Automation: The cause of, and solution to, all of our problems - Jonny Milliken

Show transcript [en]
uh hi everybody um thank you for coming so my talk today is entitled automation cause of solution to all of our problems um if anybody gets the reference for that there's going to be more references in a similar going forward um so the kind of basis of this talk is that a lot of the time in cybercity we talk about the malicious automation that attackers are using right oh they're spinning up all these things in AWS and then automating this and automating that but really whenever attackers are doing all of that stuff whenever that hits you know the blue team whenever hits the seam whenever hits those other Technologies it tends to generate like a
couple of alerts right so if we think about well what is generating all of the alerts that we're handling all of the time inside the soccer inside security operations was not attackers so what is actually going and doing it so we have the malicious automation which is assisting attackers then we also have our own automation on The Blue Team side right that's attempting to you know try to make our lives easier but the thing that's actually causing most of our alert fatigue is as a consequence of bad automation that is internal error organization is doing some other function and yet is also performing some sort of activity that looks similar enough to something an attack would do
that that's what's causing all of our that's what's causing all of our um all of our fatigue so that's what this is about um SL on me but I've already been introduced uh so yeah me um this is my fourth bside presentation I think um and then that's me presenting a big data Belfast and although that's one pandemic and two Stone ago so so just a quick uh quick poll because I know use love raising your hands uh who here suffers from alert fatigue or Works in a team that suffers from alert fatigue oh that's pretty good there's some vifer ones at the back they're very fatigued um okay yeah so ultimately in the end like
that hasn't really changed so if we look back on the the history of the industry way way way back right so 15 20 years right then we still have fatigue then we still have le fatigue now and yet we have all these other tools have turned up and then said we're going to solve it and yet here we are right so what is actually generating that right um now one of the first things uh I wanted to talk about was uh AI right and I like to describe AI as a a wolf and Gran's clothing right makes a good story but it's definitely about what it pretends to be right it's not actually what it
says so um we've seen this we've seen this before right the security industry is repl with uh companies turn around saying I've got a new technology that will solve your problem I've got a new technology that will solve your problem and yet we sit here with the same problems that we had 10 15 years ago so maybe technology isn't actually the problem whenever this goes on and off can you still hear me yeah yeah okay so uh if we go back like far enough back right then uh uh what kind of Technology what kind of detection Technologies do we have in order to try to help us go through a bit of a background so signatures just basic
signatures right just write some logic if some sort of data matches that particular signature well then fire an alert right okay pretty simple back then people saying ah these signatures are terrible oh we've got all these false posi are going everywhere we need something else it's going to go and fix it okay so they said the seene was dead and they also said Manchester United would constantly win the Premier League so that tells you how far back that was so we said okay signatures very bad so what are we going to do we're going to have an only detection that will solve that problem because ultimately in the end if everything that an attacker does
is atypical compared to the environment that they exist in then orgo that's going to be much more successful right which can only really be said by people who have never worked with either networks or users before because anomalous things happen all the time in it's sufficient lar environment right the difficulty being that you could really tuned them because it was a matter of saying okay well it's going to reach a threshold somewhere okay well can I tune that you can change the thresh thrh yeah but I don't want to change the threshold it's just doing certain things and generating false positives but how do I tune that it's just kind of doing anomalous things right so they said okay well pass an
detection what's the next big thing next big thing is machine learning right only we got yet more false positives just nobody can really tell you why the Black Box okay system learned something it says this thing is bad great why did it say that well I don't know it just says it it's bad super d right so we got to this point and yet we still have alert fatigue right I mean this isn't fairly you know was fairly recent we because a sort of machine learning component people said oh yeah I'll all the problems don't think any of us could say that all of our problems are fixed right um the only good thing or one of the
good things about machine learning is that we brought signatures but in reverse because the only way to stop generating all those alerts was to Whit list it which is just a signature in Reverse so now we have gen right and that's being post or posited is the thing now finally going to solve all our problems right but who knows we're going get hallucina false positives things that have literally never happened just been generated who knows we'll see right but I don't think any of us could say that this time this time this technolog is going to be our savior now if we think about this from a from a more basic perspective right and again try to get to the point of what
was the actual cause of all this to begin with so if technology isn't going to fix the problem well then what would right so if the signatures AR signatures aren't the cause of the problem they're just one of the tools so if we say the signatures are say a right then if I give that hammer that tool to someone who either doesn't have the time or doesn't have the skill in order to wield it effectively well then you're going to get false positives that's how that's that's how that's going to working so for example if I give that hammer to my kids well then the heist would be a mess they probably take my kids off so that's what you get if you
give a particular tool to someone who is able to going wield it right we then continue on to the analogy we' got an only detection right so an detection isn't repl for a hammer nobody ever built a screwdriver good enough that it made all out hammers obsolete so it's another tool to solve another problem and more effective way but it doesn't replace any of the things beforehand they all need to be there right now if we continue with that then we have machine learning right let's call that a Sol why not right now if we talk about gen gen is really just a larger extension machine learning so we say that's a power saw right so then that's a power saw and
then that's going to make us much more effective in the things that we do but if you think about the damage that you can do with a hammer like if you think well how many false positives could you generate if you only had a hammer like what bad things could you do well say you had an electric saw say give an electric saw to one of my kids right well then probably would much of H so what is the solution to that problem right the solution to that problem is this unit right so ultim in the end the problem has never been Technology based the problem has been human based the problem has been business based right
it's about trying to generate a scenario whereby we have sufficiently trained staff here able to wheel these tools effectively in order to actually address the false positives and the alert fatigue that we've got in there right because in the end these are just tools if there isn't a person that car them around well then they just be Ling the floor so you know this is the GU the solution to the problem not yet more technology so you say okay well geni is going to be I don't know this speed right great but still not going to solve the problem because somebody pick it up and use it right that person who's picking up and using it is going to be
is going to detate how successful whatever it is they're trying to go into so like I said didn't take long so this is kind of the scenario We've Ended up with right um we have created enough Automation and Let it Loose inside our environments and not pay sufficient attention to what it is that it is doing that it ends up causing us problems further on down the L right it is to a certain extent in charge of a lot of the detection a lot of the decisions that are being made and we take that away from the humans who are supposed to be making these decisions right but it's we have to do that in a way whereby the
humans are still in control and the humans are still involved the process and not just say hey let's have all this automation just run up right and I'll talk about an example of that later but anyway let's talk about automation generally speaking right so good automation automation we like right uh what does it allow us to do so it allows us to respond events in near real time allows us to process very large volumes of data all once um and allows it to reduce human effort and repetitive task and that's a good thing right as long as that's driven by human knowledge and human uh human expertise well then great right it's harder to do
the designs but it's still objectively a good thing now if I think about bad automation right you can take exactly the same uh Concepts and then turn them evil right so instead of responding to things in near in near real time what you end up with is the the incapacity for a human to intervene so the machine is just going to continue to go off and do with the doors by the time a human has been able to react and correct and do whatever that fixs whatever it is It's Already Done Right already done perhaps even at scale right right so the fact that you can do things at scale is good but the fact that you can also do
errors at scale isn't particularly helpful right so if you do it badly then it's going to end up being much worse than if you had done it at all and then one of the things that I tend to see in practice happening an awful lot is because there's so much automation that's sat inside the environment and then laugh and then maybe somebody somebody laughed and then there wasn't really a proper handovers and then someone else is getting responsibility for it but then they don't really know what it was cuz they didn't build it etc etc you end up with this reduced accountability so if you something in there that's doing some something that is not meant to you say well hang on a
minute who's responsible for doing that everybody looks each other and goes I don't know it's Gary he left a year ago okay well then who's responsible for making sure that that either didn't cause a problem now or isn't going to cause you know freeing problems in the future well I don't know we should pick somebody else to try to work out how all this works again well you know that's bad automation right and again that's nothing to do with technology none of these things you can get this bad component nothing with technology just does what it's told but depending on the humans are managing it well then that's how you get something bad right now if
we're trying to think of examples in the recent past we may have had some kind of automation which isn't malicious automation perfectly fine automation does a perfectly good reason or a perfectly good job for all of us that may have caused us some trouble in the recent past um then you can kind of see where this you know where this can lead to right and one of the big things about you know some of the outcomes from the C strike stuff is um chances this happening again are pretty high because while cry strike are you know one of the biggest companies in the world their particular demographic and these are all things that are as a consequence of an
over Reliance on Automation and too little involvement of humans in validating the automation is doing the thing that is meant to like the automation didn't know that whenever it ran and the P all this test that it wasn't meant to continue like I human would and then said that police is probably not good you to stop this and then have another test right so in the end you know we do have to Leverage automation we have to make sure that it continues to make our lives better but we don't have to turn over all of uh all of the um all the keys over the Automation and just have it do exactly what it did there so um yeah so we'll
talk a little bit about some of the different automations some of the bad automations that you've got inside security operations which ends up then consuming an awful lot of our time and then talk a little bit about what we could potentially do or what tools are available for us to try to fix it so scanning Discovery right A lot of people will be familiar with this right so let start off with the scanner right the basic prise of the scanner so uh call us lots of scanners call thing so uh scanning is good right we like scanning scanning is good it tries to identify whatever vulnerabilities or whatever risks exist inside the environment then tell us about them don't want to be
logging into every computer yourself to work all this out so it's good automation from that perspective but it's only good from a security bling perspective if it's scheduled and known right if it's unknown well then that's the kind of needs investigated right if it's unexpected well that's the kind of thing needs investigated objectively if you s and The Blue Team someone says well we have an unexplained scan should we look into that you go yes we should but it will probably be callus or any other scanner right so um the question is how do we keep those components off our radar because they're just a reality there's good automation but some bad components out of it another example
of uh this as well is asset Discovery right which is kind of different from scouting and also like in a worse way so the purpose of asset Discovery is to try to identify all the different assets inside the environment um and then build that into like a cmdb so that people can access it and say okay well here's all the stuff we've got in the environment right people Jim brought a new printer and plug it into the network right J why you do that but you have to actually find the printer first in order to go in shut again so the way that this causes a bigger problem is that it isn't actually it's a lot more difficult to establish
exactly where this asset Discovery is going to be coming from doesn't necessarily always come just from the set of devices you've got inside the environment it can actually come from other devices inside the environment because again asset discoveries by trying to find the other things you don't necessarily know about right so um it also then tends to have more ad hog running pattern if you've got a scanner and you might scan say on a Saturday okay or last day on a Friday no problem but ultimately in the end if you're doing something like asset Discovery we can't to on a regular basis then if something is constantly turned off on a Friday well then you're not going to
know it exists so was much more ad hoc from that perspective um yeah and it can also then uh carry out activities inside uh existing devices for software numeration things like that which then causes even more difficult but we're just talking about Network scanning and network discovery right so what is why is that a problem right so this then defines your noise floor right so your noise floor will then DET take how can you actually detect unexplained scan so if you have constant scanning constant asset to Discovery going on then this is where your noise Flor is right you got your outside voice on constantly now if you have an attacker coming in and the
attacker is using their whisper SP voice right well then you're not going to hear that because everybody's constantly shouting using the right door voice so this is the consequence of that not just on from security perspective because even if you've got a seam or some other technology and you think okay well we're getting C positives it's coming out standing and Discovery Well you might be able to tune that the scene right you're Lu um but it's still inside the environment right so if you find yourself in an IR perspective where you have to go and look through all of your data all that data is in there right so one of the consequences of having this
scanning this acid Discovery at the rate at which it is being performed inide the environment is that you're raising this noise floor wherever it is and then anything below that noise floor well you're not going to be able to spot it right and then even if we were to take some of our more advanced tools right if we were say Okay gen or machine learning please you know learn what's going on in environment well well then this is what machine learning is going to do right so if it's unexplained scanning is happening constantly it's not unexplained anymore or unexpected so there's just lots of scanning yes there is lots of scanning so well how does
that help right so um I'll talk about some potentially some ways that we can try to combat that later but even some of those more advanced tools logically speaking like from within that set there can be very difficult or impossible for them to say that it is atypical or something that's not expected my one of the ways with becomes even more difficult right this is a difficult uh picture so um this is also from service Discovery right so say you have this mid server one and it is attempting to do Cloud Discovery from inside the network right this the way it works so you've got asset discover asset Discovery server asset Discovery server says okay I'll just discover Assets in
here if you've configured it to also look for cloud assets it will go no problem and I'll merily scan the cloud for you but inside the network you can usually find it because it's going to be happening inside the Network segment but whenever it attempts to then contact says or jur and other things right you're doing it this way well then as it traverses through the network right any number of points there you might lose the original place you might go through some sort of one it might go through any number of things right that we um strip the original uh the original origin so when it when the request appears here at the firewall going out into the end s
right not unreasonable for some security system say hang on a minute I blue something inside the environment attempted to just contact thiss IP address that has never contacted before that's a bit suspicious and you go yeah that is a bit suspicious okay let's have a look at that but whenever you come and look in the firewall right you're only going to get the next hop so like where did that come from BL bouncer okay low balcer like where did that come from I okay so you go further back further back if you're even tracking that Pieceful information right it's quite common in fact to be tracking information here and tracking information here everything in the middle not to much right so in the
end you have to go probably Discovery and then come all the way back here in order to try to find it right or like somebody said in the previous talk you just doar short clothes you go so um yeah so this is also a problem you get from as well and then that can generate not just noise but it actually you know triggers detections for suspicious you know CNC coms at unknown AWS addresses yeah it kind of does okay so what can we kind of do with these some of these things so one is to attempt to aggregate the scans over a larger time period right rather than say okay we got the scan got scan actually
if you um widen up your time period to less say an hour and from that given Source location sometimes the combination quaries the combination portch that it uses are fairly like constant and can be used as a kind of signature and then from that perspective you can identify okay well you know in that time period I'm going to call that scan this thing because it matches uplo this criteria if an attacker doing something else well then the chances are it's not going to do exactly the same things as whatever You' got configured to go on do so you know there's no way to tell the another one is uh canaries so uh people are generally aware of canaries so um
the basic Parise of this is you get a like a token a canary token or a canary device stage environment and then you wait list it from all of your scanning of everything and you say Do not scan that right um now from that perspective once an attacker comes into the environment L not to scan that so it's going to scan absolutely everything else H the noise floor but then they they'll be the only ones that SC the canary then you go hang on be SC the canary again inevitably you know the actual people hitting the canary in practice will be that admin like I wonder what that IP is and you go please stop doing that but
that's one way in order to try to reduce and get that noise floor away and instead trying to focus on things that are actually unexpected inside the environment because you've made a decision that this is supposed to be unexpected inside the environment another one is enrichment right now that you know comes back to the asset inventory so bad assent inventory but whenever we have it well it'll be quite helpful to try to work out what things are so if you do have that kind of acid inventory uh using that to enrich whatever is going on if you can configure that and say your SE or sore we'll talk more about sore later um then that can help like the more information
you've got the less lookups you've got to go and do the less lookups you've got to go and do the quicker you move through your queue the last R the these alerts will seem to be then the last one is to be in the room even for things you think are not security tools right so if you're a security team right well then obviously if there's new security to you probably involved of that or some sort of or decision making on it some component but also be in the room for other tools even if they're not uh security ored directly because again if we think about say service Discovery right it's just ask Discovery just got
to do with security but one of the consequences of that are the increase in noise for one of the consequences of that are we may end up having to go and investigate a lot of this stuff that looks an a like suspicious standing so that's how the conversation right at the start about you know what are the consequences of this right can we configure this in a way that is more effective and the only real way to do that is to be in the room right so don't just let the organization run off and do its own thing and then say okay you know we'll just we'll do our thing we they'll do theirs in the end a lot of these
tools are owned and operated by other people in or other other departments inside the inside the estate so if you partner with them you might be able to take the edge off some of this okay so that's uh scanning assets uh next one's emails so again the point of this is to do uh bad automation not malicious automation but if there is a demand whereby malicious automation V strips the defenses it is in fishing and eal protection right so I'm not even here to talk about like URL rotation URL delay like use a capes so the companies can't like redirect so the you know the security systems aren't assessing the correct is actually going to be uh
served to people right none of that right that's not even our problem here one thing we've got is about automation right is uh it's called cold email domain variation see this quite a bit right I've just just for people's purposes cold email so the way that this works uh if I um say this Middle address well see bot so find the bottom address there and I send 100 time emails the chances are they're not going to get blocked to begin with the chances are your email protection system is going to say okay let's read the first 50 then be like quite a lot of emails it's probably SP what more SP all right so you sent 100
emails 50 of them got through right well then if you just use automation right and order for this cold email delivery then you just change the Senter to be that okay and this is all done automated sense so again then the spam system is going to get that and then say okay hang on a minute about 50 I think it's a Spam again I'll stop that okay but the two of them you got 100 Li half of those and half of those and even if it starts to learn and say hang on I'm a bit suspicious about this mean it's still reduced your certain components so instead of 5050 you might 50 50 40 and
then that'll give you some level of deliverability inside it right so this is one way that you're going to be these um uh get P into the spam protections right as you start to bury those this is all automated now you might think well okay well just block the demand genius but yeah okay but obviously there thought that so you start off with this to me right well then again from an automated perspective and all this entire thing is auto so you got that just that. at the end okay well then you haven't block that domain it's complet new domain so okay then the next one email the next one.net again each of these is going to
add 503 5050 5050 5050 then again you don't have to just be doing the TV just add a couple of actual letters on there e r i do that yeah no problem and you can combine them so youve got r.co r. r.net over and over and over each of those maybe they'll get 50 to go through now you combine that with that one and you're starting to the sender and the Domin in a way that how do you st that right so most email Protection Systems aren to in order to defeat this um so now I talk about spam right now why is Spam a problem spam is a similar problem from a security perspective as the noise
floor is a problem from a security perspective right because in the end whenever users receive they they still then report a certain component of them to the security team they still say hey security what's this about it's SP okay so you have to have a look at it then say no that one SP again too okay all right that is a problem from an alert uh fatigue perspective you might find it certain scenarios then all the things are reported to the from an email perspective uh to security tees end up being spam but uh there's also a fatigue perspective from users right so if I go to the average user and then say hey I'm
going to send you 100 emails one of them is a fish you tell me which one it is chances of them doing that slim compared to if I say tell you what I'm going to send you five emails one of fish you tell me which one it is okay well then they're going to have this dominant in order to try to assess all of those and then go through it rather than thinking not another one of these so the more spam that they receive more spams reported into security tombs and the less likely they are to spot actual problems no in terms of the variation of those sanders and the and the domains right how you going to solve that now
there is one C that saying that does something quite Nifty right and you'll have to DFT off your gcsc French for this one so uh these guys whenever a new sander is observed coming into the mailbox the email Isn't delivered instead what happens is the sander gets like an email effectiv complete this Capt you have to prove to your person then after you complete all that only the is your email to be delivered and then going forwards down your are deliver because it confirm There's an actual person there and that doesn't solve all problems and certainly what it does is it slows down you contacts you still have to go and do this and as you
would imagine if you send an email to somebody and then they get this back and then they immediately report that to the security team that's say this thing but it does nonetheless work right so um it would solve that particular cold uh email demean variation problem because as they start to vary it's not going to solve capure many time so they're not going to get through so we solve that particular problem although you're hold them um so this is some good automation that you can have right this type of uh type of approach is one that can try to combat that spam problem and ultimately the security problems that come with it okay sound boxes
sound boxes are good I do like sound boxes sound boxes are one of the more effective ways that Security Professionals can dat with potentially malicious uh like artifacts and files and links in a way that is safe um you know it's quite cost effective in order to get people access to these and to try to learn try to use them like there is a certain amount of skill that still comes into assessing sandboxes and using sandboxes but nonetheless they are a component of good automation right but they can also be bad automation right now different things that a soundbox does not any detail we're not here about soundbox analysis but you get static analysis you get damic analysis static
analysis just signatures bomic analysis calling all the attention so from that perspective this kind of stuff is kind of predictable this kind of stuff not people right so if you're going to be taking a piece of technology and then putting it in an automated perspective I think it's fine to then either be very uh prescriptive by which these static comp you're going to rely on because again if you're a human you're making a decision you're making a business decision that I'm going to do this thing um and I'm going to automate it and as a result I'm going to stand over the the consequences of it then from the dynamic analysis perspective you don't necessarily know what's going to go do
right you don't what is going to pick up what's going to say is good or bad so uh you end up a scenario where you got something imp plag is malicious but of course like is it like the soundbox says oh this is bad whatever this is set up AC and does all those things right great but it isn't like you're require human to come and look at this and then assess it and go like I a sand what you talking about cuz the sandbox is completely of context it doesn't know so if I have if I have loaded Excel sheet into uh into the sandbox and execute and it goes red and says you know there's macros this me be
MOS mro go oh it requires a human to know that like the soundbox is devoid of contact it doesn't know why that's happening and say oh hang on I this one's also writing 10 meant write 10s or this one this is triggers Ms Edge acting how else would it view the web page I mean that's how this works so the thing about this is uh if you rely too heavily on the decisions that are coming out of these sandboxes then you end up with far too many false positives and then this is what ends CA in so much of our um so much of our alert fatigue right so if the sandbox says I consider this to be
bad right there's too many scenarios particularly in uh open source intelligence or even certain threat intelligence feeds that'll come along and say okay well this is my wear everything this malware does there therefore must be bad if it checks the time things that check the time must be bad well no obviously not right not everything that malware does is inherently malicious and not everything that a malware does does need to be reported upon and yet if from for years and years and years but if I go into particularly open source or CR Source or Community source and threat intelligence feed you'll find hang on where did this come from you go all the way back and
you said oh somebody just put that in the automated consequences of that being submitted into the OR quences of the the analysis being submitted into thatn feed and then go that FSE positive causes all these problems right now like inside security you have to have a certain amount of skepticism right pretty much everything but particularly where you have a computer if a computer is telling you something on circumstan you just be like okay yeah that's fine like one of the first things that I do tell like more Junior analy whenever they start is that the the computer says this or the security system says this do not believe it use your human brain you're not there to just say well
computer says no that's not what you're here for right so the more that we can encourage and train and develop people right be that big blue unit guy right rather than just being somebody who's just Leed the tools all back to automation how do we turn this into good automation right to a certain extent it is bad automation right because it do lead to these false positives do lead to these false impressions of the maliciousness of stuff but so I've stolen this right now this is a a this is about Team Dynamics right people know this forming storming forming right now where do you think you should go where in the whatever it is you're doing the project or the system
whatever it is you're time to design where do you think you should be most of the time business imperatives would impel you to try to do AO all the automation here right that's your bad automation Zone because whenever you're trying to do whatever this thing is you have an idea then you put it into practice and find your roong then you fix whatever you were wrong about and then you go okay let's try to go and optimize it so this is your time foration right youve decided you know actually what's going on you're trying to find out how to optimize it and get it as as good as it can be okay well then let's try to see if we can automate
some components to that because we've not proven over time that it's actually worthwhile doing great automate here don't automate here right and that's difficult to do because like I say business turn up and say hang on AE I've got this AI thing so this AI thing should be able to all these bits and faces so I want you to take this AI think and solve that problem well we don't really understand the problem let's see if we can go and do like even a small component of it and like do it not even by hand but like just with normal tools before we automate no has to be done quickly done last Fray in fact I told the board it's already done
okay then but let's try to the more we can fight against that the more we will stop to generate bad automation right because bad automation timly ends up cosing us more further on down the line then if we're just taking the time in order to truly understand the problem and that Auto whenever we're trying to move from norming into performing rather than right at right at the start and the other thing that can help in this perspective is making sure there still a human in the W so uh if I interestingly I used to use this slide s many years ago and there that used to say ml model no just says model so whenever this
comes in right whatever it is you're doing doesn't what doing comes through this chain right and then whatever technical system you've got will have a certain confidence level and if it doesn't have a confidence level while then unfortunately you're going to have to work out what components of things that it does you have confidence in and in fair that yourself but if the system doesn't have a certain amount of competence involve the human like if you have too much automation that is allowed to run Mar by itself without any human involvement that's where you get in the scenarios where like chist strike I I don't work for stri CH strike I haven't I don't particularly know anybody those
work for C strike but I would be shocked if there weren't people inide say yeah we had a couple new misses were just like that right so if you were to include a human in the loop as part of this right well then the human might be able to identify what's going wrong here and I would also suggest that from this perspective even the things you're saying okay well look I've looked at this I've understood this problem like if something is very low confidence will involve human but even if it's high confidence I still want to Q see what's going on in here right so even from a sample perspective take a certain am of
things that are in there and then once a week once a month once a quarter take five of them and then have a human look at it and go is that still do the thing that is meant to go and do right there's this fallacy that that you'll hear in terms of like well no complain is probably okay no you're just continuing to pile straw on top of the camel's back and one day one will be too much and the camel will fall D and say did you not notice that the camel was overing with straw no because nobody was nothing of what was going on if it was coming out here we just blinded we just blindly
believe the automation so I would suggest that we don't do that we try to reintroduce the human into the loop here possible even if it's not in the like the the critical path right but even from a sampling perspective and then say well human is just least going to check that it's do the thing is meant to okay so a couple of other examples but we'll talk about this very Brickly um other other examples right so you have secm talk about secm earlier so other things that can then cause bad automation then trigger security systems right so copying AES or. files around the around the internal of the network looks a lot like l movement terraform
and AWS is one right sping up assets from an automated perspective looks well like coin mining or resource consumption um pretty much anytime anible uses Powershell for almost anything people go what's that doing that's not me to be doing that anible um patch management when it's trying to Stage files that can also look like lateral movement um security controls whenever they are attempting to do domain lookups for things a lot of the time that actually looks like looking for the domain in which case then that can look like CNC then you've got anyy pound Solutions in there as a bit you know s of more of a bu be whenever you do have uh admin
accounts changed into shared accounts and shared accounts are used at least whenever somebody was using their admin account in order to log into something I knew it was them or at least it was supposed to be in whereas now they using the share to go all the way back into the system trying to find out well hang on a minute who actually went and did that and if those logs aren't being retained for long enough in that system you don't have a data Lake in order to store them in you're like if you did that that's not particularly helpful right um that will then trigger you to go and do much more digging into some
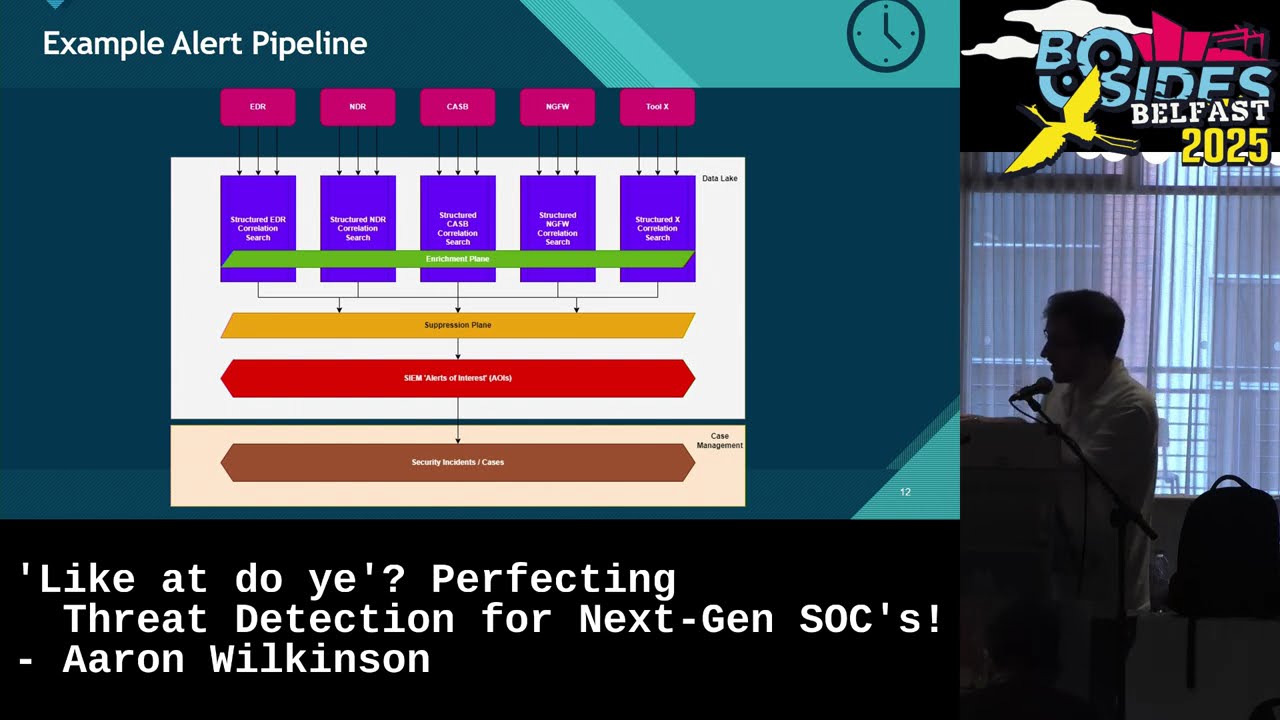
other security system that had validated was actually okay rather than knowing in advance it was okay uh some takeways so high level concept we come back to work right so from a from a good automation perspective like no tool will guarantee that can supply you all the information you need in order to make proper decisions like you will have a a stable of tools right where they're doing lots of different things but they can all be used together if you just have something to N Them All right so if you got an EDR if you have a you know a proxy if you have some ass monitoring if you have all these other different tools right if you
can bring all those ear Le orchestrate those inside a sore well then you're going to be much more able to go and make those decisions from a sock Bas perspective rather than being limited and what it is that each us individual TOS life you going through and you don't necessarily need to jump all the way to sore like of all the technologies that are available I went through you know nor detection geni right s is probably the one that is more focused towards um being good automation right like if it turns into bad automation what you're doing then there quite intentionally a human has done that so you know that's to G back to the human training
protective um but you don't necessarily need to jump to your sore right sometimes people think okay well that seems like a whole project and a whole staff and things like there are sometimes you can get workflow engines those workflow engines can come from uh existing tools that you've got sometimes they're bolt on so you just get them for free because they want you to use the tool so if some of those workflow engines existed other tools you have access to try that first demonstrate that that work well inside that tool and maybe that can make a case for sort a wider sord platform um but s is largely the solution to a lot of this right
because it is a security analyst or security engineer security expert driven automation where you're deciding this is the thing I want to automate this is the thing I want to go and do rather than the tool say okay let that tool out it and it will decide uh another one which kind of linked to the sore component is the advocacy for apis ultimately in the end if you're using a lot of security tools and then those security tools don't allow for the richness of the data you get inside the UI to be exportable from the API into either a DAT lake or into your sore well then you're going to be hard blocked under ability actually go
and do those WIS or solve those things now that has to be up to kind of us to a certain extent but businesses to a larger extent right because like at buy time as our buying decision right I need to make sure that becomes a component of the buying decision let me see what your API is like what data can I get from it no not the docs I need to be able to see what it actually does and then validate that you get the necessary level of information out of there otherwise what you will find is that you will come up with a great theory in terms of ah look I find this thing is constantly FSE
positive so I take the data from over here it's in the console then if I marry that data with this data then I'll know where it's coming from and then we can just automate all that way because we know what it is uh well no I know the DAT is in thei but you can't get that out of the API it's just not available right well then when are we going to have that maybe never so from that perspective trying to advocate for the tools that you're using to to invest in their apis because large scale to large extent those that API investment isn't a natural thing for them to go and do and drives you out of their platform right
but when you want to then go and put it in just work um the other one is being repetition to being in the room right I think that is quite important the security is involved in in security tool identification or security tool roll out across the Estates um even if you don't think it's going to be involved the chances are it's going to come back and do something inside your Environ later so probably want to be in the room whenever that's being rolled out being or decisions are being made um and then just again to do the expertise right so new technology is going to come and see this right new technology has yet been
generated or yet been provided that is actually just going to do all of this for us so from that perspective we all need to be the big blue unit right so we need to be this guy we have tools some of the tools we'll have some tools we want but ultimately is about the skill and the expertise of the specific individuals that are using them that is going to decide whether or not you can solve your false positive problem right so don't turn to tools turn to people those are the people we need um in order to solve this for us all and that is the end I think we have some time for any
questions