Block Cipher Modes of Operation - Theory and Practice
Show transcript [en]
everybody we're gonna get started here let me turn off this music hope you enjoyed some Jack Johnson music here so hi everybody my name is John Z Ola thanks for coming to Steel City InfoSec that is where you are if that's not where you expected to be there's the door and there's the you know the ally 26 offices are down that way again like I said my name is John viola I run this group in coastal city in Busiek I've had a lot of great help lately so I'm gonna give a big THANK YOU to Kyle and Joe here raise your hands those guys are have been assisting me yep I've been a huge hand a huge help to
me recently they stepped up and helped and then another thank you - this unsung hero back here Brian gray he's been setting up all of these recordings and makes this stuff available online so big thank you to him as well so we're gonna get started here in a minute I just had a couple a couple of things to cover at the beginning so if you guys are looking for the bathrooms go out the store take an immediate left and kind of go down the hallway and then some of these rooms are down that way and and you know we've got this area until I think 8:30 or 9 o'clock tonight so feel free to hang
around afterwards and talk you know I'm sure Jim will be around for a little bit the chat and I definitely will be so so one other thing I want to cover is oh that today is a Wednesday for new people that might be that surprising but for people who have been around to the group for a long time this group is always met on the second Thursday of the night since I started it in 2012 this is really one of the first non Thursdays that we're doing and I did a poll a little while back and people kind of liked North Shore area and they're like Thursday and Oakland and they liked Thursdays and Wednesdays so I'm mixing
up a little bit and doing the Wednesday on the North Shore as opposed to a Thursday or Thursday in Oakland so if this time works for you you know that's great let me know that on the meetup if it if it was really inconvenient and you would prefer a Thursday but you came waise please let me know that as as well or if you're watching online and on the recording you know please let me know if if Thursday's are better than Wednesday's if you know Oakland versus North Shore and Pittsburgh what's what's better what's more convenient because this group is meant to be you know whatever's easiest for the people that would like to attend it so I wanted to
make sure I get that and then I want to give a shout out also to this space so this is a co-working space and they're giving us this area completely for free out of the goodness of their heart and they they're really they really they really seem to have a good thing going here if you haven't taken a tour through the area you know there's some co-working areas and some offices and they do a lot of you know month based no lease engagements here so you can if you if you have a small company or if you're just looking for a place to work everyone smile you could come here Natalie will be sitting out kind of
towards the front area in the in the lobby if you guys are interested in learning any more about this area but a big thank you to them for providing this on two percent free of cost and then the last thing that I want to mention is about sponsors so we have a sponsor for the first quarter but we don't have a sponsor for the second quarter or for the third quarter so if any of you guys were companies that are in any way related to InfoSec or want a sponsor this group let them know that I have some sponsorship levels and or you know if you're responsible for that feel free to reach out on Meetup and we can you
know I can I can give you essentially the sponsorship information what it what it costs to sponsor one event or three events or even a sponsor whole year but that being said tonight's sponsor is C so C so is great because it's a company that I own yeah it's this o is a small information security consulting company that myself and some others Joe in the back there co-founded recently and so we're doing information security consulting in the Pittsburgh area in other ways so if you guys have anything that you'd like to talk about along those lines feel free to reach out to myself or Joe and big thank you to C so for sponsoring this event at the last
minute it's a I worked really hard to convince them that they should sponsor this event but I was able to work it out and so that being said I'm gonna pay hand it over to Jim so Jim is gonna be the presenter for tonight Jim clan taenia is how you say his last name took me a little bit of practicing but he is a developer and he's interested in app sack and various other things crypto being one of them and that's we're gonna be talking about tonight so let's give him a warm welcome [Applause] thanks a lot everyone it really appreciate all coming out tonight I apologize we'll set more soft-spoken than usual I'm a little under the weather but
better got it cool and thanks again to crown John for giving me this opportunity who they appreciate that so I'm Jim I'm a UI designer and a web developer and what business does that give me telling any of you about cryptography well that's a good question hope you get something out of this I hope people get something out of this who really don't know much about cryptography and if I'm lucky the more expert types in the audience might get something else out of it too you'll see you can tell me afterwards how good of a job I did so when we're talking about block ciphers we're talking about a block we're talking about a fixed chunk
of data usually 16 bytes or 128 bits and they can come and other flavors but that's that's the flavor that I'm going to be talking about smoothing in that context I mean a cipher block cipher just consists of an encryption algorithm and a decryption algorithm and you can represent that most simply like this where we get we get see bypassing okay a key ek and planes xp into the encryption algorithm and then we just invert that to decrypt that's in the same key and the ciphertext back and that's pretty basic hope that all makes sense at this point now one note before I move on you'll grab my water it's important to keep in mind there's an ocean security goal
called indistinguishability and that is the output of an encryption algorithm should be indistinguishable from pseudo-random output and if it's not we've fallen short and there's some discernible pattern in that output that could lead to totally revealing the plaintext or revealing something about the plaintext and we don't want that
so then when we talk about mode of operation we're now talking about what are we doing we're encrypting or decrypting several blocks and we're not I'm not just talking about encryption and decryption in general but what is happening on the block level to each block as the encryption decryption is happening and this is crucial this makes or breaks the entire set up the entire crypto system even if the cipher is itself secure if the mode is not selected well then you're all screwed so start with the humble almost modeless mode electronic codebook well try to code book mode is described by the niste recommendation for block cipher modes of operation from 2001 it's a pretty dry
document I hope you don't have to read it but it has this to say about it the electronic codebook mode is a confidentiality mode the features for a given key the assignment of a fixed ciphertext block to each plaintext block and now against the assignment of code words in the code book so first of all they mentioned in confidentiality and that's obviously security goal and whether or not what trying to code book mode provides confidentiality is questionable at best but another I looked more into what they meant by codebook exactly and it reminiscent of Cold War spy stuff really like I was reading about a Russian Russian codebook that was found and it's just you're
going to have some fixed short phrase that is a stand-in for some longer set of instructions and this is what it looks like it's very basic and as far as the formula goes it's not a big jump from how you would generally present encryption except now we're talking about for some ciphertext block CI we're going to pass in some corresponding plaintext block P I into the algorithm to get that in decryption what is the opposite there so then the problem is we're always going to get the same output no matter how many times we we encrypt with this and we've given the same key in the same plaintext the ciphertext is going to look exactly the same and the
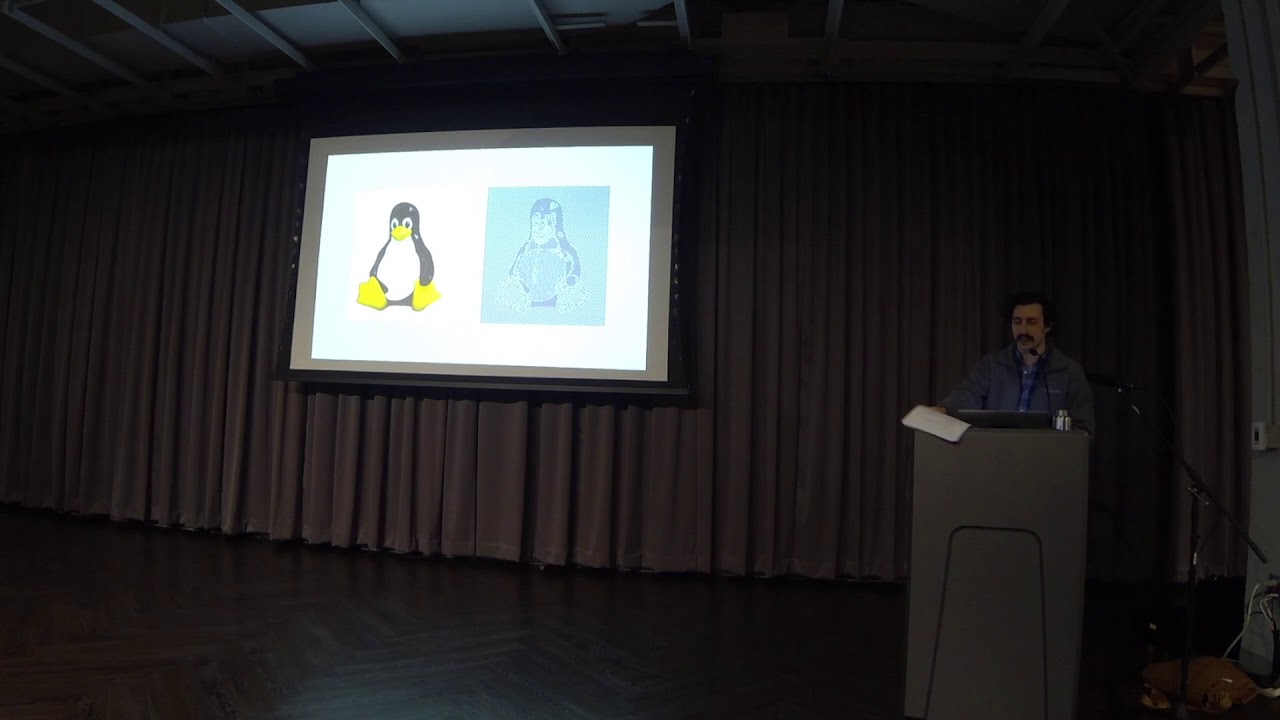
most famous way of explaining the problem here is the famous ECB penguin which some of you may have seen before and what's what's happening here is the penguin on the right is the ECB encrypted version of the penguin on the Left it's encrypted but every every similar and same pixel value is encrypted to the same some other similar pixel value and so there's clearly a pattern there this examples may be a little a little tired so I decided well maybe I can try this try one of my own here and so I tried my earn coat the Pittsburg favorite now what's interesting is the results are not the same if you look really closely you still get you know
where there's this white area and the tag you get you've got some similarly encrypted pixels there but the important thing is not the things as they appear to us because that's that's a kind of like a common sense world view and if we're going to have any kind of scientific approach to it you could look at the values as they relate to each other and rest assured the pixel values on the right are not in any way devoid of a pattern there is a pattern there it's just not readily apparent and so then again okay what's the problem here I can't see Myron cope I can see the penguin you know it's busy why don't we all use ECB mode on a daily
basis that might be best explained through a particular chosen plaintext attack [Music] now there's imagine there's some some old aging box somewhere that for some reason it's still encrypting with ECB against everyone's best interest so you know let's say I as an attacker I can feed it some kind of input yes and it gives me back these three ciphertext blocks so again the formula here for some ciphertext block see I passing in the plaintext and the key and equipping it that way so that's what's happening behind the scenes there but more specifically we also know that the plaintext is the concatenation of s which is our input and that's prime which is some unknown input and well that's what we
really like to get as the juicy stuff so that's prime is provided by the server for that a terrible terrible box out there in space so then what if we fashioned a block entirely of null bytes but we we left it one byte short what we can say about this first cipher text block is then that so we know we know the plaintext is some combination of what we're giving it and what the server is sticking in there and more specifically the first the first plaintext block is going to be the 0 through the 14th byte of s and the 0 of byte the very first byte of s prime so now we have a record in in this
output of what it looks like when we include the very first byte of s prime some of that secret information again at first might not seem like a big deal but then at that point you you fill in this byte with all 256 possible by values and you cycle through them and you see what the what the server gives you back and whenever you get back this same block value again you know that you know whatever ASCII character is behind that that corresponding value you've hit on the actual decrypted first bite of that plaintext and that's very bad and you can very easily proceed throughout the rest of the block and other blocks in the same way and you've totally broken
it and we didn't need to know the key so ECB mode don't use it or anything just don't use it I won't make many recommendations tonight because a lot of expert but I can say that for for sure
alright so that brings us to cipher block chaining mode which here's an attempt to not just let each block be some you know stamped out deterministic output of the same the same function over and over again always revealing something about the plaintext but something some way of intertwining the blocks so that those patterns are hopefully totally eliminated this was proposed in 1978 by air--so Myers Smith and Tuchman IBM owns the patent but the title was originally a message verification and transmission error detection by block chaining and so they were concerned with increasingly complex networks with detecting errors and so there there was there was there was more talk about error propagation before authenticated ciphers came into play and
that's the idea that you know when there's an error how noticeable is it is it is it going to propagate to just one block is it going to propagate to all the blocks let's look though at what this actually does so each plaintext block is force first ex-ored over the previous ciphertext block before being encrypted and in the case of the first very first plaintext block well there is no previous ciphertext block there is this IV initialization vector it's very important that that does not get reused
now to give you an example of of the importance of the initialization vector [Music] if you encrypt the same message oh yeah
clever we'll see that okay so if you if we encrypt the same message that the same key but provide a different initialization vector or even off just by one byte you end up with these these two blocks being entirely different and that's well that's the success of cipher block chaining mode is that it does away with that determinism of ECB mode
and then we represent this this way with instead of his passing and the plaintext we passing the result of things or is the some plain text block PII against the previous ciphertext block CI minus 1 so this against that and then for decryption we're passing in the ciphertext directly into the decryption algorithm and then only then is it XOR it against the previous ciphertext block to get us our plaintext and this is this is an important part we're going to come back to this but at this point it's it's the the data is decrypted but it's not readable because the crucial part of the process is that XOR and so but you'll still see where this comes up again and
so again we're out that our plaintext we [Music] end up passing in ciphertext block into the decryption algorithm and then eggs with that against the previous ciphertext block one interesting note is that this the decryption here is parallelizable meaning you can perform or at least the the first stage of it is you can do all the decryption first and then exhort afterwards but I'm going to explain that better in a different context I promise so then what's the problem with CBC mode the error propagation which out here I'll explain that more - let's say there's an error in this byte in this last position upon decryption this entire block is going to be scrambled but it's corresponding by
position will in the next block and you end up opening yourself up to bid flippin attacks to where you can you can if you have some kind of insight into what the plaintext might be or what you might want it to be as an attacker you can alter this by in such a way to in the classic example is oh I actually want to withdraw a million dollars that I don't have so I'm gonna add some extra zeroes you know that kind of thing now is a good time to bring up padding know the pkcs number seven padding scheme and this scheme states that if we've got some one or more bytes short in our last block we can't feed
that into the encryption algorithm because it wants a fixed size block it's just going to throw an error it's not going to work and so for all over many bytes we need that's the value of the byte and so we need one byte at the end and we're going to get as its as one byte of a value one and likewise if we needed to then we would then Pat it with two bytes of value to one thing I initially overlooked when I was looking into padding and CBC mode was that the when you have when you don't have a padding issue technically you still need to provide a last block entirely padded with 16 in order to make it valid in
that scheme and so this padding ends up being an attack vector for the padding Oracle attack originally pioneered by Serge Bowden a in this paper security flaws in juice by CVC patting applications to SSL IPSec WLS dot-dot-dot in 2002 people kind of forgot about it for a while seemingly because by the time 2010 rolled around Ruby on Rails and asp.net were using CBC mode and were vulnerable to padding Oracle attacks and so Juliano reso and tied Wang published practical padding Oracle attacks in that year and that's when it finally got some attention and people started focusing on it and eventually moving away from CBC mode probably as a result of that it's also worth mentioning that tied along
was also co-author of the poodle attack against SSL and TLS which itself involved another padding Oracle and there's a there's a great Moxie Marlinspike blog post about about padding Oracle's in part and how they just keep seem to keep coming up and coming up and you fix one and then another one is enabled and it's it's it'll come up later when I started talking about the cryptographic doom principle as he calls it and so then what it is a padding Oracle attack one thing is we would consider this a chosen cipher text attack because the attacker can choose what cipher text to feed into the box and get back some kind of result and so let's say we've gotten a hold of
some ciphertext blocks here we feed it into the Oracle and it's going to check the padding and tell us whether it was valid or not actually were you know in in a real world example from back in the day it would probably be you're only gonna get a code if it's invalid if I'm understanding that correctly but for the sake of teaching I'm going to have two strings here that say valid and invalid so then behind the scenes again use our CBC formula get a pint X block we're ignoring the corresponding ciphertext block against the previous ciphertext block and then that that plaintext is going into some some padding validation function and returning valid or invalid so then
here's where things get a little interesting if we deliberately alter the last byte of the first block which is in this case the initialization vector so this is this is going to be sent in the clear anyway it doesn't contain anything of any value it's just going to be a random value meant for you know for lack of a better way of putting propagating randomness throughout the next blocks and getting rid of that determinism we saw with ECB and so if we if we if we changed that last byte again here's here's our formula and more specifically we're focusing on getting the you know the first plant X block index one rather not the zero and so we're going to be
ignoring the result of decrypting the first ciphertext block against the previous ciphertext block and then more specifically than that if we're looking at just the fifteenth index 15 of each of these values we know what index 15 is of this because we decided that that's not a mystery now let's say we're cycling through this and we're trying different values for that last one and for the sake of explanation let's say we got lucky with zero and we got valid padding what we also know then is that the last byte of that first plaintext block is equal to one that's that's the so that the valid padding message is telling us and because XOR is a linear
operation we can rearrange the operands and we then know that that this here is just a matter of X or in these two values and so once again without a key we've managed to discern what what the data is coming out of the decryption function and all that's left to do there we've since we've altered this first ciphertext block but we have the original if we weren't sloppy and lost it so it's just a matter of ignoring this value against the original byte value and we have again the original plaintext and so and this is a very fast attack to because you you make you know 256 guesses at most per byte and so it's
it's not it's actually faster than I won't be able to explain why but it's faster than attacking ECB and so this got its got CBC into a little a lot of hot water and so people started moving this is very incomplete history but started moving towards stream ciphers and reconsider extreme ciphers again even and they had they had a bad rap for other reasons but well this is not a talk on stream ciphers so what's the deal Jim well counter mode is still a block cipher but it they really wants to be a stream cipher I'll explain why now the earliest reference to a counter though knock counter mode specifically that I could find was in paper by Diffie and Hellman
in 1979 privacy and authentication an introduction to cryptography everybody says kalanor mode started there and I believe them because I have not read the entire paper but it never was reference to a counter but not counter mode and so I think there's a lot of history crypto history that is just not on the internet so that's that's for someone else to figure out but counter mode being modeled after a stream cipher ends up taking instead of encrypting the plaintext it didn't crypts of a key stream and creates this key stream and the key stream is based on concatenations of a nonce which is literally number only used once you can liken that to the initialization vector
of CBC mode concatenation of that with a counter that increments for every block so that gets encrypted to get some secret key and then call the actual encryption is just a matter of exhorting the plaintext against the key stream and so it's it's a very it's very fast and then we can just we can express it this way if some ciphertext block CI we we XOR the corresponding plaintext block P I against the result of passing in the nonce and counter concatenation into the encryption algorithm and decryption is very very similar you just switch the plaintext and the ciphertext there even and here's here's one good thing about counter mode is that it doesn't need the
D doesn't actually need the decryption algorithm for say AES it's it's only ever encrypting the key stream and so that's one less thing to implement as far as getting things wrong which no one wants to do with crypto [Music] so that's one benefit of using this also no padding if we found our last block is short it doesn't matter because the the encryption algorithm is still always taking a fixed block 16 bytes and then the we just we were just X or whatever bytes there are here against however many we need so we avoid the whole whole class of attacks that would involve padding Oracle's also a benefit this is fully parallelizable so that meaning we
can we can process each block in parallel and we don't have to wait for any other block to finish before continuing so that's a performance advantage there also pre-processing let's say I have as a recipient I've received the nonce but I have not received the rest of the ciphertext I can go ahead and compute the entire key stream and and get that ready and so there's an advantage there as well [Music] problem here is whenever the nonce gets reused the whole thing falls apart and what that looks like is
these are multiple cipher texts encrypted against the same key stream and so all these values here and you can see you make a little smaller so the columns line up if you look check check check this is that okay in the first column you can see you can see duplicate values and even if you didn't know for a fact that these were all cryptid against the same key stream that should be that's a big red flag there so you know we got 35 35 we got 39 and 49 pop up again and so you can start to pick this apart and and take guesses about you know what letters these might be and you can you can pick
this whole thing apart manually like that and it's not it's not difficult does take a while but it's just trial and error and you know you guess the 49 might be a and so you you find out you know what you have to XOR 49 against to get a an ASCII and then that's your key stream but you test that you can you see in that first position but you know the first byte of every ciphertext there like if that key stream by checks out if you're getting ASCII characters and and you know it's English then you're on the right track and you just continue from there that's that's totally doable the better way of doing it is attacking it
statistically and how you do that is you would you would take the shortest one and truncate them all down to that size so you know say this one here and you make a block of the first bite of every block and you make a block of the second bite of every block and and so you end up with all these blocks that are all encrypted against the same keystream character and then for each one you try exhorting it against all two and next with them against blocks that consist of entirely of all the same bite and you do this with all 256 possible white values and you and you record what comes out of it
and on the most basic level if you get you can count spaces if you're getting spaces chances are you've got the keystream bite and so you're actually going to recover the keystream with this if the keystream gets reused you can recover the keystream that's very bad it's not you've got the content and the key so it's it's bad but it's also fun to do it's a lot of fun so anyway that's the that's counter mode that's and that the danger of reusing the nonce
does anyone have any questions so far yes back to the yeah do you think that that would have had a different result if you like your attempt yeah do you think if it was like a saint greyscale or 256 bits I had considered that because my the first time I tried to encrypt Myron cope it was it was a very low quality image and I got that I got very nondescript lose all doubt of it so I thought I better try a high-res image and I again got a nondescript result so I'm not sure what the trick is but does that answer your question though okay all right ask me ask me more later if if you think of it
all right so then that leaves us with this Galois counter mode and here's where we step into authenticated ciphers this was named for every scale wha-hoo was a 19th century mathematician who died when he was 20 but still managed to do a lot with abstract algebra which I know some of you know a lot about but I really don't understand but anybody who can do a lot before they're 20 they can just die and then leave behind this magical legacy is pretty impressive this was designed Galois counter mode was designed by John Vega and David a McGrew as an improvement to carter-wegman counter mode which is based on the carter-wegman mac function message authentication code that's that's a
interesting set up that I would not be able to explain because I understand enough but I would highly recommend it to anybody who finds this stuff interesting so then when we're talking about an authenticated cipher we're talking about something that returns an authentication tag along with the cipher text so that you know our these packets weren't tampered with and there wasn't any error along the way thanks Jason and so then as far as representing authenticated encryption they would return a cipher text and tag pair instead of just the ciphertext and life lives in order to decrypt we need to provide the cipher text in the tag to get our plaintext the basic security requirement here is that
it should be impossible to forge a cipher text and tag pair that this function will except and this setup is it's inherently stronger than a basic cypher for that reason because you can't you can't just keep querying it with random malformed cipher texts like we saw with the padding Oracle attack it's so it wipes out certain classes of attacks entirely well but then when we're talking about this authenticated ciphers have the authentication layer and the encryption layer all wrapped up into one in a convenient way but it's worth talking about some other to shine light on Galois countermoves but it's worth talking about some other ways of devising it for sure ciphers that don't actually include authentication and for
anyone who doesn't know Mac is message authentication code it's also the function that generates the message authentication code I don't know why we we use this term but it's it's confusing like that and so there's there's this arrangement which where the ciphertext comes out like usual but then the the authentication tag is computed from the plaintext and then because the security goal of a Mac is to make tags unforgeable and not necessarily to achieve pseudo-random output devoid of pattern then the tag computed from plaintext could reveal something about the plaintext you can avoid it if you use a strong-enough Mac Mac algorithm like H Mac sha-256 but there is that possibility there if you're not
careful there is another set up Mac then encrypt which is better as far as possible exposure of plaintext through the tag but the ciphertext must be decrypted before you can compute the Mac so you could be exposing the recipient could be exposed to corrupt data and then the ideal scenario is where the tag is computed directly from the ciphertext there's nothing you have to do as far as some additional cryptographic operation in order to compute that and that is what Moxie Marlinspike talks about when he mentions the the cryptographic doom principle and that is the doom principle is if you have to do any additional cryptographic operation just in order to compute the Mac something bad is going
to happen and it's not like he lays out this proof of it but he gives all these examples and you're very convinced of it by the end I'm very very much recommend that blog post it's worth noting that this is the approach that Galois counter mode uses more or less even though this is again this is this is when I hope you will explain it any more than this but this is an odd marriage of a cipher and authentication kind of like you know bolting them together versus having them all rolled up into one well before I actually show you the diagram for GCM it's when we there are times when often times when we're going to want to just
authenticate some data and not encrypt it for example a packet header you don't want to encrypt that these two get to where it's going and we call that associated data and so then we get this love it's as cat I'm sorry when we get the cipher text and The Associated data some-some packet header and the authentication tag by passing in key the plaintext in the Associated data and then we get we get back our plain text and our packet header bypassing all those in again and if the tag doesn't compute we're not getting that back the benefits of authentication and so here is there are two basic layers here on this top layer is essentially counter mode it
does specify in 96 bit knots and so I have not seen any implementations of counter mode that that had that but certainly I don't see why you couldn't use that this is getting into the weeds a bit but so I find it interesting and then so we this is this is all counter mode up here and then once we get to the authentication part we they were passing in our Associated data a into the G hash function which I'll explain what that H is there this is polynomial multiplication who knows what that is polynomial multiplication even Matt marks doesn't know you know I imagine you know if anyone knew okay you do okay hey I feel
a little better now because I really don't know what it is but I know that it's it's not easy for people to do but there are specialized machine code instructions for that it's a C CL malts careless multiple multiple occasion and so that's what's happening is there's this there's this multiplication happening of that and there's X word against the ciphertext multiply it again and and so on and then finally the length of the of the packet header and the ciphertext get concatenated and thrown in there and then multiplied again finally the 0th counter block is is getting passed in here notice the starts of one and not zero I really wish I understood more about G hash but I can't
say this much the H is is a derived key and you won't always see this in depictions of GCM but what this is is the we derive this hash miss hash key by encrypting an all-zero and out block and so if this is a yes we're almost treating AES here like a hash function which is there's got to be one way so that it can't be forged so that this is a security benefit because if this this key is compromised then you still got this key intact so then like where this is this is widely in use where does this fall short well it's it's still not misuse resistant in the same way as counter mode which is if you reuse a
nonce then you've got the same situation all over again because we are dealing with more implementation here it's difficult to get it all right and even the developers of OpenSSL managed to get it wrong and they'll out a bug to get into the code that allow for forging max and if that's not good either and there are no slouches so you know this is something to contend with as far as performance goes this is not going to be as fast as counter mode because the GI function is slower than encrypting against the key stream so it's only as fast as as G hash can do its computation it's worth noting that there's a there's a faster and actually there's a mode
that predates this an authenticated cipher called offset codebook mode it has not seen the same one of the options GCM because of its license but it's available for free if you for non-commercial purposes that's all I've got hope I didn't bore you anybody have any questions yes
[Music]
has claimed this and actually those encrypted Texas difficulty so they came reverse engineering that's a good question so let me find that slide again this is the one you're talking about so this this might be when I was first writing the code that would allow for an attack like this I started to think to myself the same thing like what what is this scenario and this could be this could be a cookie and so if you know this could be session data so this is that's that's where it starts to make sense and I should have mentioned that but outside of that context it's like I mean I've been I've been you know reading so much cryptography lately out
of a book that to go of course is this is a scenario but you know I have to keep track of like what is this in the real world that's that's a good question anybody else yes yes I should have been more clear about that that's the same nonce value yeah and that is that's an interesting thing about in in the arguments made to the NA n is T for counter mode I forget who was making the argument but the there were critics saying well look we have an essential component of this crypto system is you know deterministic input into the encryption algorithm like doesn't this spell trouble but this it's more about the with the
strength of the cipher you're using and for AES that's that's no issue it hasn't been broken and it might not ever be broken and so as long as the key is secret you know a one bit change to anything here totally changes the the outcome of what comes out of this encryption algorithm so it is actually safe to go ahead and feed the same knots and a deterministic counter in there as long as the key is secret
that's your question yeah
hmm there might be a word like that paralyzed the phone to the noise that we're not the best
Thanks that's it I would look at that anybody else yes oh I do not yeah but I should say that this is not part of my job so I was prepared to fail spectacularly at this talk and then I I you know I still may have I might be deluding myself
this is an efficient way of computing a hash it's one little side note it's not as far as like indistinguishability goes and the the output of that being not revealing anything about what you put into it it doesn't meet that standard I found out but it's it's efficient and it still still secure as far as computing authentication tags I I answered your question as best I could matter
a lot more issues there is ok so there there are elements of what Galois field feel in that in the math there and I am totally abstaining from attempting to talk about any of that there there there Layton's and they're waiting for you thanks again everyone
[Applause]





