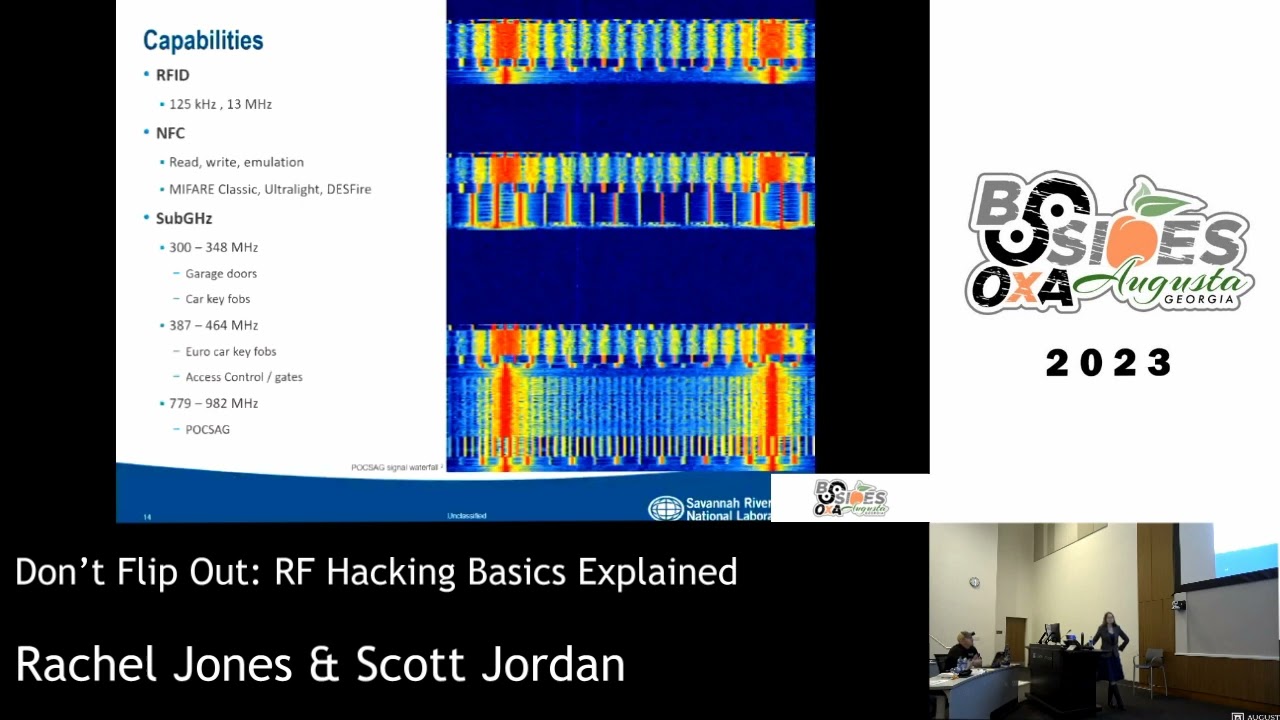
Probing Toms: Creepy hackers on your house doorstep
Show transcript [en]
Perfect. Hello. Thank you for the warm welcome. Thank you B-Sides Augusta for letting me speak. My name is Bryce Self, funny enough. Last name is Self. It's real. So yeah, so thank you for coming. This is ProMotons, creepy hackers at your doorstep. So let's get started. I don't think it's going to read.
Because RF is a thing, and RF blocking and shielding is a thing. Alright, introductions. So,
if you would. Maybe it'll work. You just have to be close. Alright, so again, my name is Bryce Self. If you're into Twitter, that's my name there, two underscores. So I'm the forensic team lead at Rendition InfoSec. We got a booth out there, one of the sponsors. So come check us out. Great guys, got a lot of information that I've been learning in the year and some change that I've been with them. So I've been in and around computers obviously since I was a kid, but mainly focusing on security. When I joined the Navy about eight years ago, did some other organizations, and now I'm with Rendition. So I am a, for this talk, I am a wireless security
slash exploitation expert, I guess, but I don't really consider myself an expert because there's always something new coming out and something I need to learn. It's like...
You know Appreciate it. Let's see that that's what's important. So yeah, like I said at rendition info sec, at rendition sec, we're actually headquarters here in Augusta. We provide many services, digital forensics, and service fonts. We're at MSSP. We're SOC, SOC, here in Augusta. So yeah, come check us out. Stop by if you want.
just to get the mindset if you're a wireless security expert and you know everything about wireless this material probably isn't going to help you but it's still very cool to learn so it's something that's very simple go ahead effective cheap and scary so when we get into this just keep those four things in your mind and you'll and we'll kind of break those down so 802.11
IEEE, 802.11 is standard. As you can tell, it's kind of lengthy. But we're talking about Wi-Fi here. So just to break down wireless Wi-Fi connections, if anybody's not really familiar with it, it's pretty general when it comes to this. So here we have John's phone. This is your client. And then you have John's router. So this is your AP, your endpoint,
right? Oh, is that you? That's why I did that. I did that. Yeah. Is that your SSID, Tim? No? We'll find out. So we got John's phone. We got John's router. So SSID there, service set identifier, it is a fancy long acronym for the name. This is your name of your router. I'm sure if you've ever set up your home router, soho router, small office home office, you can set this and this is how you say, oh hey Jenny, thanks for coming over, yeah connect to my wifi, it's atlanticawakistan27 or whatever, and the password is this. So what actually happens when you try to connect to a wireless router. So you turn on your phone, you turn on your wireless, maybe it's
already on, and a listing of APs, or access points, come up. And you'll see these names. You might see John's house, Dave's house, whatever. And you go through that list, and you pick which one you want to connect to. Well, what this AP is doing is sending a beacon
10 a second is the default that can be changed. But it just constantly keeps emitting this frame up in the air that anybody can see, unless you can stable it. But saying, hey, I'm right here. This is my name. You can connect to me. Go ahead, next. So it does this over and over again. Next. So let's say John's phone is already connected to John's router. So what John's phone is actually doing on his end, while the router's saying, hey, I have beepens. I'm beepening. This is my name. John's phone says it sent a probe request that says, I'm looking for John Smith Wi-Fi. I'm looking for this router. So after this probe request happens, there's a
probe response that comes back from this router that says, hey, that's me. You're looking for me. but he sends it directly to John's phone. Everyone tracking? So then John says, okay, cool, I'd like to connect. If you've already connected previously, you save your password and your phone right, it's gonna automatically do this, so this is what happens. The authentication starts, so John's phone connects, says, hey, I want to authenticate. The router then says, okay, sure, let's authenticate. Then there's an association request, an association response. The association is just we associate it, now we're together, now we're connecting, now we're talking, and I can send you data. So this is your basic connection between a client and a wireless router. So let's talk about this prompt request.
This is actually why you're sitting here. These prompt requests are really cool. They give a little bit of information. To some people like me, they give a lot of information. So these probe requests coming from your phone, again, we're going to see John's Wi-Fi. However, what if John has connected to another wireless router, his buddy's router that was FBI surveillance van 3? Well, his phone, if he's not connected to anything, is going to send out that probe request for that router. Because the way it works is convenience, right? Convenience over security is what Maybe not you guys, right? You guys don't know about convenience? Is that enough lengthy passwords? You're lying. So this phone is going to, when you get the wireless cord on, it's just
gonna keep probe requesting. I'm looking for John Smith router. I'm looking for FBI surveillance banner. I'm looking for ATT Wi-Fi. I'm looking for all these. And it's gonna send them out over and over again, hoping to get what we saw earlier, the probe response. Right, so that's where the router is sending and saying, hey that's me. Alright, so where's this going? If you do know where I was at a minute, you're thinking, ah, evil twin, right? So what is evil twin? Evil twin is where I can set up what looks like an access point, and if I see John's phone looking for John's router, I'm going to make myself look like John's router. And I'm gonna connect to the internet, and he's gonna send all this data right through
me. That's pretty scary, right? I can collect everything he's doing. I'm gonna make him think I'm John Droughton. That's not how we're going. It's even scarier, I promise. Alright, so scenario. It's late in the evening, you're craving some coffee, go to a coffee shop, you walk in, see the barista there, and you see one person on their laptop. No big deal. You pay, get your coffee, you walk out.
I was that person on the laptop, right? I'd grab some coffee, I'd go sit down in the coffee shop. Before you get there, I start some wireless tools and I get a little baseline going, okay? I see you come in, right? The only other guy is besides me in the barista. You got a Rolex on, right? Wearing some fancy stuff. You leave, you drive a fancy car. Well, what do you know? You're not a person of interest to me. So I know what you're thinking. So what, Rice? Doesn't mean anything. I didn't connect to the Wi-Fi in there. I didn't do anything. I walked in, paid for my coffee, and I walked out. So your phone actually had your
wireless on. Did anybody read my summary and then was like, I'm going to turn my wireless off before I come in there? And I did it. Don't do it now. It's too late. Go ahead. So this is what I saw on my site. So Wireshark. Wireshark is a free open source packet analyzer. Really cool tool if you've never looked at it. So this is what real world data, those frames that we were talking about that are in the air so you can kind of look and see what it is. This is actually what it is. So what we have here are probe requests. So these are our clients. phones, mobile devices, laptops, whatever, sending these frames and probe requests looking for these routers.
So there's a router that someone has previously connected to called a password intern. Well, when I saw you come in, it was around this time right here, because this is when it popped up, and I see this right here, SSD faculty's rule. Maybe you had a faculty's jersey on. And then I'm still profiling you and I'm like, okay. So this could be him, it could not be, it was around the same time. Wearing a Falcon's jersey. I see that someone connected previously to a rather-house Falcon's rule. Well, what about this? OUI, anybody tell me what OUI is? French for yes. Say it again? It's French for yes. It's French for yes, that's good. How about in wireless terms? You guys can ask. Oh, did you answer?
Organizational. What? Organizational unique identifier.
Yeah, so. Organizational unique identifier. Right. Right. Organization unique identifier. So what this is, these are MAC addresses. OUI is the first three bytes of this MAC address. You can take the first three devices in this MAC address and you can go on Google and you can look up a Go U Live lookup. You plug that in and that's gonna tell you Apple. That's your manufacturer, basically, serial number. And then the next three bytes after that are actually unique to your device. So then Mark Sharp already broke this one out. This is the Samsung device. And then there's Cisco and all types. So what am I getting at here? Well, I saw that you had an iPhone. So now that's another profiling technique that I
can say, yeah, that's probably him. Because I saw the barista get a Samsung, let's say. All right, so what can we do with this? So there's a site, a really cool site, called Weichel.net. We can do a little open source research, open source reading on. So we get on the site, and I'm going to look right here for that SSID. Because we were in Augusta when I saw it, and maybe we were in a coffee shop right around here. Okay, so I can actually, there's different searches you can do here, you can search all over the globe. But what this site is, it's a war driving site. War driving is where guys in cars, or walking, what have you,
drive around with wireless tools, sucking in all the data that's available. in the air, open. So a lot of this data is used for where you can find the nearest hot spots to you. Maybe there's an app for that. What's a free open network, no password, connect to, what happened. So you can use this site for bad things because I can search for that SSID. Let's say his name was John. I can search for his SSID, his router, And I can find that it's somewhere on River Ridge Drive. Anybody look on the street? No? All right. Someone's like you. So I see there's an actual, historically, this is all historic data, it's not live. Historically, there was a router on
that street called Falcon's Rule. So that's probably where my guy is living. Or this was a router that he was connected to, maybe his buddies. Who knows? But I'm taking a chance. So now, so I can do some targeted board driving. This means I go out in the car and I go to River Ridge Drive and I take a wireless tools and a wireless car antenna and I stick it on the roof of my car and I go see, I lock in this MAC address that I just saw on the previous slide and it'll alert me when I hit within proximity of it. All I have to do is drive down River Ridge Drive. And then I see that, hey, I drive past this
way, and it goes away. I don't see it anymore. And you can do this all to worse. So you're like, OK, Bryce, well, how do you know which house it is? I got it. You're in the strip of the street. There's maybe six houses on either side. How do you know which one it is? Well, you can take what's called a hatch panel antenna, or a directional antenna. What it is is instead of an omnidirectional antenna where it captures everything around you around this antenna like a donut, it's going to capture a specific direction. So I can point it towards these six houses and I see what's RISI value, which stands for Received Signal Strength
Identifier. What this is, is it's a number that says how strong that signal is coming off that router. So I point it this way and I see that it's pretty weak and I point it on this side of the screen and it's pretty strong. So I know you're on that side of the street. Now I just have to maybe drive my car right here next to this house, and drive my car right here next to this house, and I see it get stronger or weaker. So, I know where you live. What can I do now? Well, typical person in this field would say, I'm gonna gain access to a network, I'm gonna crack your WPA,
what have you. What about the other stuff, the scariest stuff? Now they know where you live, they know where you drive, they know what type of person you are. They can just sit outside your house, wait for you to leave, go into this other stuff. Just because you left your phone on, your wireless cord on your phone, walking into a coffee shop. Pretty cool, right? You're like, no, it's scary. So use this for this. Where are we at on time? 10 minutes. So uses for this, red teams. Maybe you want to target the CEO of the company, but they're pretty secure, they have a nice perimeter fence, guards at the gate, they don't respond to the
USBs dropped outside the parking lot, what have you. So you can maybe know where that CEO goes and likes to drink coffee, and hopefully, if he has this wireless card on, you can figure out where he lives. So you build a pattern of life. You figure out how to use for different entry factors. Law enforcement, same thing. Building the case on someone, this is another way that they can figure out information about someone. And then of course, peeping toms. That's the name of the talk, guys. Probing toms, you get a different request, peeping toms. It's a play on words. Poor Tim. Thank you.
So benefits to this, it's passive. I didn't do any type of active injecting anything, deauthentication, nothing like that. For lack of better terms, I was invisible within the wireless spectrum. All I did was listen. That's all I was doing. It's free to cheat, depending. You're going to need some type of laptop. You're going to need, we'll get to the next slide on that. And then it's just free. Passive, I was just another guy in the coffee shop sitting in the back typing away, just another guy doing schoolwork. So like I said, here's some tools that you would need to do this. You got your laptop, Kali, or formerly known as Backtrack, that screen to download. It's a penetration
testing OS, and then an alpha card. An alpha card looks like that. I have one over here. And those are cheap, $40. All right, challenges, obstacles. So I talked about a couple of them. So if eight people go into the same coffee shop when you have your baseline, that might be a little difficult, right? Because maybe all of them have iPhones, all of them have Falcons jerseys, because it's like a, I was gonna say bachelor party, but what bachelor party goes to like a coffee shop? That's weird. He's like, I do it. All right.
And then it's board driving dependent. So the data on doing that OSR on vital.net, it might not be up to date. I might have changed my wireless router's SSID to name yesterday, and someone drove by my house two weeks ago. And that's the data that was uploaded. However, caveat to that, you can do your own board driving. So if you just feel like going all around Augusta looking for this SSID, you could. You just drive around. And then you hook up a GPS puck to your laptop, put it all in Cali, and basically you match up the times with when you saw the SSID and at what time where you were at within Augusta with the
coordinates. OK. So now everyone's like, all right, I'm here. People are going to break in, especially for ICE. How do we protect ourselves? Well, turn off your Wi-Fi. So everyone, just get your phone out, your laptop, turn it off if you're not using it. That's one way to do it. If you're not probe requesting, if your phone, your device is not sending out those probe requests, I can't see anything. Do not remember. Whenever you connect to a device, you have the option, save this password, remember this device, that kind of thing. Well, uncheck that, and then that way you can, convenience over security, right? No, you want to keep reconnecting to it. There's options within some of your devices, most laptops, windows. You can
go in with the network configurations and remove all of the previous
access points, network data. So basically, none of the group requests So I can still leave my wireless card on, but I deleted everything so I'm not sending out any probe requests because as the phone sees it, I haven't connected to any other device. Forget this network. Like I said, we never set this. And then a bonus, so you remember the evil twin I was talking about? As a bonus, to protect yourself against that, you can do ask to join networks. If someone's trying to set up, hey, come connect to me, and you are probe requesting, which you're not supposed to do after today, it'll ping on your phone, or whatever it is, and it'll say, hey, would you like to join this network? And you're like, uh-huh.
Something's going on. Questions? I'll throw it up. You said using software in Cali. Yes, sir. Do you have a Windows preference? That stumbler's kind of gone away, and I guess the traditional now is the insider. Is there anything else that you might try? What are you trying to do? Well, just associating with the war driving. Yeah, there are war driving programs. I'm not going to say I'm not going to stand behind one. I'm pretty old school. I just like FireShark and I just throw a filter in there and I have someone else. I'm sorry? NetSelver? NetSelver, yeah. So yeah, I mean, there's a time there. So yeah, I mean, I have to put a wire short. It's just proven this works. Anyone else?
So in the case of someone using your wire host name to go to your home, wouldn't it be better to remember all the networks you connect to
in California so they're less likely to get the one that's actually at their home? So you're saying obfuscate your own, so connect to a bunch of wireless routers in California and then here in Augusta, I don't remember the one here, that would be great. That would be really cool. I tell you what, if an attacker wants to go all the way to California to find you, then you've got bigger problems. Call the FBI. I don't know. I don't know. I mean, that's a great question. To me, I think it would just be a lot easier to go to the steps of protecting yourself, uncheck remember, don't connect to a network, reset all of your network settings, that kind of thing.
That way, if you are probing, or rather, if you do have your wireless phone on, you're not probing anything at all.
I'm sorry? Does it still probe once it's associated with the switch? It will probe. However, it's more of a, it's different. It's more of a management, hey, are you still there? Yes, I'm still there. Okay, we're still connected kind of thing. Right, right, so it's not going to probe the other ones. Right, so if you're going to Starbucks and once it connects into Starbucks Wi-Fi, then you're not going to probe anymore. So you have to kind of round before they connect to Starbucks Wi-Fi. Absolutely. However, do you have it set up where you automatically connect to Wi-Fi? I mean, if I was just going to, like the scenario was, if I just go in with my wireless card on, it doesn't connect to
Wi-Fi, let's say, Starbucks Wi-Fi, and I just walk out, it's just going to keep probing. It's not going to connect, and I have that window. So. Sir? I wonder when you're hiding your
SSID. Is it still broken? If you're hiding your SSID, so you're talking about the AP? Yeah, AP. OK, so the access point, if you're hiding your SSID, this is within your wireless configuration where you can say, hey, I want to hide my SSID.
Technically, no. It's not. It's not going to beacon anymore. So AP's beacon, client's pro. So it's not going to beacon anymore.
if you're near, say your name's John, if John's phone sends a probe request, says, hey, I want to connect to John's router, John's router is going to reply with the probe response, and then now your SSID is unhidden. Does that make sense? Because now I know, or rather, Wireshark says that's within proximity because they answered. And then it's going to unclear. It's going to find out.
the AUT-SME will just reconnect to the most recent one of the previous two or does Paul list strength? Not a list. You remember the RISD-I receive signal strength identifier? What it's going to do is if there's two within proximity, it's going to connect to the one that's stronger. It's going to probe for all of them. And then if there are two within the area that I previously connected to, I have a potential say it's going to connect to the stronger one. Was that your question or not? I was asking, like, will it start at the top of my guy connected to my coffee shop? So if you ask me, will I probe for my home router or will I
probe for the coffee shop first? It does it really quick, within nanoseconds of each other. So the order isn't really important. It's just going to be a chunk of pro requests. I'm just curious as to whether or not someone can deal with me and then see. I see your question. OK. His question is, if he's connected to an AP and then he deauths, or an attacker deauths in the deauthentication frame saying, hey, disconnect from that AP, your phone will send probe requests out unless the beacon comes first. So it will still send out a probe request. But if the connection, if you have it automatically connected, credential safe, it's going to just go ahead and connect again. So certain
configurations within, yeah, it's weird. Certain configurations within where you might, you might not. I have a run at time, Russ. OK. I'll answer your question, I promise. I just want to plug a little Snoopy NG framework. Snoopy NG framework? Yeah. It does all the stuff you did and then saves it to other people like that. Snoopy NG framework. You better that? Great. So who's this left? That's weird. All right. Lock it set.
Down here. Right here. Yep. It's yours. Missed. Why five nine? It's yours.
I'll trade you up. Okay, sir. Thank you so much. Really appreciate it.