Security BSides Kraków 2024

Show transcript [en]
[Music] oh [Music]
[Music]
fly so high I'm hypnotized what's up is down what's left is Right chasing stars and holding you I can't see the end but we'll see it through
[Music] Ving get off for we're smly on top of the
world dangerous times don't fly too high be sure to keep the ground in sight F forever if you keep it tight love the world that keep the sky on your [Music] mind get off for we're smly on top of the [Applause] world get for we're sming on top [Applause]
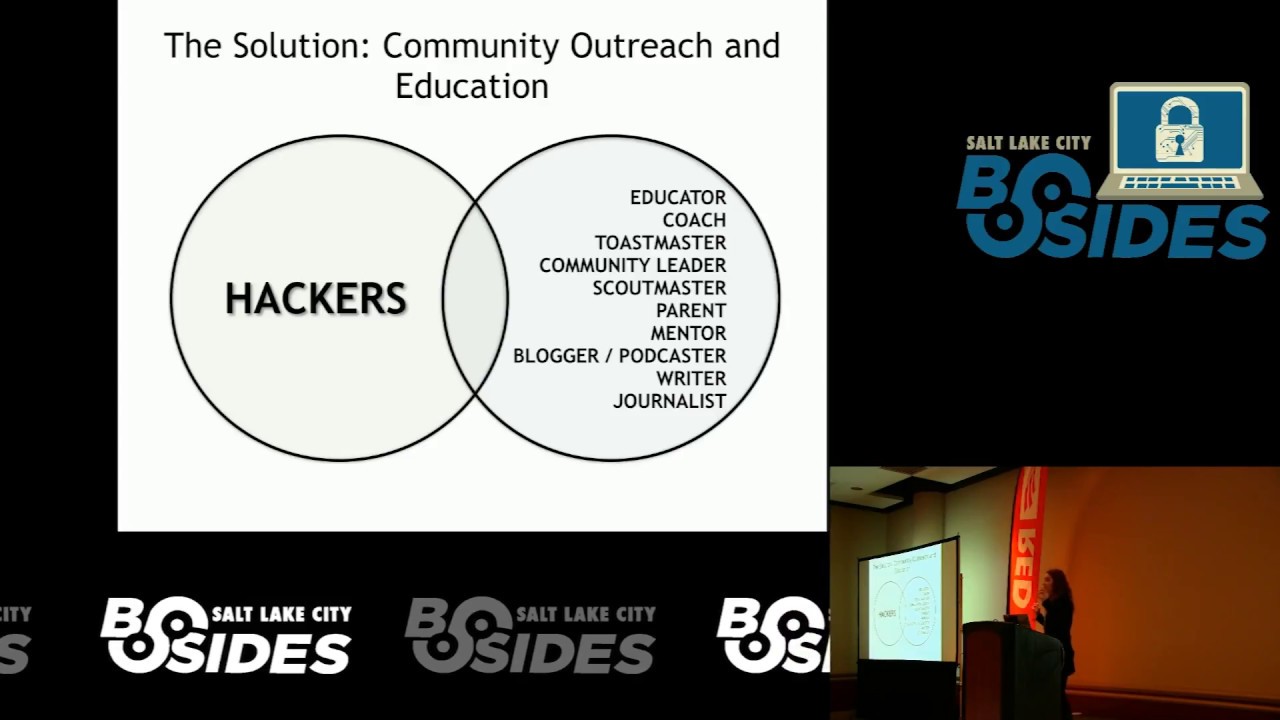
[Music] [Applause] [Music] of hello this is Casio I'm the co-found I'm actually I'm the founder and the coordinator of besides kov it's our third year and we invite you for all the next years besides all about information security so we can find all the content about cyber security infos forensic application security anything related to this topic uh you are very welcome for besides CCO actually besides a whole community of conference around the world more than 200 cities more than 1,000 conference already by 2024 uh and I started besides kov 3 years ago since I moved to Poland because there was no besides kov and it's a very nice way to share knowledge uh to bring people to the community uh
to connect companies that want to hire or they are looking for talents or they want to do business and it's a very nice way to share knowledge I think it's all about sharing knowledge so we have hackings or Hackers from the world people from all the continents they are here as speakers as sponsors are collaborating and uh making the community environment for all of us in besides all around the world you can actually in besides kov as well you can find workshops trainings exclusive trainings for besides you can find uh talks interesting talks technical talks nontechnical talks you can find uh the only one thing we don't allow in bids it's sales talk you will not have
commercial talks actually it's everything about sharing knowledge and Tech technical knowledge or everything related to cyber security for example 2024 we have three tracks and two Villages uh including application security Village including cyber games village where we can have fun and learn at the same time also amazing talks from Hackers from Poland and all around the world so we invite you to share your knowledge as well and come to learn with us [Music]
I
a
[Music]
[Applause]
w
w we are not having the complete set of values or G features and even if we are whatever WR the fact that this is Mr opener what was his first name Robert or or not yeah of course you can check yes he was using his second name Robert but actually if you grab the bigger context you can see more we should be extra and [Music] he
he
[Music]
was even funny because all these stores they had antivirus and PR protection and so on but this is just a normal code right and the antivirus like behaving uh checking the signatures hash files and all these things and this couldn't the antivirus couldn't get because it's tomorrow itself right uh now they have some more Behavior monitoring and see what the actually code is doing to block and so on but it's expensive actually not be not everybody has this kind of power yeah a little bit of theory now for the first first part of the Pres presentation so we all will understand what will happen later so this is how the FD tax looks inside because normally
there just a white cards nothing clear but inside there is a chip and there is antenna this is this red wire that you can see and this part is important so Focus because it will come up later in the presentation in terms of Access Control Systems we can divide the RFID badges into two main Fields it will be LF which stands for low frequency and H which stands for high frequency be prepared for work think about the worst possible scenario what if I'm going to lose data from my GitHub account that the data come from am I able to restore data to completely different account the same data in case I had malicious subcontractor cutting off from my
account but I have back my
I [Music]
[Music]