Together, We Could Land a Plane: Our Community as our Strength
Show original YouTube description
Show transcript [en]
[Music] everybody you haven't even heard it yet it might be terrible you don't know yet all right so uh we're going to finish out beside Salt Lake City with a kind of obscure set of skills and how affect our community so we're going to talk about our unconventional community and we all know that the hacker Community is a little eccentric which is awesome it makes our cons awesome it makes our parties awesome but we don't really talk about it from a learning and a corporate working perspective um so let's start out with for the three people here who I an annoyed yet um my name is Leslie carheart I run an IR team I've been
doing infos for for God almost a decade now and I've been working in it General all sorts of areas of electronics and Tech for about 18 years which is terrifying to me and yes I'm really that old um I blog I speak Newsweek says I'm an influential cyber workor consultant which makes my grandmother very happy I am staff at Circle citycon and I do a lot of resume editing for you guys um and I do other stuff too I am a martial artist a marksman and a reservist all right so what are we doing here talking about our unconventional Community well today we're going to talk about all of the stuff we do other than
Hack stuff get shells pone stuff all the cool stuff in the dual core songs um we're going to talk about that and we're going to talk about why that's important to us in security and so what does that mean in more sensible words that means we're going to talk about cross-discipline research and I have some unfortunate news for everybody here today um keep in mind that the camera is facing me not you but you are my demo today so you are there is this is an atheist presentation there's no demo Gods here so uh you are in charge of all the demo success or failure so I'm going to need some audience participation which I know all of you hate and you're
all like hiding behind your phones and your laptops now but this said there's no demo Gods to save me here it's all up to you guys all right so what I need you to do very first before we get anywhere else in this conversation today is I need you to sit there for a moment close your eyes don't fall asleep yet and imagine a hacker um if somebody wants to turn on some Prodigy that might help um so yeah picture a hacker in your mind the perfect hacker the best hacker you can think of the the leadest hacker the coolest hacker the person who you aspire to be or you aspired to be when you were
getting into the field okay everybody doing that awesome cool all right so let's talk about that hacker you just imagined oh my God green text on black we're getting into hacker space here okay so uh well there's probably some things a lot of your imaginary hackers had in common they are socially awkward they're probably kind of paranoid and introverted um but they were man they were so super cool and cooler than you think you are they started cloting when they were five they spoke at Defcon before they were a teenager man they had a cool cool Elite handle that they uh went by when they were a teenager um they never had to work retail they never had to enlist they
never had to go to college at some point they hacked into the IRS dbase and uh got sent to prison and got out and got a cool Consulting gig and um they've uh they've never really learned how to do business stuff they've never had to because they've always been so good at hacking that they've never really had to fit into the of the world um they just kind of sit in their dark basement and they listen to their techno music and they fight the man and they probably know a mafia that's pretty awesome right I wish I knew a mafia no I don't um so they have no family they have no non- haacker friends and that is your
stereotypical hacker in their hoodie all right but as most of you know here sitting here today because I see not all of you are wearing black hoodies but really we don't look like like that um I mean some of us may have some of those characteristics which is fine and it's cool but all of them no um not all of us started going to Defcon when we were 10 not all of us started coding when we were five the only thing that really ties our community together at a fundamental level is that we like to take things apart and see how they work and make them do different things hacking at its most fundamental level
understanding how things work understanding how to make computers do different things and electronics do different things we might share some interests like uh there's a big Trend towards Lockport and uh a lot of us like electronic music and stuff yeah we might share some interest in small groups but we're all very Unique Individuals and we all have very very different backstories than the one I just showed you that's our imaginary hacker has so first of all if I can get three things across you today only three things it's not that hard it's time to be stop being embarrassed about whatever work is on our resume before we became an infosec professional or a hacker that
means everything from working in it to working retail to being in the military to you know being an an a uh you know an apple picker or something you know anything um that's all awesome all that work experience makes us a better person and secondly as a correlat to that um it's time to stop be embarrassed about our Hobbies um we don't always have to pick locks some of us like totally different non-technical things um some people like clothing some people like sports and uh all of that is awesome and it's all important you none of I don't see any imposters in this room I'm trying I have like a second sense for imposters and
I'm looking out at all of you and I don't see anybody here who's not allowed to be here because they're not haacker enough well maybe one no okay all right guys security is needed everywhere in our world right can we all agree on that security is needed in all kinds of places from you know the retail industry to the medical industry all over the place information security and understanding how hackers work is really important um our information our privacy none of that exists in a vacuum and we're facing a lot of problems I think most of us can agree on that too um so what I did is I surveyed like a ton of people most of which are in this room
back at around the uh New Year and I said what are you worried about in 2017 so anybody who participated in that thank you very very much you're awesome so I basically said what scares you you know either being a hobbyist or a student or a professional working in infosec or it what's the security problems that make you really really nervous and I took all those answers and I kind of generalized them into Cate atories and I picked the top 10 and uh what we're going to talk about today is those top 10 things that you guys have said that you're scared about and our news Medi tends to agree when we're talking about security and hacking and
we're going to talk about all those things in your background that you think are totally uncool and un haacker and how those are so so so important for solving those problems okay so the name of the talk is about Landing a plane and uh the reason this talk came about is I was having a conversation with a bunch of people who like myself have Aviation degrees as well as uh network security degrees and uh we were aming that we had enough skills between all of us from our prior work in aviation that we could probably get a 747 on the ground not in you know in one piece not in pieces which is pretty cool um so there's a lot of
Aviation Security concerns out there right so there's the insides of the plane the the the sidey dragon stuff the what's connected to what IP wise um is your guest Wi-Fi connected to your avionic systems then of course there's air traffic control which is so critical to our aircraft not running into each other or running into static objects or the ground then there's all the things that Pilots use I mean I'm not this is a whole another talk on its own there's all the systems that Pilots use to fly when they can't see or visibility is limited um to navigate um the IFR type systems ILS ads Las um all the things the signals that are going through the
air that tell the the aircraft where it is um and then finally there's everything at the airport the passenger security the flight line security and the security of your baggage and the Privacy involved so a lot of people are worried about that all right so we know that to solve these hacker type problems we're going to need some people with some security skills doesn't have to be our super hacker in the green text on the black background who we talked about earlier because that person probably doesn't exist which is probably good um so we know we need some some hacker skills in our vend diagram but we need some other stuff to really solve this problem we need people
who know aircraft avionics uh things about navad that are satellite or groundbased um we need people who know how aircraft radio works we need to know um we need people who know about aerospace engineering and how aircraft fly we need people who have experience with how air traffic control does things because that's not all documented out in neat wikis for us um we need Pilots because learning how to fly an aircraft really well takes a lot of practice and a lot of training um and uh that's not necessarily an easy thing for a hacker to pick up overnight um we need flight engine engers we need people who know how airports work right so we need those two
circles in the ven diagram to solve this these sets of problems having to deal with Aviation Security all right guys I know it's late in the afternoon and I know everybody's sleepy and I know that uh Twitter and stuff is really exciting but we've reached the uh unfortunate audience participation demo segment of this talk um so okay pretty much everybody in here raise your hand if you consider yourself a hacker either professionally hobbyist or just as a student uh interest yeah a lot of hands here so pretty much everybody in here says there's some type of hacker of varying skill levels and various niches super cool you filled one circle of that V diagram here's where it gets
hard I need everybody who fits a category in that second Circle in the ven diagram which I'm going to show you again in a minute to raise your hand if you've done one of those things as a job in your college in a college or a tech school even if you didn't complete it or as a hobbyist and if you fit more than one of those categories I would appreciate it very very much if you would raise two hands or you'd stand up this won't work without you guys I'm putting all my faith in the community there's already hands look at you guys all right so first ven diagram we've got our hacker second vend diagram who fits one of
these other categories either oh my god there are a lot of X Aviation people here awesome all right I was inm once that's awesome so we're talking about Aviation maintainers radar techs aerospace engineering aircraft enthusiasts people who have worked in air uh air traffic control Pilots Electronics techs radio techs people who have worked around aircraft all of you are the necessary people and to fix to fix this critical problem to do the talks to give people the information they need to solve these problems you are the necessary bridge between those fields we need you so let's talk about another problem you guys so don't feel bad if you weren't uh if you weren't um one of the people who
raised their hand in this section because we've got lots more problems that are really hard to solve oh boy so um some people have already done some interesting research in this space um Chris Roberts of course everybody knows about him and his uh various assorted Adventures um he uh so what I'm going to do here is I'm going to talk about a few talks and you can go ahead and take a picture of these slides if you like these are talks I thought were really interesting on Bridging the two Fields um some top recommendations um I tried not to center around a specific con but uh we've got render man talking about uh hacking airplanes again uh
we've got Aviation Security hugot teso we've got um uh oh the adsb talk um by C uh that was fantastic I really enjoyed that all right second problem all right so we all kind of agree that human beings cause problems in security you know that's always the thing we complain about uh oh my God our users we're never going to solve any security problems because they keep clicking on things yeah okay we exist to serve and users I'm sorry we're there to secure them to make business secure we cannot operate security vacuum and it's uh unfortunate cuz we'd be super secure if we never had to secure any people or any of their things um and we know that uh there's
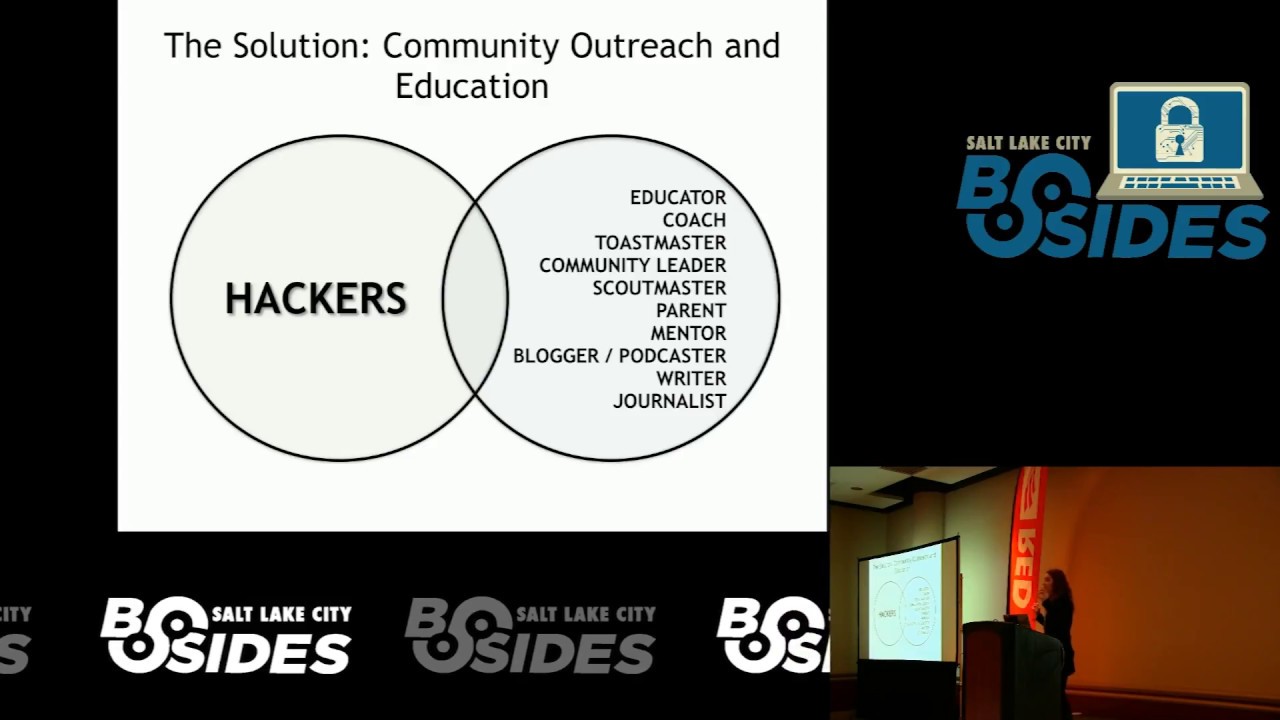
more and more digital devices out there all the time that are operated by humans which pose a big security risk and we know that uh we don't really control the media out the media outreach and the media message about hacking still I mean there's a lot of fud going around in the news media space about computer security and uh if you're up on that screen thank you again for your commentary on why this is a terrible terrible problem I appreciate it very much all right so our V diagram for community outreach and education um if you are or have been or have a hobby doing or have had education as in education or experience as a coach as a
Toastmaster a community leader a scout master a parent a mentor a blogger or podcaster a writer or a journalist I would appreciate it if you would raise a hand if you fit more than one of those categories if you could raise two hands or stand up I'd appreciate it oh my god there look at all those hands I wish I could turn the camera around you guys we need you not everybody in security has those social and education skills we need you to tell us how to do those things better so even if you don't think you're the best hacker or the most experienced infosec person out there you can lend so much by speaking at a
con on one of those things and how we can use it in security to solve this problem of reaching users and reaching the news media and some interesting talks there hasn't been very many unfortunately um I went hunting on this topic um there's uh a lot of space to do talks and do research in this space all right third problem hiring people and getting hired um I saw a lot of complaints about both um yes it can be hard to break into infosec especially if you're in the wrong place and it could be really hired hard to hire people who are experienced and are interested and motivated um those connections can be very hard to make um
we know that we're going to need more people in security and we know that we're going to need more qualified people and graduating with a college degree doesn't necessarily make people qualified or motivated or interested in really learning about security um inclusion is a big problem um we have trouble reaching out to minorities and that can be Geographic as well as uh any kind of social minority or ethnic minority um we have a hard time of hiring people so all right so we've got our hacker Circle we need people who have a little knowledge of infos and hacking but we also need people who and you know the drill now guys it's not that bad I hope
it's not that bad if anybody's arm falls off I will try to sew it back on for you if you have been a recruiter a coach of any type A hiring manager a teacher an office administrator Human Resources a mentor or a tutor a psychologist or a technical writer or if you've done that as a hobby or had education in that if you could raise a hand more than one two hands all right not as many people but there's definitely people out there again we need you to learn how to better train people and get the message out to people um who want to get into the field some interesting talks there's been quite a few but there's a lot of
ground to cover there um a lot of interesting work by Johnny Christmas and Eve Adams um on recruiting and getting a starting a career in infosec um there's been a couple of panels at Defcon that were very very good um all again of these are formatted like they are on YouTube or iron geek.com so you can go look at the talks if you're interested in seeing them or learning more all right next problem attribution everybody cringes I see people looking angrily at me for just using the word attribution on a slide that's great um all right so obviously 2016 and this is a non-political Zone um again as several other speakers have said um 2016 brought attribution really
into the media Spotlight um we're talking about countries hacking other countries influencing things uh you know having influence on purchasing marketing all kinds of different things um attribution of attackers is really really hard and that's kind of a catchphrase but it really is very very difficult it takes a specialized skill set um where it's necessary it's very very necessary however when you're talking about countries going to war or you know sanction in other countries um or you know corporations choosing not to do business in a country um so it's something that we need to do to some degree in some places occasionally and we're not very good at doing it and it's really hard and we are lacking people
with new ideas on how to do it all right so this is a different set of people and it's kind of a more unique skill set but I think that there's probably a few people who have done this either in their college program OR tech school program or in the military or as a previous career so let's go through a few different roles that we really need information and training from as Security Professionals so that what people who people with experience in intelligence analysis Foreign Studies National Security Linguistics and translation of course people who are bilingual especially in languages that are in sensitive regions from a national security perspective anthrop ologists and I'll talk about
that in a second politics and law enforcement so if anybody has experience in one of those roles please there's a few people out there there's a few people who have two hands up right now you guys with two hands up right now we need you um this is a big problem to tackle um and it might be kind of odd to think about anthropology being necessary for solving the attribution problem but um you've got talks like uh Dr samples um who went and looked at soft indicators in attacks like what hours of day did they work and when did they take breaks because some countries militaries give their people breaks and others don't some people make them work three
weeks straight without a day off some of them give them a day off to worship or something so she used those anthropological indicators to start identifying threat actors on a network so all of those different skill sets about looking at other countries looking at language um looking at uh different cultures can be very very useful in analyzing threats and we need those creative ideas to solve this problem so thank you for everybody who raised your hand all right this is a problem that a lot of people are familiar with business pressures and budgets um raise your hand if you've ever had a problem getting enough money to do infosec well okay all right just making sure yeah there's a
few hands there all right for the people at home I hope you're following along um so Executives still buy shiny black boxes that don't help us yes we know that um and business can sometimes override security to absurd levels um Beyond what's risk acceptable by a sensible risk management assessment um and we sometimes lose arguments that we should be winning for the sake of security yes we exist to serve the business but there are points where people hold the line to an unrealistic level where a good risk manager would say we need to make some concessions for security here um no you can't run Windows NT anymore connected to the network with your payment processing
stuff um all right so that's definitely a problem let's talk about our vend diagram here so we have our accountants we have our people who have done sales either corporate or retail we have people who have done business administration who can tell us like how to associate with business how to associate with with Executives we have Finance people who can tell us how budgets are made and uh Finance decisions are made at a corporate level we have project managers who know how to address schedules and budgets to an executive we have uh business Liaisons we have Entre entrepreneurs who have done this on their own and understand how to run a small business and hire
people and uh associate with customers and um we have people who have just done a lot of management and know how to make those relationships work so again I'm not going to tell you guys this time you know the drill all right hands all right there are a lot of people who have done those things we need you we need you to give talks we need you to give trainings even if they're informal you know write a blog tell us how we can solve this problem you are bringing wonderful expertise to a problem that's distressing a lot of people we just saw the show of hands some interesting talks we have um oh Coleman Kane yeah that was a
terrific talk on doing maler analysis on a on a tight budget um and uh yeah hacking uh hacking Senior Management at bides London was wonderful using social engineering skills to get your Senior Management to understand what you're saying um so yeah there's a lot of space for talks there there's a lot of problems all right next problem law and policy um so we know that there's been a lot of attention on the the Cyber this year yes um and a lot of it has been Incorrect and misguided attention and a lot of us a lot of it will end up getting us in trouble eventually um legislation that has been created and uh suggested over the last
couple years has not been useful from a security perspective even though legislators think it is and um it can also looking at parts of the EU really inhibit our ability to do our job as pentesters or white hats um or security researchers Etc if it restricts our tool use or restricts our ability to report bugs or makes us more liable for damages when we do to solve those problems I need lawyers I need people who have studied law I need people who have written policy and worked with the government to create policy and legislation Ian people who have actually done work as an elected official you know it doesn't have to be a congressman but maybe just
working at a m Municipal level understanding how to uh politicize issues properly and uh get the message across to other elected officials we need uh people who have worked in journalism who know how to address the public and uh address other journalists when there's misconceptions and uh also tell us how to deal with it when we're misquoted or we're not being uh paid attention to on a critical issue and we need of course even formed voters who are spending the time to read bills and understand how they work and political activists so Hand show who fits one of those categories who fits two of two or more of those categories there's not a lot of people out there so
that makes it even more important that you guys help um I know this is a much more specific skill set I'm asking for like lawyers and stuff and I have utmost respect for people who study computer law and then get an infos SEC and learn those two skill sets but when you're out there and there are a few people giving talks we really need your help um and thanks to all the eff lawyers who are giving talks every con talking about this is the policy this is how it affects you making it human making it understandable for people in security but we need more of that um especially right now with all the new legislation
about cyber coming into play all right problem number seven industrial control systems and skada um all of our stuff is connected to networks now and it's terrible and it's terrifying um Power Water electrical oil and gas the list goes on and on and on um transportation infrastructures our traffic lights um lots of things that are affect our daily lives in very very critical ways are connected to IP networks or uh you know more Legacy networks that are still being at some point converted to IP and we've proven multiple times during conferences that they are very very vulnerable to attacks and in pentests and in real life cases where there have been kinetic effects um so far fairly limited but there's
definitely been cases I bet some of you are thinking about some right now so this is a little bit harder to talk about um we need people who know who understand and have learned Electronics very well because we're often dealing with Legacy computer systems but even more critical than that we need people who have worked on those Legacy systems and now have moved into infosec we need people who understand how computers in the 1970s and 1980s worked because a lot of those are still in place albeit with IP conversion or translation and they're still being used to control critical systems and they've been made that much more vulnerable by their Network um we need people who know
physical security um we need people who know how to use shoden we need people who know Legacy code um so if you fit any of those roles I think there might only be a couple people out there who know any of those Legacy systems or have worked uh extensively show done I'd appreciate it if you could raise a hand but there's a few people out there that's terrific you guys so again we need more talks like these uh we need people talking about how those not just how those devices can be exploited but how to secure them and then more importantly the thing I see vastly missing out there is telling infosec people and hackers how those things work
okay because it may seem simple to you how a water pump from 1980 works or how an elevator works from 1978 but it's not simple to us we have never seen that work before we've never seen the diagrams for them we've never seen what kind of traffic they generate especially if it's proprietary we need you to get out there and tell us how things work so we can learn how to secure them all right internet of internet of things so uh we connect a lot of stuff to the internet right uh everything from uh TVs and phones to now like Barbie dolls and stuff um we connect a lot of stuff to the internet and it's really
terrible and uh people want to buy those things cheap and they want them to do cool things on their apps on their apps on their phones or whatever so cheap production fast production that means cutting corners and security and so we've got a lot of insecure devices out there on the internet that were cheaply made poorly documented and as we've learned with Mirai and dine uh a great attack vector and then also as we learned in the last uh few days possibly a uh well we didn't learn that actually we already knew that that uh iot devices make great spy devices we were talking about that like years ago but as the rest of the public learned a couple days
ago uh iot devices can be used to spy on people and that's not necessarily talking about you know three-letter agencies that's talking about people looking at people's baby cameras on showen um and uh all kinds of other things that are harmful to people's privacy so this is a kind of broader category but uh if you buy iot devices for your kids or your family if you bought them for Christmas for people why not sit down with them and figure out how they work um if you're buying them if you're designing them uh if you work for a company that makes them and you have access to the devices when they're in production or even after
they're in production and they're out on the shelves that you're a wonderful candidate to start taking them apart and figuring out how to secure them better and uh if you just like Electronics um a lot of things are are um open to you that way so if you buy iot cameras toys home security appliances like baby monitors like I was talking about um or uh home appliances that are iot which are sometimes your only option when you're buying appliances now spend some time learning how to take them apart and tell us how you did it put it on your blog tell us how they're insecure once you've reported uh ethically um so if you fit
into one of those categories there in this ven diagram if you could raise your hand you bought an iot thing you work for an iot company um yeah okay so there's a bunch of people out there who could be doing some iot research it doesn't take a lot of time you know go to iot Village at a con and you know um you can you can do a lot of good in a day or two and of course we have endless talks about cool iot stuff and there's endless possibility to talk about new stuff um obviously uh hello Barbie being the most high-profile amusing uh example in recent history but we have all kinds of
interesting talks like Runa sandvik's Linux powered rifle getting up there on stage with that was amazing um if you haven't seen that I highly recommend it especially if you like Firearms um but yeah there's potential to tear into all of those devices and I really need your help there all right medical device security this is a matter of life or death um a lot of these things that we've talked about I mean yeah uh IC when you're talking about like traffic control could be a matter of life and death but for the most part the things we've talked about so far are nuisances they make it hard for us to do job they make us it hard for us to do business
but medical device security that's like people living versus people dying um and then even beyond that there's still patient records with tremendously personal data that we've seen breached over and over and over again um there's um the threat of ransomware where we see like medical establishments and hospitals being taken for thousands and thousands and thousands of dollars because they don't have backups and they get hit with ransomware and the most critical thing being medical devices and you know uh either uh medical devices that are external or internal to the body so medical device security we need some doctors and need some healthcare workers here I mean even if you did it 20 years ago you can still lend a lot to
the conversation we need people who have worked in healthcare and tell us how Healthcare the foibles of how Healthcare operates we need people who have been EMT and worked with medical devices we need people who even in a volunteer status work as a first responder um we need people who have actually used or have you know people in a few degrees of separation who are close to them who use medical devices that are networked um and uh we need people who have been caregivers of people who need medical devices because not just because it's important to you but because you have firsthand experience in the foibles and the issues in securing those systems and how they actually operate in a real
environment the manual can only tell you so much about how like a pace a pacemaker works I don't have a pacemaker I don't know what it's like to have a pacemaker or have one installed I don't know how often they need maintenance um I don't know if there's different types that's just not something I've ever torn into but I know there's people out here who know the answers to all of those questions if you could get up here for a half an hour or 15 minutes and tell us how pacemakers work and from a network perspective when we're talking about like Bluetooth devices what they do and why they need to do it that would be so
critical for doing more security research and inspiring people to get more interested in that research so if you fall into any of those categories Healthcare EMT first responder um within a few degrees of a person who uses a medical device um or um requires some uh consistent medical care that uh involves medical devices um if you've been a caregiver um or you work in medical products or for a medical Product Company um if you could raise a hand raise two if more than one applies I know that this can be a sensitive subject but again we are dealing with matters of life and death um we're dealing with can this pacemaker be hacked or can it not be hacked and
how do we deter it being hacked if if it is already vulnerable what do we do who do we report it to we need you to talk about those things if you can um because you could honestly be saving lives um okay so there's been a lot of interesting talks on medical devices um Scott Irvin does tons of talks and they're all fascinating um I really liked um the most recent shukan Jeff Dodge did a talk on uh where he was and I mean this is this is kind of situation where you analyze a device that is relevant to you that you have experience with and you are talking about something that's utterly fascinating to people um
cyborg self- hacking um and then um of course there's simpler things like Hippa that we can I really liked the talk from Louisville infosec on what Healthcare can learn from the banking industry that's somebody who's in the banking industry talking about bringing that skill set over to medical devices in the medical field so again taking multiple Fields bridging them together and doing security better all right finally po device security um and this is about software Dev and the secur dev developers still lack uh tack on security instead of building it in from the ground up um new devices it we're talking about the problem of cutting Corners in security because we need to get things out fast um we need more
stuff we need to doubt faster we have less budget we have less people and uh then there's a more fundamental problem that people aren't being taught to code securely which is very unfortunate and we need people's help with that and um for that we're going to need people who are info in infosec now who have experience as a coder a programmer a developer software engineer people especially who have worked in devops and understand how that works um and then we can also get a lot of insight from Project managers and evangelists and um even software consumers so if you're any of those things if you could raise a hand we need your help yeah hopefully everybody's
hand is up because we're talking about software consumer oh my God all right you guys there are huge problems in the software development life life cycle pertaining to security and you can all give insights and you can all out do Outreach to the software development Community um and there's been a lot of interesting talks including one this weekend that I thought was really cool by David Moore is he here I don't know but uh that was super awesome uh trying to trying to make fuzzing more available um we need your help figuring out how to fix the problem of inserting security after the fact instead of building in from the ground up and that can include
everything from educating students who are learning how to program about security to figuring out how to solve those problems at a corporate level so we need a lot of help solving that problem but it's doable it's fixable so I added an extra one because you guys aren't totally sick of me talking it I hope and that is us um into SE has a huge problem with burnout and unfortunately it has problems with other things too like substance abuse and alcoholism um we've had some suicides in the community um we have health problems and there's a lot of very healthy happy people in our field and I certainly don't want to give the impression that we're a bunch of drunks or delinquents
or something because we're not but there are problems that exist and we should recognize them and then even Beyond those more dire problems we're in an echo chamber and it's it's very frustrating we can hardly ever break out um we're often Talking to Ourselves inside our own conferences and that can make problems seem really insurmountable like the problems we just discussed today and there's a lot of people out there who have experience who can help us start fixing those problems and those are a wide range of backgrounds and hobbies and niches that we've experienced in our lives from people who have been mentors who know how to do mentoring for young people getting into the field or people who are having a
hard time nutritionists who can tell us how to eat and live better um when we're struggling with that with long hours and hardly any time off um healthc Care Professionals who can talk about the impact of stress and what we should do about it um Fitness coaches who can tell us how to be healthier people people who are you know the old gym rats I'm kind of a gymrat so yeah people who like like the fitness thing and enjoy it and it's their hobby don't be ashamed of liking Sports and being an infos tell us how to be healthier that's really important counselors who know how to sit down with people who are having trouble
um and then finally just friends and human beings who have dealt with these problems and uh maybe have gone through these same things themselves at some point in their lives so if you fit any of those categories are there a few friends and humans in here I'm I'm going to walk around and see if anybody's not raising their hand that they're a human cuz that'd be awesome if there's an alien in here that'd be so cool anyway all right you guys that's a really important problem and people are like struggling and in serious serious problems and all it would take is your expertise in this thing that you think is totally unimportant and unrelated to infos saac
and it makes you a less cool hacker getting out there and talking about it for half an hour could change their life you could change somebody's life and there's been some interesting talks about that Jack Daniel does a wonderful talk series on uh on you know he he talks a lot about health and well Wellness in infosec now um but there's been talk on suicide risk awareness um how to uh deal with burnout um how to deal with stress but we need more of that I mean look at the years on some of these these have uh these were a few years ago there's there's plenty of space for you to help all right so we've talked about a lot of
problems today a lot of things that a lot of us are really stressed out about that seem insurmountable in 2017 2018 and Beyond but none of those problems are insurmountable I just gave you a bunch of avenues where you guys can help solve them and maybe it's not the leadest talk maybe you're not up here you know poning boxes but it's really important that you Bridge those pieces of experience together with a little hard work we can solve those problems and for every daunting challenge that people brought up when I surveyed them a cross discip a cross-discipline skill set can solve that problem or multiple cross- discipline skill sets um and those non-technical skills that you think are
embarrassing or boring you're like oh my God I did 10 years of work in this field before I moved to infosec and now there's going to be agism and I'm never going to be a cool hacker that's not true you're going to be the coolest hacker because you're going to take those 10 years of experience doing something else and tell us how to tie those into infosec you don't have to be the leadest hacker to be really helpful to give a talk to motivate people and you're not alone you know if you're interested in one of these topics and you're like well I kind of know about this but I'm missing this part of the ven diagram go find somebody else
who's interested in it too and combine both of your skill sets and make your full vend diagram of skills to solve the problem Be Clever but no infosec hacking training will make you the best hacker in the world that comes from you that comes from your experience as a human being that comes from you being well-rounded and having interesting creative ideas all right let's talk we got a few minutes anybody have any questions comments stories go ahead hi
hi all right well you're going to have to get some basic skills in security somehow um but a lot of that isn't coming into a job interview saying I know how to use all these tools and I'm awesome at poning boxes it's more like I have an interest in security and I want to learn more about it and uh this is what I've been doing to learn about security or what I've been reading so having like a home lab and saying I don't know a lot yet but I built a lab at home I followed this blog I've tried to learn some basic tools and I think it's really interesting because I saw this talk or that talk showing
that motivation and interest and then saying I'm bringing in these other skills like I know personally you ran a business which is awesome and and uh I was I was gushing over that yesterday I'm like oh my God you actually know how to like hire employees and manage people and manage time you know that's all wonderful stuff that is really beneficial to doing any kind of work including infosec work so take those skills that are like non-hacking specific that still are very beneficial to infosec and then combine them with I'm interested in this I really want to learn this I'm motivated to learn more this is what I've done so far make sense cool thank you anybody
else questions comments thoughts all right all right um well we kind of did the hand raises for the aviation thing but um do we have any pilots in here all right we've got some Pilots do we have any AV avionics people other than me in here emps people who know avionics do we have any crew Chiefs or flight engineers in here all right we've got a few all right I think that we could probably get a plane on the ground without it being in pieces with the people in this room and that was totally off the seat of my pants so I'm really really glad that somebody raised their hand there so thank you that was fun all
right well you know I number of hours over 10,000 10,000 hours in Microsoft light simulator anybody all right great awesome awesome I feel safer already yep I I trust you guys I trust you guys not to crash the plane all right who else go ahead he has an airport where if nobody heard that he has an airport where you can land the plane it's really great I I'm not going to dig into that right now all right you guys anybody else thank you all for participating and for raising your hands and making my demo not fail miserably I really appreciate it um I also appreciate everybody coming out to bide Salt Lake City the team here has been wonderful if
we could give the team who put on bide Salt Lake City a round of applause I'd really appreciate it cuz they did awesome