Moby Dick: Stories from going after phishing sites
Show original YouTube description
Show transcript [en]
started with uh alan newland's talk on moby dick stories from going after fishing sites so i'm sure everybody here has received a phishing email i know i received plenty of them so i'm looking forward to learning about some of these interactions that alan has held with vendors and other hosting providers and getting these feedback taken down so uh thank you very much alan hey hey so let me see let me share my screen uh or let me see yeah well
all right so me crap all right so all right so this is my uh talk moby dick stories from going after phishing sites the original uh talk the original title that i had when i um when i gave this actually a month a month or a year and a month ago or damn it a year and a week from now so a year ago from like the 21st of this month uh i gave it at the local boston security meetup and um actually funny story the picture here is from that meetup um so anyway you may be saying who the hell is this guy i uh work help desk for a hospital network in massachusetts i mean there's only
five of them i think so you know you have a 20 chance i guess of you know guessing it right um for about six months i worked uh four days a week tuesday through friday with the security engineering folks uh in at the data center in like dorchester and uh when i'm not at work um most of the time i do security research uh going after phishing sites and finding other interesting stuff like a like open directories with weird stuff um anyway uh on twitter i'm uh a neon i know rather creative you know anyway and uh according to thug crowd a long time thug safari contributor and skilled pirate treasure hunter so anyway so what do i do i
monitor certificate transparency logs using search stream which is this utility that monitors certificate transparency logs and turns them turns the binary data into ascii text and so i dump that to a file and i uh every so often usually once a day i'll separate it into a daily log because it's time stamped uh you know to 20 uh 11 12 uh t and then a and then a uh time stamp for like the time of day and so um in 24 hour uh 24 24-hour time format and so i look for certain keywords you know apple.com icloud.com apple id the various misspellings because of course you can only uh you run out of you eventually run out of spellings
and so you have to start it's it's like modifying passwords you know replacing o with the zero and what not and so yeah and so i'll throw those domains into multigo get the hosting information and um domain information who is start of authority all that jazz and then notify the relevant parties on twitter so if it's targeting apple it's you know i'll tag them on twitter i'll tag a bunch of my the fellow security researchers to check it out and then usually the hosting providers will be like wall submit an abuse report like all right fine fine so like i said what do i find well lots of interesting stuff um fishing kits targeting dating sites
for over 50 uh over 50 people um fishing kits targeting social security folks um and mostly and in one instance a person who left an entire backup of their website that was like a 10 gigabyte zip file and um yeah uh i probably don't have to tell you what form what type of text that is at the bottom but um anywho lots and lots of open directories as well and um so my first story uh aws so basically uh about about a year and a half ago now uh middle june or middle of july uh of last year i found a fish panel a apple fish panel uh basically when you go to the main website
it it throws a 403 but if you go if you add uh slash admin to the end of it it brings you to the admin panel and it's you know brings you to a login for the admin panel and it turned out later that the actual configuration for the kit is in you know url dot config and it gives you like the exfiltration email address the email address that the results appear as so when you if you as the attacker get a email with phish credentials the from email address will will have whatever is in that value and so so i get asked by amazon to submit an abuse report because the ip resolved to
a aws system and so um i get this you know thanks for submitting the abuse report we've been doing our investigation into the source of the activity and the content you reported uh we'll notify you once this case has been marked resolved thank you for alerting us to the issue and so two hours later i get thanks for your report we appreciate your assistance into helping to identify potentially abusive content on our networks we've reviewed your report and at this time the content appears to be no longer active or available if you have any evidence otherwise please let us know and so yeah and except the site was still resolving and even so uh to the point where i
took a screenshot on my phone with the timestamp you know relative relative to the time stamp and i'm like do you see this like you know it's like the site is still resolving what are you doing i like i pointed out where you're supposed to go what are you doing and so they sent me the same exact message second time and so eventually i'm like i i give up i don't know what you people are doing but you go away so anyway yeah and it stopped resolving after a few months basically i checked i checked the day or so before i first gave this talk and the site wasn't resolving anymore so i'm like all right well whatever so
my next story paypal basically i found a sketchy phishing site that was targeting paypal you know the the url was basically this um you know update.security.problems.pay.user.gianthunt.com um and so it was that such and such i p address and i pointed it out to paypal i'm like hey uh you may want to throw this over to your abuse people and take a look and so um they said oh uh how did you come about this site and so i basically explained what i explained to all of you at the beginning it's like i monitor newly registered domains and and whatnot and so um yeah what do you think their response was i'll i'll give you like 10 seconds to
think you know one two three four five six seven eight nine ten okay their response was thanks for writing back since the url of the website is so complicated we will not be able to judge if it's a scam if you're looking to log in yada yada please make sure to use the link paypal.com this is the genuine link yada yada yada it's like what the hell are you doing like like of course it's a of course it's a fake website i i just told you there's a screenshot or at least i think there was this screenshot of like in the original tweet and um yeah like okay anyway next uh next story uh namecheap
uh well the first part of namecheap because there's something later on um basically there was i was using this um i was finding these weird uh domains that were like in this format i took a um i took a little screenshot of it and it's basically in in this kind of format it's like dictionary word either a number or another dictionary word and then you know dot more you know dictionary words in in a row dot either info xyz icu and i think there were a handful of dot pro domains and um basically if you hit them with anything other than a mac user agent it would redirect you to some sketchy like pc optimizer thing you know think like
those the the same kind of stuff you see in those infomercials late at night where it's like oh maximize your speed or um you know make your computer like it's new again or whatever um but however if you hit it from a mac user agent it would redirect to a fake adobe flash update that was hosted on aws and so all these domains were registered through namecheap and so i submitted a um abuse report with actually a handful of them one of one of which was this giant list of domains um and so they i got the response uh please be informed that all the aforementioned domain names have been suspended plea they have been rep placed on client
hold status and locked to prevent future uh modifications and so okay you know you may be thinking well that's nice it's like well just wait there's more uh later on and so my first uh or rather my fourth sorry my fourth uh story uh bank of america basically there was this uh program that i used to use before i was just uh before i started just taking search stream and piping it to a file i would use this thing from a security researcher i believe his name is xors i'm not entirely sure how to pronounce that he's i believe french um anyway it was fishing catcher it would leverage search stream and do some python stuff to judge whether or not a
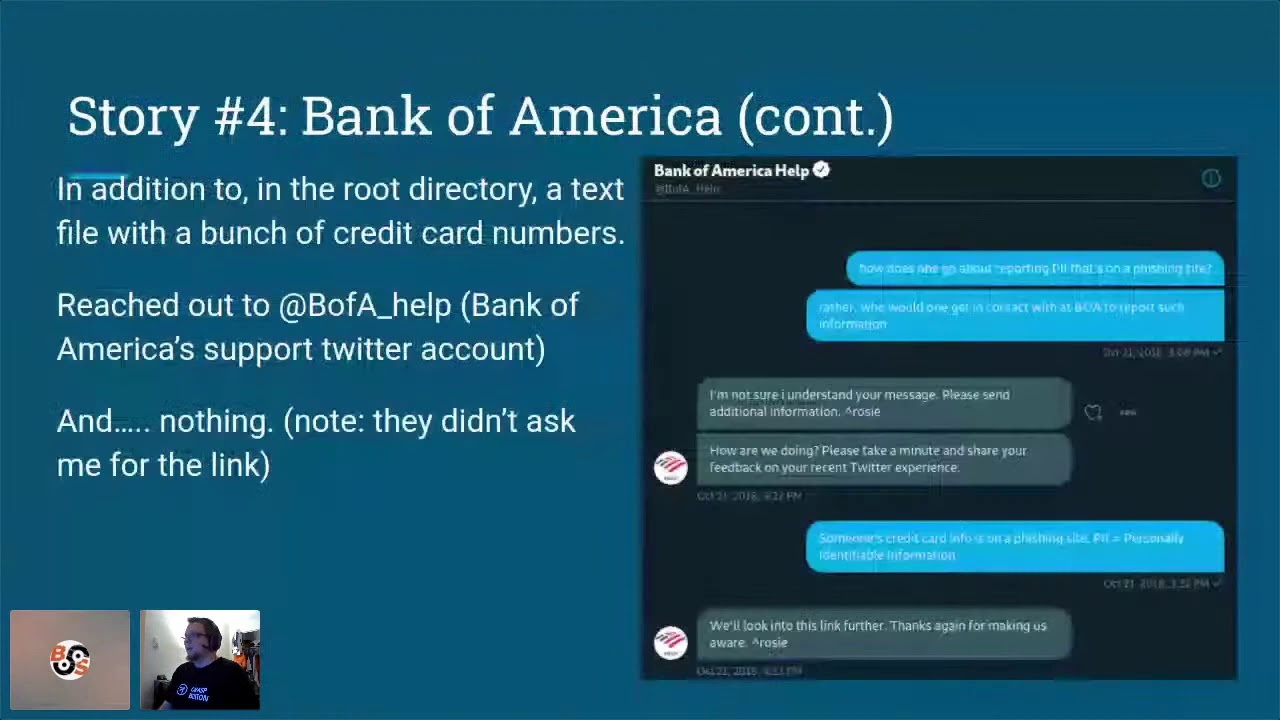
domain is sketchy or not and it would put it into a giant log file and you know you could kind of pick through them if if you want and so there was one that was a open directory with a bank of america fishing page um a active bank of america fishing page that is and so and the the kicker is i'm not entirely sure if this was the actual one because when i was uh originally writing this out the um as you may be aware twitter's search uh function is is a bit janky so i think this is the one but basically this uh this particular page would dump the credentials to a text file on the root
of the draw the root of the site and there were like credit card numbers and and what not in it and so i reached out to bank of america and i said hey um how do you go about reporting pii that's on a phishing site and um and they're like i don't know what you're talking about um can you send more information and then for some reason they immediately sent another how are we doing message um and so i'm like uh yeah someone's credit card info is on a phishing site you know and they said oh we'll look into this link further mind you i didn't send them a link to it i just said
hey how would i go about this because they i needed to make sure i wasn't gonna be you know uh have a hey van show up in front of my uh parents house where i was living at the time it's like yeah uh cfa ain't no joke man uh anywho they said oh we'll look into this link further thanks for making us aware and it's like they never got like what are you doing and so i never uh i never heard back but eventually the site stopped resolving so you know and this was let me see the date this is two years ago like two years and a month ago and so they yeah they they never got
back to me and so my fourth or fifth story um so uh that one time a relative got a um hookup spam text message and so one of my relatives uh texted me hey um i know you do like security research um can you take a look at this and so i'm like oh yeah just forward me the link and they forwarded me the entire text and so it's as you can see in the picture yeah um and so i threw the uh the link into multigo and so it looked like this the the link is like that's the that's the url that's the domain uh that's the ip that's the actual domain and it's you know hosted
on namecheap hosting and it turned out the domain was registered also through namecheap and so i posted on twitter and twitter was like i'll submit an abuse report i'm like okay fine whatever and they responded um yeah thanks for your email regarding such and such domain name unfortunately we are not able to investigate incidents of text message spam please contact the mobile operator service provider yada yada yada like it's like dude what the hell like i'm not asking you to get like investigate a text message i mean asking you to investigate a domain what are you doing ah jesus christ people okay all right so and before uh i'm not entirely sure how long i've ran already but
um you know the before i close out i just want to give some you know treats to some fellow security researchers and good folks um you know jeremy richards over at uh scope security the folks in thug crowd um a couple of my a couple of my buddies steve reagan sean gallagher um silas cutler and his mouseshare site which is where i if i find an open directory with a phishing kit i'll i'll typically upload it to mouseshare so that um you know researchers can take a look in in the event that the site gets taken down and some more uh security researchers and um yeah and um i forget the guy's actual name but he
he works over at uh zero fox um those are good people too anyway uh thanks for listening that's my twitter like i said in the beginning my key base is that my blog where i have a occasional trying to make it a habit or routine my series of posts crap i found on the internet um and so um my blog is over there at amylon.github.io and uh yeah let me check to see if there is any questions let me just hit there all right so let me see if there's any questions okay so this all right so there's no other questions um so yeah if um if any but yeah uh let me see if i what time is it because it's
i really gone wait a minute what time is it it's oh okay the time didn't update that's why it's like so um any anybody have any questions you know put it in the text or the discord um uh but yeah i totally didn't realize that it went this that i've got through that in like 20 minutes oh man um yeah all right so just to make sure people can hear me correct like so i'm not it's uh okay um yeah anybody uh and if anybody has any questions just uh oh so roy asks uh in the in the chat uh what do you recommend for new people to get into what you're doing okay good um so basically
for new folks i would say um try definitely get a virtual machine if you're not running linux and if you if you want to get into it basically download search stream it's it's it's a uh python uh library or a well technically an executable but it's you you know pip install search stream and then search stream uh space disable colors because it for whatever reason um it it puts uh color text or color on the text and so if you pipe it into a text file it like and you view it in i think certain text editors the escape codes will show up so it'll be like um you know uh carrot uh bracket or yeah carrot
brace you know whatever and then the the ascii code for for whatever color and then the and then the actual domain text and whatever and so uh so that's to say to disable the coloring you do dash dash disable colors and then to get the full sub domains because if you just type a search stream to a file it just does the regular domain so law.com or blah.blah.com but if you do full it gives all the sub domains that are also on that certificate so if it's you know sketchy sketchysubdomain.blah.com or appleid.apple.com or or so so on and so forth and also you get a lot of um a lot of aws um aws like literal you know dot aws cloud
sites as well as azure um something called kinetic.io which i think is like in europe somewhere and then uh what it what is it and then um a lot of uh western digital apparently has this uh thing where you can access your uh networked hard drives remotely so it'll be like long string.wdhosted.com and then there's a lot of that and it's basically as ssl certificates are regenerated and issued and for such and such domains they get put into these logs and uh you know you can the the command i typically use if it'll hang on let me share another window uh so i can pull up a let me see pull up a window uh
i will hang on one second i'll open up another tab in my terminal um okay so i'm gonna uh have i run into fishing sites that are legitimately used by fish testing organizations surprisingly a handful of them um i believe i found one or two that was uh no that were like know before and um yeah thanks for the thanks for the compliment about the t-shirt i had a you know i was trying to uh tomorrow's laundry day so this is like my last uh t-shirt that isn't uh rather grody um so anyway i'm gonna share the terminal window uh whereas it's i believe it's this one okay so basically what i do is i do uh because
what i do is i separate them into logs by date so you know 20 20 11 12 11-12 and so um and then i g-zip them so i so i do z-grep uh dash e for extended graph typically it's dash dash no file name because i'm you know grabbing more than one of them blogs and so for example what i have taken to do in a watch is freenom domains which are dot tk dot damn it dot ml dot cf dot gq dot
and then search stream logs and then say for example today 13 or yesterday rather and then start last and it's going to take a minute because it has to grip through that like i believe it's like a half a gig file and uh it's going to take a second so for example there's stuff like for example invite w a dot whatsapp you know it's it's somewhat uh it's somewhat highlighted there and so um basically it's you know you pull these up you you uh dump that to a file and then i pull it up in vs code and i'll typically will you know get rid of the uh space bracket thing get rid of the
comma space into such that it's a just a list of domains and then typically i'll get rid of cpanel cp calendars cpcontacts mail webdisk basically anything that's not um the that's not actual subdomains that aren't like default ones that are set up so like when you register a domain sometimes you get like auto discover uh auto config web disk whm you know the type of like administration panel stuff that that you know gets registered in edition and so i'll uh what i've actually taken to uh uh recently is using a program i believe it's by project discovery where it's called httpx where it's you feed uh domains to it and you can there's different flags like
dash ip to get the ip address dash title to get the http banner so if it's open if it's an open directory it'll be index of slash and if it's sometimes they're in like a foreign encoding so the the banner will just be some weird ascii like escape code text and so there's that and um so it's some weird weird stuff you end up coming across let me see if there's any other text or any other comments no okay so basically i do that i throw it into multigo and you know it's it's uh sometimes the the results that you would get if you're in if you're using multigo and you don't have the uh the capital to
spend the thousand plus dollars on the uh actual um not enterprise but the excel version of multigo where you can have your own transform servers instead of having to use um patervas over in i believe it's south africa where the country is based or with the where the company is based rather and so some of your results like if you grab the url throw it into maltego get the banner there it'll come up with something completely different possibly than if you were to say for example open up a incognito window in your browser um and just throw the domain into that and so um and you know but um yeah any uh you know feel free to reach out
to me on you know twitter on the discord i am it's pronounced uh it's pronounced woodsman but it's uh it's with os and it's with zeros instead of o's um there's a there's a backstory to that name from uh from the days of you know runescape if that's if anybody remembers that um but yeah um thanks for uh honestly thanks for having me folks um and i didn't run over my time nice all right thank you so much that was good great talk and unique uh way that you're harvesting all these uh new domain names and checking those out so yeah yeah the original because the original title of the talk was uh stories from going after phishing
attacks but then i realized wait a minute i work at the help desk i'm not the one i'm not like in the information security office or the office of information security or the uh security operations the folks that actually respond to the um phishing emails that the enterprise that the rest of the folks in the company get so it's like yeah i should probably change the title slightly all good we know everybody's titles are misleading we're always put into situations which we got to figure out and get out of so good job on that nice thank you very much everyone we're gonna take a break