Risk-Based Decision Making in Security Incident Response
Show transcript [en]
all right can you hear me now excellent so who here is involved in security incident response we got a good number of players who here is involved in security risk assessment and all that management that goes with it okay so who does both there we go not very many our dilemma was somewhat like this were we're passionate people all of us in the room we're trying to present something that people might find a little boring so we're going to do our best to to make a good show today and what we're gonna focus on really is bringing a risk-based perspective to security incident response I'm Keith Jonah and I'm Kevin pewter smile very good all right warning
we're actually not here to go through a full security incident response process that's really not our focus ours is a bit more kind of focused you know and but how to bring a risk perspective to it we will talk about kind of a general security incident response process but we're not here to pitch it per se but we have a really good presentation for next year if you'd like to see that one so oh sorry speaking into the mic so here we go concept and unfortunately we don't have a different screen down here but we'll wing it the concept of risk decisioning during security incident handling that's we're trying to bring to the stage and
we're doing a bit of a test where's Alan Alan this is for you if I had two to five minutes to give my presentation I would do it in the following manner just so you know just watch but we would start with input and really what we're going to talk about is quantifiable measures if you will of impact and the degree of compromise at a point in time and really there's three perspectives that we're going to look at potential impact as set by a business unit prior to the incident current impact Institute you're right there you're dealing with the ship and you're trying to figure out how bad is this what's my impact at the
moment and also what's my degree of compromised so those only three things that we're going to talk about in a great deal of detail the outcome of this risk decisioning process though is we call the si severity level which is probably you know one that everybody tries to use because when you're doing security ins in response you're always going like yeah I lost a laptop over here I've got a mail thing coming in here spamming me I've got I think it's Russia coming in through here the attack pictures are all very different but we're always trying to figure out even how bad is it how much energy should have put how much priority should I put so that's the
challenge you need to select a level of response you got to figure out how fast how many do I call out the guards like what do we do we need to determine who should I tell in our chain of people who send us money every month in terms of the notification addresses as well as the schedule of updates because by law and other aspects sometimes you have to have very very timely materials going out to people to say how bad is it what are we doing about it and so on and finally we also have to set what's the seniority of the people who should be on the cert team to respond to this and
those things might change over time if we only had five minutes al I would give you two slides one we'd throw up this slide and say it's a risk model and we're bringing risk to security incident response and we tore up this slide and this is what we do about it okay but we're not here and we do have slightly more than five minutes okay so what we're gonna do is I'm gonna turn to Kevin for a minute we're gonna start slower and say well let's start with what we'd like you to take away and then we'll work our way back Kevin over to you sure when you think about it if it's a risk assessment what you're really
doing in an instant handling situation is it's a live tra you're sitting there wondering you don't really care who's attacking you per se you don't even know necessary but what you want to know to stop the damage is what's the potential impact what am I trying to do here so you're on fly doing a threat risk assessment so we came up with the concept of something we call psych on it's the security incident condition it's a it's a value that's a floating value that is changes over time based on your feedback your investigation your dodging everything that you're doing and then the severity level is something where you kind of go is is this guy
polling how fast because you're not gonna handle every incident same way right you're not gonna handle something that is like an email threat the same way you handle a huge dass attack right so you have to have a way of kind of grading these attacks so that you can throw the proper resourcing proper seniority at these things and the other thing that we came across was just in the traditional instant handling models what I found was it's very linear you go through these phases and heaven forbid reality actually kick in because I remember one time I was doing an incident and I can talk about this now it was a Ontario government's primary DNS server so where are you anyways we
had been compromised and while we're doing the investigation on the DNS server we find out oh wait this isn't the first person who's been here we now have six other people on here so all this triaging that we're doing everything we're doing was four oh crap now we have to go back to go start retreating because now we have multiple incidents really on the start so it's not like a straight linear slide through where you go you have one incident and you're just able to deal with that sorry that's what happens with life when you're busy making plans right so instead what happened was we had to get into Singh where we had to go back to go
when we got into his multiple iterations and it was not like this thing where we went straight through it the other concept that we came across was this notion of a security incident ticket sometimes is actually the IT team that you're investigating so you don't want to have your security incident ticket in their system it's like you know emailing an email blasts when the emails been compromised it's kind of stupid so if you want to if you want to keep the IT team out of the loop you got to have a separate ticket system some in some way that it's air-gap from them where they have no way of getting at it and then finally there's with the traditional
models I also found another thing is they have this phase called eradication and whatnot and containment there is no such thing if you lost a laptop so you have to have a framework which is flexible enough that it can handle also types of security ends it's not just the ones that are IT based question they are but you can be selected but who you have right and and I that yet there's always a risk in anything you do yes you could actually be inviting the person who is at the root of all this into your inner circle absolutely this is not perfect but that's the best that we can do right I don't have all the answers but the
thing is is that you have to have a certain level of trust about who you bring in and it's the most senior people and you look at and kind of go what to be motivated to do that or whatever no it's probably someone that you know you just did some downsizing and that person was one of the people going out so this person who's still here you have to trust at a certain point right sure thank you we're putting up some definitions but we're not expecting you to read them it's just more for us to today have a bit of taxonomy to work with so recognizing that you know if you will coming in the front door is
typically the adverse event you're not sure what to do with it it may or may not be a security incident you have or we're going to explain our security incident condition which is really a rating system or how badly are you compromised as well as the SI severity level in terms of you know how to prioritize what I should do about it next but what we eventually lead ourselves up to typically is that we're really arriving at we have a security breach and then we get into the discussion of is it a material breach yet or not material being it's very significant but those are there for your kind reading after I guess but what we
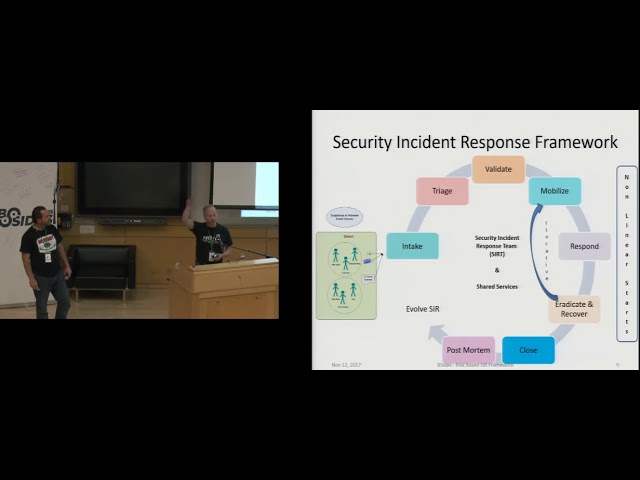
wanted to do was just introduce now if you will the general framework and all the friends that know me know everything starts with a circle so we open a knife slave psycho circle and I'll let Kevin just walk through it this is at eye level the purpose of this one is to show that it's not just a one-time walkthrough it is a self-healing mechanism or self-improving mechanism so we go all the way around through all the different phases we might muck about in this phase for a little bit because we have the nonlinear starts and that's where it's like all sudden you discover a weight someone else is in there too and you have to go back to go and you have to
accommodate to the new realities before you can actually get through this whole understanding what you're dealing with right through to the closed postmortem and then you evolve it and again with the whole thing with this icon is we have these differential levels of severity so it does everything go through a post-mortem no I mean if it's a 90 bar thing where you wipe the station it's a BAU type of activity do we need a post no close we always have to close but the point is when it's appropriate we have this self-improving mechanism over time great now when Kevin and I were developing this we went through of course many different layers of detail the second is just to start to
get the idea how they're interlinked and the types of processes that happen between them you also notice that there are sometimes bars that go all the way across those are activities that occur in all the phases and yep thank you in terms of the different people involved as well as up on the far right you see as well the outcomes in terms of your problem management risk management and so on that might be contacted post this incident we go another layer of detail this is not for us to walk through today and just for the eye candy you know trust me we got all the details there the point being is though we want to
step back now okay so we've established you have a security incident response process rate but now we want to bring to it a bit of a risk perspective and what we need to do though first is we have to count on our organization having undertaken a couple of risk exercises prior hopefully before the incident has occurred one of them is they've developed their own enterprise impact rating table which we'll see in a moment as an example and basically your enterprise risk or one of your organizational groups might have done that and might have applied it in many of their business continuity or disaster recovery planning exercises or through threat risk assessment exercises which were much more in tune with right in the
sense that you've established I guess an apples-to-apples way to look at your business assets and understand how important are they to you the other thing is though out of the TRA is the BIA is and so on that material goes into a database hopefully the CMDB or your risk repository either one that are available to your security incident response and your siem teams that's what's important so that's pre-established upfront and available to your team here's an example potential rating table different organizations use different categories but the common ones are financial reputational legal and operational if you ignore all the other wasn't just focused and operational it's like how bad is it you know aren't we
disrupting our services can we can we live to see another day type of thing but what they do is we've established in this case five levels if you will and you can tell as you read through the different text basically each level it's more and more compromised more and more damaged and what you're looking at in terms of the potential impact that's the impact that the Assessor does prior to an event occurring so basically you know every year they'll redo their be IAS or they'll undertake more threat risk assessments they're establishing a potential impact should something bad happen here's what we would do right now DRM BCP also feed into this this is like your enterprise risk management team
should be having this basic impact table already pre sorted and it's used by all different groups not just security that's the other thing to know as well now here's an example of they've done a little area they've established what are the if you would call it more of the impact type of information about some of your critical business applications and as we run down kind of that middle column you can see the potential impact right going from high down to low you also see on the far right they've looked at also a confidentiality integrity availability aspects the normal kind of things you would come out of tra or a vi8 but that's going to be something
that's available to your team if something occurs now what we're doing we're just gonna take a moment just to kind of sidestep and say okay now let's step back out of the si our mode for a moment and just talk a little bit of both model this wrist model should look familiar it's been around forever it was actually a Canadian invention that went on to become part of NIST and which is now part of ISO but we've modified it a little bit on top you'll see the common things on the right on the right-hand side we have the potential impact of our assets we also have between each of them there are either results in compromise
or whatever but the key components here are we protect things through our safeguards we have assets that have a sensitivity the vulnerabilities that remain even though we put all our energy into creating great safeguards there's still vulnerabilities that occur whether it is within a product when we try to combine products or other or even design within code we have the bad guys outside that's right agents who operate different types of threats scenarios upon us but at the end of the day from a security incident perspective though incidents occur right and what we're going to see in a few minutes we we mentioned saikhan in there which is really if you will in this context a
little bit like likelihood but it's the likelihood of how bad is it going to get next kind of thing and if you will above on the very top we have the SI severity so we know how severe is this incident coming out and then what do we do about it so it's triage to the left we try to do containment actions that we move on to the responses are developed and we move into eradication and recovery and back to should we improve our safeguards so it's a nice model but now it's starting to involve not only your typical security risk but now also your security incident response as well okay what we want to do now is now we're
going to step into okay we're out we're on our si M every day and an adverse security event has occurred Kevin sure whether you've outsourced your talk to like toilet and douche or lirikl or any other organization doesn't really matter actually have to use the rating method that we have it would actually perfectly dovetail right into this and they could if they had available to them and so we would highly recommend that your instant handling talk to your outsourced sock or your in-house talk just to make sure that you standardize but here we're at the phase where we know something's going on we don't we haven't declared anything yet it's an adverse event you don't want to declare
too early the thing about declaring early as soon as you declare an instant in many cases you're now bound by certain regulations to actually disclose that right so you want to be very careful about doing your proper diligence before you actually come to that point so the way we handled that within our framework was we had something called a notional incident security incident so this this icon has basically three phases there's a notional value then there's a declared value and then there's a closing Book value so you have the opportunity to serve have a formal number out there where everyone can latch on to and serve oh okay what condition are we at right now if you remember that movie wargames
how they had you know DEFCON 1 and whatever like I know that's reality but if you think about that that was like the first time that concept was introduced we're sort of introducing saikhan now as serve an incident rating how and how much you want to be paying attention to it at any given time we're gonna jump through because I know we're going a little slow today I will laugh however once we make it to the triage phase what we're gonna do first is we're gonna look at not the potential impact but now we're gonna look at what is the current impact to my financial reputation illegal or my operations so that's where the typical
cert Analyst is going to be working with ops to understand how bad is our operations effect is you know we're 50% down our disruption of this is and so on and so this is actually the current so we've got our potential but now we've got the current impact which is important and now we get to the site con so it's like on really as Kevin was explaining us really about how badly am i compromised right now and this is devoid of who's doing it and how they're doing it this is simply this is where we are and it starts at the bottom which is typically the very low phase is typically used as our way out of the
whole system but if we start at the low you're looking at localized known malware infections or significant vulnerabilities or threat agents identified doesn't mean they're doing anything yet but they've been identified next layer up suspected deliberate attacks or reported by a non trusted source because sometimes we're listening to our agencies and so on some people you trust more than others that's all or there's a widespread known Melissa malware infection going on or confirmed non deliberate attacks as well and up we go the chain to the point of where we get to very high you realize that we have a confirmed security breach or a confirmed deliberate or non deliberate attack with imminent breach if action is
not taken so those are the different kind of levels and that's our in a sense our condition rating that we've provided for our level of compromised it's important to note that one of the things we did different than traditional frameworks is this isn't threat based this is impact based typically next you'd be moving into a validation phase where you've got those two pieces of information and what we're going to do next though is we're going to look at this how do we bring it all together and sometimes the best thing to do is you you realize we started with we have this database of potential impacts we have a psych on so we've now established that
our current level of compromise is at level 1 2 3 4 5 and we also know what our current impact that we're having as a result of this those basic factors come into play into this matrix that we've created I know it's got a lot of colors but it actually works quite easily in a sense the first left-hand column really is the assessed potential impact if you follow across the next column is the actual current impact that you're experiencing and the third one is simply what is your level of compromised at the moment and by just falling across the lines you arrive at a value and within the cell depending upon which saikhan value you arrive at you end up
with a number that number is your security si severity level okay and it's just as easy as that for the people to walk through as soon as they have those three pieces of information you come out and you have an assigned si severity level okay with that in hand and you've established that you are dealing with the security incident you move quickly into the mobilization phase and that's really where you start to make use of that si severity level to help you make decisions very fast because in these times you can't sit down and go like who to go who should you call Kevin I'm not sure you need a plan and the plan is
driven now by this si severity level and the first thing that you're going to do is you're going to establish based on it what is the right type of response to take and again we have five levels pretty much all the ratings have the five levels starting with again we skip five because that's our way out of the loop but be a you response it's just our daily compromise you know of email systems or whatever timely response to priority response to immediate and continuous response and each of the levels is defined and it in sense justifies what type of energy ie money people etc should be put against in the other factor that the SI severity
level also drives out are your types of notifications to which distribution lists and how often often you know again in the the fog of war you're all trying to fix the problem but we forget we got to talk to ops we got to talk to the business we got to talk to as a certain point auditors and outside so again this really is helping us that one severity level is telling us exactly what to do next exactly it's formulaic now it takes discretionary that hands of like level one analysts who are dealing with this or stuff there's no discretion anymore per se it basically gives some parameters within which they have to make decisions once those things are
done it becomes formulaic where now they have an exact understanding of how they reach a certain severity level and it's standardized it's repeatable and one of the other factors that we mentioned earlier on was the severity level of your incident also determines what level of seniority is required within your certain team so we again we have yet another matrix where we actually broke down the different types of roles and these are virtual rules so we work with the idea of a virtual cert team there's it's basically driven out like when you need it and there's certain people have been trained and so on meda teams exactly and so for each of the phases once you've established your level of
security incident severity again this matrix tells you that I'm sorry but Bob is too junior to be put in charge of this we need this person and so on and it just goes up Chane we also have a distribution list which is driven out by the same approach again your security incident severity level means that you know for this one we don't need to bother to see so but at a certain point you're going to have to and also business owners and so on so again the severity level is now driving all these decisions so you are acting on impact decisions which is really helping you to come around to risk and just to close the loop on when you're talking
about level fives are where the loop sometimes something becomes non-material or was a false positive the reason we keep that there is for tracking purposes for metrics and measures because if you're getting your sock feeding you a bunch of false positives you want a way of tracking that as well right so it's non-material to the actual incident but you still want to know those metrics sure yep and the final kicker to this is you know just to bring it all together and show those first different diagrams but we knew what the inputs were potential impact saikhan and the current impact we know how we came up with the SI severity level and the outcome of it is that
drives immediately who are we going to assign to this cert what level of responsiveness must we enact upon right away what types of notification schedules do we have to do first for the initial as well as for follow-up and also who has to be notified okay and so if you will that kind of I think we made it within 20 minutes we did pretty good now but we'd like to ask if there's any questions and of course we have lots of eye candy but let me open the core and thank you again for your patience this afternoon [Applause]
the trick is the idea of introducing if you a lot of those tables and matrices was actually to make it very easy for the cert team who doesn't operate every day as a cert team to actually step right in and go okay I need three things going in you know my potential my currents and my saikhan they turn to the matrix and is okay here's what I'm going to do next I notify these people with this schedule I bring on these people to the cert etc so it's purpose was actually to facilitate versus making it too complex the complexity is behind how we set it up but actually how it runs with the cert team is actually very
straightforward and there's some operational pieces that go to that that we don't show is like pre-templated to communications and stuff like that which support these interactions so this kind of gives you the framework but it's not necessarily the operationalization of it and we've got time for one more question
the idea of this was that it could be applied to basically any cert or any si our perspective and it what it does is it bridges between the geeky guys who are over here doing security threat risk assessments but who don't actually do operations versus the guys over here who are in the trenches every day monitoring the assim and then oh my god alert and DEFCON comes up and out they come so this is actually meant to apply over anybody's eg RC or DRC processes or cert processes it's a standalone process that has a lot of process hubs sorts runs in parallel with everything else and what you have are these interactions between these different teams so it's kind of
the glue that binds but thank you very much [Applause]





