The Art of CISO
Show transcript [en]
hello and welcome everyone my name is zaina antoine and in the next good half an hour or so i'd like to make a call to think together the title of this presentation is the art of ceso and by the end of this session even though there will not be any demo here i hope that by mixing art logic technology and the people behind all of these can assist us in enhancing cyber security a little bit of my background i was lucky that i could have hands-on experience of a great variety of aspects of i.t including cabling building up new branch offices supporting client and server side computers and firewalls during the outsourcing era in the early
2000s i was privileged that i could be a member of corporate ito the team of a multinational corporation traveling the world to audit the i.t services provided to the customers of this company and the id security posture that was delivered to them during the early 2010s later in the late 2010s i could lead a program that aimed to harmonize regulatory requirements globally and translate those to id controls and in the last one and a half year or so i act as a cso for a number of subsidies of one of the largest banks in hungary so with that introduction let me start to frustrate you on the next slide is there anything in common with these
two pictures well what possibly could be in common in leonardo da vinci and the i.t guys of the 1990s the caesar of our modern corporate world and the art that we have in the title of this presentation by the end of this session we will establish a link and see that these seemingly distant things are not that far from each other and the title hopefully will make some sense as well but for that we have to start a little bit further we need to understand a little bit of history where we came from the common thing behind both of these pictures is the concept and that concept is already dead wow some might say that's gross
how can something be said even or some might say well hell yeah it's dead of course so well the common thing the concept behind leonardo da vinci's famous picture and a computer that i used to learn i.t in high school is lying within the concept that they are representing
leonardo was a polyhistor or as literature often refer to him a renaissance man the worst polyhistor originated from the latin and ancient greek meaning greatly learned they are men who use both left brain and right brain type of thinking and as a result these are the characteristics of them curious risk taker creative has perseverance self-discipline has a thirst for knowledge and new experiences excellence in physical intellectual artistic and social fields and including deep experience in at least one of the field and is exceptional in some other fields and most importantly they are always learning in the early stages of the computing era when someone knew how to use a computer and how to fix it they knew the
computers period at that time the iit guy of the 1990s was some kind of polyhistor as they knew the machine they could write code they could fix hardware issues and do all kinds of magical stuff however like beginning from the renaissance age the aviable knowledge started to grow within this industry as well well it became an industry after all and became first harder and then later impossible for someone to became a real polyhistory
similarly in our modern age things getting more and more connected and the available knowledge within the iit industry grew well it became an industry for starters people start to get specialized corporations became more and more complex entities with numerous business units and organizations within them of which more often than not have at least competing interests segregation of duties and the specialized and standardized tasks within a workforce process resulted in isolation and that high level leaders are less able to oversight the cooperation as a whole compared to their ability to do so a decade ago technology became an integral part of the business in most cases without senior executives and the board's consciousness thus today we live in an era of
monoliths or specialists well sure you can say okay so what's the problem with that well almost 30 years ago two academic writers highlighted that business and marketing strategies should be viewed as interlocking rather than separate back then they stated this for businesses and marketing strategies and it was quite a thinking today i.t strategies can neither be overlooked nor handled separately what else is a problem well that humans don't change as fast as technology did while culture itself changed as well edgar shane defined organizational culture as a pattern of shared basic assumptions that the group learned as it solved its problems of external adaptation and internal integration that has worked well enough to be considered valid
and therefore to be taught to new members as the correct way to perceive think and feel in relation to those problems have you ever heard this we do things this way around here this is the way we always did it so what's the problem with specialists the problem is that people stuck with one way of thinking they have blinders on and they cannot see the big picture including the relationship and similarities between different things as i said it seems that the concept of the renaissance man is dead but what the heck does it have to do anything with the ceso and the title of this presentation well like in any good sandwich and i do
apologize for the vegetarians and vegans here the meat is in the middle and in the case of the word siso the letters i and s are in the middle meaning information and security and in the media another word is often used between these two which is cyber security we do believe that we know what they mean but do we really know so let's open up a little bit information what is information there are a number of different definitions according to the oxford dictionary in general it means facts provided or learned about something or someone in computer terms it defines this word as data that is processed stored or transmitted by a computer however we can use a different approach
like legal boxes if you like the little building boxes data information knowledge wisdom let's say for example that someone gets data from my computer's browsing history and since that i was looking for information about the security requirements of the hungarian nuclear power plant from the browsing history they can see that later i was listening to some german punk metal music and i was looking up to concerts of that band in berlin germany again later they can see that i was looking for flights from berlin to budapest so this is data once whoever got these individual data parts of my browsing history can say that she or he has a piece of information about me and
can make a deduction from these pieces of information and try to get knowledge from it using all these previous uh examples uh that whoever got this information um maybe got from my browsing history combined it with my family name antman which which is a german name someone might deduct that german cyberpunk wants to blow up pakish the hungarian nuclear power plant deduction yes knowledge and wisdom not quite see putting it like this it obviously feels bogus but in reality leaders are making decisions based on data that were organized into information by incorrect deductions and they believe that they are acting on knowledge based on information and wisdom while in fact they have not
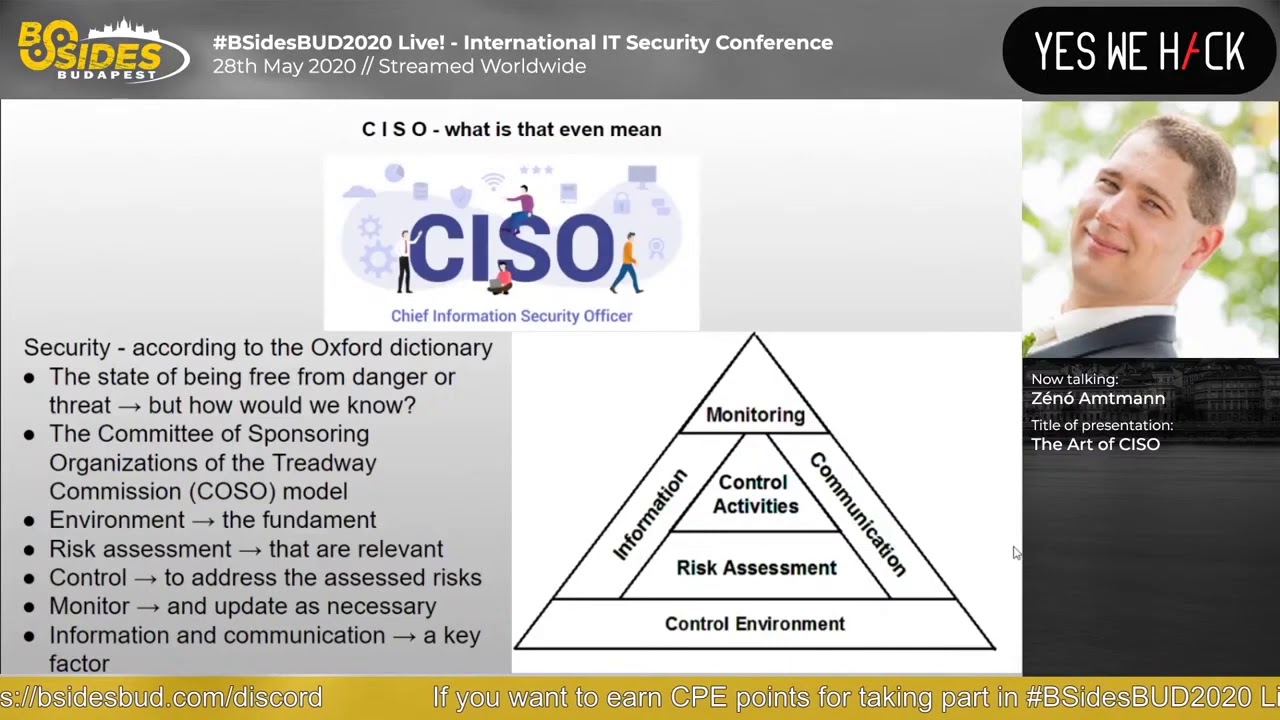
the second letter in the middle of the word is security this word is defined as the state of being free from danger or threat well this definition opens up a question the question that how could we know whether we are free from threat especially today when every source of news is full of reports of crimes data leakage attacking our personal and private information and so on the committee of sponsoring organizations of the trade way commission or koso developed the model and although it was updated in 2013 and it's a cube now i believe that for this purpose their original model could illustrate the concept i'd like to convey here better so control environment this is the basis and foundation of
everything only when we knew with real knowledge can we assess the potential risks that can affect it once we know the risks that are applicable to whatever we have we can develop controls to address these risks mitigate accept transfer once we put appropriate controls in place we just have to monitor any changes change any changes in these elements and adjust as needed for which information and communication are a key and we come back to the communication part in just a little bit consequently there is another word that is commonly used amongst the previous two which i mentioned which is cyber security so let's have a little bit under the hood of the cyber part of this world
cyber according to media is derived from cybernetic which comes and originates from the greek word i don't even try to pronounce that but it means skilled in steering or governing cybernetics has been defined in numerous ways such as the art of steermanship the art of securing efficient operation the art of effective organization the art of interaction in dynamic networks or a science that is connected with the study of systems of any nature which are capable of receiving storing and processing information so as to use it for control okay so now that we know what is information what is security let's have a look of an element that plays an important part in the equation namely human beings the individuals
working within a company and their personality and my apologies again let's pause here for a second and let's look under the hood the word personality this word is originated from the latin word persona which was a mask that an actor wore during a play which signified his character by displaying it in an overamplified way according to the american psychological association personality refers to individuals differences in characteristic patterns of thinking feeling and behaving this different behavior can play a part in two dimensions firstly in a person's interactions with others and secondly an individual's reactions provided to stimulus from the external verb in other words in the first case some folks are talkative in a party some
others are there to eat drink and to be left alone in this second case someone might crack under pressure while some others get strength from it one of the most well known categorization of the second case is the myers-briggs type indicator or mbti which categorizes people from four different aspects and assessing people out of the 16 potential types for example extroverts and introverts for the first case minsberg's categorization is the most well known as he differentiated between ten roles and three categories without going too deeply into the topic i just like to highlight three which could contribute the best for a cso one of the most important roles lies within the information category namely the
disseminator role in the information age one of the most crucial key element is the ability to understand assimilate and appropriately rely information remember information and knowledge in the interpersonal category the two key roles for a ciso would be the leader and the liaison as motivation internally and representing unity externally is vital lastly the category related to the ability of decision making has two key roles which are the entrepreneur and the negotiator as the prior one needs to realize the opportunities both external and internal and negotiate it and bring it through senior management and the board as needed okay but why the heck are am i talking about this what do we want to achieve what's the end game well the end game is
to secure information secure information a data breach is an incident in which sensitive protected or confidential data has potentially been viewed stolen or used by an individual unauthorized to do so ibm defined the data breach as an event in which an individual's name and medical record and or a financial record or by an debit card is potentially put at risk either in electronic or paper format the distinction of paper format is important these numbers are actually scary cyber attack occurs every 39 seconds the average time to identify and contain a breach across all industries is 279 days it's more than nine months nine months and we can see the cost of the data breach which has
consistently risen over the past year and the cost to recover from a ransomware skyrocketed as well an interesting twist that ransomware attacks nowadays are actually threatening their victims to release data rather than asking money to unlock a computer than they started off with the number of data breaches increased by 54 in the half or first half of 2019 uh and in total more than 4.1 billion records have been exposed in the year 2019 so last year on december 4 2019 a security researcher discovered 2.7 billion email addresses and plain text passwords for more than one billion of them in an unsecured online database verizon's 2019 insider threat report estimates that insider threat caused more than third of all data
breaches as far as root causes the 2019 ibm study found that 51 percent was due to malicious attacks and 24 due to human error only 25 percent caused by system glitches according to a fourth article published in uh april uh this year 70 of all data breaches are originated from end points like laptop computers phones mobile devices pcs further due to the skyrocketed home office introductions across the globe due to this coveted 19 pandemic a may 2020 fourth article predicts that the biggest cyber attack in history will happen in the next six months well how is it possible that we have this many breaches how is it possible that with all of the increased spending and
focus on information security still 70 percent of all the breaches are originating from the endpoints well at the end of 2019 people are still using the passwords that you can see on the left in addition more than 44 million microsoft accounts were using passwords that had already been compromised elsewhere so the question seems obvious real people ever learn but the answer is not that obvious the world economic forum provides an annual platform and an opportunity for leaders and multi-stakeholders to engage with each other participants of this forum were asked to [Music] conduct and participate in the global risk perception survey which is published each year according to this year's report although more than 50 percent
of the world's population is online i let it think a little bit more than 50 percent of all the population in the world are online still approximately 1 million people go online for their first time each day let it fit this a little bit as well 1 million people go online for their first time every day therefore what might be repetitious and obvious for us in this conference room and whoever is listening to this there are 1 million individuals each day who have no clue in addition these new users are mostly from developing countries and in the world economic forum survey they concluded that today's emerging economies are expected to comprise six of the world's seven largest economies by 2050.
respondents of the survey also rated information infrastructure breakdown as the sixth most impactful risk in the years until 2030 and cyber attacks on critical infrastructure very very rated as the fifth top risk in 2020 and this is not just some irrational fear such attacks have already affected entire cities and multiple states for example in december 2019 new orleans had to declare a state of emergency due to a ransomware attack shortly before that the governor of louisiana had to do the same earlier in 2017 attacker could take down the emergency services number 911 in 12 states imagine the situation you want to ask for help from 9-1-1 or from 1-1-2 call the police and the service is down
could be shocking especially if you are in that situation when you would desperately need a help an interesting fact is that only 5.9 percent of the emergency centers had any program or plan to address events like that so public and private sectors are like at risk of being compromised and or held as a hostage organized cyber crime entities are joining forces and the likelihood of detection such an organization and the prosecution is estimated to be as low as 0.05 percent in the u.s we all heard about the software as a service and platform as a service model well there is a cyber crime as a service which is also a growing muslims model as the increasing sophistication of
tools on the darknet makes malicious services more affordable and easily accessible for anyone some experts stated after the new orleans state of emergency that cisos focus on technological defenses when they should also be patching their colleagues with regular stimulated attacks and security awareness trainings besides all of these threats the amount of data that we generate both structured and unstructured is exponentially and we almost could say concerningly growing in addition the fourth industrial revolution technologies will dramatically reshape economies and societies who makes money and how has already changed and this is still changing doctor zoltan chef ambassador of hungary to the oecd and the unesco quoted cleve humbly sheffield mathematician who stated that data is the new oil
and highlighted that on a data economy highlighted on a data economy conference in january 2018 that the age of globalization is over today there is a shift towards the age of technology and new economic models such as peer-to-peer economy sharing or on-demand eclipse collaborative economy and platform economies in the data-driven economy ownership is replaced by access and products by services according to the idc by 2020 50 of large enterprises will be generating data as a service revenue from the scale of data and by 2025 50 of the revenue will be generated by sharing economy while it was only five percent back in 2013. uber one of the world's largest taxi companies owns no vehicle facebook the most
popular media owner actually creates no content alibaba the most valuable retailer has no inventory and rbmb the world's largest accommodation provider owns no real estate since the industrial revolution the world has developed a complex supply chain from designers manufacturers to distributors to importers wholesalers and retailers it is what allowed billions of products to be made shipped both and enjoyed in all corners of the world however in recent times the power of the internet especially the mobile phone has unleashed a movement that's rapidly destroying these layers and moving power to new places so it's clear that demographics have changed even the skills that brought our society to wherever we are today have changed we previously mentioned
world economic forum survey concluded that approximately 50 percent of companies worldwide predict that automation will trim their current full-time workforce by 2022. and by that same year researchers expect at least 55 percent 54 of employees will need re-skilling and upskilling to complete their jobs folks this is just two years from today not in some distant future and in this economy where data is the new oil the question arises who owns and who controls the data and who is protecting all these information ok so we know all this see this but there is another hidden challenge besides the obvious ever increasing rate and sophistication of attack vectors which is unfortunately senior management and the corporate culture
that's harsh i know i know still it is our reality more often than not well we know that there is no such thing as 100 percent secure environment security costs money and when appropriate funding is requested from the board who might not have a clear understanding of the full depth of the i.t security as we discussed earlier the change happened without their consciousness they might ask okay so we are spending this money now on this fancy new firewall i understand but what's on the income side well this mindset unfortunately seems to be validated by a survey conducted amongst the csos that found that almost a quarter of interviewed cesos said that boards didn't accept or understand that
breaches are inevitable and said that they hold them personally accountable for any incidents so it would seem that culture and corporate and organizational culture plays a vital role here remember we talked about the importance of the foundation of everything earlier when we had a look at the corso triangle i mentioned that we'll discuss the information and communication part a little bit more later well this is later as it was mentioned there if senior management acts based on an understanding that it is not funded on knowledge they cannot act even with their best interest in place appropriately i have seen far too many times that middle management simply does not report yellow or red kpis or
slas to senior management because of various reasons it has to be green they said well in september 2015 electronics conglomerate toshiba admitted that it had overstated its earnings by nearly 2 billion over 7 years independent investigators found that toshiba had a corporate culture in which management decisions could not be challenged and employees were pressured into inappropriate accounting by postponing loss reports or move moving center certain loss and costs into later years another example probably one of the most well known to date and of course we can thank the birth of stocks and many regulations since then is the enron scandal the company reportedly has had a go-go culture in which senior officials cast aside traditional business controls
it is possible that all of these previously mentioned facts were part of the reason why 86 of the participants of the 2014 world economic forum survey identified a crisis in leadership as the world's most pressing issue issue and 51 of the respondents of the 2018 world economic forum survey expected that the risk of authoritarian leadership would increase in 2019 william h white an american organizational analyst said that the single biggest problem in communication is the illusion that it has taken place one of my first mentors said to me that thinking is hard word that is why so few people do it char sparrow a famous sociologist described today's world as a complex and tight coupled system
in which even a small issue can cause cascading effects that is why it is so important to start thinking again and see the big picture vincent van gogh said that great things are done by a series of small things brought together vince lombardi a famous american football coach said that the achievements of an organization are the results of the combined effort of each individual you can say that these sentences feel obvious or cliche but the fact is that in our world and day-to-day work we are doing the trim down blind sign the downwork of a whole we might not even oversee even more and in many cases we don't even realize this but we should because in the i.t work
the renaissance was only 30 years ago so why do i believe that it is an art to be a cso because they have to see the big picture understand the engine room understand the fly deck and the environment the playing field as well speak their respective languages and have the ability to relay between these layers however security is not even one-man show we are in this both together we are all responsible for the security of tomorrow the developer cannot say that i code this because i always did that in this way or because they didn't specify any security requirements why should i care everyone should work together do their part because a series of small
acts from different divisions and laws can produce a great deal and enhance security overall so it is not just the ceso who has to do the art it is us everyone who is listening to this recording uh everyone who is within this industry it is our shared responsibility towards ourselves and towards each other as well like in the way we are responsible for children we are responsible for those one million new children those individuals who go online for their first time every day it is our responsibility to develop applications in a safe way secure by design and not just because of the regulatory expectation but because we understand that it is in our best own interest as well
so if we'd like to see a better nicer picture of security of tomorrow we everyone who is listening to this presentation have the power we have the brushes in our hands so let's start painting it today thank you very much





