TokenFlare: A Serverless AiTM Framework for Phishing
Show transcript [en]
Thank you everyone for coming for to the talk. Um can anyone in the back hear me? All right. Cool. Cool. So today um without further ado, I'm going to do a um tooling release here in um besides London um with three things that I am deeply passionate about. Um one entry ID for reason. Uh second initial access good reasons. And thirdly, um operator user experience uh which we'll go into in a bit. But Um before that okay who am I the obligatory um head of ATSIM in jumpsec um effectively the red team lead um in engagements um helping the team the team helping me um we achieving good outcomes for clients um yeah agenda for today um what is a
serless AITM framework you know there's a lot of words here and um why do we create it in the first place and why we releasing it unleashing it on into the wild you know blue teamers in the audience might you know question me on that have good answers um during the release um some IOC's um for first steps and notes on detection and then Q&A time right so what is a serless AITM framework for like you know the audience here um first and foremost serless functions um might have a lot of names you might call it functions workers lambdas different cloud providers call them differently but basically the cloud our provider runs your snippet of code
for you. They handle the SSL, load balancing, you know, routting, CDN, logging firewall everything right? So, you don't need to do any of that hosting stuff. So, that's fine. Um, the code tends to be more lean, smaller side, you know, there's low over uh low overhead. So, it's easy on on the people using it. And the second bit about, you know, AITM, what is attack in the middle fishing? So in a sense it is sort of like a malicious web server where the users visit you and then they punch in the password um into your website and then you send it to the IDP here being enter ID. So you're logging in, you know, on behalf of the user and then the
little bit of logic that's needed is capturing the credentials, capturing the cookies and send it to your the attacker, hence you know, you or me and then you use the cookie to authenticate, right? So that's the basic high level idea. Um, so putting one and two together. So what is a like serverless AITM framework is sort of think of it as a simplest service function or set of service functions that runs the reverse proxying credential capture all that good logic for for the you know offensive person here and there's a low overhead needed because the cloud provider handles the hosting handles rooting um does the infrastructure basically for you and the framework itself is sort of the wrapper
the glue that you know glues everything together to make sure the operator has a good user experience. experience. It's easy to spin up, easy to configure, easy to use. So, yeah, it's the first meme on the deck. Uh done this 1:00 a.m. last night, so hopefully um a couple more to come. So, yeah. Um before we go into nitty-gritty of the technicals, I like to show you like a short video on how quick this is to use, right? Um so, here we we see a command, you know, python, you know, our tokenflare.py, Pi and you do a init and then you do a configure Cloudflare, you do a configure campaign and then you deploy and then it's up.
It's about 2 minutes in the in a in a video, but um I'm going to go bit deeper deeper into you know what it's doing. But basically here the init um command sends you you know sets up the environment um you know create some SSL search for self-sign um needs and also you know configure environment basically and it tells you next step is what I like you know run that right. So I'm not going to show you my API key. So the the configure is run offscreen. But then um the next step you do is to configure the campaign and which is a sort of like semi um interactive prompt asking you for what you need. Um what
you need um basically we'll we'll see here um what IP allow listing. For example, when you are testing you just want your IP to go through first. You don't want to expose it. You can configure here. And I'm not going to show you my home IP. So I'm skipping um target. So uh you can do client branding here. You just punch in the tenant. Um here we use jumpsack.com and then off um you could use um the default is office home that's similar to you know evil jinx and um lure path. Um we'll go into that later but basically um there's like eight questions the the thing will send you uh token flare will send you uh with
you know defaults sensible defaults and after punching in all the rest I think the the the last question uh it it has is the web hook URL which is where you want it to send the cookies to you um uh basically here we we use web hook site never use that in production you know obviously but just for demo purpose it's like a temporary wrap we're thing. So I'm never use web hooks site in prod. So yeah sensible defaults and um I would also have never use uh you know open to public on fraud as well uh initially because you need to launch your campaign eventually right. Yeah. So, the next thing I'm going to do here on the video
is just, you know, uh, Cloudflare, not Cloudflare, token flare status to make sure everything's good. And then we do cl uh, token flare deploy. And it's up. Shows you the lure URLs here. You know, don't try to hack my box. Uh, it's, you know, shut down already. Um, yep. So um and then we run a little deploy remote and you know it's taking 10 seconds to put push to cloudflare and then you can see the fishing page in just one second. Yep. And right um it's been deployed. Uh lure URL defanged in the terminal shows you you know five six of those you could use the testing and then we punch the URL in um refang
it. Is that what we say? But anyhow it works. It's a jumpack branded fishing page on Cloudflare. Pretty cool. Yeah. Um, if we try to give it a wrong UU ID, uh, it goes to Jumpsack Labs. It's configurable where you want the user to be, but basically it, you know, configure campaign takes care of that for you. Hopefully, um, so it shows how quickly is and how easy is to use. Um, and you know, the on on the next, you know, little video, I'm going to punch in um, MFA uh, on screen, but you know, password has been inputed off screen, of course. Um, so we punch in the MFA, you know, logs in. Where does it go?
Hey, pretty cool, eh? Um, in the real campaign, you might want to do like a one drive file um or static um like static hosting to some sort of user flow that makes sense for a pretext, but it's easily configurable. And on the right, you can see um web hook, you know, can capture my cookie. Basically, I I did change it to uh our private Slack. By the way, in case you're wondering, I'm not sending my corporate cookie to web.hook web hook. Cool. So, with that out of the way, I'm going to discuss or explain, you know, why we created this little toolkit in the first place. What sols is it trying to solve? You know,
obviously, it's quite cool. At least I think it's quite cool. Hope you, you know, agree. Think um second meme by the way. Um five power ranges, we have four problems. um usability and complexity with the existing tooling. Basically, they are, you know, many of them are a bit of pain to use to be honest. and um built-in OBSAC that is easy on the user, easy to configure and it's not going to burn your campaign in an hour by default setting and um re reliable customization because redirect has been you know a bit of a pain for for us and you know training new people on how to use it right and the fifth one right uh because
we have five power uh power ranger the fifth one is getting a talk on these size of course um right so not going to go too deep on you know the pain because is like dissing other people but it's like redirection after completing of case and has been always been clunky to configure with existing sort of um frameworks. Um, we've had full red teams run on one of these. Uh, it worked. Uh, but it was a pain lot of pain of gotchas. I once hosted like a 40-minute internal talk with our guys and girls um to teach them show them how to use like one of those. And I was like, does anyone want to
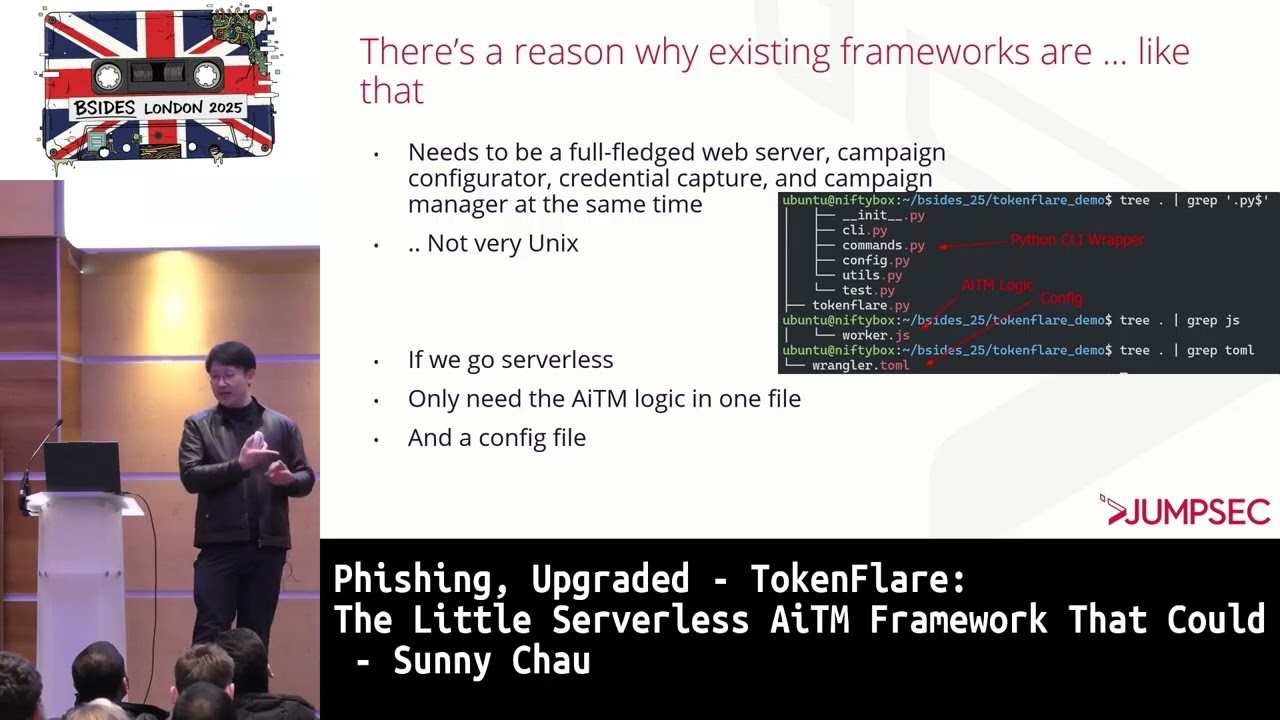
watch that to to like jump through the hoops to to to you know use one of those, right? It's opinionated. The third one is why use Golang to write something that could be written in, you know, but JavaScript and you don't need like multi- threading and all that. it it is opinion native right don't burn me right there's a and also you know bit empathy right there's a reason why existing frameworks are a little like that they're trying to be like a full-fledged web server because it's a reverse proxy uh campaign configurator because you need to you know configure your campaign credential capture is handled there so the core logic and also campaign manager you you need to spin up
stop your campaign configurate everything so it's like five six things or more in the same place so it's not very Unix and codebase tend to you know get a bit speculative about all um so if we go serless right we only need the AITM logic in one file is a JavaScript file you can see worker.js JS does that and a config file wrangler tommo does that and the rest is like the C cli wrapper so it's like all about source code there um but basically to go a little into how you build your your own aitm right if you don't like token flare build your own right how do you do it right you need to for entertra at least
you need to reverse proxy loginiconline.com you need to start an user on a appropriate you know o flow unauthorized and when they hit your lure of of course um and there will always be a final redirect is all of defined in RSC 99% in entra is in the location header so watch of that and check it in your proxy redirect the user accordingly and when it uh sets the yes off and persistent cookie send it to you and when there's password send it to you that's it you know um five lines there not five five highle pseudo code line there of course um somebody did that with um serless function a year ago um so Arios u they
PC that in 140 74 lines of JavaScript. Um check it out if you like to like customize for your own. It's like the prototype before our v 0.1 PC basically. Um it worked. Um but then our runtime is like 500 odd lines. So so what is like that 400 lines of you know bloat there for the Linux people in the audience right? Um so basically our v 0.1 worker the first one you use on pro was about 250 lines of code. Um back then we copy the entire uh worker into the cloud dashboard. Click deploy and it's up. You know that's that quick even quicker than you know what you saw there. It's like before you could pour a cup water it's
done. And uh recall like usability and complexity. I I I would argue like copying something into CloudFare and click deploy is far easier than you know um trying to fight with the your your infra um and also you know what you saw there with token flare is pretty easy. So consider that solve um but then OBSAC right if you run that sodario um worker there uh on cloudfare today it's going to be burned like in half an hour I can I can guarantee it would be malicious. So you need some sort of obssec uh what is there burning your campaign right? If you work with evil jinks before, you know there's a blocker for evil jinks. You need to
block certain bots. You need to block certain ASN, for example. Is it defender? Is it um so and so Michael uh the Google equivalent or whatn not different user agents and you need to block the non-lure uh people, you know, maybe it's the sock trying to see what it is, right? So sorry, but not sorry. And also you need to redirect maybe restrict to a certain browser. Maybe the company has certain you know edge um requirement or maybe a mobile browser requirement you want to you do that and on evil drink it's not easy right so these stuff did us like 100 lines of JavaScript basically we we wrote that it's more or less static so it went into
v 1 uh 0.1 uh which was like 250 lines we were happy for a time but then you know we need more we want more right as red team we want you know the campaign to be interesting thing to be, you know, sort of like customized to our client. We don't want the user to just see like a generic u Microsoft login and then goes to office home afterwards every time. Right. Right. It's like a pretty me user experience if you ask me for the for the fish person. So I I want them to have a good user experience as well. So you want client branding, you want, you know, sensible place for the unoffic
unauthenticated UR redirect. So if someone comes in without a valid UID, you want them to go to perhaps the client's u sort of homepage or maybe some place, you know, Rick roll them a little. Uh you want IOC, but like some some place sensible, easy to configure, someplace sensible for final redirect. We've gone through that already. Um maybe it's a one drive document, maybe it's a Google drive document, maybe it's something I don't know. Uh it's up to the pretext. And you want the sensible look and feel for the URL, right? for like if you fish an engineer if the um uh if the if the you know the the path is get cat API uh query you know uh uh
some sort of like bre equals British shot or something you want that you know or or maybe it's more sensible like um devops um authorization query um infra equal whatever so you want that and also I I don't want to stick with like a static lure because it's going to be an IOC soon um I'm or the default uh uh uh thing would be an IC soon as well. So I want to be able to configure that. So um how do you do client branding easily? So um the common quote common trick is basically if you swap out the common word in the URL with the client's um domain for example jumpsack.com here um you would do it do a client rendering
easily. So it's like just one line um not one line but three lines right and you want to be able to do like congressional exit bypass for example uh this something I've mil for with mil for entire year it's like um thing we blew up around Christmas last year basically um showing how to use um in company portal to bypass compliant device restrictions and um um thank you to Benjamin uh he wrote a uh thing that you combine token smmith with mital with evil jinx um like 3 days data to show you know we can incorporate some of these bypass into you know fishing workers. So no thank you uh big shout out to you man. Um, another some some of
the things might be, you know, you might want to use a special use agent, maybe Chrome, maybe Edge, maybe mobile, whatever, uh, to to to deal with the cap in place. Um, usually is a mobile that's weak, but sometimes the Mac you want your worker to um, you know, do that and ensure device similarity basically, right? So a small point around you know why we need condux bypass for the fishing worker is because the it's actually the website or your malicious site which is signing in on behalf of the user. So essentially it's not the user checking against entra for compliance things but rather your malicious website checking against entra. So if there's something a user
has but your website doesn't or maybe the profile doesn't match and will block you and and you know you won't get your cookie. So yeah that's why we need the bypass right. Uh so we have like many many things we want to do many many things we want to configure. It's all not very not very easy uh not very difficult on its own but it starts adding in complexity. So we bloom to like 20 something variables we need to manually configure in the cloud dashboard and when we try to troubleshoot something trying to troubleshoot in a you know uh uh in a text editor in a browser it's like a poor developer experience right I'm a
vim person so I want to work with vim right can I have this right so and there's not infest code right uh it's not maintainable and uh uh although we had sort of like a quite clunky cloudare worker we've got working uh we can customize our campaigns we can bypass stuff it's difficult to use uh it become clunky at a point and training someone become difficult right how do you explain um you know how do you get those 20 variables right like another you know half hour video maybe but I don't like that okay the third third one the four the fifth one get a talking b sneaking in there um so how do you train someone
on the new stack um I was looking around how do you do development on like cloud workers and um wrangler came to rescue So turns out um basically Wrangler is the CLI for um Cloudare workers. You could run them locally on the server. So you could run actually Cloudflare worker on your VPS or maybe you could push them to Cloudflare. So you could do development on your server and then push the Cloudflare or maybe you could push it to Cloudflare and then write write some changes and push again. It's a simple workflow and then you could version control workers easily, right? Uh basically locally you run you know wrangler dev uh with with the flags and
then um on cf you wrangler deploy right and it takes one wrangler file for variables which is great uh again for configuration you could uh write all the comments inside wrangler tommo file and people will understand and I wrote a read me explaining what the commands do for our guys who were joining team because we're having good year um you know we need train new people and how to configure the tommo file was like about 10 20 variables was good and sort of okay but then I have guys coming to me hey Sunny um how do you use this thing I'm like read the read me where's the read me so so okay we need to do better right um
so then that came to sort of like the I need a good team lead UX because I don't want I want the guys to you know learn themselves but learn set easily then and then if they're comfortable with the CLI they could you know move off to the manual approaches to configure the worker and the tommo file manually Right. So the you know Python files are uh entirely separate from the ITM logic. You don't need it. It's basically there to configure the dependency set of environment uh ask you the configuration questions um show you what the URL is and you know sort of give the guy a pat on the back because you did something
cool very quickly. So it's like they have a good user experience as well. And um experience operators they're free to do manually change the whatever in the workers.js JS file change the you know wrangler file to file easily right so so it's like the best of both worlds and um before you know the next part you know what's the token part of token flare right so you you you can see here we would um receive sort of like a code variable from um from token flare as well so that's how you redeem authorization code um from like the oaf flow if you're interested um have a read at the docution yourself I'm not going to go into details here but u it's there
uh when you need it. work in progress and then you know hey the jump guys have made some very cool tech why are you unleashing it on the wild in the wild that is it good enough that you guys you're keeping it to yourself you know you you're doing it for your clients that's fine are you creating a risk for the you know community at large or maybe general public by release by releasing this so I've had a you know not little amount not a small amount of juggling or or struggle before I decided to make this public uh But I have a good reason right a couple of good reason in fact first one shift the narrative I think
the browser 205 is the new frontier versus endpoint our experience we've run we've run entire red teams without touching the user endpoint uh both in hybrid environments both with cloud native environment the red team can do without a C2 entirely right in multiple red teams um and from TIS and from our own you know IR work we know threat actors like to go payloadless so the token or the cookie centric approach right why because you could do initial access um get the SSO and then SSO into the VPN and then tooling in Cali is you're in a happy place now or maybe you know even one of our favorites ask for VPN from help desk uh they're very
helpful um sorry and look for a VPN installer in SharePoint this is one of our favorites as well or maybe search for one with Olen uh is out there um so when I went to a red team conference this year so eight out of 10 uh maybe a bit ex exaggerated but eight out of 10 talks were you know C2 binary payload talks where very hardcore Windows internal stuff and one of them was a cloud native talk was mine and uh the one last one is AI talk unfortunately which is a good AI talk but you know can see sort of the still how the industry is seeing it so yeah that's how we want
to push a narrative shift in this areas and also level um you know reason to level playing field if you have gone to sort of the fishing kit um commercial fishing kit threat hunting talk earlier I'm sure you know the threat intel threat hunting people in the audience would know Christian kits are super popular being sold on dark web day in day out they cause a lot of havoc in the in the wild but there are not a few plugandplay open source things I want to defund those people who are selling fishing kits as well u and also I think ors and consultants should be able to spend more time focusing on the pre-tax creation not not battling with
infrastructure because um finding um gaps in people process and technology is is I think how adversary simulation bring value. Um I think not you're not showing you know your client how good you are at setting up evil chains by bringing them value. You're showing them like how you get past some defenses to bring value to them. So so that's my my my belief that lowering the bar of entry is uh not just beneficial but essential but my belief uh feel free to have a chat you disagree that's fine. And the third part is uh we actually this is our first party TI we seeing threat actors using workers.dev death on real campaigns. So as you know th simulators
it' be good to simulate some of what they're doing as well. They're using it as sort of like a uh reverse proxy more than a m logic but you know it's to the user is the same or to the threat for the threat hunters very similar defender very similar right and I think reason four it's generally cool tech I like to share with everyone is uh something I've built I like it I like to use it so um you could deploy on VPS yourself too uh so if you don't like to push on cloudfare because it might be you know bit iffy with the TLC's don't don't use it on any you know any unorth authorize
people uh you test it on your own clients or your own infra but if you like to deploy on your own your own VPS as well uh you could configure SSL gra and then deploy local deploy locally it's as simple as that two commands um so here's a public release uh we flip that to public um two hours ago um feel free uh to use the URL instead of QR code because that might be iffy but you know it's not give it a star if you like it if you enjoy the talk as as well. Uh we appreciate uh we'll come with a companion companion blog post as well as a detailed fleshed out wiki sometime
later as well. Um also you know we'll we'll put the link back in the end as well. So if you don't catch it, don't worry. Right. So some love for the defenders and the CIS admins and the blue team is in there. Um IC's and notes on how to detect or block these things. Right. Um obvious um header uh has you know X token flare is super obvious if you look into entry locks um use agent token flare 1.04 for you know authorized testing only. Um look for these um you know mark these as risk and um fortunately um you know if the this script kitties basically if you know a bit of that you you can you know
ask chat or claude how to get rid of those so it's not entirely you know fail safe um for better ones you know look for workers workers.dev depth in lengths in emails is genuine genuinely a good a good shot for me. Um I'm sorry good shot for me. Uh default URL parameters is verify me uh query u ID equals it's another good one but the UIDs we randomize every every campaign. So unfortunately uh it's dynamic and sign in from Cloudflare ASN. Um that's a good one. So why do you does your user need to sign in from cloudflare unless they're using warp to to access your you know corporate infrastructure which I don't I don't I don't think anyone does
yet uh maybe someone does uh but but maybe like one one one person in the audience does that for the rest you can block you know cover asn or alert there at least advanced detection we have some you know content on our labs uh our MDR experts are working on some you know bpoke stuff uh for token flare specifically uh to offset some of the harms D basically but yeah and also um [snorts] not for advertisement but some of the um defensive kit I've seen uh in in in in B size with us today. Uh basically push uh they they they can detect and block our thing. Um I'm not going to talk about evade evading them on stage. Uh happy to
have a talk off stage uh if you're interested. Uh but I have had a good chat with them today as well. Um so basically um recap we unleash u token flare python depend uh deployment wrapper right is basically a deployment wrapper but the the core logic is one javascript file and one tommo file uh written javascript um same stack has been used for a year and a half um core stack at least in our own production red teams been very successful and um here's a link if you're interested and >> [snorts] >> um before the end um acknowledgement um thank you for Tom in the audience Max in audience uh Dave not in the audience um and the entire drumstack
team without you all um I wouldn't be able to you know um do what we are doing here today and also so Dario um for creating the pro prototype um starter worker that started it all right um features to come um to be honest many more I wouldn't uh wouldn't be comfortable putting into public release like uh a pass key downgrade attack um there's another good sh for me if you want to block this um put a conditional access policy that allows that requires the user to uh agree to a terms of service before they sign the first time. It's like like one time for the user but um for the workers it breaks the logic
completely but I'll find a bypass at some point but it's super super super Microsoft thing for them to break like break the by TC for for a reason and um maybe builtin turns out we capture static HTML uh response but about for we need a we need cool art for the repo if you looked at it it's quite bad but it was just marked down right so yeah um that's it for me uh thank you everyone >> [applause]
[applause] >> Uh, thank you. Have we got any questions from anyone?
>> Happy to take any. Um, gentlemen there. def coming your way. >> Have you got any ideas for good defenses against this kind of stuff? >> Um, are you asking about like defenses against against this? >> I mean, obviously you're designing it to bypass those defenses, but um if going forward like 3 years time, what would you expect um to be reasonable defenses? >> Yeah. Um I think passwordless uh aka pass key is the future. Uh here I see you know pass key down quote unquote downgrade attack but it's basically if the user can click I don't want to use a pass key clicks that for the user but if you restrict them to use it I think you
know in three four years time I think that would be you know for ultra secure uh requirement environments that that would be you know the the the way to go. Yeah. Cool. I hate to ask the thorny question, but how does this sit with their terms of service? Are you likely to get a nasty gram from uh from Cloudflare for doing this? >> Yep. Um I've been talking to through their red teams um earlier this year. So the long and short is don't put anything production like production production workload like your company website on the same place you host this. Um yeah, from us on stage I'll say we haven't gotten any um abuse abuse uh notice yet. Uh but yeah, if you
use it uh do it at your own risk, do it at your own infrastructure or authorized testing only. Yeah.
>> First of all, thank you for the talk. It's really interesting. Um, as a fellow red teamer, I'm always looking at different ways to, you know, do fishing, initial access and whatnot. Um, comparing it to other tools like evil jinx, the barrier for entry, let's say, to, let's say, clone a page is a lot of the time fish fish lip development. How would you compare token flare's approach to that? >> So, um, this is a token flare is a bispoke kit for entra ID only. Um so if you ask if anyone wants to ask about Octa or the other IDPs um we have other kit for that not releasing it yet or anytime soon to be honest. Uh but um
fishlet creation u we do it we we do away with that entirely uh it's basically inside workers.js if you like to tinker but um all the as most of the operators need to create a campaigns there in you know u token flare configure campaign. Yeah. >> Okay. If there's no more questions. Oh, there's one.
>> Hi. Um, yeah, just a quick one. I think it's quite cool, um, that you're using, you know, AITMs for fishing. Um, I guess is there a plan for you to port it to Azure functions instead? Um, I'm just thinking because of emails, right? like I I don't feel comfortable sending a workers.dev. Obviously, you can send like a CDN redirect to your workers.dev, but is [snorts] there any plans to use the Azure functions for example? >> So, uh as it is just 500 lines of um JavaScript uh just like going back to the it's it should be straightforward to port to ads or Azure. um should be um the the the deploy functions is basically a wrapper
on a wrangler command. You know, it should be simple, but no plans yet. Uh but should be simple. Yeah. Cool. >> Well, if there's no more questions, can just ask you to show your appreciation one more time. Thank you. Thank you.