Who You Gonna Call When They Come for You......and They Will: Preparing for 'The Day', Incident Response, and Law Enforcement
Show original YouTube description
Show transcript [en]
all right thank you thanks mark good morning to the morning everybody thank you for having us uh we appreciate the invitation to come out and speak um before we get started let me just kind of put out there that this is really intended to be a discussion
there's a good likelihood that they will either as a victim or as a partner any number of reasons so we hope that you'll ask questions you'll engage with us and uh we'll prompt you that we'll get you out before the other two so you'll be first in line for chick-fil-a my name is brian i am the supervisor here in the augusta office so i supervise a team of agents both in statesboro i cover about 26 counties we also have in the room fortunately uh todd renner he supervises the cyber one of the cyber squads in atlanta uh he didn't realize i was gonna point him out but it is it is great that he's here
because the way the fbi and i'll talk about this in just a few minutes we're kind of we're organized geographically but also by so there's a there's a reason that he now coordinate uh almost on a daily basis certainly on a weekly basis uh to help provide support for the cyber community here in augusta and with that i'll like introduce himself and then we'll get started so good afternoon or good morning everyone i'm mike capacity i work for adp i'm the senior director for fraud detection and strategy prior to that i ran 24 7 incident response and detection for adp and before that i was involved with dod for a while most of you a lot of people in
the room knew me at various parts of my career i want to remind everybody that even though brian and i have roles and we have employers we are speaking here as ourselves and even if our employer should happen to agree with us that's nothing we can control it's very important say something stupid i don't want to be fired all right so we'll get started let's kind of talk briefly
really maybe all right so question who is law enforcement when do you deal with law enforcement law enforcement generally just divided into three types of organizations federal you've got obviously fbi you've got secret service and then almost every federal agency has some law enforcement component associated with it i think there's even one for the department of education they go down to state this is kind of a georgia focus but in georgia you have the georgia bureau of investigation in some states you're going to find you have state police agencies that fill that role and then at the local level you have a county sheriff or a police department you have some sort of superior court organization that's going
to deal with local crimes state crimes and then federal crimes and this is important because when you decide you're going to involve law enforcement who can help you who's available who's going to have interest in your case you know who can drive down and actually visit your site if that's necessary or visit the site where the crime occurred or visit the data center where the crime occurred so there's lots of nuance to this and it's important for us as law enforcement that we all we we work with with the fbi i work with everybody on that list very close when we talk to you all about it's not you know certainly there's certain things that we definitely want
you to reach out to the fbi first but we're never going to discourage you from reaching out to locals if that's if you have that relationship already established it's incumbent on me and my office to make sure i then have those partnerships with the local law enforcement or the gbi that they know hey this may be larger than something we can handle or this may not be jurisdictionally something that we're able to help with so then they would come to me and then we would assist them as well so this is just kind of a just to let you know there's a there's a large law enforcement population um but you should build those those
partnerships at all levels if you can so it gets a little tricky in the federal system here a lot of different organizations i mean there's a lot of organizations uh affect dod nsa here locally that you hear about you you know they're involved in in cyber cyber warfare cyber threats so what do they what do they actually do and how do we work together it's it's not as simple and this is probably a difficult chart to read but i'll kind of explain it to you in simple terms dhs is more on the protection side infrastructure they they try to mitigate and recover dod nsa that's the national security side obviously you know they're the war
fighters offense and defensive protection of the united states they do a lot more international and then you have the fbi doj attribution if we have victims here in the united states trying to figure out where that victimization came from who the identify who the bad actors are if it's something we can prosecute then working directly with doj so that we can either get some sort of restitution or or criminal uh prosecution on those individuals that that's you know that's a very broad that's how the federal kind of system works and i'm not going to read we have a cyber mission for the fbi is broad uh the biggest thing we're trying to do is bring uh
world-class capabilities so that we can we can basically take bad actors and try to prevent them from hitting us in the united states we can't always prosecute folks i mean a lot of times you know this is often unclassified briefing so i can't go into a lot of detail about nation states or or some of the things that that they're doing but where we can't prosecute we want to try to deter and we bring a lot of resources we have a tremendous team of folks both in atlanta and then locally that will work with your organization to try to identify and and try to prevent those these crimes before they happen so that you can you cannot become a victim
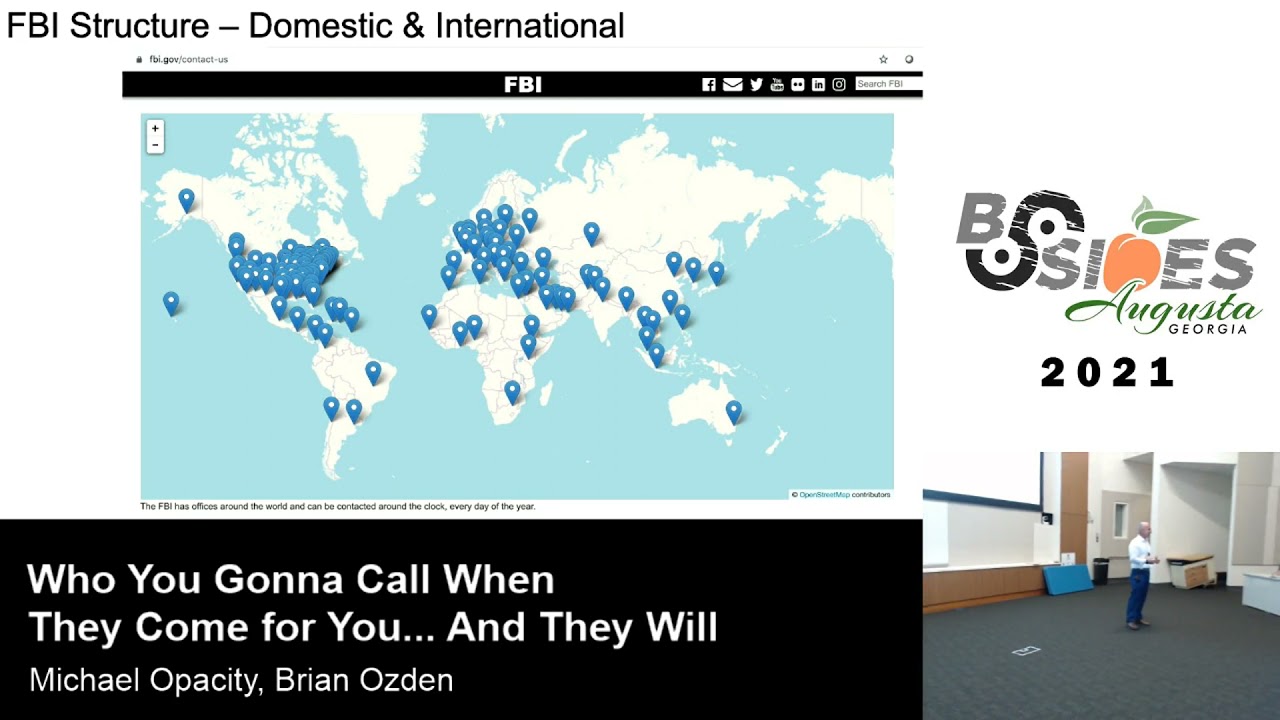
but if you are we also give you mechanisms to try to recover and and prosecute so the fbi is kind of structured we have 56 field offices throughout the united states georgia's covered by one field office that's atlanta but there's 14 resident agencies like mark talked about the augusta office the reason why we have these resident agencies so you can build these personal relationships with the folks in the local geography so i you know my goal is to know everybody in here so you guys can you know see my name if something comes up if you get if you become a victim of a crime and it's cyber related i want you to be able to
call me i want you to be able to to reach out to the local fbi if i can't handle it locally if it's something that's above the capabilities and we do have cyber agents here that are very capable but if it's something that we can't handle we have the resources of the atlanta division we also have our headquarters element and if you look at this map those are our offices across the world we have legal attaches so if there's a bad actor in another country we have the ability to reach back to those countries and try to work with their law enforcement to get whatever you know whatever prosecution or or recovery we can do so
and these cases they've moved very fast so we have to have this flexibility and have to have these resources already in place to have any chance to be able to make the recoveries so what do you what can you expect from us i mean this is really the big question people are always reluctant the thing that we find within law enforcement especially the fbi's a lot of times victims don't want to come to us because they're worried about you know is it going to look bad for them is this going to be are we just looking to put it on tv are we going to publicize this and that's not the case we're going to make every effort to to help the
victim and that's minimizing downtime minimizing the time that your organization is not operational because clearly that's going to be your number one priority how long if you get hit by ransomware or or or something that shuts your network down we're going to try to get in there we're going to try to collect evidence we're going to try to do it in a way that that minimizes your exposure your downtime we're also going to make every every effort to work with you in terms of of media relationships not every case is gonna the news but obviously some like colonial pipeline was one recently and and i know todd has worked a number of of big cases where as
soon as they you know as soon as they happen you know they could have national implications so we're going to work with your folks to try to minimize any kind of publicity that that you're not looking for we also want to keep the victims informed what we do throughout our investigation is is work with the whatever level of the organization you want us to whether that's the the cio level or or the implementation level we'll make sure that we're talking to them and we're keeping them informed of the actions that we're doing and what we're saying and then the only negative that we do have is a lot of times our cases can be lengthy uh most
fbi federal cases they're not they're not they're not quick turn operations they take a lot of resources and they can tend to be launched we would we try to keep you informed throughout that but but some of them can last several years if if that's how long it takes to get the results we're looking for okay i keep getting off i just think the computer doesn't like me okay so one of the important things to remember when you have a cyber event that takes place on your premises is that there's actually three locations that are in play there's the data center where the malicious activity occurred there's where the victim of the crime if you
have a financial crime in particular if that victim was in another jurisdiction and also the location of the criminal if you can determine that so all three of those positions are in play and any of the law enforcement agencies in those areas can be called on by you to try and support you in investigating and possibly prosecuting a crime has anybody had an example where law enforcement has to come into your organization we have to ask a couple questions so we can give out prizes so raise your hand go ahead sir
what was the you said it was cp oh yeah and that's and that actually that's one of the ways that uh mark and i ran into each other yeah it wasn't it's okay it's okay mark's out he's out now it's enough um no it was a it was an example of where we identified something on his network and we actually had a large network that that large corporate network had a large print okay so it's not it's not unusual that we may come to you without you coming to us if we see something on your network through our investigative access or tools or some other victim might might identify we may we may come to you and say hey we see something and
hopefully you'll work with us to try to try to determine what that is and that's where the crime scene becomes very important okay so a couple things you have to understand all law enforcement agencies have jurisdictions fbi's jurisdictions and authorities are national and possibly international in their through their legal attaches they are not the same agencies have different cyber capabilities they have different abilities to assist you we all watch you know the tv and we see you know the wonderful you know grab an image of a drive as they slap something on top of a hard drive 10 seconds later they're done they've got it they're running out the room that's not real you have some cyber some agencies that
cannot really actively support cyber some people who are world class so you're going to see different capable differing capabilities again we talked a little bit about federal crimes going those are united states code those are the fbi u.s federal court gbi can actually go to either state or federal court and then of course your local district attorney is going to probably charge state crimes in a state court so there's different if you're if you're dealing with a federal crime if you're dealing with a state crime there's different agencies that can both you know reported and prosecuted they are all fully engaged they're all busy they all have limited resources so there's gonna come times when you knock
on the door and they might say yeah that's a real great problem uh maybe you should call this guy so be prepared if that's what happens it not so much in the kind of cases that that brian's alluding to where you've got active ransomware you've got an active intrusion active compromise but if you're dealing with more financial crime uh or if you're dealing with with a a more of a financial loss situation sometimes it's you have to actually go to a couple of different uh law enforcement agencies until you find someone who's got the time resources and ability to prosecute it the very first case that was cyber case was prosecuted in the southern district
of georgia about 10 years ago it was when i first brought it to the u.s attorney's office it seemed like a pretty low dollar value case and they weren't they were interested because it was new as cyber because the dollar value was fairly low they weren't super excited about it but when we started to dig into what the actual cost of the crime was and it got over several hundred thousand dollars you know then you can get so i say that if your organization is struck by if you're victimized as part of a criminal act don't just look at you know the amount of ransomware look at the the what did they what did they defeat the amount of
resources that you utilized what you had to replace in order to protect yourself the the the client damage that you might have had so there's there's other areas that you can look at in this particular case it was just a matter of a former employee had logged in uh surreptitiously and and grabbed a bunch of uh of proposals and then underbid them well also lost business was one of the was one of the victimization so so think outside the box and those things will get your local prosecutors whether it's state local or federal they'll get them interested and it all because it helps the it's not it's not always worth it to go through a year of trial for a
six-month sentence or a probationary sentence but if you go through a lot of work and you can get somebody some true you know penalties you know that makes it more it's a little more it you get a little more out of it so that's but think outside the box when it comes to what the actual victimization is so at this point you know what can you do today if you know if you haven't had an engagement with law enforcement what can you do to make your life a little bit simpler well it's hard to call somebody you've never talked to you know call the front door and say hi fbi i've got a problem what are you going to do it's a lot
easier to call hey brian this is what just happened and you know how do i get support who do i talk to how do we move forward and the way easiest way to do that from a corporate perspective is look for outreach opportunities infragard is fbi's outreach program for critical infrastructure there is a chapter in atlanta there's actually a sub-chapter in augusta so you join the atlanta chapter and you're in this area put on the bottom of the in the notes field augusta and you will actually join our organization at which is just standing up right now it's great because it gives you an opportunity to go ask questions of the federal government ask questions of of the fbi get act some
access to what resource they can make available uh other things they they can possibly do is maybe deliver a threat brief targeted for your area do you know what the problems are in the area of your your building in the area of your data centers and the all of those questions that can can be addressed by asking the right people and again if time and resource resources are available they can do a threat brief they can talk about general threat and this is fantastic for you because it allows you to begin to do some targeting in terms of threats you want to be able to mitigate a risk you want to reduce it's also wonderful when your auditors come
around and they say well what have you done to kind of understand what's going on in your area well we talked to the fbi and they've delivered this particular idea and concept of current threat and we've addressed that in our program and we believe that we you know have reduced the risk to our operations so that's some of the benefits some of the ways you can do it um i don't know if you you know take people knocking on the door or calling you just saying hey we're very excited about the new regard chapters actually only one of two satellite chapters in the us and in guam it's because cyber is so important to this area so if you if you're interested
in that if that's something you want to be a part of um if you want to grab your email we'll make sure you're on the drug list we had planned on having a kickoff meeting in the next really we're talking about september october but because of the delta variant some of doj's policy prevented that but as soon as we're allowed to we're going to uh have a kickoff meeting at the cyber center it'll be an in-person and virtual and i think that the benefit of that organization here locally because we're a smaller community but we're very cyber focused will allow you to have some real good personal contacts but also access to the national level threats yes sir
that's a great question you're absolutely right there's there's so people are scared to reach out to us for a couple reasons one is that disruption to the business and the other one is what it will look like to the corporate brand is it going to negatively impact the image of your business and and i can say we work very hard to minimize both of those i can't always you know i can't guarantee you know the brain issue i mean if it comes out if you'll see under everybody knows colonial pipeline now and who talked about colonial pipeline until they got hit with ransomware and shut down gas or made gas prices go up probably but so i can't guarantee that
their image because some things are outside of our control however the disruption we will work everything and if you have a you know a company that you're working with some if not everybody has their own you know staff in-house so if there's corporation that you're working with that does your your protection we'll work directly with them we'll try to uh work off the backups we'll try to work off just the section that's maybe been in that has the the malware or the or the problem whatever we can do to get you back up and running as quickly as possible is what we're going to try to do todd you want to add anything to them
you've worked i mean we do the best we can i mean it's not it's not always easy but our goal we don't do any it's no value to you if we just re-victimize you down for for several hours or days yes sir
not obligation uh there are now it depends on what's taken if there's if they've got client victimization where uh people's personal data has been stolen there are regulations that control what they have to notify in terms of their sub-victims but corporates don't have to come they don't have to come to us they don't they can you know they can get something and deal with themselves and we hope that that doesn't happen because we can't prevent it if we don't know it's happening and and we have the and i can speak mostly for the fbi but also in working with secret service and dhs and we have great capabilities but we have to be able to utilize those i mean if
the corporations don't come to us and tell us or they come to us six months after the fact once they've realized that maybe they did have personal information get stolen and now they have an obligation it's too late for us to really do anything about it so the the idea is to encourage everybody to come to us immediately so that we can start to work proactively maybe even get on the network and start to track some of that stuff while it's still being active it gives us a better chance at success if you have a cyber event if you think about it you know you you've got a last ip that that came at you so if it was a cloud
service provider or some other formal hosting provider that really doesn't tell you much but you can't exactly call them they can actually serve subpoenas they can get that start working that hop backwards but you can only do that while the logs are available so time is of the essence if you want to start working that kind of thing backwards and your question is actually very relevant to this email right here so this is kind of an example of an email that might have been received it's kind of a precursor to a larger attack hey if you just give us some bitcoins and pay us now we'll prevent but this is an example if a corporation gets something like this and
doesn't notify us personally i think that's a not successful for for me for making the outreach but also for the corporation because at this level if you get something like this that says hey we're gonna we're planning a bigger attack we're actively on your network right now this would give us a great opportunity to go in and try to identify it and prevent it now the question has come up and i've heard this before is are we gonna make ourselves a bigger target if we go to law enforcement and i can't say that you won't but you also might make yourself not worth the effort if if they know you're going to go to the fbi or law enforcement then they
may go target somebody that's not going to do that the last victim we had locally that got hit with ransomware the owner was came right to us told us about it and he made one of the best comments i've ever heard he said i'd rather build my network back up from zero than pay these guys a dollar so that's the kind of that's the kind of attitude we want to try to hopefully instill in everybody so that you'll feel comfortable coming to us with this um 30 minutes goes by so quick the other big issue that we see a lot is business email compromise and this is critical if you get if you're if you get if you're a
victim of business email compromise and you notify ic3.gov which is the internet crime complaint center you can immediately there there's a there's a kill chain that works that will immediately try to set some things in motion to activate stopping the transfer of funds if you wait 48 hours to do that the chance of getting those funds recovered becomes almost i don't say zero but they become a lot less likely but if you can if you identify an email compromise where somebody has reallocated funds to a different account and you notify them through ic3 there is a really good process amongst the government that will try to stop the transfer of funds you know it's no guarantee i mean we had one
recently where they caught it pretty quick and they still you know didn't get all of their money back but if you get if you get half a million dollars stolen and you get four hundred thousand dollars back that's a better than losing half a million dollars i would think so so yeah and atlanta is number one for this risk i don't know why that uh is the case uh we're trying very hard to get the word out uh but a lot of times it's just education of your staff don't uh making sure they don't uh fall for login tricks or you know the banks should know not to transfer money through email change of accounts but a lot of we we
still see billions and billions of dollars being defrauded this way so it's very low cost it's actually no cost all they do is they create a forged email they send it to somebody for example your payroll administrator saying hey i just changed my bank account you need to make the update i'll make it effective immediately please um it happened to me it happened to another gentleman sitting in the room and you know we laughed because it's my job i chased that particular kind of fraud for it to happen for them to pick me was the absolute the most fun i've had with a fraudster in years if your organization is here with a business email compromise and you've
lost money you should do two things in two you should go to ic3.gov and you should call the local fbi though you should do those two things immediately that's that is your best chance of any kind of recovery yes sir
24 hours
you probably answered that better than i can i don't have a cause so i was trying to speak loud but for the regular we don't record direct regulators at all so when you report it to us whether hypothetical we're happy to have those conversations as well i have a friend company ryan we're happy to have those conversations there's no magic pause button but we don't report to regulators and we can certainly work with depending on the industry you're in we can work with those regulators to say hey this and company x reported to us we would like to work together to make sure we could do any operational necessary uh attribution pieces because there's definitely things we can
do on our end that may if if you actively being attacked we want to get in there while it's happening so so i think the answer is yes but it's probably on a case by we don't want to make a blanket statement and say we hit the pause button but we can certainly work with work with you to to facilitate if if there's a reason why we want to do that it helps the investigation we're bingo on time so why don't we just open the floor for questions and get rid of someone else we want to get you to chick-fil-a in the back please celestro
that's a great question so from a corporate perspective your contact to law enforcement is something that you need to organize and you need to have everybody engaged you need to have the team built that includes your corporate council you're going to want to know the executive board is going to want to be involved if you have a crisis communications team that keeps that critical portions of your company informed they're going to all want to know what's going on what's the next step they're going to want to know what information they have to release are there is there a requirement to notify regulators do you know what customer notifications have to take place if any so there's a lot of people that when
this event happens that are going to want to be engaged from a corporate side and this is something you can make your life a lot easier if you tabletop it if you exercise it so that you understand how you have to work together it's not just all pure play law enforcement there's a lot of work needs to be done in corporate side i'll i'll caveat that with when you have when when you reach out to us and get a threat brief and we're happy to do them um i would include your your practitioners but also you know your executive level and include your attorneys because i think when they hear and see the bigger picture they get more involved we do
we definitely want to get them involved early on because they can they can slow down and and shut down investigations where they don't really they're trying to be helpful but they're they're just causing it to be delayed and a lot of times if we don't act fast the chances of success become a lot less likely so i would get them on board very early invite them to the to the meetings with us prior to and invite him as soon as you're meeting which might happen part of the conversation we have anything left to give away uh mark had all the giveaways i don't know we have some more good gifts for the people asking questions
i gave them all to one person
yes sir i misunderstood what you said
um
i had a slide on that and i deleted it because i thought we were talking mostly about the liaison side of things but evidence is collected by law enforcement it's not collected by system administrators that being said collect according to best practices preserve logs preserve your regular business reporting that's going to be best evidence that you can provide to law enforcement uh preserve state to the extent possible if you can get if you have a compromise machine collect memory collect you know hard drive all that stuff all that best practice is critical um if you can put it in a in an envelope and and seal it and say this is sealed up and here's the image that's even
better because now you have a physical hard drive you can say which matches the actual image that you're that you're actually doing work against or you can give copies away if you have to so that's best answer i can give you i think no i think that's good i mean the evidence is what it is what you give us is going to be the evidence we'll come over we'll sign we'll once you give it to us we'll we'll establish the chain of custody for it and then it's you know in our in our lane and we'll protect it as we do any piece of evidence but i think i think mike's right i mean you
you do your best practices um anything you give us uh is is going to be helpful we're going to ask for any logs any data that you have any screenshots anything that you might have collected through the process and then once you give it does then it becomes evidence yes
um
that that's a great question if you and we we want any even if even if you're not you say you catch something before you become a victim we still might be interested in that we collect a lot of intelligence that we can either if it's you know maybe it's class nation state stuff it might be on the classifier we might provide that to some of our classified partners or if it's something that can help everybody in infragard we might put it out there so they can see that vulnerability and and make that pass so so just like everything else we've discussed if you see something like that the best thing to do is reach out to your local fbi office or whoever
secret service dhs whoever you're the most comfortable with but absolutely we're very interested in that we're in the way of launching this all right enjoy your lunch thank you all very much for your time enjoy the rest of the conference [Applause]





