Technical Deep-Dive: Trend Micro - Zero Trust Paradigm
Show transcript [en]
[Music]
[Music] let's get going here so i want to thank everybody for having me here today my name is ken stevens i'm a senior solutions engineer at trend micro canada i'm also a subject matter expert on xdr uh today this chat will focus on zero trust and i'll start by discussing a real world attack i'll talk a little bit about what xero trust is i'll talk a little bit about the use case and i'll show some quick examples and this will be the only time i showed a trend micro product today then we'll touch slightly on the zero trust journey and where we are today and what steps will take to move in the direction towards a zero
trust uh strategy and organizations just gonna kill my video to save some bandwidth and perfect so let's just start with a real world scenario situation uh today so organization gets hit 75 of their computers are encrypted using rebel ransomware right so this does happen today this is a real world scenario and how does this play into zero trust just when i talk about the attack that i'm about to go over and we go through the talk today i want you just to just to relate on where xero trust could have played in so that we could have gained visibility sooner
so this here is a common attack we see today a threat actor leverages access into an environment whether they purchase those credentials on the dark web and or rdp abuse or they find a vulnerability on a publicly accessible application multiple different ways or if they fish a user in this particular scenario they did purchase uh credentials on the dark web so they had pretty easy access to the environment once they once they got in so as they got in there they started to move lateral within the environment they compromised the active directory server they compromised the anti-malware server they removed agents and they ran their ransomware so think about zero trust and when you think about how we could have caught
this before it got to the exfiltration or the impact stages where that is what we're trying to stop is allowing our attackers to get all the way to those end stages we want to catch them at initial access right during some of their routines as they move through your environment and zero trust is going to be a big part of that to gain this level of information and visibility so let's talk a little bit about what is zero trust uh what it means to organizations like forester what it means to cesos and then we'll talk a little bit more about the use case as we go through so zero trust according to forrester really means
say that says to trust no one both inside and outside your network they say it requires network analysis and it needs a lot of visibility when we talked to csos federal cso came back said it's all about verifying every user validating every device and then within that and this is the really important part limiting limiting access intelligently and that's really the heart of this is really limiting access so that when adversaries do get into our environments we actually gain some visibility into their lateral movements and we can restrict it today we have an implicit trust model in a lot of organizations once they breach the perimeter they usually have unfettered access or you know very unrestricted
access to the rest of the network as they try to figure out what's happening and we'll talk a little bit about micro segmentation and those things to help with this but really this is about gaining visibility using that big data and limiting access intelligently it's really what the focus is when it comes to zero trust and really it means zero trust means never trust always verify ensure you understand who the device is ensure it meets the conditions that you want to allow that device or that user to access the network right whether the user is bringing in risk or the device has a vulnerability using those to assess if they get to data or a resource like an application
you want to gain that visibility so that you can stop it if they're introducing too much risk or it could be a malicious activity from an adversary and so a lot of threat a lot of organizations today have this approach castle and moat and we found you know as the pandemic started we found that a lot of organizations weren't ready to extend the perimeter with their current defenses so zero trust model of information security basically kicks to the curb the old castle and mentality that organizations focused on right well assuming everything inside did not pose a threat and therefore was cleared for access and we know this doesn't approach some of the most egregious data breaches have
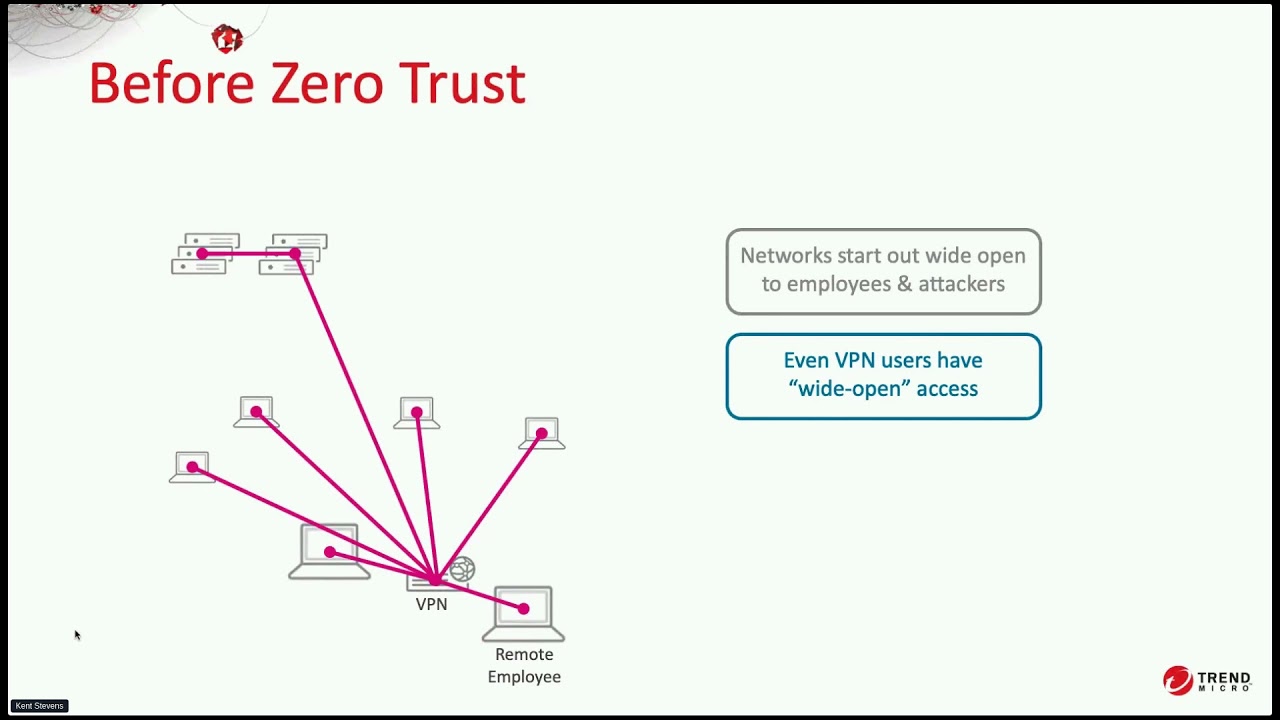
happened because hackers have gained access through corporate firewalls were able to move internally without much resistance today's enterprise i.t departments require a new way of thinking for the most part the castle itself no longer exists in isolation as it once did and companies don't have corporate data centers serving a contained network of systems but instead typically today some applications are on-prem some are in the cloud users employees partners customers accessing applications from a range of devices from multiple locations and even potentially from around the globe and all of these macro changes have led to this new model zero trust and so when we talk about this so before zero trust you know the old approach was
everything was wide open and employees and attackers had full access to the network if you have a computer in the office right you can reach lots of network destinations because verification for the user is different than the network communication layer they're already inside they don't have to go through that layer they are on the network already and even with vpns yes we've done micro segmentation and we've you know we've used a number of different capabilities when it comes to networking to try to limit but once they get into a network they have usually unfettered access to all the applications within that network right and this became problematic right when really organizations really only wanted access to one or two applications
but once they got in they could touch the anti-malware server they could touch other resources inside the environment and so when the attacker gets in the environment maybe phishing an employee then maybe credential dumping elevating privilege they can do a lot of damage as they transverse the network they can spread ransomware they can exfiltrate data because the network is so available to them without restriction and network segmentation is a strategy right that people are starting to adopt because it makes some lateral movements more challenging right putting various parts of the network in different boxes and saying okay this traffic from this network segment can't flow to that segment or only these circumstances and what of what evolves is really a complex
set of rules and those rules and policies are hard to manage either you have a really strong set of micro segmentation rules or you have a practical set easy to manage but isn't that strong and so shifts to the cloud right made it even more challenging right so infrastructure as a service right everybody's adapting cloud solutions sas services like office 365 and salesforce and other cloud services you now have more complexity with respect to traffic patterns that are going to be legitimate in the traffic patterns that you want to protect against and so one final challenge is that employees or especially remote employees are able to connect directly to those sas infrastructures without going through the corporate network and that
reduces visibility even more and so a zero trust approach has started to emerge where the fundamental principle is to start by trusting nothing by default you know zero trust part you trust nothing and all and so that means you allow no network connections by default an endpoint that is trying to reach out and connect to all kinds of places in the network isn't allowed to until it is verified and then allowed and before it gets allowed to connect to any particular place that it's trying to do it has been assessed for risk risk based on health of the vice health of the identity presenting itself the nature of the the destination that's being accessed or the data that's being
upload and the overall application health and the assessments feeds and decision whether or not allow a purposeful connection from that endpoint to a particular application so using the information being presented to really decide does this user or does this device actually get to access this application and that need that connection needs to be assessed continuously so that the health of a device whether user identity or application changes that connect can in fact be found out to be true right so we understand who is there what they have and what device it is and are they introducing risk into our environment and so this is a very different approach but it's very effective approach at making life more difficult for attackers
and that's what it really is all about is they're getting in today they're getting that unfettered access to the network once they get in they're finding the assets they're exfiltrating their data and then they're dropping the ransomware right that's what's happening today that's real world and i mean i heard a number today four trillion dollars when it comes to ransomware in 2020 it was a four trillion dollar industry that's pretty impressive and we don't want to be on the news explaining why we got hit so that's why zero trust approach approaches are going to be the future right so attackers have more trouble moving laterally they have more trouble successfully leveraging a dump credential right and
this really does complement an xdr approach and really if you haven't heard about xdr yet that's the ability to do cross-layer detection and response it's really taking that edr story and bringing it to multiple security levels having the black box on each security level and leveraging that big data so detections don't go away you actually improve the odds of detection when you actually use this kind of approach because you're making the attacker's life more challenging for example xdr is help gathering context around the device for a risk analysis and that helps you understand and make a threat or risk informed decision on the device whether it connects or not and this eliminates the wide open vpn
challenge scenario right you can ex we have users on site or off-site they can connect to specific applications or you're able to determine an access policy driven off the risk that you find from inside the environment and that means your overall policies are going to be a little less complex around around who you allow and it really boils down to the health of the users and the devices and of course there's going to be more right to simplify this as we go forward of what's allowed in the environment and what's not so i hope this adds a little bit of context to what we're talking about today and now i just want to do a little bit
of compare and contrast of the traditional security model versus what it's going to look like in the zero trust paradigm so traditional security everything on the network is implicitly trusted and when we move to zero trust that paradigm is going to change and we're really going to trust nothing by default nothing will be trusted until it is verified and traditional security assumed identities are not compromised and we see this a lot today credentials being you know bought off the dark web credentials being phished from an email right that is happening today and they are getting in our environments and so everything whether it's users or devices are going to be are going to be identified and their health status will
play into the zero trust paradigm it's going to provide a lot of lot better information to make those informed decisions about who gets access and who doesn't and we assume users act responsibly in the traditional security model and right we only and then in the zero trust paradigm are only going to allow network applications accessed selectively so not everybody is going to be accessing everything all the time you're going to be able to use risk informed decisions and ai to make these decisions for you to ensure that you know if they don't meet a certain amount of conditions that you can cut off their access to either the network or to the application at hand in the traditional model you know
you work to detect actor behavior right so using patterns right very strong and right and when this becomes in the zero truss paradigm right we're increasing the challenges for the attacker right now we're seeing them at every level whether they're you know attaching to office 365 or whether they're trying to get to an application internally on the network uh with a zero trust and with xdr alongside it you're increasing the challenges for the attacker to go unseen so essentially we'll be able to gain some visibility from the zero trust paradigm and allow you to make those decisions appropriately and so quickly i just want to stats talk about some various steps towards zero trust and organizations are taking them
today i mean first and foremost is verify identities you know mfa if it's not a part of your practice today it needs to be you need to have that second layer and whether it's you know using an application to do this or using you know sms having some layer of multi-factor is better than no layer of multi-factor you need to restrict network access so micro segmentations dmzs those are all going to play into this as we move forward um but they only take us so far and they can with micro segmentation it can add some complexity to our environments that some organizations may not be able to handle and then application safe listing default deny app execution so you know
application safe listing making sure that an application is not allowed to run unless it's explicitly allowed right we also need to gain visibility right to sas applications we need better control access and organizations are bringing casbies for this and secure web gateways are also part of that and then last and not least is beyond the vpn right we need to have a zero trust network access capability right ensuring that we can do blocking to applications based on the risk or the health of a user or a device which is very important and this is where we get into this sassy zte conversation um and really those focus on those technologies about having the ability to see what cloud access is
happening leverage a secure gateway and then provide some kind of zero trust network access is really why organizations are moving into those technologies and so zero trust is really all about exposing and prioritizing risk for better decision making and so this is going to be the only time i'm going to show any kind of trend micro product today but really it's just to give us some visibility and examples of what a zero trust application can bring to us the biggest and most important one is xero trust is going to be able to bring us continual monitoring of threat and posture risks right they're going to be able to pull in threat detection data they're going to be able to pull in xdr
style data or cloud app activity they're also going to be able to pull in information around account compromise or possibly vulnerability detection you know leveraging vulnerability scanners in the environment they're also going to be able to leverage logs from your identity provider to look for anomaly detection when it comes to where users are logging in from right where users are accessing the data from right so new ip addresses new devices all of those things are going to be easier to identify with a zero trust approach user usually signs in from the office in calgary all of a sudden that user account is being leveraged from europe those kind of things are going to be a
reality and it's going to play into this zero address zero trust paradigm as we move forward and like i said it's gonna give us abilities to uncover account compromise risks whether it's a leaked account whether it's suspicious user activity whether it's a targeted user account zero trust is going to be able to bring visibility into these different areas where we can make an a a detailed you know obviously a determination based on these different indicators to if a user gets access to a particular application the other piece is around users identity right they're going to be able to pull in multiple different data sources to give you visibility whether it's you know account compromise or whether it's
you know different locations logging in you're going to get the ability to actually have a risk score at the user level so this user is introducing x amount of risk and whether that is you know risk because the credentials got dumped on their endpoint or risk because they're being phished in the email channel or even risk because they're using they're having sketchy cloud app activity these type of indicators will help calculate risk scores for users and allow us make determinations if if a user should have access especially to critical assets if they're introducing high or elevated amounts of risk into the environment these zero trust capabilities are also going to allow us to understand the
health of devices so prioritizing vulnerabilities in the environment really understanding you know where printer nightmare would lie as a vulnerability where hive nightmare is allowing you to understand the impact scope of how many devices are in my environment that have a particular vulnerability and allow you to you know obviously can get your plans together to remediate those right so you can focus on a particular vulnerability get those patches in place get those devices healthy and if there is an underlying you know protection layer from our product suite we'll also provide you a rule for that also if it is available but understanding you know is this device even though it's my administrator is it healthy have they patched it
recently is there some major vulnerabilities and understanding the health and risk of a device at any point in time will help us identify any kind of risk coming into the environment at the device level and so where are we today and how are we going to navigate this journey because a lot of organizations i speak with today really are just starting this journey they they've seen the term zero trust you know they started to investigate and understand a little bit more about what it means uh you know in some organizations they you know they think it's going to be very hard to implement this but there are ways to get started and there might be baby steps at the
beginning as we start to develop but you will see more and more of this capability as we go forward and so we're still in the early days and so there's no vendor that has a complete zero trust solution right it's still you know much time for innovation and opportunity ahead you're gonna see a lot of organizations and a lot of vendors come with their zero trust solution this is going to be requiring more of a mindset or a strategy to get going it's not going to be one single solution it's going to be policies it's going to be solutions it's probably going to be multiple solutions as organizations gain that visibility but no single vendor today has a
complete end to end zero trust solution according to uh what we determine as in the industry and so like i said this is going to be a long road organizations are going to have to shift their mindset from you know you know that least privilege model where you know you only give them access or the ability to to leverage these particular resources that mindset has to shifts like slightly so it's not a product it's it's a mindset oh sorry and we need to gain this visibility for better decision making you know we but we need to continuously verify end users and devices right utilizing a zero trust solution and without risk analysis how can you effectively enable trust right
you need to have big data to make this happen and like i said earlier really limit access intelligently using sassy solutions using scores from zero trust solutions and really allowing you to make better determinations of who gets access to data or applications based on the risk that they introduce into my environment and so big picture here is as you move forward and think about zero trust there is going to be a direct correlation between xero trust and xdr solutions right essentially they are going to work together it's going to create an ecosystem right where threat detections are key to understanding risk in the environment and zero trust approach is really going to slow down attackers
and make them much more visible in the environment so they are really going to work hand in hand as we go forward so zero trust is is not only a single single pane of glass to understand risk but it's going to be brought in and leveraging xdr as it goes forward to understand threats in the environment
and with that i'm just going to check and see if we have any questions or anything if anybody wants to open their mic and ask any questions about xero trust on where they are in their journey or or or ask questions directly uh we can answer some but zero trust is is not a single product it is a mindset right it is a strategy you're going to have to use multiple solutions there is no single solution today to give you in complete visibility and network access capabilities it's going to require a few products today but we're leaving a lot of room for innovation uh here at trend micro we are we are working hand over fist to get these
capabilities within our product sets today um and you'll see the other vendors doing the same thing thank everybody for joining i appreciate it hopefully you learned something new about xero trust and and we'll sign off thank you very much





