The Emotional Rollercoaster That Is Penetration Testing

Show original YouTube description
Show transcript [en]
hello everybody thanks for joining me uh my name is kurt palmer i am an i.t security specialist and pen tester ethical hacker with ion united and i've been fortunate enough to be employed in this cyber security industry for a little over three and a half years now not like i'm counting or anything but um really happy that you guys are here sorry i'm about five minutes late i was actually logged into the wrong uh meeting room so i had to reconnect and log back in upload my slides but i hope everybody can hear me um so we'll just get started right away my talk's only a half hour it's not uh technical in nature it's basically just my
observations uh working in the cyber security and pen testing fields for the last three plus years um so what we'll do is i'll just do a really brief introduction i only have 17 slides so we should be fine if i take a minute or two on each slide uh we could have a little bit time left over for uh from q a um but let me hit the button here here we go so who am i the typical who am i slide right so i'm 42 years old now are you 42 years young maybe it's a better way to say it uh i so i've been in it for about 20 plus years now uh proud
newfoundlander and living in alberta so i moved to myself and our wife and our two doggies in the screenshot there uh we moved to alberta at the end of 2018 so very very happy we love alberta weather's fantastic summer's much better than newfoundland so but i do i do miss home of course so no kids two dogs that's roman on the left and junior on the right and roman was rescued so yesterday i believe was national adopt a pet day so if you're looking to add a member to your family i would recommend going out to the adoption shelters and there's lots of lovely lovely dogs and cats that need a good home so uh quickly
there we go sorry third slide uh my background so i graduated way back in 97 uh maybe some of you guys probably weren't even born then so what i i was interested in computers but didn't really know what i wanted to do so i enrolled in a three-year it program and part of that uh had a um about an eight-week 12-week work term so i was lucky enough to land in a couple of uh private k-12 schools and then i turned that into full-time employment for the first seven or eight years of my i.t career and of course during the during the three-year it program we touched on everything so there was programming networking security and windows nt
at the time um so that's where i kind of got my start into security and once we had our first linux course i was i was hooked right away love the command line and so i was a big linux fan and google ever since so that's pretty much my background i've been been in i.t for a long time uh and you know three to three and a half years ago i was thinking about switching from it all together and actually my first ever b-sides presentation was two years ago uh besides calgary and uh so my talk was about how i transitioned from an i.t generalist to cyber security so if you want to google that and check it out i
can send you a link if you need it and youtube has a really funny screenshot a thumbnail of me i don't know looking looking sideways or something just it's hilarious so check it out all the reasons why i don't really like being on video and cameras and things but that's it no worries you sometimes you have to step inside your comfort zone right so next slide so we're just going to talk about um and i'm going to talk about some of the highs and lows that i've experienced during pen testing and no one really teaches you or explains that to you when you're in you know pentest school or where you're studying for a cyber
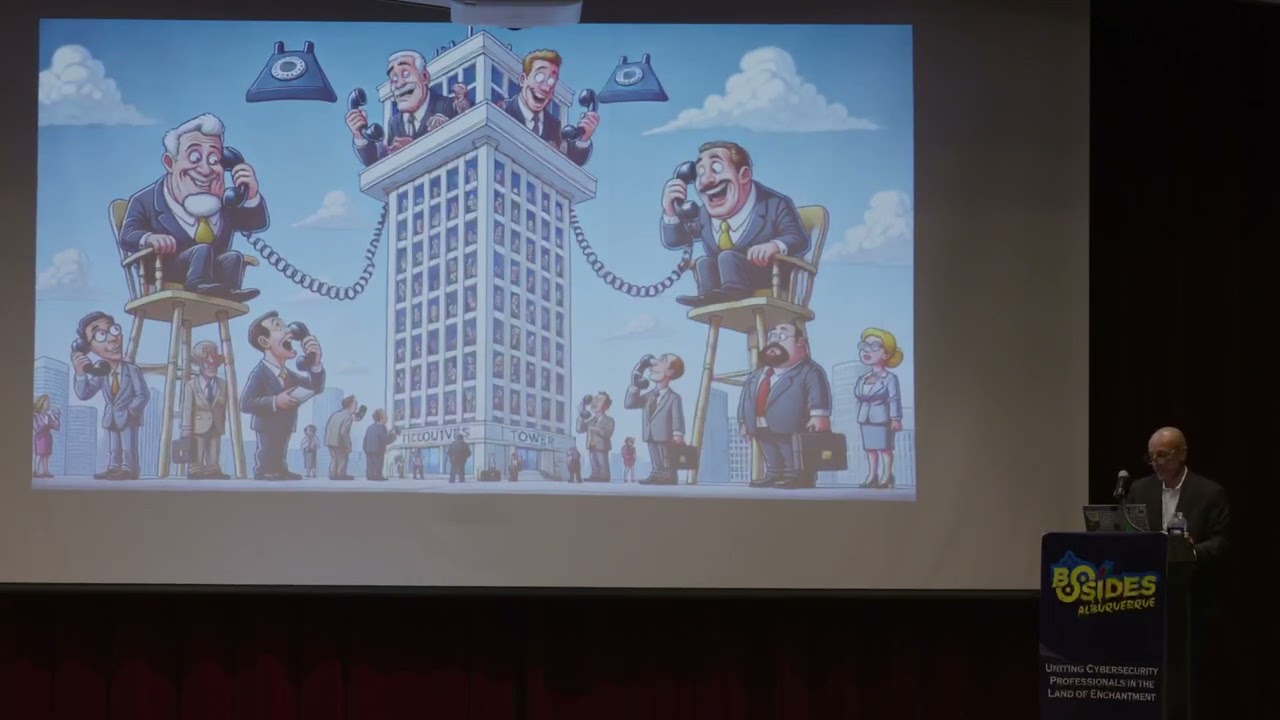
security certification you want to be a fantastic so they're just some of the things that i noticed and and things that i get worked up about or or you know nervous about when i when i do these pen testing engagements for clients so unfortunately the slide animations were not supported so normally i would have probably had the start and then the end and things you know those little areas would have been circled as we go so you kind of just get the full screen right away but so let's talk about uh scoping calls right um you wouldn't really think they would be stressful but they are for me and uh nerve wracking i guess sometimes so
you know even when when you start a scope and calming started a pen test for an organization uh you know you're excited right you don't know what what the organization does what they're all about you don't know their security posture security settings they have in place so sometimes when they talk about we have a new project and we have those discussions with the customers and we ask you always phishing in scope and then they say no so you know boo bummer um that's always the first area so you know you start off being really optimistic right you start down here in the optimism section and then you find out well fishing isn't in scope and of
course fishing is one of the main ways that attackers gain access externally so now oh yeah i kind of have anxiety thinking well if that's not going to work well what other options do we have right so the next option is password spring and and maybe their password guessing is another common way that attackers and security professionals gain access to systems and networks externally um but of course you know sometimes during those conversations they take our recommendations from previous years and they uh say well we've implemented a 12 or 15 character minimum password policy so then you're like ugh that's depressing because you know you you really want to see from an attacker perspective you want a
security assessment perspective you know maybe it's nicer to see the default password policy of seven or eight characters so when you it's great that the company um accepts your recommendations from previous years but then it sucks because it makes password spring a lot harder right it's hard to come up with 14 and 15 character passwords that users are might most likely to choose so that's disappointing then you're kind of in that ah that dreaded sort of denial phase uh you know phishing's not in scope password policy is very strong you know you're in trouble right away right so so scoping can be very uh stressful you know highs and lows maybe there is phishing maybe
they have a weak password policy so you have those ups and downs and then of course the last thing that sometimes we talk about is the testing window and oftentimes companies are okay with nine to five monday to friday but sometimes they'll mention you know to be safe it's best to work after hours so that's very disappointing and depressing just because you know i'm used to working monday to friday night at five of course we'll work after hours if need be uh whatever the customer wants but it's just uh it's a little depressing when you think well now you have to work after hours it kind of screws up here um your sleep schedule uh and your typical work you know monday
to friday type thing so those are some of the areas in when when you do uh scoping for customers those are some of the areas where you can experience some of those highs and lows right and this is pretty much what the slide is about so okay so you've had your scoping you've been assigned your project and now you want to start doing the constants or the reconnaissance or the information uh gathering phase so maybe you'll check the dns records right that's always an important area to check and you see systems like uh you know subdomains like web like webmail.clive.com or mail.client.com or remote.client.com so that can indicate um that there's probably an exchange server
so there's you they're usually juicy targets because there's a lot of opportunities for password guessing bypassing multi-factor authentication and of course there's some of those uh really critical remote uh code execution vulnerabilities that that came out with exchange last year like proxy logon and such so really exciting to see you have those dns entries and then of course the downside is um that they don't resolve or you know there's there's no ip behind them right so mail and webmail uh and that's a typo it shouldn't be admail this would be it should be email but but there's no ip address listing on the other end so you start off in your excitement right you're starting a new
pen test you're doing your information gathering your recon and now it's like crap you know the the dns settings aren't what you wanted them to be uh and another time it was working on a pen test and the company had been acquired by another organization so now when you're doing your reconnaissance you have two sets of email addresses user accounts usernames it's basically double the work so that can be really challenging also and you know it's it's causes more work for you uh but it can it can make me feel sad or depressed or or anxious the typical the typical uh you know emotional rollercoaster phases that i feel right during during these security projects and of course the
other thing that can be a real bummer sometimes is you find out who the organization is and you realize that like i mentioned before they do year over year over year testing with us or another company only to find out that they they've implemented a lot of your previous pen test findings so that's just going to make the job that much harder and that much difficult so again now now i'm feeling uh you know i don't really know how to pronounce that word exactly properly i think it's uh capitulation and so i had to look it up but it means you know basically like you want to give up right you're in the depths of despair
so that's um often disappointing when you're doing your information gathering and you come across issues like these so you know you're really high really excited to start a new pen test and then you're down in the dumps again but you know there's the ebbs and flows right testing so the next one here is um external testing so you've done your scoping you've had your scoping calls with the customer you realize what's in what's out of scope uh you've done your internal you're doing your external information gathering and reconnaissance now you actually want to start testing so there's some areas here that i noticed that that i kind of hit that roller coaster right so the first
thing would be the password policy that we talked about that earlier uh maybe they've got a really strong password policy or maybe we talked about the length minimum length requirement but maybe what about the lock of the threshold so my way they only allow you know three bad or three failed password attempts in 30 minutes so now you can really only do two every every 25 minutes or every 28 minutes so maybe you can only do for an hour you know times 24 hours so you can only do 48 a day so that can really slow you down i would other times you may be on a pen test and you could be really optimistic and you
start and sometimes the customer says well we have a 10 10 failed lockup policy uh 10 failed bad passwords in in 30 minutes so then you can do eight or nine uh let's say eight every every 30 minutes 16 an hour times 24 so you can do a lot more that way so sometimes it's depressing when you find out oh you can we know what's your password policy and we often guess ask the customer for the password policy because we don't want to intentionally lock it at any accounts right we don't want to impact any user accounts or the organization so that's depressing it gives me anxiety um and then sometimes you'll get lucky right you'll perform password guessing
password spraying so i'll just you know password spraying is just trying one password against all of the accounts uh so that that's very effective sometimes season in the year has been really effective for us so you know uh spring 2022 might be a good password to try winter 2021 summer 2021 summer 2022 those are often fruitful uh so sometimes you'll guess the password you'll be really excited or i'll be really excited uh thinking yeah it's great now i can i can gain access externally but then maybe there's no there's no citrix or maybe the vpn requires multi-factor authentication or there's no vmware horizon desktop or the account that you access uh hasn't been granted those privileges and that's
happened to me a few times where i'll guess a credential i'll try to log in and you log into citrix but you have been those applications like remote desktop or whatever haven't been published to you so that's really that's a real uh um hit to your emotional state sometimes or for me it is anyway and of course the last the last option is you know when you're doing these coping calls maybe we find out if they have mfa or maybe they don't tell us so you capture a credential you're all excited you guess the password uh you try to log in and then you see that prompt that says you know sending the uh the code the to the user's mobile device
so that can be really tough and sometimes you can think well maybe we can bypass mfa by sending them by capturing their credentials and then logging in right after them sending them that rogue mfa push to their mobile device but sometimes you you find out that the only option available is for the user to enter the code so the push notification option might not even be available so that's obviously really disappointing depressing so i'm kind of hanging out in the in the lower area of the emotional rollercoaster but so what i wanted to talk a little bit about some of the lows and then we'll talk a little bit about some of the highs so
um the next oh here we go next slide so password guessing right so i'm thinking back you know three plus years now i'm trying to remember the first time that i achieved some of these sort of uh goals i guess when you're pin testing so the first one was password attack so i definitely remember my first time on a project by myself performing password spring externally uh using i think i was using burp suite actually a web application tester and i was actually able to guess passwords it was really exciting and i remember we had to go out and maybe get groceries or something and i didn't want to leave because because i was actually you know
guessing that credential i was actually about to break in externally so those things are are really um high points for me and uh so you can see you know you start off maybe with your um i can't really see that slide what is that you start off with your um excitement and optimism right and then uh so then when you do guess the password now you're on that high right you've got that thrill you're thinking yes you know i've got credentials now i can move the pen testing engagement forward a couple little screenshots here this is just an internal password spray using uh invoke domain password spray which is a powershell script and down here the size is probably
pretty small but this is hydra doing external password spraying against autodiscover against the uh on-prem email server and you can see here spring maybe spring 2019 uh was the actual password i think i have it over here in bigger size but uh so as you can see it is really exciting for me and it still is really exciting for me when i actually guess a password uh just because uh you know it's exciting right you've guessed a password that user has chosen and in this particular screenshot the user had chosen secure one two three four five six so that's not really a really secure password at all uh the next slide so here here's a big
one for me and this is really exciting it still is um and so i might start off on an internal pen test with anxiety or fear or worry because maybe in the scope and calls the customer says you know they have some really advanced endpoint detection response software like palo alto cortex xdr for example tough tough av vendor to bypass although all of them have their weaknesses so when you actually uh and i definitely remember the first time i bypassed windows defender because all those tools stopped you from doing the job right they stopped you from loading powershell scripts in the memory they stop you from dropping executables or executing your malware trying to get
command and control established so av we're always battling with av all the time never stops and then it always changes what might work today won't work tomorrow right and vice versa so the very first time you know i started off with with anxiety trying to battle with palo alto cortex the slides are probably small i don't think i can make them any bigger here um but the screenshot is the palo alto cortex xtr running and then that's my interpreter session one open which if you're a pen tester you know that's usually a really good sign and time to do your happy dance but that's me bypassing uh windows defender a cortex story and then establishing using that
interpreter command and control for for remote access and post exploitation activities right so that was a really exciting one for me so then you feel that that relief right it's like okay now i bypassed av now i can get my tools to run now i can run tools like um bloodhound for example to do session enumeration and to find you know vulnerabilities with an active directory maybe you have other reconnaissance scripts that you want to run there's some there's a powershell script what's it called something recon adrecon.ps1 that's a nice one gather up information on users and groups and permissions and privileges uh i i got a question here from janna sorry are you uploading slides or
sharing your screen i think i'm sharing my screen and i did upload my slides i can give you guys a link if you want the the slideshow a slide deck afterwards like i said there's only 17 or 18 slides in it not a whole lot but if you want the slides just reach out or maybe there'll be a link or something but i'll send those along if somebody needs them so that's really exciting just just to bypass av and it still is to this day so i always get a rush my heart starts to beat and start to get a little sweaty but that's it you know i enjoy my job and sometimes um you know those are the
those are the highs and lows that i that i like so i want to share those with you guys especially for new people too when they're just getting into any industry and maybe it's maybe it's weird maybe i'm i'm not i'm not the norm uh or you know maybe it's as people do this for a long time maybe it's not as exciting but it is still really exciting for me a big one for me also was was fishing right so we we had a fishing system that i kind of overall overhauled made it better and then the first time when you run your fishing campaign you know i'm always really like nervous and it's it starts with anxiety
as usual uh and um so you run that fishing campaign you know you want to double check and make sure you've got your spelling correct i did launch efficient campaign before where i spelled the person's name that i was impersonating wrong uh and then i had to kind of quickly send the second email with the corrective name and it worked out but it was still still a big mistake so uh you know launching that campaign is always exciting and watching the information like how many emails were sent watching those numbers go up like emails opened emails clicks and then it's really really exciting when you see uh submitted data oftentimes we'll quickly log in grab
those credentials and then try to log in right after the user and bypass multi-factor authentication send them that mfa push to their mobile device that we talked about before so you know you start with anxiety but then it's really thrilling right when you actually capture those credentials um the next one so this was probably the most exciting still is always will be is when you achieve domain admin right it's not always the goal of a pen test uh to to achieve that don't wait admin access but uh usually when you do you know you do that domain admin happy dance and i've done that a few times thanks thankfully no one's i've been around to
see it but it is really really exciting it's probably one of one of the uh most exciting things about pen testing is is reaching that domain admin level knowing that you've you know you've bypassed the security you've found holes in the environment um and now you have essentially have the uh keys to the kingdom so and a lot of times i'll start down here in this really really bad state just just because maybe the external pen test didn't go well right maybe phishing the the email was sent to the spam folder maybe we didn't capture any credentials maybe nobody clicked on a link so that sometimes you start in a bad place and now you're on the internal network and
you're thinking oh now i've got a battle with av and i have to do all this enumeration and i have to try to find vulnerabilities and escalate privileges and you only have a certain amount of time typically a week or so maybe less to do this so you know and then you have to battle with av on top right so um that can be really uh really low point uh sometimes but oftentimes maybe maybe within the first hour to you you achieve domain in mid-level access and then you're on top of the world right you feel you feel great so that's really and this screenshot just shows that i created a user account called ion and i added it to the domain
admins group and then i grabbed a screenshot from my my trophy for my history um so that's you know really really low really high like that euphoria feeling that that's it's not a lie for me i it really feels like you're on top of the world and sometimes especially early on there's trouble getting to sleep at night because you're so excited about wanting to want to continue and log in the next day and keep testing right so another one which is really exciting for me and it still is like we talked about oh sorry um we talked about the highs let me go back one so that would be um here we go so now we'll talk about some
of the lows right we talked about getting domain and men we talked about uh bypassing av but now we'll talk about some of the areas that can really bring you down sorry two screens open here here we go and i'm trying to hurry just because i was about five minutes late so maybe we'll go to about 2 35 so about 10 minutes if everybody anybody has to drop off in five minutes totally understand uh so we'll talk about some of the lows right we talked about the highs uh so password spring definitely sometimes you start off you're very hopeful right you're thinking okay new project external pen test here we go and then you try passwords of all different makes
models and varieties season and year company names days of the week you know weak passwords like password one two three and and you know you substitute certain characters you try all these different things passport spring just doesn't work so that can be very disappointing um and often and sometimes it has happened occasionally not very often maybe once or twice um that i've uh read a password spray and i've actually locked into account so now you feel really bad because you're you've impacted the customer and and their environment right so then you can feel uh really crappy and so i do have a question from janice so i'll i'll answer those janice in a couple of minutes i'll just get through
these last few slides i've only got three or four more and then i'll get to any q a if you guys have any so this this is a really can be a real soul crushing low for me when you you try password spraying and it doesn't work and you try for days and days and days and it doesn't work so often times then we'll just typically uh move to the next phase of pentest which is internal and we'll note in the report that uh you know exterior defenses like password policies mfa uh blocked us from gaining access externally because you want to talk about the good things in a pen test report as well as the areas of
improvement so the next one here uh this soul crushing low i call it is application white listing so sometimes you get in a higher security environment where they've the organization has implemented application whitelisting so i'm on a pen test right now actually where i have no access to powershell so that can be challenging because powershell has been built in the windows and there's so many attack tools and techniques built around powershell so that was really depressing whoops uh when you bypass when you log in and you realize not only does can you not access like an older version of powershell but you can't access powershell at all there are bypasses i tried different things but they didn't work so again you start
hopeful and now you're you know this one here uh this the c drive has been restricted so that's group policy and also down here this application has been blocked by our administrator so those are group policy settings so now you're really in the dumps right i mean what are you going to do you have you have the command shell sometimes you don't even have the cmd.exe command shell so now you're really up freaking you have to really think other ways of um living off the land and gathering the information that you need but i mean we rely on powershell a lot as the bad guys do so when powershell's blocked it really it really um
makes for a bad day uh and here's another one this very dif disappointing i should say difficult um which is av and edr right we talked about bypassing it but then we talked about what happens if it doesn't work and i'll use palo alto cortex because it's really strong um really really strong 80 edr products so every every type of memory corruption or dll or anything you try to incorporate into the environment doesn't work so that can be really tough uh especially and and sometimes uh you you'll get your shell code in memory right you'll have some command and control maybe some interpreter or something like that metasploit you get that shell code in your memory you
finally get it to execute and it bypasses edr but then the av right maybe there's a palo alto firewall or some other next-gen firewall that detects that command and control communication and cuts you off right so you work really hard you get your av and you bypass av get your malware running and then all of a sudden it's blocked up a network layer so again really high really low right but that's it that's that's part of the job and one other area um yeah i'll get to that one may also uh the last last two slides one slide two slides um sorry i do realize we're going over here by five minutes but i'll keep it short
uh so presentations right um not really comfortable uh we can move q a to the session for track one after the top okay uh so i'll finish off these last slides and then we can do some some q a uh so for me report presentations being online doing this right now is very stressful um it keeps me up at night makes me worry i'm not comfortable on camera you know i never have i probably never will um so presenting right when you when you work if you want to study to be a pen tester that there's not a whole lot talked about actually presenting your findings to clients and that's really really important because you're you know
your pen test report is your leave behind your executive summary uh is really really important because that's probably all that the ceos the executives are going to read so being comfortable presenting is really important and it was something that you know i started at the beginning of 2019 and covet happened a year later and my job was work from remote anyway but i was in front of clients quite a bit and now i haven't really been for a few years so it's just a little harder to present because it's tougher to kind of read the room uh when you're doing things virtually so that's a big area of stress for me and especially when you're doing things over
teams or zoom or or webex and i know i worry about making mistakes or not telling a convincing story not not driving change or demonstrating the risks adequately to the customer right so that one is i definitely start on the anxiety level i'm definitely not over here sometimes it's optimistic if the pen test went really well i could be really optimistic and excited to present the findings but a lot of times it's usually a bunch of anxiety and not so much they'll make for an hour uh but then when you're done you get that relief right so you're really high really low um so it's it's nice to have that relief when when the fan test uh
presentation is over you can kind of relax uh so i do have just have a couple more slides at the end and i did mention in my preview i guess is how you can win against these apex defenders how many these really strong next generation customers who have implemented all your recommendations you know they have advanced edr software they have monitoring and learning they have a sim uh they have you know web application proxies and firewalls when they when you're up against all of these different um compensating controls there are still possibilities away and i kind of kind of feel like i kind of stuck these slides in at the end here a little bit
but i just wanted to give you uh just a couple of of ideas and most of the time for me personally when when you're trying to to uh to win you're trying to bypass endpoints and av and edr software so i just put a couple of tips in here about how to do that because if you can bypass av and edr you can run the software you want to run and then you can assess the way you want to assess and you can stay away from the antivirus software so that's a a big one for me right it's all it always comes down to bypassing av and edr so a couple of tips so the the general
theory that seems to work well lately is you need to create some shell code and you can use like msn venom or some other shell code creator for that you want to get that shell code into memory you want to decrypt it because av will will see it every time just off-the-shelf you know interpreter uh shellcode or something like that will just get flagged every time so you want to encrypt and decrypt at runtime and you can do this in any language you can use it in c or c plus plus python column doesn't really matter also if you use metasploit and interpreter like i do a lot i don't use the second stage payload so there's a
first stage in the second stage so when you use second stage payloads there's an initial communication and then a follow-on connection to to run the rest of the the payload so that that second stage connection that calling out to the network shortly after you execute a binary that that always gets caught so just use a single stage and make sure you're using valid tls certificates and you're using the state like the staging coding options like chicago ni or zutukiro or xor decryptor there's xor one i can't remember the exact name so make sure you're always encoding your uh your stages and of course you when you want to communicate when you want to establish that command and
control of communication from your endpoint to your server back in aws for example do it over https port 443 as that's always allowed outbound you also have good success sometimes doing it over dns but that can get if if the the customer is looking that sticks out like the sore throne sore thumb sorry and you also if you're going to drop an executable to the disc not really recommended but sometimes still works make sure you sign your executable uh and you populate the resources section so that usually just gives information on uh like if you right click on the binary choose properties you can see the resources and it just gives more information about the
executable so make sure you populate that make sure you obfuscate your source code also and there's a couple more tips in here uh so i always like to try to use a command and control software that's got some socks proxying built in so the metasploit interpreter you can use posh c2 cobalt strike that's another good one uh and if you can use that proxy support you can stay off the endpoint so you basically you tunnel your connections through your compromised server onto other internal networks so you attack that way and you don't drop any tools on the device you're given the compromised desktop or workstation uh use and leverage content delivery networks like cloudflare uh
cloudfront is an option that way it makes it really difficult for the blue team to detect the communicable traffic and to block it and again research common by that but pi bas bypass methods uh sometimes you might if you have administrative privileges you might be able to uninstall though it doesn't work very often or stop the service although that doesn't really work that often lately either maybe you can crash it or maybe there's a known bypass so stay up to date with uh common bypasses for these products and maybe maybe download a trial version put it on a vm and practice that way and there are tools like defender check which will actually check your binary
and see if it's malicious and you can also upload to virustotal but i don't really recommend that because um the end of virustotal where share will share your malware with the developers so i've got one slide left this is just dedication to my dad uh he passed away in september 2021 but he was really happy and proud to know that i um was accepted for my first b-sides circumference security conference in 2020 so just just a shout out to my dad i'm sure he's up there watching somewhere and cheering me on so just want to say say hi to him so that's pretty pretty much it for now i know i kind of went through the slides a little bit quickly
uh just because i started five minutes late but you know that's it it's there's it's the highs and lows you know of of pen testing uh lots of highs lots of lows and you know some some days are better than others but don't give up and stick with it and some days sometimes i've had days where i felt like um i can't do this or i'm not going to be able to do it and then sometimes you will you will find something uh you'll find a hole or an exploit or a misconfiguration and then the whole outlook changes right maybe you've found i found domain admin credentials in powershell scripts so you go from not really having any
credentials uh to having domain admin so don't give up because it can literally change on a dime but it is uh you know it is it is an emotional rollercoaster before and i said that to a few of my co-weaker co-workers so i figured it might be good uh a good option for a talk so that's pretty much it just just a half hour uh i'm not sure how i would this uh i think darren mentioned that we can move q a uh to the session track one after the talk so i don't know if i need to do anything or maybe i can just answer the questions there but um any ideas actually on um do i need to do
anything else or am i finished so we've gone over a little bit so what i'd like to suggest is that we um you can pop into the q a uh in the main stage there and hit reply and reply to any questions that pertain to you and we'll get to vivek on stage right now it was great having you kurt cool thank you apologies for going over all right