and here still for 2024 this is still the same 12 cyber control security controls that we expect our client to have and filling out the those questionnaires also too help us assess you know what are the area that you not as strong at and if Improvement could be made if you made those improvements then
you could po potentially get a better rate and so forth and be easy to more company might want to come to you uh want to ensure you as well so those are kind of things this is the list of uh controls that we still recommend to all of our clients and if you don't have the top six a lot of the carrier won't even Ure either won't insure you or charge your arm and leg that you don't want to pay basically so lesson learn reduce your data reduce your risk uh store less and delete more have automated deletions and limited data provided to your supp suppliers and um uh there's a maybe have a make the supplier have a surface level
agreement that have delete datas up to dat inventory of your data and classify your data and treat them differently and understand where data store and third parties third party partners that I keep going back to supply and third parties uh so plan for zero days um IBM says average cost saving with the Cyber event is $2.66 million if you plan for it um so educate your staff and the last thing was Workforce training so this come from the law firm as well as uh Coalition uh doesn't matter what you do you got to train your uh Workforce to understand your risk environment to understand don't click on stuff and you're not supposed to and don't
download stuff you're not going supposed to go to and don't click on this don't do that so anyway that's the uh Sans has a good training class on those things that's it [Applause] questions I have my email on LinkedIn here yes
check thank you Wendy can you uh share with us why Marsh considers the crowd strike outage a zero day attack no it's not it's a software bug right okay so that's now that you clear that up thank you thank you very much yeah yeah so that is insured by the way if you have that's insured under third party liability correct liability is insured and it depends on what your language is in general if no it's actually in your cyber policy the second one it's the second one on the bi thing let me go back to bi oh right there oh yeah that one that's the second one system failure Sol BS in third party software it's used by
you okay great thank you so by default the language that we have in our policy paper we do include those but some companies some insurer depends on where you get your policies and stuff may not but you want to make sure that is in there as well and same as con so if you provide services like uh software as a service or environment a cloud type of thing um you want to make sure that is also included great thank you
yes Optical course so uh great presentation by the way thank you um so in your network um you know in your breakdown of which uh what are the most common sort of um in like breakdowns uhhuh one was like Network breakdown and the there was a impersonation now if if a system administrator's credential has been compromised to then uh compromise yeah the network breach right uh so if a system administrator's credential is compromis is that a network breach or is that an impersonation it could it would be could be a network breach okay this is just what we did was we took all the uh claim informations that we have and the event description deson that we have we
classified it so how did they get in is it because of misconfiguration is it because the network breach is it because impersonation if it's because of so any of those kind of description and then we look at the back end on the other side what kind of business event did it trigger did it trigger you know uh extortion did it trigger whatever things that right no I mean um because if you're compromising a system administrator's credential it is actually impersonation so I was wondering you know are you yeah if it's it's not so clear in the sense actually this is one this is the stuff we actually use a large language model to do the classification for us thank
you
yeah
yes and by the way this is just for retail I didn't run it for the whole thing does Marsh track statistics on um applications for insurance that Marsh has either deemed uninsurable or that companies have decided that the policy is too restrictive to afford we don't track specific applications we track what industry you in how much Rec how many record do you have what do your control environment look like and we're try to get you to do better in your control so you can get a better coverage uh application wise there's so many homegrown applications that you can't track all of them because sorry uh when I say applications I mean applying for insurance so companies that
have applied for insurance with Marsh that have been denied a policy or that the policy was so restrictive to cost that a company has decided that they couldn't get into cyber insurance usually it's because one of those 12 controls that you guys whoever it is didn't do yeah but it's not tracked or it's not tracked in terms of application wise oh in terms of application like number of companies we don't track those um okay we usually yeah we don't track what what did they usually it's because of the control one of those five controls that they didn't do and when we say you need to get this done before you apply and they didn't get it done then the carrier
looked at us uh we don't want to ensure that so yeah yeah thank you
I'm on [Laughter] time thank you





