Machine Identity & Attack Path: The Danger of Misconfigurations
Show original YouTube description
Show transcript [en]
Welcome everybody to our last talk of the day for Passwords Con, but certainly not the least. Just by way of reminder, if you are uh first time attending uh a talk with us today, uh just reminder on the on cell phone usage, um please don't take any photos of the attendees around you without their consent. Filipe has said you can take pictures of him and or his slides. So, you're welcome to do that. There's no need to take any video because uh it's being streamed and recorded. So, no need to do that. And please put your phones on silent um so that it doesn't interfere with anybody else. Again, a quick thank to us to our
sponsors, our diamond sponsors, Prisma Cloud and Vanter, and our gold sponsors Drop Zone AI and Project Circuit Breaker. and then all the other sponsors and volunteers as well that made this conference possible for us including yourselves for being here um that make bides enjoyable for everybody to learn and to have fun. So we're going to welcome uh Filipe um from Brazil. So I will try and say Filipe. >> Yeah. >> Right. Good. Right. So, we're going to hand over to Filipe who's going to do machine identity and attack path, the danger of misisconfigurations, and then afterwards there'll be some uh Q&A as well. So, let's hand over to Filipe. Okay, thank you. Thank you. Can you hear
me good? Right, that's cool. Your Portuguese is very cool. And uh yeah, thank you so much for being here. Mainly the last talk. Are you tired? I'm tired. >> Come on, sir. Who's tired here? Yeah, everyone is tired. Okay, thank you for being here by the way. And uh yeah, so let's talk about our main topic. Um actually our conversation will be divided in two parts. The first part is more [ __ ] part. The theoric part is kind of [ __ ] I know that but it's necessary. But the second part is more sexy or let's say the more technical part. So please stay until the end because in the middle I'll share more of the funny
things and more sexy party. So by the way who here work with the you know AWS just to okay who works with Azure who work with um Google yeah or OCI who work with nothing because someone worth nothing. Okay, cool. So, basically I'm a head of identity thread labs and global product advocate at Seura and I'm responsible for doing investigations uh about the threads understand how the thread works and mainly how the attackers are you know investigation the attackers are creating new techniques and explore identities actually and machine identities. This is a kind of type of name by Gartner. Let's say [ __ ] Gartner. I can say [ __ ] Gartner. It's not polite, right? Sorry guys. This is
the community event. Okay. Anyway, so I'm part of the red team village, director of the team, responsible for sponsors and I'm organizer besides Porto in Portugal. By the way, I'm living Portugal right now. Actually 50% of my time I live in Portugal and another 50% I living out of Dallas here in US. So, but I'm one of the organizers uh at Besides Porto. So, I know how this event works. So, I'm found I'm founder of this community called the red team communities. This community is focused on red team in Brazil. Basically, I'm Brazilian as he said and uh but I'm living Portugal. We talk Portuguese and I'm a part of the high cyers. Basically, hiis or races or we can it's a kind of
root. It means root. Basically, the idea is to spread the message and to helping people to get inside of the you know cyber security stuff. This created for the Spanish people and Portuguese people as well to helping you know to growing and to get inside of the cyber security. That's uh if you see I just received in salary for the first company here and the other is no proof it initiatives and the community events let's say. Okay, cool. By the way, first question is just who was last year here? Anyone is who last year watching my talk here? Cool. This will be yous here last year. >> I think so. >> Yeah. Okay. I will bring some things to
you and you watching my talk at Hackspace Con right at Florida. Okay. Cool. So, first of all, my company it's called it Seura. It means secure in in Portuguese language. We responsible for providing solutions for identity and mainly pen solution when I mean pen is privilege access management just to let you know. So we are is a Brazilian company but we are have an office here in US and we are growing. Okay let's talk about our main topic. So what is machine identity? just to putting every people on the same page. Basically, machine identifers this unique identity because we are using two to use on the user and password, right? But nowadays we need to have the let's say um not
more password. So probably you heard about passwordless technology, right? And sometimes when you have a two different applications in the cloud for example or even on primes, you don't need to have the user password. You can use you should use in service account, right? is more best practice to integrate those type of things and you talk about this is about machine identity or no h or human or no human identity right because you have a permission above those identities and need to set those permissions between those different applications to talk between applications one and application two right you don't need to have the user like Philipp user or password because if I leave the company the
application is going down right because should be based on the service account. That's cool. So basically machine ident refers to that. Okay. So about secrets, tokens or mainly now we are involved with the docker containers you know like the kubernates and many things about that. So we talk about this machine identity. When you talk about the human identity we are talking about the user and based on user password and many things you know about that. Okay. So basically our vision about machine identity just to understand everything is about machine identity. How you manage the government's privilege account secrets cloudy entitlements it's quite new another [ __ ] word of Gartner anyways okay and access management certification lifetime
identity poster manager of the famous ITDR another [ __ ] word I'm not good in this to be polite anyway identity threat detection response is ITR and you have like um many others you know security posture but I know that's necessary for organizations for to manage cloud providers and so on and so forth. Okay. So that's the vision about machine identity how you can manage this first is when you look into the kind of solutions. So we are like let's say I'm supposing that you work with the you on your company you are analyst or you are like a principal you are a staff whatever the position when you need to look into this kind of
solution you need to figure what is the best solution that you should using for discovering for this identities let's say the machine identity server containers pipeline many cloud workloads when you need to you need to look into the governance let's say the best practice to enforce the policy or even have a kind of control or the ownership. The other one is to automate it again to thinking about just in time access because I published it I think one week ago one the big attack that happened in financial sector in Brazil I don't know if you have opportunity to read but you can came to my social medias after this talk you can see this completely article
that I investigate and this attack is is happened because the company that suffered this attack didn't have the just in time access enabled because the attacker happened during the night like happened to the started at 4:00 a.m. in the morning. So you know the attacker they didn't many fraudulent transactions during the morning. So it starting 400 p.m. actually start before like 2 3 p.m. So like if the company had the just in time you access to block at this access or this transactions during the night or in the morning at let's say the company could block at this attack. So when you think about the identity access management you need to look into this type of things. Okay. And to be secure
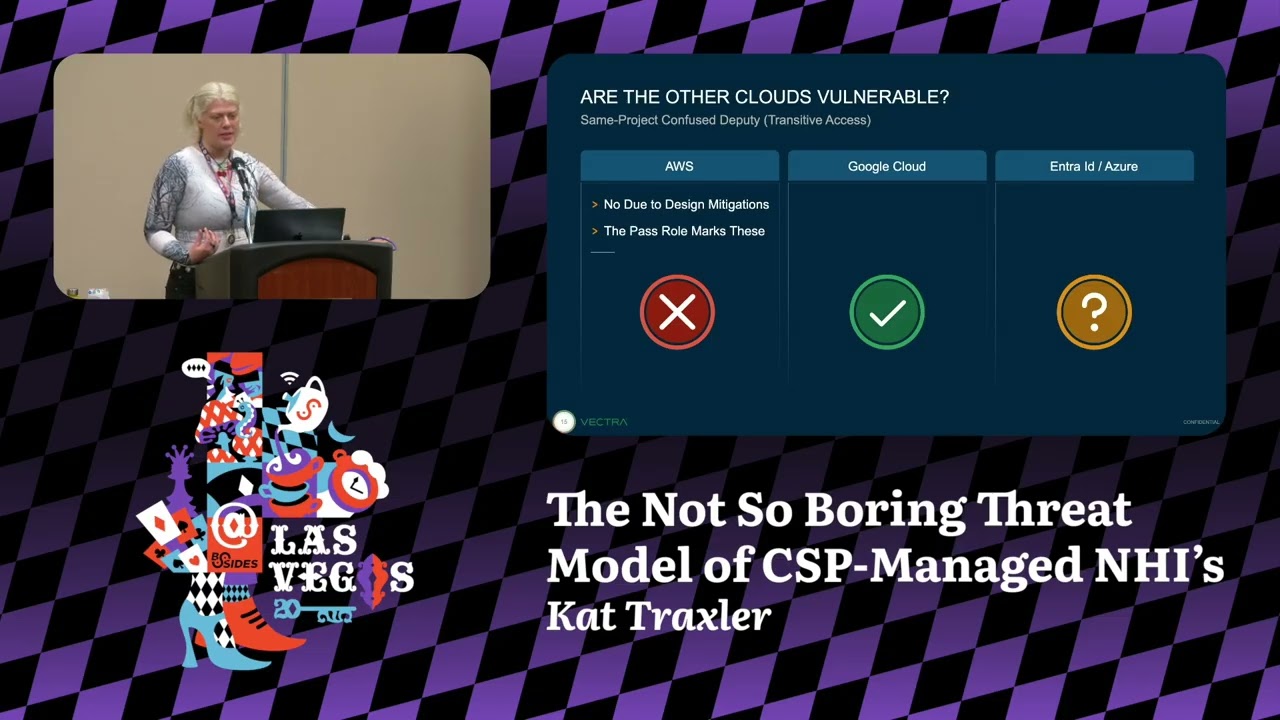
like looking or working with this kind of concept called the list privilege. Okay. Just to understand what is machine identity. Okay. So talking about cloud. So if you think about offensive perspective in the past when you talk about on primes we have the high value target. So we look into the active directory and active directory had the administrator guys. Okay. So how do you work in the cloud or how do you manage those type of things? So high value targets comes to the military is the terminology here from US. So to refers to the person or the resource that the enemy commanders requires to complete the mission. Okay. So basically this is the talk about military perspective.
However, if you think about for example the organization so you need to think who is the high value target in my organization. So thinking you who could be the high value target in your company. So maybe is a C level maybe could be the like the CFO because the guy responsible for pay the salary. So usually we think that okay who could be the most impacted position in my company if the attacker gain the access and this identity or if the guys should have a kind of uh let's say the permissions attach it to this guy. So what is the impact? So think about that. So maybe we think okay the high value target can be
the C level board member or can be the senior executive management sometimes we think that this guys is the high value target however we have here people with elevated privilege so now I have another point about that case that I share with you about the Brazilian financial attack the guy responsible for uh helping the criminals the facilitator he was a developer junior developer Who is developer here in this room just to Jesus okay sorry for that but it's not your guilt that's the point here the point is about VS code let me explain to install VS code VS code requires what administrator access so the you know the guilt is about the VS code because I'm
kidding you know like the many different application that you need to install in your machine requires the administrator access And that's the key here because the security level should look into that and the identity perspective how I can give you the access to this machine if I'm suppose that I'm developer and I need to use in VS code I need to use in many different stacks to you know doing programming things and the key is how I can go deeply and to giving the access for the a specific application in the certain granularity is a challenge here you know and that's the key so let's wait in here okay Philip you are explaining us that maybe
a junior guy can be a high value target the answer is yes so that guy that was the facilitator in the financial attack was a junior guy but they had a privilege in the in the environment just because of center applications so if they had a just in primary access, perspective access or other type of protection they could block it or you know um like protecting the environment. So that's important thing to understand here. So many teams involved with the sensitive you know information or even a stack project can be the high value target. So that's important to understand here because I will show you some misconfiguration. Actually I'm not bringing to you the zero day. I'm
bringing you [ __ ] misconfiguration. Yeah, that's true. Okay. Another important thing is attack vector is a simple like the method used by the cyber attacks like they can use in difference methodology and it's just important to clarify the difference between attacki vector and attack surface. Attack surface is your tech guy is a many possibilities in this [ __ ] room here. I cannot using more [ __ ] I'm using a lot of [ __ ] you know that that's okay. Sorry for that. In the end of the day, we're asking what are you learning this talk about [ __ ] sorry but anyway so if you see we have a different you know windows here we have a two rooms
here so when you talk about attack surfaces the many surfaces that attack can go inside of the environment so that's the attack surface attack vector is the way that attacking using to go inside of this door that door and that door you know what I mean so that's the difference about attack vector super common malware malicious software rams that's cryptography your environment and request The payment fishing has a kind of technique that you can using has a method a method to go inside and you can have the vector inside but there are human errors like weak credations poor encryptions and misconfiguration. This is our main takes here and of course is when you allowing someone to access the
sensitive information is another type of attack vector. Okay, cool. Another is attack path. Our main topic here basically is the vis is the chain is the visualization of the events and how they occur this attack or how the attacker can explore environment. Okay, this picture is so nice. So my team created this image but basically this image it came to the OASP or risk is not exactly graphy way as you can see in this picture. However is one idea how this chain works. So you see here the thread agent so the malicious guy the vector I explained to you what is the attack vector in this case misconfiguration okay and security weakness when they explore the weakness in some application
so let's suppose that you add some wrong configurations or you you know perform this misconfigurations in your environment you are bringing to the your environment this security weakness even if you don't know is a weakness because you apply the wrong perm permissions to the wrong user. So it's a weakness. So when you get inside you can of course control the security sensors in the environment and after that you can bring the impact of the technical or even business impact. Okay. So you can imagine this is example of Brazilian that I bring you. By the way this is very nice topic to bringing to the next year the talk. Okay. Talk about this is attacking in Brazil. But basically you
have a technical impact. Why? because this uh company responsible for realtime payment they need to be stopped by the the central bank in Brazil because like the this is example a real supply chain attack because like probably here in US you know works like the same case because in Brazil ba basically you have a person here the client that would like to buy a a cryptocurrency let's say let's suppose the bitcoin you can pay in Brazil in a real time payment we call pix but here in US we call zi that's right right if you don't know if you don't okay I live I know that's in US here but if you another country like in
Portugal is call amway it's another service if you live in your country probably another country you have this similar payment process but you have another name but how this working in the technology perspective you have here the user buy the cryptocurrency you can pay in real timing process you can buy buy z here in US or in Brazil you can buy by picss so these companies in the middle they responsible for offing offer this payment process in real time it's a third party company so this is the supply chain involved with that so this company responsible for offer this API payment the real time payment they need to inform the central bank responsible for uh in our case in Brazil I don't
know the name of the central bank here in US responsible for the government payment. This the do you know the name >> the federal reserve >> federal result so they responsible for regulate all those process when they in Brazil we have the reserved account for every bank. So let's say the banks in Brazil they manage the all accounts in this reserved account. So this is the flow. So I I need to buy here remember the bitcoin I will pay okay in pix or zi. So once I start this flow, I need to inform the Fed here or the central bank in Brazil. They go to this reserved account. In our case in Brazil, they okay this bank has this reserved
account. This this amount of money. So they return to this flow again two three companies involved. So this is a kind of chain is a real supply chain attack. So if you see in in US work is a very similar way when you pay in the real time if you pay in the credit card to you have another company like a visa or you know masterard or whatever or like American Express but they use another visa or master whatever so that's the key like you are a young guy here not too old like me but in the past when you need to you know pay someone or I need to you know doing deposit I need to go
to the physical bank when I go to the physical bank I put in the envelope You know like in the end of the bank close the one people one person go to the bank retire your envelope go to the system type okay this is account of sleep they you know deposit this amount they put in the system was a person in the past right but right now just paying is very fast so because of that is important to understand those path here those chain because remember I'm talking about the business right now so you need to think about your company how it works in your company. How many third parties companies is involved with that and this
process because in the end of the day you will understand what is this exactly thems
path converge for the same high value target. Cool. I explain what is high value target. I explain to you what is attack path and I explain what is a chalk point. I don't understand what is a [ __ ] chalking point Philillip just to explain to you. So imagine that you have a high value target in your company here like this one guy here. You have many possibilities to go until this high value target, many attack path, many shortest path. Maybe you have one or two short path. Who knows here? Who here knows about the blood hound? Okay, you if you go to blood hound, you can click in the short death path, right? So for the one single uh ad the
first person what is the shortest path until the domain controller right? So this is the shortest path you can have the long path or you can have the shortest path. So when you talk about the chalk point basically you can have more than one path to go into the high value target. Here the chalk point is the way when you stop the attack because if there are bunch of ways to go to the high value target there are one way that you can cut stop it the attack basically this is the chalk point okay that is cool challenge in the cloud you know that better than me so this is the challenge many branches comes to the
cloud because 76% at least using two who here using more than one cloud providers just to so in this room we have a more than 76%. Just a statistic here more than 76 in this room. Okay. And 33% comes to the account you know compromised privilege account compromised. Okay, that's a lot to manage it. Like this is I don't know if you know this information. Okay, this is a lot of information but like more than 80,000 uh you know permissions in the cloud AWS 2,000 in uh in Azure and 11,000 in GCP. Cool. Something happened here. I was hacked. I'm not talking about virus. I'm talking about cloud. Okay, here we go. Let's sorry. There we go. Okay. Anyway, let me just
stand it and meet her again just to organize this. Not too good. Okay. One second. Let me press the bottom once again. But you know like just to I know that okay it's many things to manage that's the simple explanation here and now talking about the sexy part okay so just to explain what is exactly am AM in AWS it's coming to the service responsible for control manage every permissions in the AWS so they will be responsible for connected like a puzzle. Okay, because if you work with cloud, you know how this works. When you talk about virtual environments in the past, we have a like virtual machine, storage, memory, how you manage those virtual machines. In
cloud is different. It's like a puzzle. you have I know storage you have a like CPU ECS or EC2 instance you have like storage behind that you need to attach it is something and basically the service responsible for control or integrate those type of things is the AM services okay here how you can manage those type of things you have a this is the policies from the AWS here you have the statement that is basically responsible for configure the policy inside of this statement you have the effect here as you can see that allows or deny you to access something and you have the actions here that include a bunch of permissions in the cloud
basically and of course resource is another important informations it's best practice to set exactly a arn it means AWS research name you should you know define each research name that you use in AWS the big here it use what here you You know what is the big mistake here in when you set some policies in AWS the big mistake using the resource the asterisks like let's put in a but ah okay Philip it's not common is a [ __ ] common take a look this so the questions for you guys because we have a time who think this configuration is safe Who is thinking that's not safe? Who thinks [ __ ] nothing? Cool. We have a bunch of people that
thinking nothing. That's interesting. That's cool. That's, you know, that's that's that's true. But like I I like this question because the good answer is it depends. That's true because if you think with me, okay, you need to buy a solution. The CSPM provided cloud security posture management, right? You need to buy what is the best flip. I haven't [ __ ] idea. You need to test whatever solution you want. But they requires to you a user and the user should have the read only access. So the right guy requires the right permission. This is the right permission. So it's safe because of the integration of this guy. However, if I ask you the financial guy needs to have
this permission, of course not. Is is the wrong guy. You see, so it depends of the person that received this permission. But if you see it's not a custom policy from from who? From AWS. So as I explained to you the effect is allow and the actions just list every single thing in groups, user policies and whatever. But again, so if you go to the AWSC website and you need to set some permission there, you go to the standard because it's best practice from AWS, right? So another question that I have to you so here knows or who knows about the framework called it AWS architecture that's [ __ ] cool. No one's worried about that. But
basically this is the guidance recommended from the AWS. So if you work with WS you see how this the problem is not about the developer it's about who configured the AWS because the frameworks from WS we suggest you the well architecture how you should implemented the web architecture in AWS but be relax because I always asking this in my talks and usually we I can see like 5% in the room that's know about well architecture and one of the principles about the well architecture is the list privilege so that I need to look into the each user and each permission remember the talk the title of the talk dangers of [ __ ] misconfiguration so if I don't know
about the list privilege concept or how I should look into the permissions I cannot apply this is in my environment so that's my takes here for you okay let's return into this this ideas okay basically it's some ideas that I'd like to bring to you get some secrets and tokens at AWS. We need to get this from some place, right? So, basically here is the simple code that you can use in your GitHub, your GitLab. Just a simple to get some credentials or secret access key and secret keys from AWS, C, GCP, OCI and generic key whatever. So, you can just configure this in your environment. Set your token here. You can running for education
purpose. I can say this. Okay. And uh you can run it privately in your environment if you to try to figure if some developer they you know putting this credentials open to the let's say private GitHub or private lit lab or even public okay but it's just a 4D staging you know it's the developer environment it's a stage environment it's not production you you you should try in the production if works or not just an idea but just to understand how you can get this uh access once you have this information what is the next steps here so if you have some access here it's simple like this if you don't have any experience just say to you just type here AWS uh am
a am like a service okay can you see my screen I think you can see my screen uh after that you just type configure if not wrong I think that's it no it's wrong uh the AWSC um configure Yeah. Configure. No. >> Just what? >> No, it's not. No. Is that Let me sec AWS. It's It's a configurer. There are some technical here just to help me. No, it's a uh AWS. Oh. Oh, that's it. AWS configure. Yeah, because I'm setting the CLI configuration. Sorry, my mistake. I'm just putting AM because I'm going fast. But this is simple information that requires to you to access the CLI. They requires to you the access key. And the
second one is secret. Once you have this information, it's done because the other information is default. Okay, Philip, but it's just getting access to the US East one. Okay, but I don't know what is the others region. Of course, you you you can know. Just go to the AWS website and ask it to the AWS how many regions they have once you have the access key and secrets. Just type in and set not the full region. You can set each one of them just to see what kind of information you have in each region. Make sense to you guys, right? The second one is another default. The output doesn't care. That's it. Once I have there inside just AWS am users for
example or policy let's see users not users is users not users I know what the common but if I share with you you know my my users no let me return here it's better because here in this case and I try at least users not users If I try list users, if you see this the sprint screen or the screenshot, we can see the access deny. Why this happened? Because the access key and the credentials or secrets, I mean secrets didn't allow me to access the list of users. So, let me hit here. Okay, this is the lab [ __ ] doesn't care. List users. So, if you see, I can see many users here. Super fast.
You see the users here, right? So just to see many user this is a live but doesn't matter but just to to explain it's just super easy. So in this case didn't allow me to list user and list policies and list group. Why? Because the secret and key they did they was the configurations applied in this user didn't allow me to access these informations. Is that okay? Did you understand? Cool. So after that I went to the AWS and I creating a new policy version. So if you see here if you don't you know like is it easy to to use it the AWS will you have like access level as you can see here we have a list read
write and permission management and tagging is a type of uh level of configuration you have in AWS I'm talking just about the A am okay you can set here the permissions using the UI as I'm showing to you now or you can using the JSON file okay once I chose here for example one single action. I just chose one single action. This this action is polic create policy version as you can see here and simple one action. Can you see here the screen one single actions I'm just sharing to you the impact of this specifically statement or this policy. I'm just creating a custom policy here custom since in the beginning. So if you see the effect is
just allow me and the action of this only one create policy and resource in this case I putting more in difficult way here let's say because I I could using the asterisk remember the first example eim really only access is asterisk for everything in this case I just posting asterisk in the policy perspective you see that is more difficult for the attacker just poling everything just to show you what is the impact. So now let's see what is the impact here. So once I I I actually let's suppose that I'm newbie guy. Okay, I don't know how I can set something. So I went to I went to the to the uh website whatever the Google or the chat
dpt whatever you can decide where is your new search or new research. So I ask it to the the Google in that case and how I can creating a full access in the cloud in the AWS. So they suggest me this code. Okay, I copy and paste as you can see here and I call the attack exploitation JSON here file and if you see they will allow me to access the whole AM remember those bunch of level like read uh right permission management taggies whatever but here they suggest me the organization I don't have what is what does that mean organization so if you don't know and when you talk about AWS and GCP and
other providers you have two different layers to manage it. One is the organization level. Let's suppose your company has organization and you can have more than one account behind of this uh organization level. So may maybe if if you're part of the big group let's suppose that your company has a group call it whatever GC I I create now the name and behind of this group we have a four companies. So usually for the architectury perspective you have an one organization level for the group and behind of this group you have each account for each group. So when you copy and pasted this code you give the access to the organization level. Okay, just to clarify this because after
that I go I went to the Google again and and asked to Google how I can set a new create policy version using CLI using command line interface and they suggest me this command AWS create policy version setting the uh AWS resource name the name of the policy that I created and they need to set the policy document if you see here the name of the document attack exploitation JSON and if You see here this tag in the not tag but this parameter here set as a default. When I type here it works. So I was here in this level. Remember this level. This is the the policy that I created right and here I was in the account level
one single account level. Once I elevate the privilege here, now I am in the organization level. Now I can see the all accounts behind of this organization. It's not a zero day. It's just one single action. The impacted one single action. You see that?
So now we have a list of user. It's interesting because I blocked this information here. I hided the information but I showed the information to you. It's a lab doesn't care. Okay. So that's the impact here. So okay. So how I can okay uh organize this? How I can deal with that? So there are a bunch of uh open source tools and you know free tools that I can share with you. I just sharing some tools to help you. One of this is ctography. Okay. Ctography like this one here is the open source tool. you can you know use in your environment you can you can test they support in this different u let's say connectors
because in the end of the day you need to connect using you know uh APIs to go to the AWS or to go to GGCP as you can see here or other platforms and you need to collect those identities and usually this type of you know tools requires to you the access the really only access the first polic that I show you. Remember that I ask you if you're safe or not requires to you these permissions. Why? Because you need to integrate with that and they need to bring it to you the users with the the right permissions to bring those informations. Once you have this, you can go to the let's say um the the tool
and you need to you need to understand more about about cipher queries. When you understand the cipher queries here, of course you need to understand more about the Neo4j database or maybe if you are familiar with the Neoforj database or main graphs you can set some comments. You can see here in the graph way this is one tool. Another tool is ctography is AWSPX is another tool that I can share with you. This is super interesting because they can bring you this informations in the same way like this one here. I have my lab here. So they will work in the same way here below you can see it's is small okay but you need to understand more about cipher
query how each cipher query works we have a 10 minutes that's cool thank you sir you're super guy and but basically here you can see how this graphical works for example if I click here in in CFO you can click here in the right bottom you can see for example about the actions you can see how many actions you you see here in this environment for example. So the question is why this blessed CFO is a part of the administrator access group just because we pay our salary but they have an access here what that means in this case so based on this configurations here and this actually is a part of the administrator group and they are part of
this administrator access here and if you see there are 49 actions. So let's see how many actions we have here. So let's take a look about this specifically actions. We can choose whatever you want here and choose what is the more dangerous actions. Remember inside of one single permissions we have a bunch of action. I just show you the impact about one action. So let's see for example this one here the attach user policy was what that means that I can the attach one specific policy let me explain the the impact of this attach user policy so let's suppose that you get the credentials secrets and access and you run this command here that I
show you okay you type this command here thank you >> yeah thank you again oh it's here you you type here the the config grouper For example, you type here, you go inside. Okay. And after that, you go to AWS EM uh list policies. So once you type here, you will see all policies you have with your environment. So a bunch of policy. So take a look this one here. This is a uh let's say this is a custom polic. Okay, let's suppose okay this user just have attach pol attach demo and demo labby two custom policies not to danger however maybe you found one of these user that has the attach user policy what's that
means the single actions allow you to attach a new user policy okay Philip can be danger or not we know You know, I know that AWS has one single administration access standard policy. You can go to AWS website. You can see this is standard there. And if if you see that is there, you just can attach a new one. Simple like this. Just because one single actions set it wrong. You see what is the impact? You don't need to know because when you go to the AWS, you need to configure the EC2 instance, right? So if you're not familiar with that, you go to the AWS and they suggest you the proper EC2 polic standard from who? From AWS. But
you need to check all actions that are inside of this specifically polic because it's a standard from AWS. Okay, Flippy, you are telling me that I should custom all those policies in my environment. Yes, but it's too is it is it too much? I have a problem with that. Is it too much? Yeah. Welcome to our life. That's we need to work with that. That's okay. I could I I could use in the let's say the standard. Yeah. But if something wrong happened, good luck, sir. you need to have more you know work to do basically this is another tool let's say okay so how seura works with that how my company works how I can help with the community we created
this program we call beauty us basically is the way that you can using the same similar tools but in this case you don't need to know about neoforj you need don't need to know about cipher query because you just integrate with your environment once you integrate with that you have the community version as I will show you here for example in my environment once you have this integrated that I'm using my private email by the way one of my private emails by the way once you register that you can use for like educations if you want for master whatever uh if you see here my in my console is in sandbox mode so when you receive the access you'll be
there you have this kind of mock you can see how the tool works once you disable that you can use in your proper environment and you see here in this right side the left side here let me just disable uh it's not here is another part here but you can disable here let's see my is not working my internet here okay leave this in box mode let's see if working right now and uh yeah it's works right now so if you see here basically is the community so you can integrate with your environment they just bring it to you the identities here and you can see how this works in this specifically perspective that I mentioned with you.
Here you can see the recommendations you can see the access path here and many different ways. So how this work in the access pack access path perspective as you can see here and you don't need to know about like the cipher query. Let me just enable the synox mode just to finalize here. And once another thing that you have in this in the future let's say is about the machining the the AI integrations. When you have integrations you have here the get insights of the you know the AI they bring to you some insights about your environment. So if you have if you have a five minutes like me that I have just five minutes to
talk. So how I can go and fix those type of things. Another thing that we have is the attack path here as I show it to you. Getting attached polace go to here and you can see here the attack path perspective. You can see what is the requirements. You can see how many you know users you have behind of this attack path that you need to fix and and machine identity comes the same way here. You can integrate the different ways and you have again the possibilities to integrate mean many different things. Another tool just to share with you is a sec bridge is an open source. In this case this two is is for a Brazilian guy is not exactly in
the graph way but here is more the offensive perspective. They organizing the two different tools like a prowler. This is like a CSPM uh cloud security posture management and paku is more offensive perspective to explore cloud environments. When you have this integrated, you can have this for uh more details, more information. But this tool is specifically not exactly for uh the let's say graph ways. I think that's it. Another tool that I would like to share because last year they asked me about that is this is specifically two is the star base. This tool is not exactly for uh the security perspectives even they call security analysis here. But basically here is the collector. Okay. Is a big source of collector. You
can integrate many more than 100 uh yeah 100 open-source graphs integrations that support you. We can integrate with that and you can manage that type of things. And this is just a print screen that I showed and I finish here. Wow, that's cool. We if you have a questions I think we have a like 45 seconds. No, I'm kidding. >> Take some times. We are finished. Yeah, I think we Oh, yeah. We have more 30 minutes if No, I'm kidding. >> Okay. Uh, okay. Question on this side. >> Sir, please. No difficult question. Okay. >> So, be kind. Be kind. Be kind. >> Okay. So, I spend a lot of time looking at same types of graphs from all
different kinds of systems, right? I have a list of people and all the access that they have and I I'm going through and I'm identifying risky stuff, right? So, I'm I'm with you there. The problem that I run into is I'm looking at a list for some person I don't know. don't know what their job is. I don't know what their role is. It's a service account, whatever. But I I see the risk. So, if I just go bother somebody and say, "Hey, here's a bunch of risky stuff that you're allowed to do. Please tell me whether or not you actually do this as part of your job." They either have no idea what I'm talking about. Or they
tell me, "Yes, I do actually do all of that. Leave all of these permissions with me." Right? So, and that's not good enough for me. So, I usually try to grab logs, you know, from the past like 30, 60 days or whatever and overlay it to say, "Here's what you have, right? Here's what you actually used. I want to take away everything that you clearly are not using unless you flag it and say, you know, that's a a break glass permission. I need that. Do you have recommendations on tools or or frameworks or whatever to make that easy, you know, to overlay the actual use data? >> So, that's interesting question because here you can see for example the
integration with these tools. Again, this is a community version and uh actually actually we have a another enterprise version but for now it's free. So it's everything is free because I'm the owner of the project. So it's I'm not the owner of the company but I'm reown the project. So it's free. But anyway you can see here never use it here. So this is one way that you can show with the the the user. >> Yep. That is exactly I need this for every system under the sun. >> Yeah just like man it's completely so they just using 35 services in AWS. So why you have more 30 you know 30 >> on my my Android phone right? It reminds
me every 30 days, hey, I'm taking away permissions on apps that you haven't used. Why doesn't AWS do that? Right? Like, >> yeah. So, but the point is if you don't have a visibility, how because you need to go to the AWS and go to the 30 days and know >> it's it's a whole exercise. I have to pay people to do this or spend like weeks doing it myself a >> but for GCP perspective in this same tool because this tool is created by you by customers. Yeah. that we we put in Brazil, we put in US for many companies are using this tools and one of the the the the features that we have for the
GCP for example is because GCPs is based on uh the rule of the users and one of the thing that we received from this this specific company in Brazil they ask us okay I would like to see the vision about everyone every user that don't have any you know permissions apply it to this users so because sometimes they have some permissions but Now I they don't have any like privilege account attach it to them to them. >> Oh like the if they get their just in time access what can they do? So that's the key. So if you don't have a v visibility how we can fix this. So basically the the the change the the
challenge is so we need to figure what is the right tool for my right environment. So we can use this for free again. So that's one one we can use. >> You have a question. >> Yeah. Uh thanks for the talk. I you didn't speak at all about agents. When it come to agents and their identity which like all new notion that is just thrown into this complicated system uh and this uh how does it affect the threat landscape and the applicability of this uh graph analysis? >> Good questions. I don't know if you're familiar with that. I can talk in two different ways here. One is about how does different tools is integrated different environments. they use an API
integrations. So I think your question is more about agent AI. Is that correct? >> Yeah. Yeah. Agent AI. >> Agent AI. Perfect. So this is one of the topics is very common that I was in the identiverse few months ago. It's here in by the way in Vegas. So I think many companies are creating or starting some research. My company for example they are creating now the integration with agent AI because many companies are using for example to buy something like because the agent AI they requires many privilege access different permissions so talking about the thread landscape so once you get the access to the agent AI you have the whole permissions behind above this agent AI and that's the big
challenge for the the identity companies because they need to manage how is this permission this agent AI has for example to buy something in different uh in different websites for example and uh and now our in my case for example I doing some research but my development team are creating the solution to that and that's the key and by the way and this year I think two months ago or three months ago don't remember exactly the identity versus uh event here that Vegas that has that are specifically event for the identity so I saw four or five companies developing the agenti for the security perspective But you talk about the landscape actually uh many companies are using this mainly for
buying things or for automated things because they will you know understand how the let me bring it real example here uh let's suppose that your company is talking is responsible for buying it's a e-commerce so they need to buy for example they need to figure what is the best Nike tennis shoes more uh cheaper so they go to the Amazon they go to whatever website that you Once they go to different websites they will choose what is the more lowest pricing and based on this lowest price they will buy this Nike tennis shoes. So the point is so to buying this they need to they have a permissions for pay for paying something like they need to have the
credit card associated with that they need to have permissions to buy the you know this product it depends of the website they need to be the research they need to have a registration so everything is about identity so we should manage this actually the identity companies is not uh prepared for that yet but some companies are doing research and other companies are creating product for Okay, thank you. >> I appreciate good questions. >> Okay, one more last one over there, >> but not least. Last one. >> So, the the question that I have on his >> Yeah, just get the mic so it'll be on the recording. So the question I have builds on his
because you were mentioning how just in time access would have helped >> the financial institute that had the hack. >> Well with one of the big things that they're selling with Agentic AI is it's 247. >> So how does that work with just in time access? And I mean it it's one of those where I'm going it seems like one of the tools for trying to prevent these hacks is actually being destroyed by this 24/7 because the purchaser >> Yeah. >> Uh Aentai there might be better prices at 2 a.m. versus at >> 8 a.m. >> Yeah. But that's interesting because in this case we should look into the another feature talking about identities call in for example user behavior or
like we should we should associ associate it like behavior um process let's say tentative of payments in two 2 a.m. and uh or like tentative of payment in 30 seconds or 10 seconds every time. So probably someone get inside of the agent AI they try to buy different uh product in one single short time. So this is or for the different locations gel locations. So we can use like okay just in time access is another way to protect but like the concept of the agent AI is about 24 hours or let's say 20 247 you know what I mean? So that's the key. So we need to using another type of um you know ways to protect
that's I'm telling about the research about agent agent AI because many companies are putting this to automated process uh it's a super nice for the security perspective and the offensive perspective guys as well because again so they are using some concepts to creating this technology but in this case and my perspective to protect is based on behavior should be the behavior because okay the attack that I hap that happened in Brazil is based on and we should block it to the just in time another way to block it it's about behavior because the access that the criminals has is based on the the insider so was the the user you know the employee access so if they had the
behavior analysis about the payment process they should revoke this credentials once they revoke this credential they will block it. >> Awesome. >> Thank you very much. Thank you, Filipe. >> Appreciate guys. Thank you so much for being here until now. Have a good amazing night. >> Thanks everyone. And that's the end of the password contract for today. Have a good afternoon or evening I should say.